Intellexa continues to operate despite public scrutiny and US sanctions, exploiting and procuring numerous zero-day vulnerabilities to deliver its Predator spyware and related tooling. Google GTIG documents sophisticated iOS and Chrome exploit chains (JSKit, V8/TheHole), detailed PREYHUNTER modules, delivery via one-time messaging links and malvertising, and provides IOCs and mitigations. #Intellexa #PREYHUNTER
Keypoints
- Intellexa remains active and profitable despite sanctions, continuing to sell surveillance tools including Predator to customers worldwide.
- GTIG links Intellexa to 15 unique zero-day vulnerabilities out of ~70 TAG-discovered zero-days since 2021, including RCE, sandbox escape, and LPE bugs across iOS, Android, Chrome/V8, and GPU drivers.
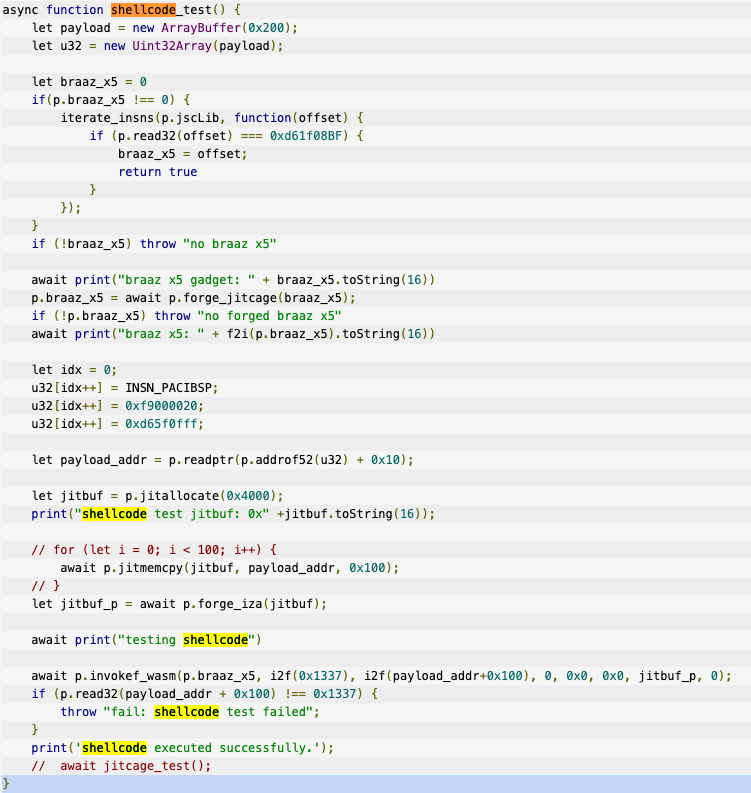
- Apple iOS exploit chains used JSKit (internally called “smack”) to achieve RCE, sandbox escape, kernel LPEs (CVE-2023-41991, CVE-2023-41992), and deploy a PREYHUNTER payload with helper/watcher modules.
- Chrome exploitation leveraged custom frameworks to leak TheHole object in V8 across multiple CVEs culminating in CVE-2025-6554 (patched in Chrome 138.0.7204.96); Intellexa both develops and purchases exploit chain components.
- PREYHUNTER’s helper and watcher modules provide spying capabilities (VOIP recording, keylogging, camera capture), environment checks to avoid detection, local IPC via /tmp/helper.sock, and artifacts revealing build paths and debug strings.
- Delivery methods include one-time links sent over end-to-end encrypted messaging apps and malicious advertising/fingerprinting campaigns; Google and partners disrupted ad accounts and added identified domains to Safe Browsing while issuing warnings to targeted accounts.
MITRE Techniques
- [T1203 ] Exploitation for Client Execution – Used to achieve arbitrary code execution via browser and rendering zero-days (RCE); (‘Intellexa accounts for 15 unique zero-days, including Remote Code Execution (RCE)…’)
- [T1068 ] Exploitation for Privilege Escalation – Kernel vulnerabilities and LPEs were exploited to break out of the sandbox and gain system privileges (e.g., CVE-2023-41991, CVE-2023-41992); (‘…breaking out of the Safari sandbox and executing an untrusted third stage payload as system by abusing the kernel vulnerabilities CVE-2023-41991 and CVE-2023-41992.’)
- [T1189 ] Drive-by Compromise (Watering Hole) – The same JSKit framework was observed in a watering hole campaign against Mongolian government websites showing use of web-based compromise; (‘…a campaign by Russian government-backed attackers using this exact same iOS exploit and JSKit framework in a watering hole attack against Mongolian government websites.’)
- [T1566.002 ] Phishing: Spearphishing Link – Initial delivery frequently used one-time links sent via end-to-end encrypted messaging apps to lure targets to exploit servers; (‘The primary delivery mechanism for Intellexa’s exploits remains one-time links sent to targets directly via end-to-end encrypted messaging applications.’)
- [T1056.001 ] Input Capture: Keylogging – PREYHUNTER helper module can run a keylogger to capture typed input on the infected device; (‘Running a keylogger’)
- [T1123 ] Audio Capture – The helper module records VOIP conversations and stores them on the device for exfiltration; (‘Recording VOIP conversations (stored in /private/var/tmp/l/voip_%lu_%u_PART.m4a)’)
- [T1125 ] Video Capture – The helper module captures pictures from the device camera as part of operator verification prior to deploying more advanced spyware; (‘Capturing pictures from the camera’)
Indicators of Compromise
- [File Hash ] PREYHUNTER payload file indicators – 85d8f504cadb55851a393a13a026f1833ed6db32cb07882415e029e709ae0750, e3314bcd085bd547d9b977351ab72a8b83093c47a73eb5502db4b98e0db42cac
- [YARA Rule ] Hunting strings and artifacts – “G_Hunting_PREYHUNTER_IOSStrings_1” YARA rule containing build paths and runtime strings for PREYHUNTER (includes ‘/Users/gitlab_ci_2/builds/jb’, ‘/private/var/tmp/l/voip_%lu_%u_PART.m4a’).
- [CVE ] Vulnerabilities exploited in campaigns – examples: CVE-2023-41993 (iOS WebKit RCE), CVE-2025-6554 (Chrome V8 type confusion) — many other CVEs listed in Table 1.
- [File Path / Artifact ] Local artifacts and IPC endpoints – /private/var/tmp/l/voip_%lu_%u_PART.m4a (VOIP recordings), /tmp/helper.sock (Unix socket used by helper module), and build path ‘/Users/gitlab_ci_2/builds/…/ios16.5-smackjs8-production/’
- [Debug/Strings ] Internal identifiers and debug traces – internal exploit names and strings such as “smack”, “exploit number 7”, and build/debug traces referenced in the binary artifacts.
Read more: https://cloud.google.com/blog/topics/threat-intelligence/intellexa-zero-day-exploits-continue/