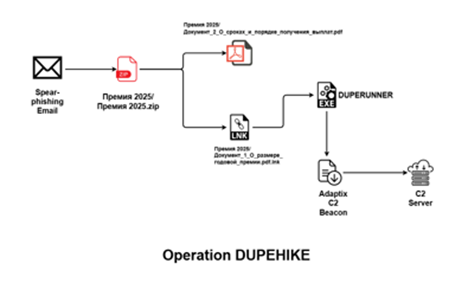
SEQRITE researchers uncovered a targeted campaign against Russian corporate HR and payroll teams using spear-phishing ZIPs with a malicious LNK that downloads a C++ implant named DUPERUNNER which injects and executes an AdaptixC2 beacon. The operation leverages a remote host at 46[.]149[.]71[.]230 to stage multiple files and host C2 services, producing observable artifacts including SHA-256 hashes, filenames, and ASN hosting details. #DUPERUNNER #AdaptixC2
Keypoints
- Actors used spear-phishing ZIP archives (e.g., “Премия 2025.zip”) containing a PDF-themed LNK lure to target HR and payroll teams in Russian corporate organizations.
- The LNK launches PowerShell (flags -NoNI -nop -w hidden) to download s.exe (DUPERUNNER) from 46[.]149[.]71[.]230 and execute it, enabling multi-stage infection.
- DUPERUNNER is a C++ second-stage implant that downloads a staged loader (fontawesome.woff/fontawesome_tld.woff), writes a timestamped PDF to Temp, spawns it, enumerates processes, and prepares shellcode for injection.
- DUPERUNNER performs Remote-Thread Injection into explorer.exe, notepad.exe, or msedge.exe to execute the AdaptixC2 beacon, then exits to hand off execution to the final stage.
- The AdaptixC2 stager contains an appended PE payload located via magic bytes (0x5A45) and resolves APIs via PEB traversal and custom djb2-style hashing to perform reflective loading and C2 communication.
- Infrastructure analysis links the campaign to IP 46[.]149[.]71[.]230 (ports 80/443) and hosting under AS48282 / AS9123, and SEQRITE tracks the cluster as UNG0902 with detections such as Trojan.50169.SL.
MITRE Techniques
- [T1566.001 ] Spearphishing Attachment – Malicious ZIP delivered to targets containing a PDF-themed LNK lure used for initial access. (‘Victims receive ZIP file containing malicious PDF-themed LNK lure (employee bonus policy).’)
- [T1204.002 ] User Execution: Malicious File – Victims open the LNK believing it is a PDF, triggering execution. (‘User opens LNK file thinking it is a PDF, triggering execution.’)
- [T1059.001 ] PowerShell – LNK invokes PowerShell with hidden flags to download and run DUPERUNNER. (‘LNK launches PowerShell with -NoNI -nop -w hidden to download and execute DUPERUNNER from C2.’)
- [T1218.011 ] System Binary Proxy Execution / LOLBIN Execution – Legitimate system binaries (powershell.exe) are used to proxy execution of malicious components. (‘powershell.exe … to run completely in the background’)
- [T1105 ] Ingress Tool Transfer – Files are fetched from remote servers via Invoke-WebRequest (iwr) and saved to Temp (s.exe, fontawesome.woff). (‘PowerShell Invoke-WebRequest (iwr) downloads s.exe (DUPERUNNER) and later fontawesome.woff (AdaptixC2 stager).’)
- [T1036 ] Masquerading – Malicious artifacts masquerade as benign files (LNK as PDF, WOFF as font, DLL/PE appended to shellcode). (‘LNK posed as PDF, DLL posing as ZIP, WOFF posing as a font file.’)
- [T1027 ] Obfuscated/Encrypted File – AdaptixC2 uses packed shellcode appended behind magic bytes to hide payload. (‘AdaptixC2 uses packed shellcode appended behind magic bytes (EZ).’)
- [T1027.007 ] Dynamic API Resolution – AdaptixC2 resolves APIs at runtime using custom hashing and PEB traversal. (‘AdaptixC2 resolves APIs using djb2-style hashing and PEB traversal.’)
- [T1055.003 ] Thread Execution Hijacking – DUPERUNNER injects shellcode into legitimate processes (explorer.exe, notepad.exe, msedge.exe) using remote-thread injection. (‘DUPERUNNER injects shellcode into legitimate processes (explorer.exe, notepad.exe, msedge.exe).’)
- [T1620 ] Reflective Code Loading – The stager locates an appended PE via magic bytes and loads it reflectively into memory. (‘AdaptixC2 loads its payload from appended shellcode using reflective loading techniques.’)
- [T1082 ] System Information Discovery – DUPERUNNER enumerates system time, Temp directory, hostname and creates a victim GUID for profiling. (‘DUPERUNNER gathers hostname, domain, system time, Temp directory, creates victim GUID.’)
- [T1057 ] Process Discovery – The implant enumerates running processes to select injection targets using CreateToolHelp. (‘DUPERUNNER enumerates processes (explorer.exe, notepad.exe, msedge.exe) using CreateToolHelp API.’)
- [T1071.001 ] Application Layer Protocol: HTTP – Beaconing and downloads use HTTP GET/POST to communicate with C2 (46.149.71.230). (‘DUPERUNNER uses HTTP GET to download decoy and beacon from 46.149.71.230.’)
- [T1132 ] Data Encoding – Beacon data and command results are encoded before transmission. (‘Beacon results and communications encoded via internal routines.’)
- [T1095 ] Non-Application Layer Protocol – AdaptixC2 may use raw TCP or non-standard protocols for beaconing as implied by its design. (‘AdaptixC2 may use raw TCP for beaconing (implied from C2 design).’)
- [T1573 ] Encrypted Communication – C2 communications are protected by encryption in the AdaptixC2 beacon. (‘AdaptixC2 beacon uses encryption during C2 communications.’)
- [T1055 ] Process Injection – DUPERUNNER uses Remote-Thread Injection to execute the next-stage shellcode in target processes. (‘DUPERUNNER injects AdaptixC2 shellcode into legitimate processes via Remote Thread Injection.’)
- [T1113 / T1005 ] Local Data Collection – The beacon can retrieve system files and local data as instructed by the operator. (‘Beacon capable of retrieving system files as instructed by TA.’)
- [T1041 ] Exfiltration Over C2 Channel – Collected data and command outputs are exfiltrated to the /result C2 endpoint via POST. (‘Beacon sends encoded results/output to /result C2 endpoint via POST.’)
- [T1537 ] Data Exfiltration – Operation results in theft of system files and corporate data from targeted Russian environments. (‘Steals system data and files from Russian corporate environments.’)
Indicators of Compromise
- [IP Address ] Download and C2 host – 46[.]149[.]71[.]230 (staging of DUPERUNNER on port 80 and AdaptixC2 on port 443)
- [File Hash (SHA-256) ] Malware binaries and stages – 87db5cbd76e7adeb6932c4ae14f3d3bb736d631460d65e067fb2a0083b675399, d9e2b6341f6de5c95dd02cf3350c07cd2be3b0a78b82c073229396b6d4c8d3c1, and other 9 hashes
- [File Name ] Lure and staged payloads – Документ_1_О_размере_годовой_премии.pdf.lnk (malicious shortcut), fontawesome.woff (AdaptixC2 stager)
- [Archive / Lure ] Spear-phishing archive – Премия 2025.zip (contains PDF-themed decoy and malicious LNK)
- [URL / C2 Endpoint ] Beacon and exfiltration endpoint – http://46[.]149[.]71[.]230/result (beacon POST endpoint used to send results)
- [Autonomous System / Hosting ] Hosting infrastructure – AS48282 (VDSINA-AS), AS9123 (TIMEWEB-AS) used to host malicious infrastructure
- [Detection Name / Signature ] SEQRITE detections – Trojan.50169.SL, Loader.S38592683 (detections attributed to samples from this campaign)
Read more: https://www.seqrite.com/blog/9512-2/