Predator is a modular, stealthy mercenary spyware developed by Cytrox and distributed via an Intellexa-linked corporate web, enabling full access to microphones, cameras, and all device data on Android and iPhone devices. The report maps Intellexa’s fragmented corporate infrastructure, documents delivery methods including “1-click” and ad-based (“Aladdin”) vectors, and details observed deployments across multiple countries alongside mitigations and ongoing investigations. #Predator #Intellexa
Category: Threat Research
A ValleyRAT campaign targeted job seekers with email lures that delivered weaponized Foxit PDF Reader executables inside archive files, using DLL side-loading of a malicious msimg32.dll to achieve execution. The attackers deployed a bundled Python environment and a base64-encoded shellcode loader downloaded from 196[.]251[.]86[.]145, created an autorun registry entry for persistence,…
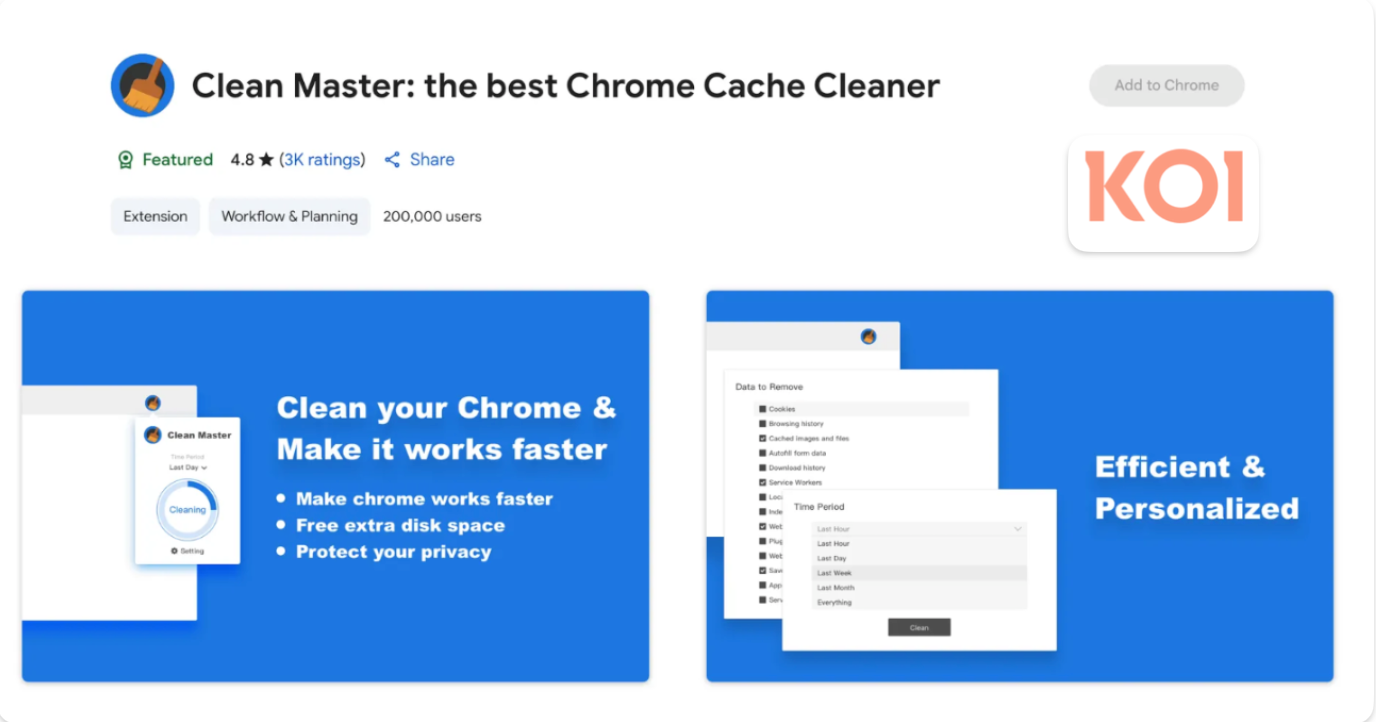
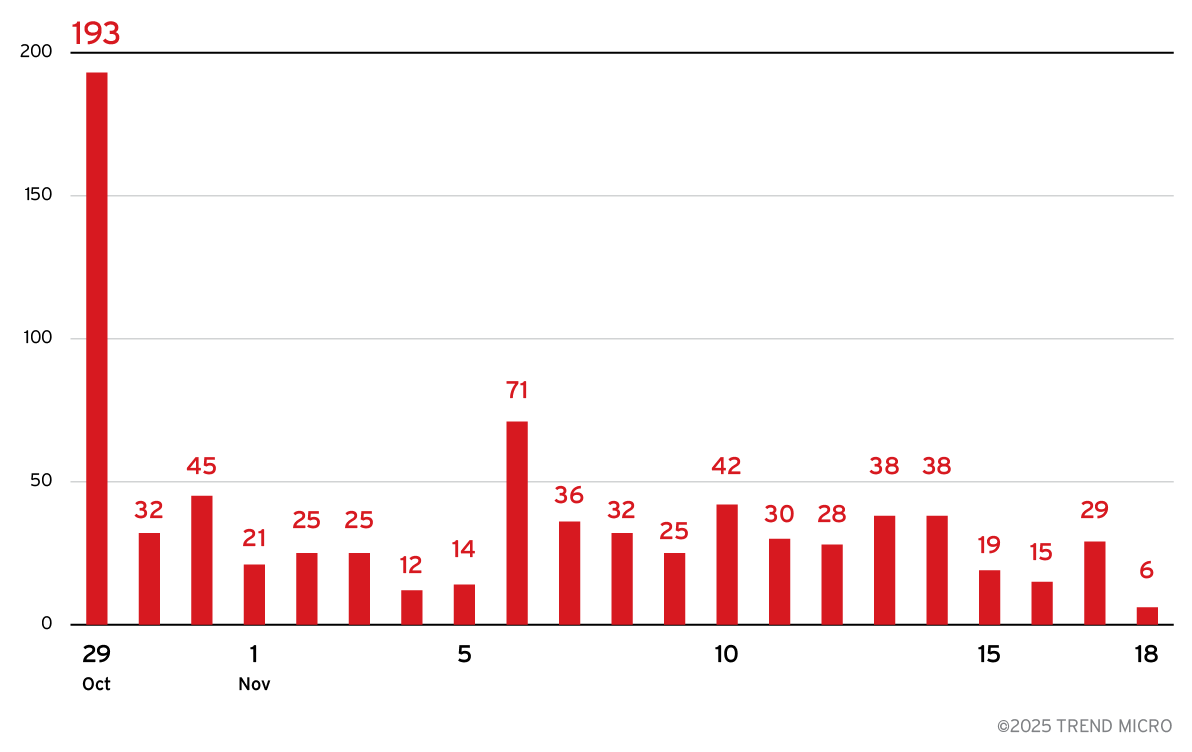
ShadyPanda ran a seven-year browser-extension campaign that weaponized trusted Chrome and Edge extensions to deploy a remote-code-execution backdoor (300K+ users) and a separate 4M+ user spyware operation centered on WeTab. The actor abused featured/verified status and auto-update mechanisms to exfiltrate browsing history, cookies, keystrokes, and full browser fingerprints for real-time surveillance and potential future attacks. #ShadyPanda #CleanMaster

Nimbus Manticore is a highly obfuscated 64-bit PE malware built to escalate privileges, move laterally via RPC, dynamically load components, and evade sandboxes using timing checks. Deep Instinct was the only vendor on VirusTotal to detect it for a full week, highlighting detection gaps against this threat. #NimbusManticore #DeepInstinct

CERT-AGID has detected a phishing campaign that abuses the name and insignia of the Italian Government and the Presidency of the Council of Ministers to steal banking login credentials. Emails titled "Verification of Banking Data – Italian Government" redirect victims to pages that mimic institutional graphics and then to fake bank login portals to capture customer IDs and PINs. #CERTAGID #PresidencyOfTheCouncil

ReliaQuest attributes an ongoing Microsoft Teams SEO-poisoning campaign to the Chinese APT group Silver Fox, which uses a modified ValleyRAT loader (including Cyrillic false flags) to target Chinese-speaking users and Western organizations with operations in China. The campaign leverages typo-squatted domains and Alibaba Cloud hosting to deliver ValleyRAT via a trojanized Teams installer, enabling rundll32-based Binary Proxy Execution, C2 communications, data exfiltration, and financial theft to fund operations. #SilverFox #ValleyRAT
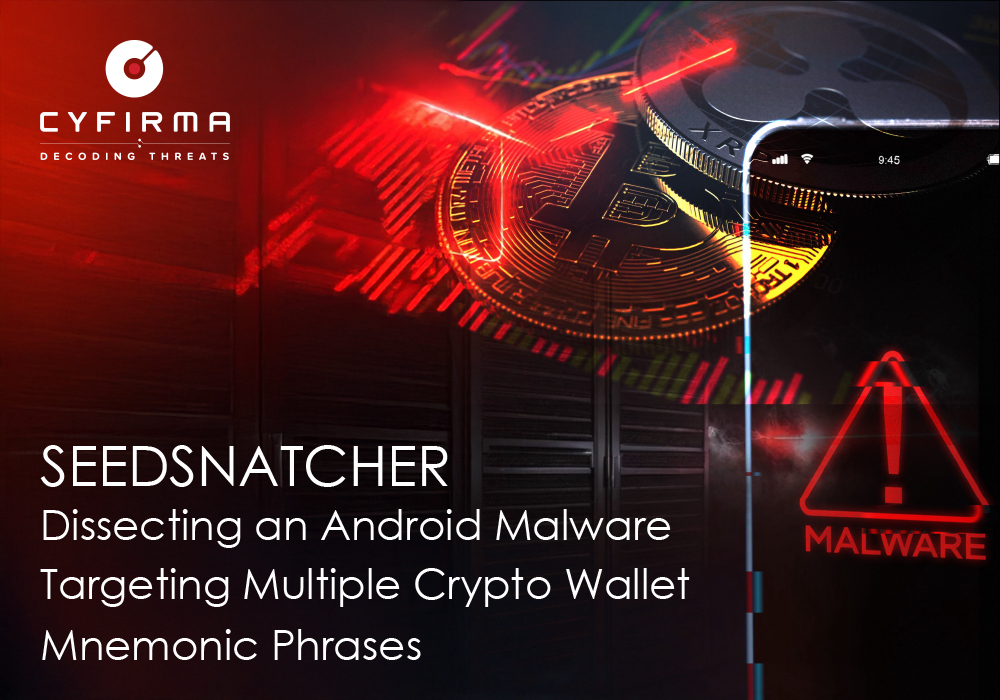
SeedSnatcher (distributed as the “Coin” APK com.pureabuladon.auxes/Coin.apk) is an Android crypto-mnemonic stealer that uses WebView overlays, dynamic class loading, integer-based WebSocket C2 commands, and broad permission abuse to harvest seed phrases, SMS, call logs, contacts, screenshots, and other device data. The campaign is distributed via affiliate links on social platforms (notably Telegram), tracks installs with agent identifiers, and communicates with C2 apivbe685jf829jf[.]a2decxd8syw7k[.]top to exfiltrate stolen assets and control infected devices. #SeedSnatcher #TrustWallet
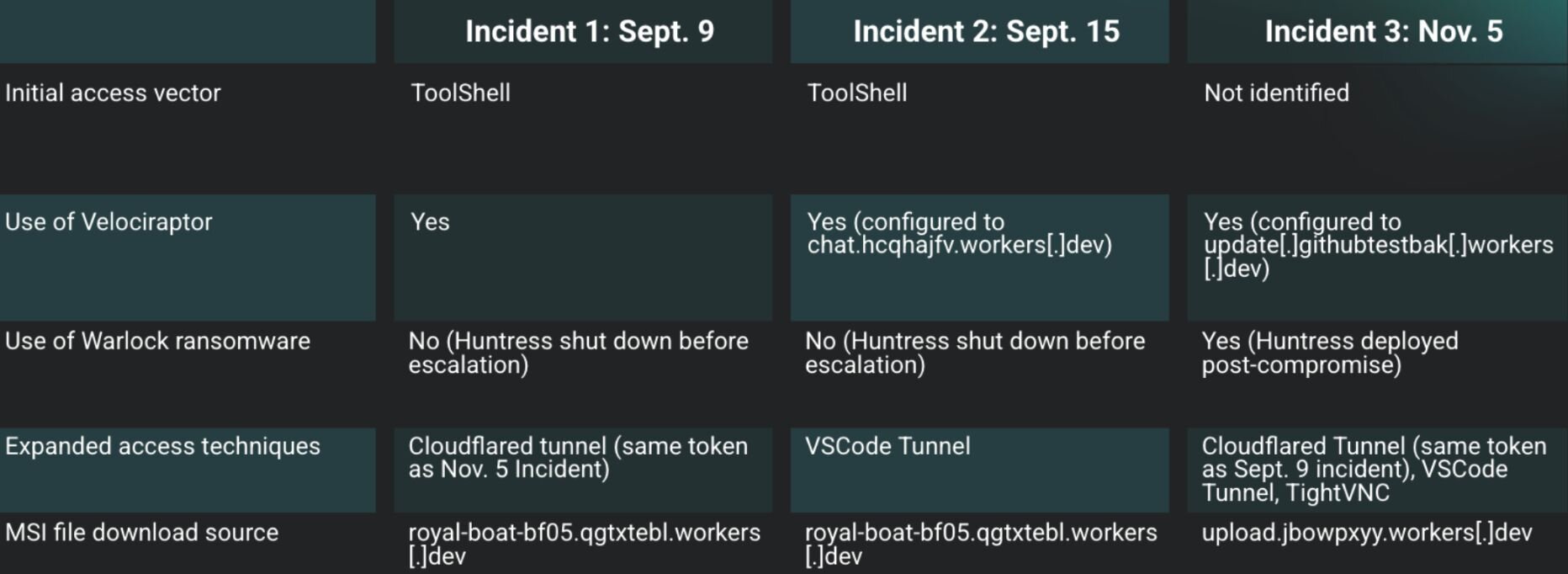
Huntress investigated three incidents between September and November where threat actors leveraged SharePoint ToolShell and other vulnerabilities to install Velociraptor and establish tunneled C2 using legitimate tools like Visual Studio Code and Cloudflare. One incident culminated in a Warlock ransomware compromise and showed overlapping IOCs (for example royal-boat-bf05.qgtxtebl.workers[.]dev) and technique reuse that links some activity to Storm-2603. #Velociraptor #Warlock

Cyble Research & Intelligence Labs (CRIL) uncovered an active Linux campaign delivering a Mirai-derived V3G4 botnet that performs raw-socket SSH scanning, C2 DNS resolution, and process masquerading before deploying a runtime-configured XMRig Monero miner. The campaign uses an architecture-aware downloader, tmpfs staging, UPX-packed binaries, and fileless miner configuration fetched from C2 to maximize stealth and evasion. #V3G4 #XMRig
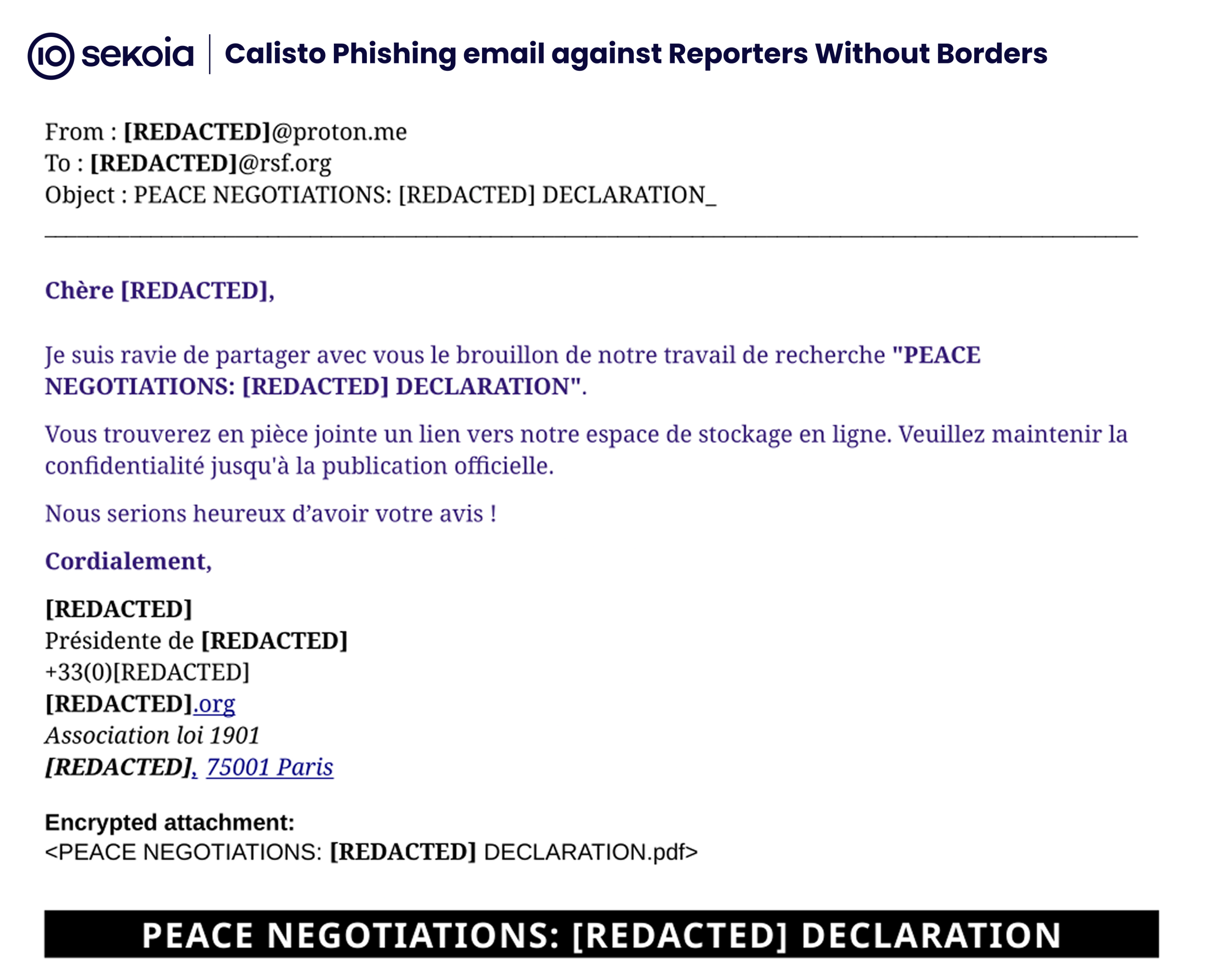
Calisto (aka ColdRiver/Star Blizzard), an intrusion set attributed to Russia’s FSB, resumed spear-phishing campaigns in May–June 2025 targeting NGOs, researchers, and institutions supporting Ukraine using impersonation, compromised redirectors and an AiTM phishing kit that can relay 2FA. The group used ProtonMail-themed decoys, PHP redirectors on compromised sites, and a homemade JavaScript-based kit hosted on domains such as simleasip[.]org to capture credentials. #Calisto #ReportersWithoutBorders

Matanbuchus is a C++ malicious downloader/backdoor offered as MaaS since 2020 that downloads and executes second-stage payloads and supports hands-on-keyboard activity, often observed in ransomware-linked operations. Version 3.0 introduced Protobuf-based serialized network communication and extensive ChaCha20-based encryption and obfuscation methods. #Matanbuchus #Rhadamanthys
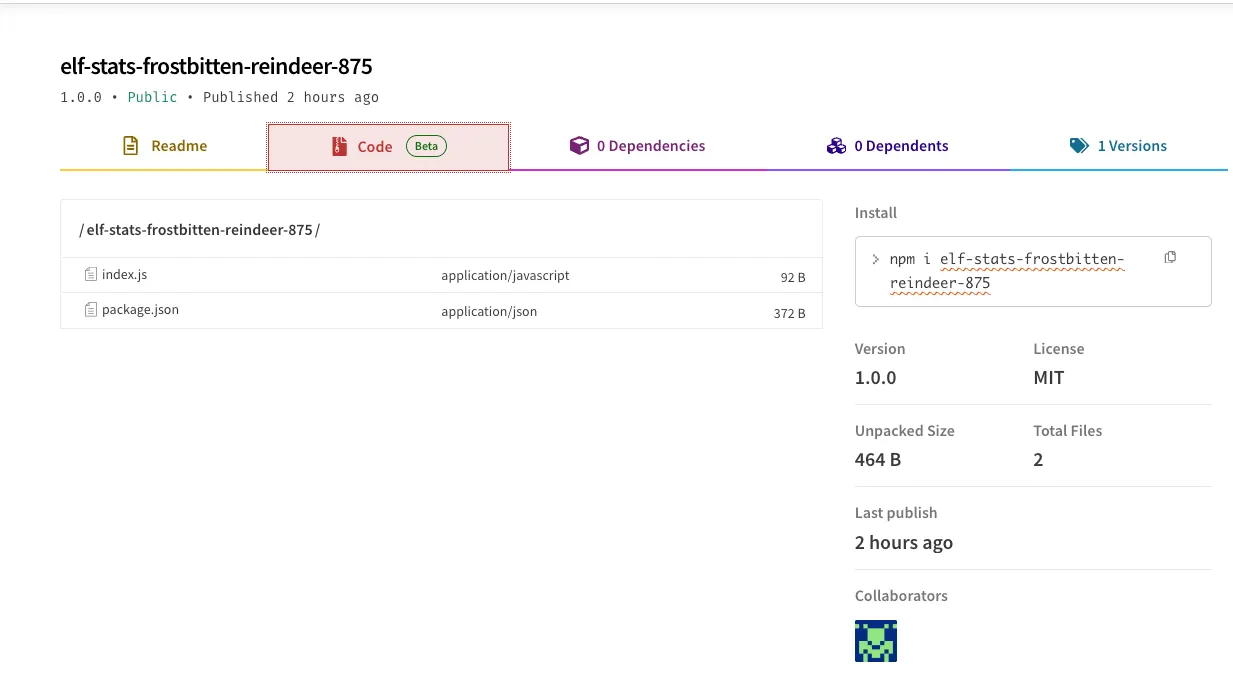
A surge of at least 420 likely automated, malicious npm packages following an “elf-stats-*” naming pattern was identified, many containing low-effort command execution or exfiltration code and rapid publish cadences. The packages are being removed by npm as investigators track payloads, authors, C2 endpoints, and related indicators. #elf-stats #npm
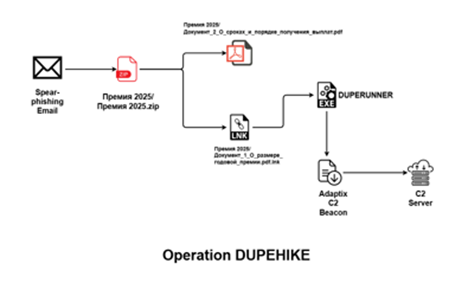
SEQRITE researchers uncovered a targeted campaign against Russian corporate HR and payroll teams using spear-phishing ZIPs with a malicious LNK that downloads a C++ implant named DUPERUNNER which injects and executes an AdaptixC2 beacon. The operation leverages a remote host at 46[.]149[.]71[.]230 to stage multiple files and host C2 services, producing observable artifacts including SHA-256 hashes, filenames, and ASN hosting details. #DUPERUNNER #AdaptixC2

FortiGuard Labs observed the Mirai-based botnet variant “ShadowV2” spreading via multiple IoT vulnerabilities during a global AWS connectivity disruption, impacting devices from vendors such as D-Link, TP-Link, DD-WRT, DigiEver, and TBK across many countries and industries. The campaign delivered a downloader (binary.sh) and the shadow-prefixed payloads (e.g., shadow.x86_64) connecting to the C2 silverpath.shadowstresser.info (81.88.18.108), and is assessed as likely a test run for future attacks. #ShadowV2 #DLinkDNS320
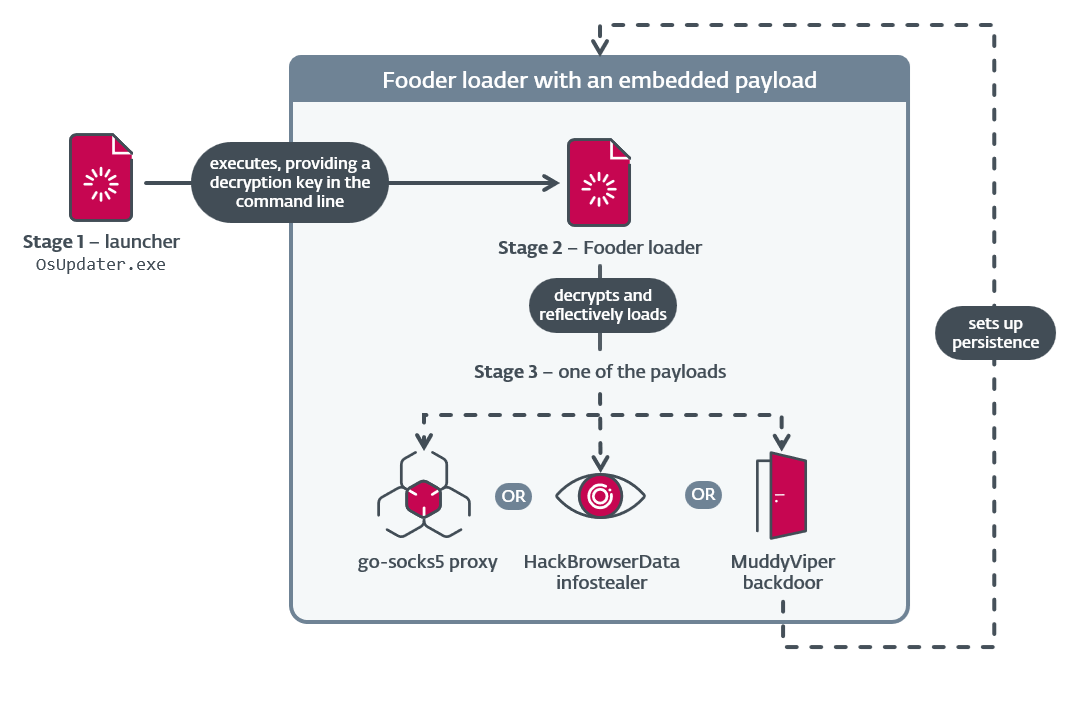
ESET reports that MuddyWater (TA450) conducted a focused cyberespionage campaign primarily against organizations in Israel and one confirmed target in Egypt using new custom tools including the Fooder loader and the MuddyViper backdoor to improve evasion and persistence. The campaign also deployed credential stealers (CE-Notes, LP-Notes), browser stealers (Blub), go‑socks5 reverse tunnels, and adopted the CNG API for encryption to exfiltrate credentials and browser data. #MuddyWater #MuddyViper
