This article presents a reproducible, Docker-packaged Jupyter Notebook workflow that leverages pythonnet and dnlib to statically extract QuasarRAT’s configuration from .NET assemblies, handling both unobfuscated and obfuscated builds. It explains locating .cctor/Aes256/Settings in IL, recovering AES-256/PBKDF2 cryptographic parameters (salt, key, IV), and automating decryption of embedded strings with a Python extractor; full code is available in the Sekoia.io Community repository. #QuasarRAT #dnlib
Category: Threat Research
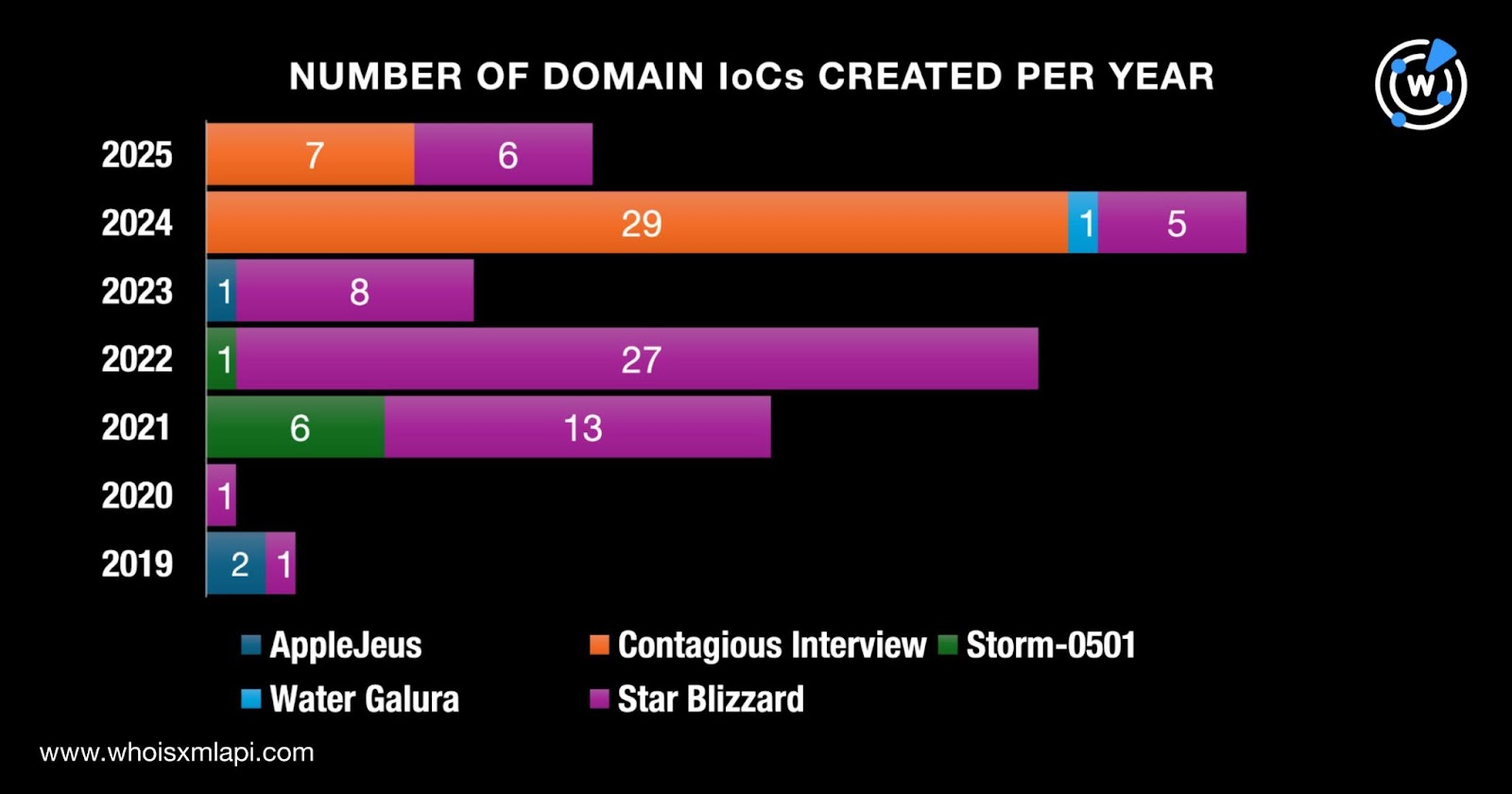
MITRE identified nine new threat groups tied to the most abused vulnerabilities from August–October 2025 and researchers compiled IoC lists (originally 126 domains, reduced to 108 suspicious/malicious after analysis) plus 31 IPs and 5 email addresses for deeper investigation. The analysis uncovered pre-malicious domain detections, extensive historical DNS/IP resolutions, and network traffic linking 1,839 potential victim IPs to IoC infrastructure. #AppleJeus #LazarusGroup

Researchers discovered a campaign using spam comments on Itch.io that link to Patreon-hosted downloads containing a nexe-compiled Node.js executable which performs multi-stage obfuscation, anti-analysis checks, and ultimately loads a LummaStealer payload. The malicious mains.js and modules.node components use heavy sandbox/VM detection and a reflective loading technique to execute the LummaStealer variant on victim systems. #Itchio #LummaStealer

Attackers can bypass MFA by abusing the OAuth 2.0 Resource Owner Password Credentials (ROPC) flow to exchange stolen usernames and passwords for tokens while impersonating pre-approved public client application IDs in Microsoft Entra ID tenants. Detection and mitigation require logging and correlating token/grant events, revoking refresh tokens, disabling legacy grants for…
React2Shell (CVE-2025-55182) is a critical unauthenticated remote code execution vulnerability in React Server Components that allows attackers to deliver malicious Flight payloads and achieve code execution on servers running React 19.x with Server Components. It was rapidly weaponized with public PoCs, Metasploit modules, large-scale scanning, confirmed compromises, and nation-state exploitation—forcing KEV listing and causing operational impacts reported by providers like Cloudflare. #React2Shell #CVE-2025-55182

Shanya is a packer-as-a-service (crypter) widely used in 2025 to obfuscate loaders and payloads, enable AMSI and UAC bypasses, perform DLL side-loading, and deliver EDR-killing components that facilitate ransomware and backdoor deployments. The service has been linked to multiple malware families and operations—including CastleRAT and Akira—and associated IOCs include packed sample hashes, malicious domains, and side-loaded DLL/file names. #Shanya #CastleRAT
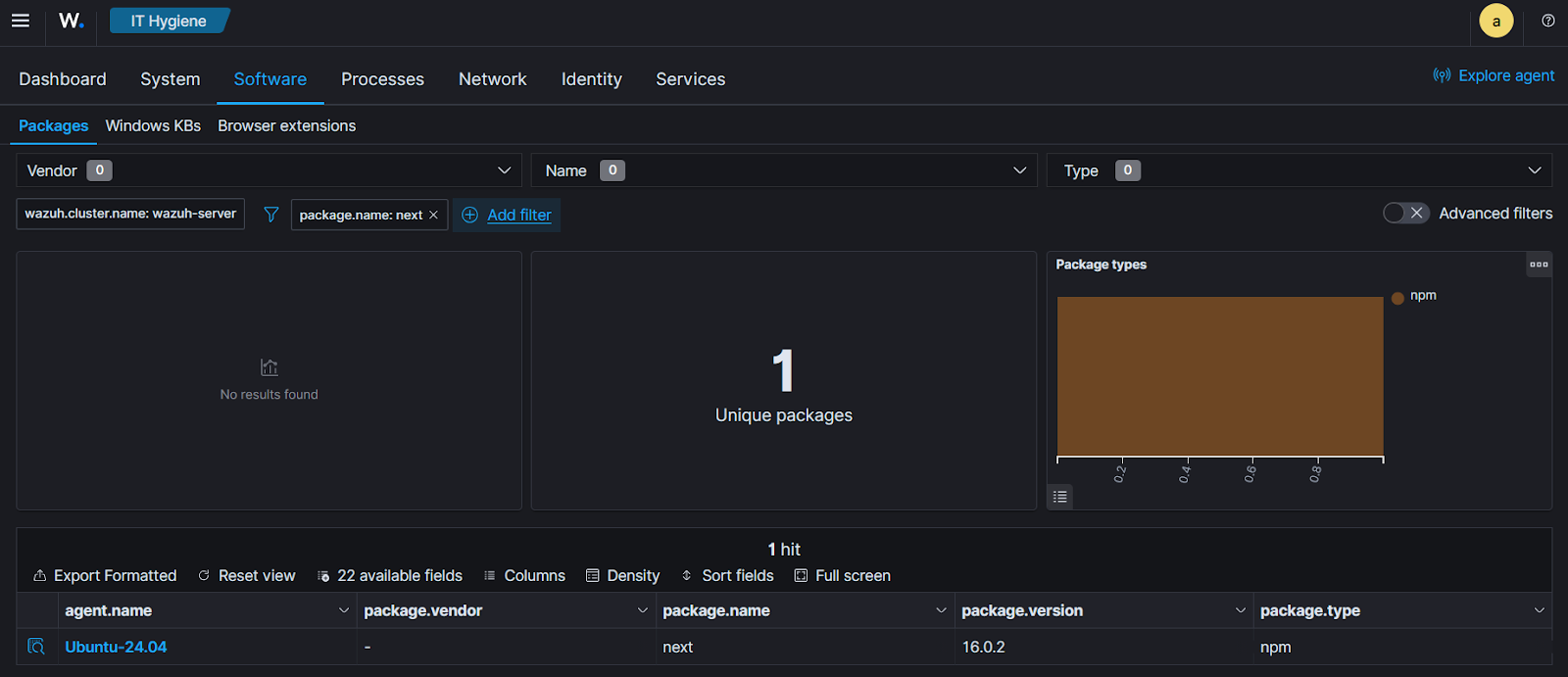
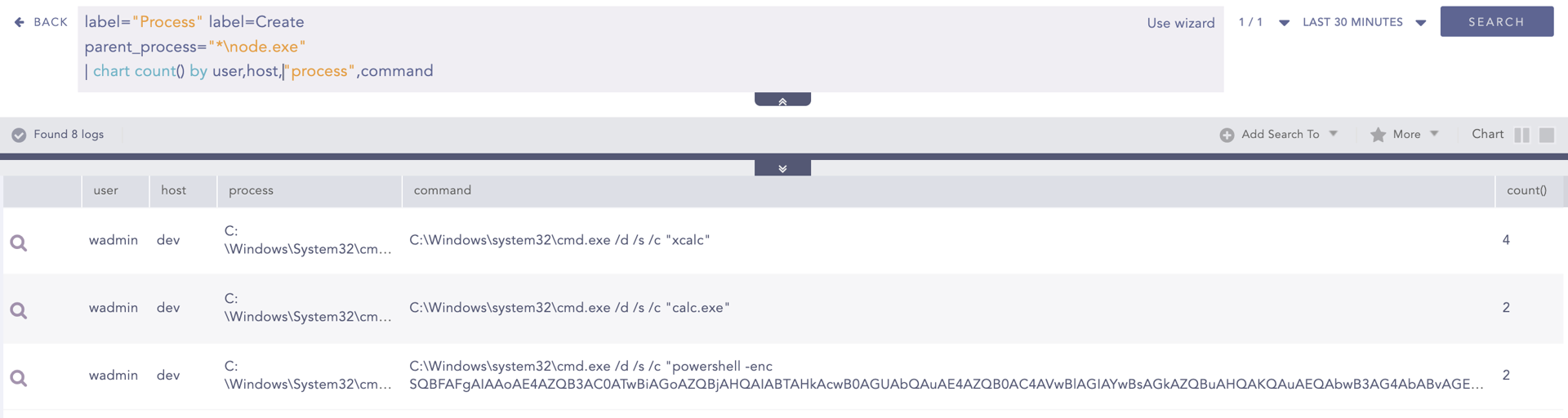
A critical Remote Code Execution (RCE) vulnerability (CVE-2025-66478) in Next.js App Router arises from an upstream flaw in the React Server Components (RSC) protocol (CVE-2025-55182), allowing unauthenticated attackers to send crafted RSC requests that execute arbitrary code on vulnerable servers. Wazuh can detect exposed systems by identifying vulnerable package versions, monitoring…

Socket’s Threat Research Team discovered typosquatting crates targeting Rust developers: finch-rust acts as a malware loader that depends on an evolving credential-stealer sha-rust which exfiltrates configuration and credential files to a C2. The campaign used impersonation of a real developer, fabricated GitHub metadata, and an unpinned dependency to automatically deliver updated malware to victims. #finch-rust #sha-rust

Law firms are an industry-wide target for industrialized ransomware and data theft, with groups like RansomHub and the Qilin ransomware specifically targeting legal firms to harvest high-value M&A, litigation, and client data for extortion. Enterprises must treat professional services as high-risk technology vendors and apply stricter vendor controls, monitoring, and incident playbooks to prevent cascading strategic intelligence compromises. #RansomHub #Qilin

A critical unauthenticated remote code execution vulnerability in React Server Components (CVE-2025-55182) allows attackers to execute arbitrary code on affected server-side applications and has been assigned a CVSS score of 10.0. The flaw impacts downstream projects including Next.js (tracked as CVE-2025-66478), public exploit code and a working PoC exist that can compromise default create-next-app instances, and widespread scanning was observed in the wild. #CVE-2025-55182 #Nextjs
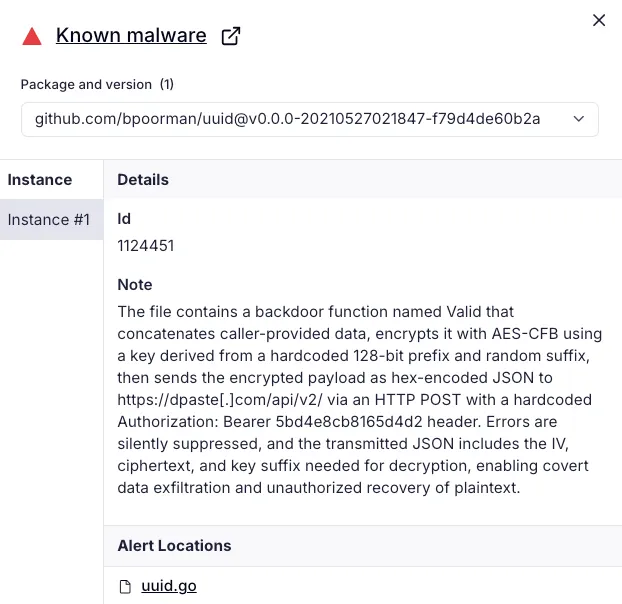
Researchers at Socket discovered two malicious Go packages that typosquat popular UUID libraries and exfiltrate data to the pastebin-style service dpaste. The packages (github.com/bpoorman/uuid and github.com/bpoorman/uid) preserve expected UUID behavior while adding a hidden Valid function that encrypts caller-supplied data and uploads it with a hardcoded dpaste API token. #bpoorman #dpaste

Sophos linked nearly 40 STAC6565 intrusions (Feb 2024–Aug 2025) to the GOLD BLADE group, which has evolved from espionage into a hybrid operation that mixes targeted data theft with selective ransomware deployment using a custom locker called QWCrypt. The group refines RedLoader delivery chains, abuses recruitment platforms to deliver weaponized resumes, leverages BYOVD drivers and modified Terminator tools for EDR evasion, and uses RPivot/Chisel for tunneled C2. #GOLD_BLADE #QWCrypt

ASEC reported that the UNC5174 threat group deployed a Discord-based backdoor built with the open-source Discordgo library, using Discord API message events as a covert C2 channel to execute commands, transfer files, and exfiltrate data. The malware stores encrypted bot tokens and server IDs (Base64 + AES), executes commands via bash…
CrowdStrike tracked a China-nexus adversary dubbed WARP PANDA conducting persistent, stealthy intrusions against VMware vCenter and ESXi environments across U.S. legal, technology, and manufacturing organizations, deploying BRICKSTORM, JSP web shells, and two new Golang implants named Junction and GuestConduit. The actor exploited internet-facing edge device and vCenter vulnerabilities, tunneled traffic and…

Attackers exploited a GitHub Actions injection vulnerability in Nx’s workflow to steal an NPM publishing token, push malicious Nx packages, and use those packages to harvest credentials, SSH keys, and crypto wallets from developer systems. The campaign evolved into a self-replicating NPM supply-chain worm called Shai-Hulud that registers compromised hosts as self-hosted GitHub Actions runners and uses GitHub Discussions as a stealthy C2 channel. #ShaiHulud #Nx
