A multi-stage ClickFix social‑engineering campaign uses mshta to launch PowerShell which reflectively loads .NET assemblies that AES‑decrypt an embedded PNG and extract Donut‑packed shellcode via a custom steganography routine, ultimately delivering infostealers such as LummaC2 and Rhadamanthys. #LummaC2 #Rhadamanthys
Keypoints
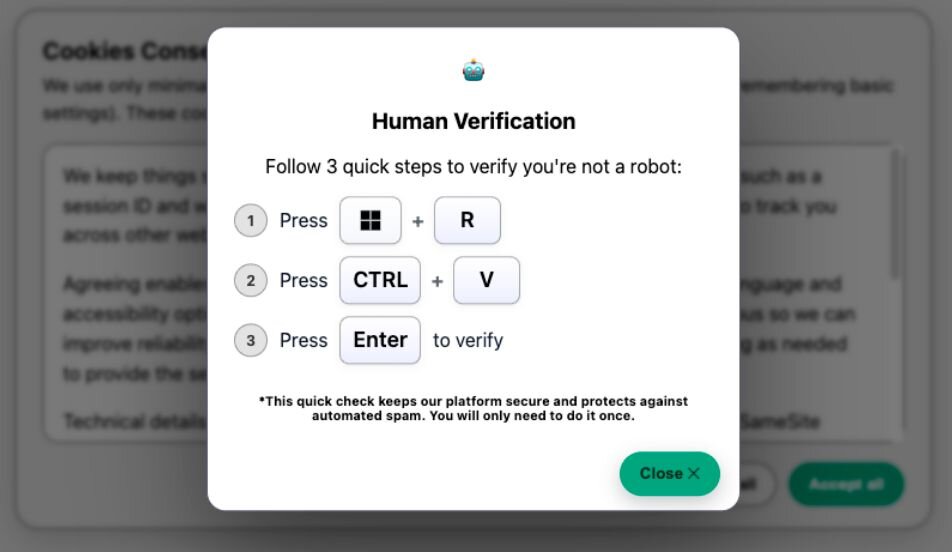
- The campaign uses ClickFix lures (robot check and fake Windows Update pages) that prompt victims to open the Run box (Win+R) and paste a malicious mshta command copied to the clipboard.
- mshta executes a remote JScript which launches PowerShell that contains junk code and then decrypts and reflectively loads a .NET assembly in memory.
- The 3rd‑stage .NET assembly AES‑decrypts an embedded PNG resource and runs a custom steganography algorithm to reconstruct shellcode from the image’s pixel ‘R’ channel.
- Extracted shellcode is Donut‑packed, then injected into explorer.exe via a dynamically compiled/reflectively loaded .NET injector using VirtualAllocEx/WriteProcessMemory/CreateRemoteThread.
- Final payloads observed include LummaC2 and, in a separate cluster using a Windows Update lure, Rhadamanthys stealer; C2 infrastructure and multiple domains/IPs were identified and tracked.
- The lure sites employ runtime encryption of JavaScript (ENC/KEY_HEX) and Blob URL injection to evade static detection, and some lure source contains Russian comments and logging to enumerate victims.
- Recommended mitigations include disabling the Windows Run box via registry/GPO, security awareness training to avoid ClickFix behavior, and EDR monitoring for suspicious process lineage.
MITRE Techniques
- [T1218.005 ] mshta (Signed Binary Proxy Execution) – Used to execute a remote JScript that begins the execution chain (‘mshta hXXp://81.0x5a.29[.]64/ebc/rps.gz’).
- [T1059.001 ] PowerShell – Remote PowerShell code is executed in memory and used to decrypt and reflectively load a .NET assembly (‘This will run PowerShell code, hosted on the URL hXXp://corezea[.]com/ebc’).
- [T1204 ] User Execution – Social‑engineering lure tricks users into pasting and running a command via the Run dialog (Win+R), prompting manual execution (‘victims are instructed to press Win+R to open the Windows Run box, followed by CTRL+V to paste a command’).
- [T1027.003 ] Steganography (Obfuscated Files/Information) – A custom steganographic algorithm encodes shellcode directly into PNG pixel channels and decodes it in memory (‘the malicious code is encoded directly within the pixel data of PNG images’).
- [T1105 ] Ingress Tool Transfer – Stages and assemblies are downloaded from remote URLs/IPs during execution (e.g., stage hosting and PowerShell download from remote hosts: ‘Stage 2 URLs: hXXp://securitysettings[.]live’).
- [T1055 ] Process Injection – Extracted shellcode is injected into explorer.exe using standard Win32 APIs (VirtualAllocEx, WriteProcessMemory, CreateRemoteThread) to execute the payload (‘inject shellcode into explorer.exe’).
Indicators of Compromise
- [Domain ] ClickFix lure and C2 domains used in the campaign – xcvcxoipoeww[.]site, securitysettings[.]live, and other domains such as hypudyk[.]shop and squatje[.]su (and several more listed in the article).
- [IP Address ] Hosting and staging infrastructure – 141.98.80[.]175 (multiple stage URLs and domains pointing to this IP), 81.90.29[.]64 (initial mshta host example).
- [URL ] First‑stage mshta and PowerShell URLs – hXXp://141.98.80[.]175/tick.odd, hXXp://81.90.29[.]64/ebc/rps.gz (examples of mshta stage URLs used to deliver subsequent stages).
- [File/Resource Name ] Embedded resource and payload artifacts – manifest resource cd8302542f494f4d8fbcb2d21425b316 (AES‑encrypted PNG resource), rps.gz (initial hosted payload example).
- [Payload/C2 ] Observed final payload families and artifacts – LummaC2 samples (config extracted by Huntress) and Rhadamanthys stealer (observed in Windows Update lure clusters).
Read more: https://www.huntress.com/blog/clickfix-malware-buried-in-images