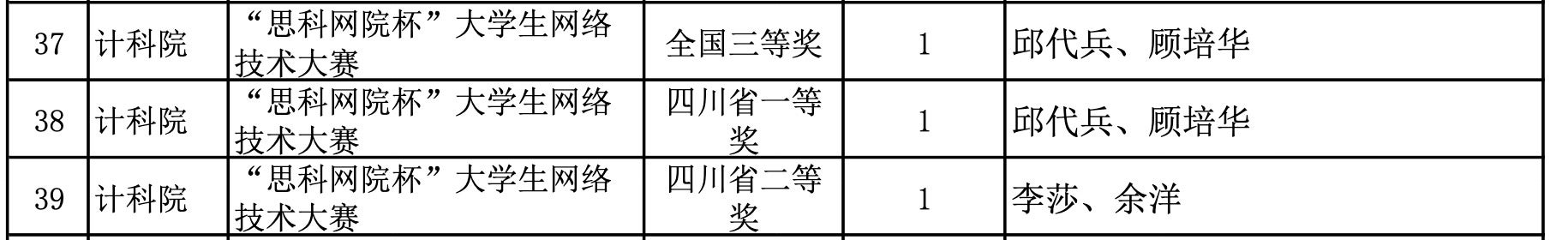
Salt Typhoon, linked to Yuyang (余洋) and Qiu Daibing (邱代兵), compromised more than 80 telecommunications companies worldwide to collect unencrypted calls and texts and to breach CALEA lawful-intercept systems. The report traces the operators to participation in the Cisco Networking Academy and a 2012 Cisco Network Academy Cup, highlighting how vendor training programs can inadvertently enable offensive capabilities against those vendors’ products. #SaltTyphoon #Cisco
Category: Threat Research

Elastic Security Labs discovered a new Windows backdoor named NANOREMOTE that provides reconnaissance, command execution, and robust file transfer capabilities by abusing the Google Drive API for stealthy payload staging and data theft. The implant is delivered via a loader (WMLOADER) that masquerades as Bitdefender software, shares code and keys with FINALDRAFT, and uses HTTP-based C2 plus in-memory PE execution techniques. #NANOREMOTE #FINALDRAFT
zLabs researchers identified a new Android ransomware campaign, DroidLock, that spreads via phishing sites and uses a dropper to install a secondary payload which abuses Accessibility and Device Admin permissions to fully takeover devices. The malware supports overlays to steal credentials and lock patterns, screen recording, VNC remote control, and communicates with C2 servers over HTTP and websockets. #DroidLock #Zimperium

AI-generated malware volume and sophistication are rapidly outpacing legacy detection tools, which miss a large fraction of new threats and give IT teams a false sense of security. A study of 500 U.S. IT professionals and real-world tests (e.g., Nimbus Manticore bypassing legacy tools on VirusTotal) show defenders underestimate unseen threats and must adopt preemptive deep learning defenses. #NimbusManticore #SitusAMC

Researchers linked a series of long-running, targeted cyberattacks against Russia’s IT sector (2024–2025) to APT31 and recovered unique samples of the group’s tools and methods. The attackers disguised malware as legitimate software, abused social network profiles and other online services for encrypted bidirectional C2, and used a keylogger that captured commands pasted from the clipboard. #APT31 #LocalPlugx

Check Point Research dissects the modular ValleyRAT (aka Winos/Winos4.0) backdoor, reverse engineering leaked builder artifacts and mapping all main plugins including an embedded kernel‑mode rootkit. The analysis highlights APC-based user‑mode injection, kernel-level forced deletion of AV/EDR drivers, valid-signed drivers loadable on Windows 11, and a rapid surge in in‑the‑wild samples since the builder leak. #ValleyRAT #SilverFox
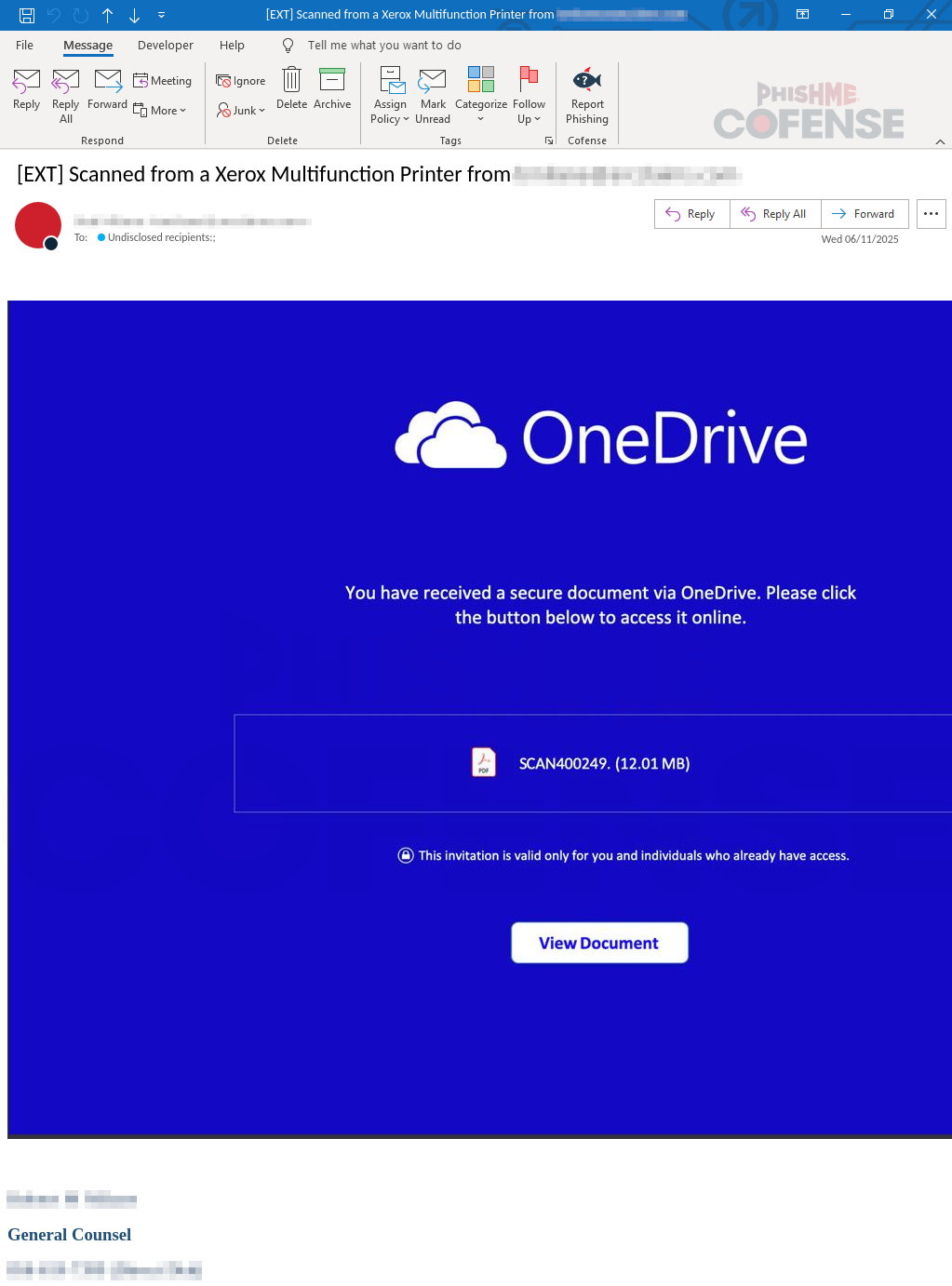
Threat actors are exploiting NoteGPT to host malicious files and lure recipients with OneDrive-branded phishing emails that redirect users to credential-harvesting pages. The campaign spoofs a trusted sender and uses a NoteGPT link that ultimately leads to a fake Microsoft login (arc[.]stylized[.]it[.]com) to capture professional credentials. #NoteGPT #OneDrive
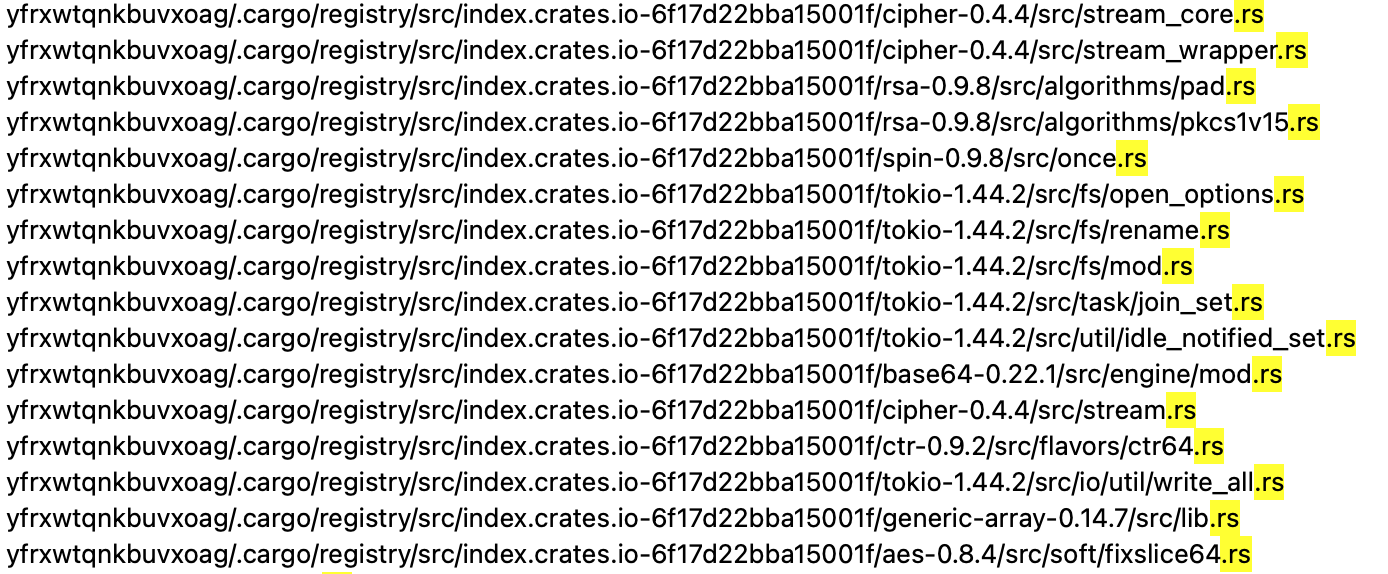
Researchers identified a new Rust-based ransomware family named 01flip that targets Windows and Linux systems in the Asia-Pacific region and is tracked as part of cluster CL-CRI-1036. The campaign involved manual activity, use of Sliver implants, exploitation attempts against CVE-2019-11580, and an alleged data leak posted to a dark web forum….

Group123 is a North Korean state-sponsored APT active since at least 2012 that conducts espionage across East and Southeast Asia, the Middle East, and beyond using spear‑phishing, malicious documents (including HWP), drive‑by exploits, and a large toolkit of loaders and implants to gain persistent access. Recent campaigns show intensified Windows-focused intrusions, advanced defense-evasion (DLL sideloading, hollowing, sandbox checks), cloud‑based C2, and a partial shift toward revenue generation including use of Maui ransomware. #Group123 #ROKRAT
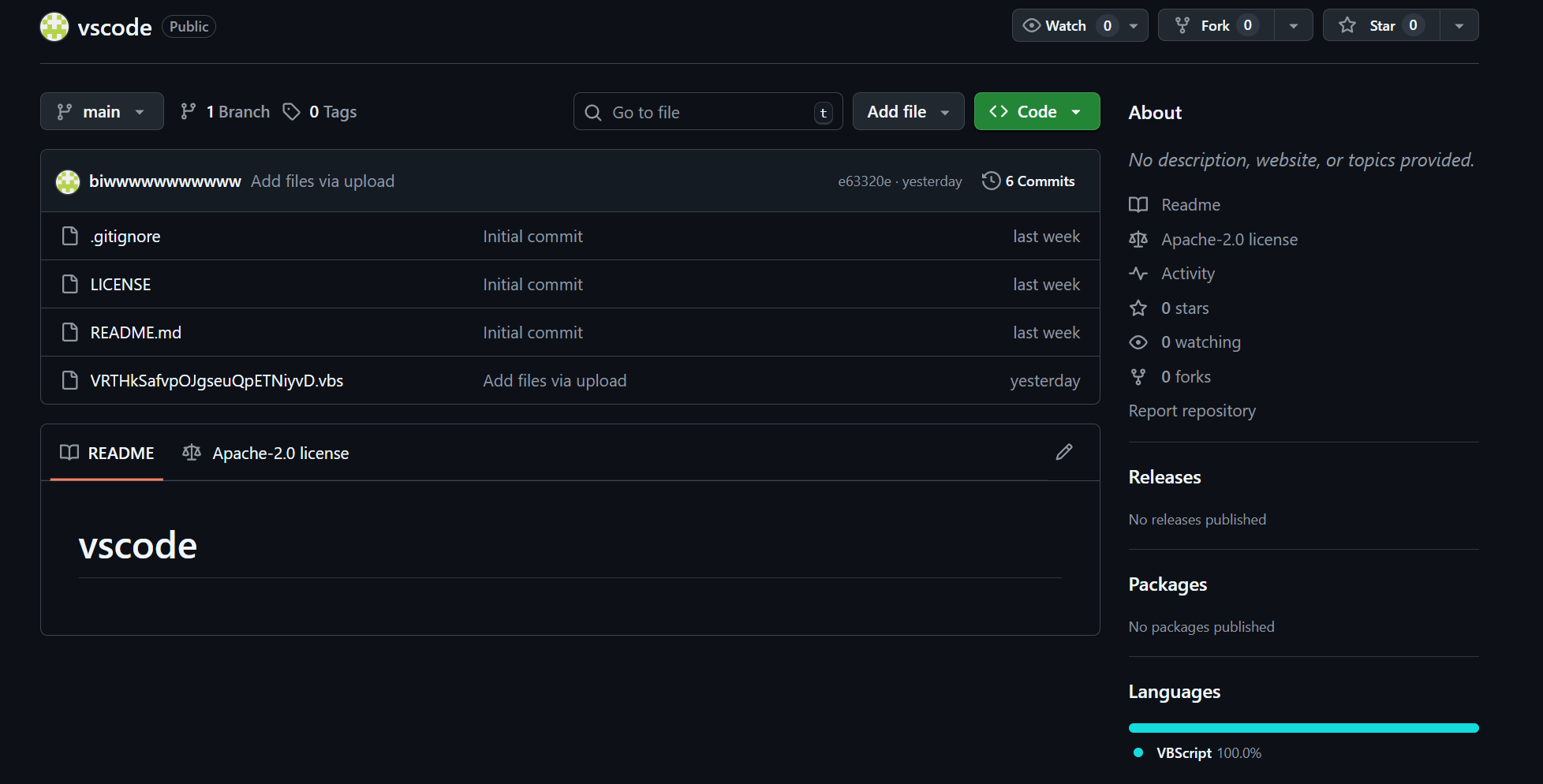
In late November 2025 a malicious Visual Studio Code extension named “prettier-vscode-plus” was published to the official Marketplace and used as a supply-chain entry point to deliver a multi-stage attack targeting developers. The chain deployed an Anivia loader (AES-encrypted in-memory decryption and process hollowing into vbc.exe) which dropped the OctoRAT remote access toolkit with extensive data-theft, persistence, privilege‑escalation and C2 capabilities. #Anivia #OctoRAT
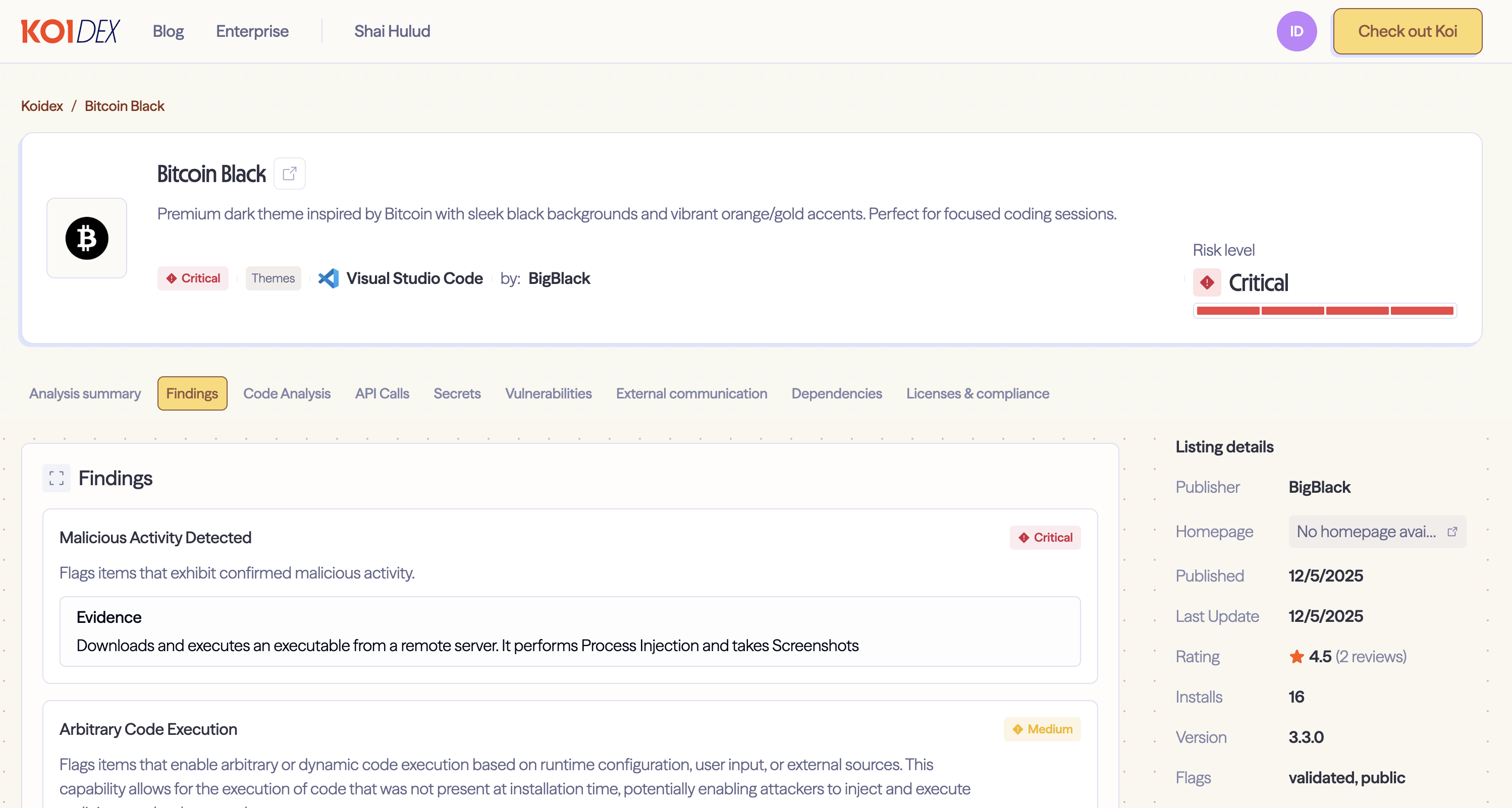
Researchers at Koi Security discovered two malicious Visual Studio Code extensions (Bitcoin Black and Codo AI) that deliver a DLL-hijacking infostealer via the legitimate Lightshot binary to capture screenshots, clipboard data, WiFi credentials, installed programs, and browser sessions. The attacker iterated delivery methods across versions (PowerShell with multiple extraction fallbacks to a streamlined curl-based batch downloader), used a memorable mutex (COOL_SCREENSHOT_MUTEX_YARRR), and phoned home to domains such as syn1112223334445556667778889990.org #BitcoinBlack #CodoAI

ReversingLabs researchers discovered a campaign of 19 malicious VS Code extensions that bundled modified dependencies to hide malware, including an archive disguised as a PNG that contained two malicious binaries. The attackers weaponized the popular npm package path-is-absolute (and in some cases used @actions/io), embedding a base64-reversed JavaScript dropper that decodes and launches payloads via cmstp.exe on VS Code startup. #path-is-absolute #VSCodeMarketplace
CVE-2025-55182 (React2Shell) is a critical (CVSS 10.0) pre-authentication remote code execution in React Server Components that allows attackers to craft Flight payload chunks to reach the Function constructor and execute arbitrary Node.js commands. Trend observed widespread in-the-wild exploitation and multiple campaigns (e.g., emerald, nuts) delivering Cobalt Strike, Mirai variants, Nezha, Sliver,…
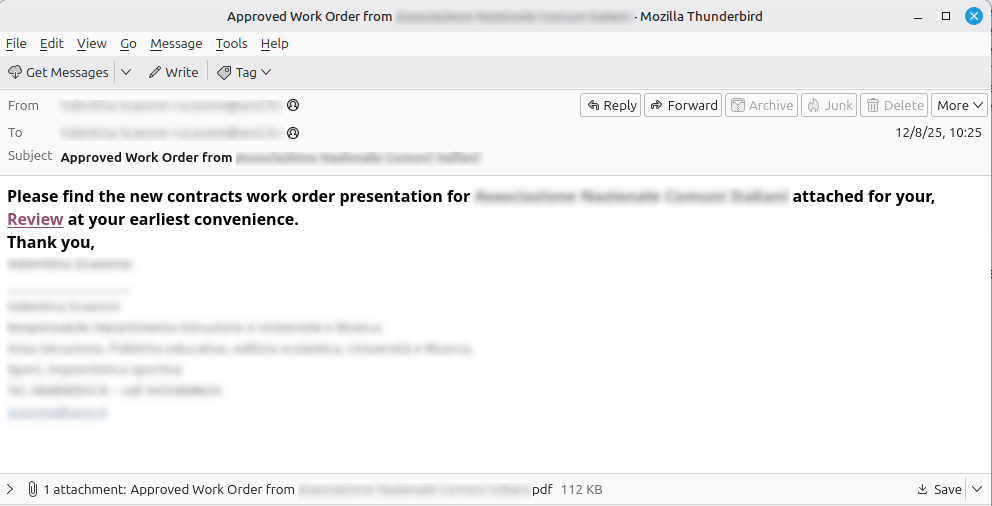
Two compromised email accounts belonging to Italian public administration users have been used since December 8 to send mass phishing messages with malicious PDF attachments that redirect victims to a Figma page requesting login. The campaign likely aims to harvest real email identities or stage a second-phase follow-up using trust in a legitimate service. #CERT-AGID #Figma

UDPGangster is a UDP-based backdoor attributed to the MuddyWater group that is distributed via macro-enabled Microsoft Word documents to gain initial access and establish C2 over UDP. The malware uses extensive anti-analysis checks, persistence via registry startup, and capabilities for remote command execution and file exfiltration to target users in Turkey, Israel, and Azerbaijan. #UDPGangster #MuddyWater