React2Shell (CVE-2025-55182) is a critical unauthenticated remote code execution vulnerability in React Server Components that allows attackers to deliver malicious Flight payloads and achieve code execution on servers running React 19.x with Server Components. It was rapidly weaponized with public PoCs, Metasploit modules, large-scale scanning, confirmed compromises, and nation-state exploitation—forcing KEV listing and causing operational impacts reported by providers like Cloudflare. #React2Shell #CVE-2025-55182
Keypoints
- React2Shell (CVE-2025-55182) enables unauthenticated RCE via malicious Flight payloads against React Server Components in React 19.x and related server DOM packages.
- Affected packages include react-server-dom-parcel, react-server-dom-webpack, and react-server-dom-turbopack; patched versions are 19.0.1, 19.1.2, and 19.2.1.
- Exploit tooling and PoCs proliferated immediately (Metasploit modules, GitHub scripts, scanners), enabling widespread automated probing and exploitation of RSC endpoints.
- Large-scale exposure was observed (Shadowserver reported 77,664 internet-exposed vulnerable IPs) and multiple organizations were confirmed compromised, with nation-state groups (Earth Lamia, Jackpot Panda) observed exploiting the flaw.
- CISA added CVE-2025-55182 to the KEV catalog and Cloudflare reported service instability tied to emergency mitigations, underscoring high operational and national-infrastructure impact.
- Primary defense actions: patch RSC packages and frameworks immediately, restrict and WAF-protect RSC endpoints, rotate secrets and keys, enhance telemetry/hunting for post-exploitation behaviors, and rebuild compromised workloads from clean images.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – RSC vulnerability used for initial access and remote code execution (‘allows attackers to deliver malicious Flight payloads and gain unauthenticated code execution on vulnerable servers.’)
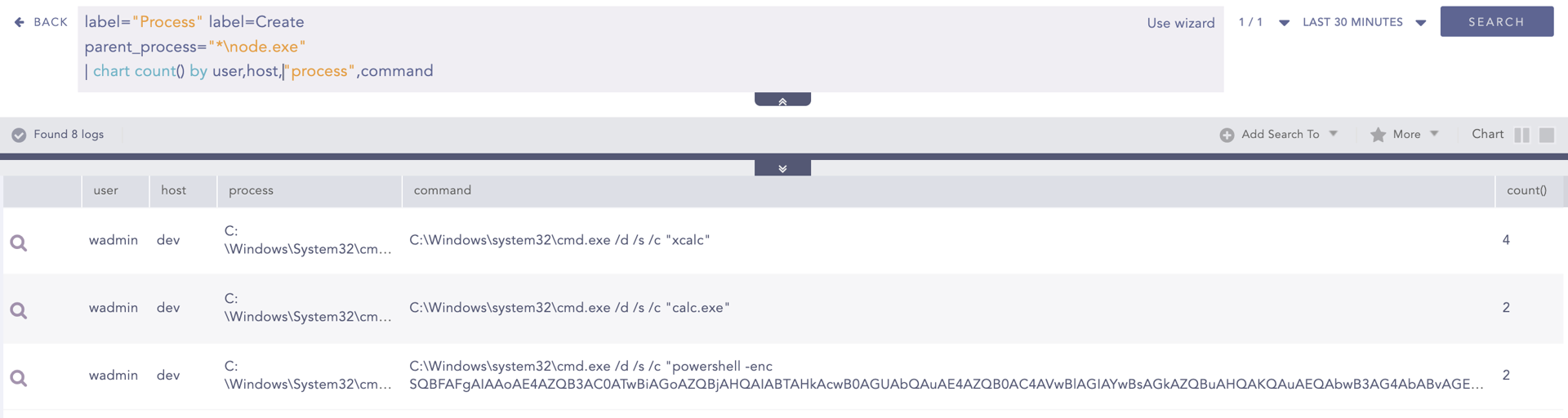
- [T1059 ] Command and Scripting Interpreter – Attackers and post-exploitation use of shells and scripting for payload delivery and actions (alerts note ‘execution of binaries or command-line tools used to perform web requests or file downloads, such as wget, curl, or PowerShell web request cmdlets.’)
- [T1595 ] Active Scanning – Large-scale internet probing to find vulnerable RSC endpoints (‘77,664 internet-exposed IPs vulnerable to the React Server Components RCE’).
- [T1136 ] Create Account – Adversaries may create or remove accounts for persistence or privilege (‘Windows User Account Created or Removed (Event ID 4720)’).
- [T1053 ] Scheduled Task/Job – Use of scheduled tasks for persistence or execution (‘Suspicious Scheduled Task CreationDetects the creation of suspicious scheduled tasks commonly used by adversaries to maintain persistence or trigger payload execution.’)
- [T1547 ] Boot or Logon Autostart Execution – Modification of autorun registry keys to achieve persistence (‘Autorun Keys Modification DetectedDetects modifications to registry keys responsible for launching applications during system startup’).
- [T1562 ] Impair Defenses – Attempts to disable or modify security controls, including firewall and Defender (‘Firewall Disabled via Netsh Detected’ and ‘Microsoft Defender Disabling Attempt via PowerShell’).
- [T1112 ] Modify Registry – Registry modifications observed as part of defense tampering or persistence (‘Suspicious Windows Defender Registry Keys ModificationMonitors sensitive registry changes that could weaken or disable Defender protections.’)
- [T1555.003 ] Credentials from Web Browsers – Access to browser credential stores for credential theft (‘Browser Credential Files AccessedFlags access to browser credential stores, such as Chrome or Edge login data files.’)
Indicators of Compromise
- [IP Addresses ] internet exposure and scanning context – 77,664 internet-exposed IPs reported vulnerable by Shadowserver (scan results)
- [CVE Identifier ] tracked vulnerability context – CVE-2025-55182 (KEV-listed, actively exploited)
- [Package / Library Names ] vulnerable component context – react-server-dom-parcel, react-server-dom-webpack (vulnerable packages requiring patching)
- [Exploit/Tool Names ] tooling used for exploitation context – Metasploit module, public GitHub PoC scripts (rapidly released exploit code and scanners)
- [Log/Event Names ] detection/hunting context – Windows Event ID 4720 (user account creation), process and network telemetry entries showing Node.js spawning unexpected child processes
Read more: https://logpoint.com/en/blog/after-react2shell-following-the-attacker-from-access-to-impact