Researchers identified a new Rust-based ransomware family named 01flip that targets Windows and Linux systems in the Asia-Pacific region and is tracked as part of cluster CL-CRI-1036. The campaign involved manual activity, use of Sliver implants, exploitation attempts against CVE-2019-11580, and an alleged data leak posted to a dark web forum. #01flip #CL-CRI-1036
Keypoints
- 01flip is a newly observed ransomware family fully written in Rust that supports multi-platform architectures (Windows and Linux).
- Initial access activity included attempts to exploit CVE-2019-11580 against internet-facing applications prior to deployment.
- Attackers deployed Sliver implants (including a TCP Pivot profile) for command-and-control and lateral movement across Linux hosts.
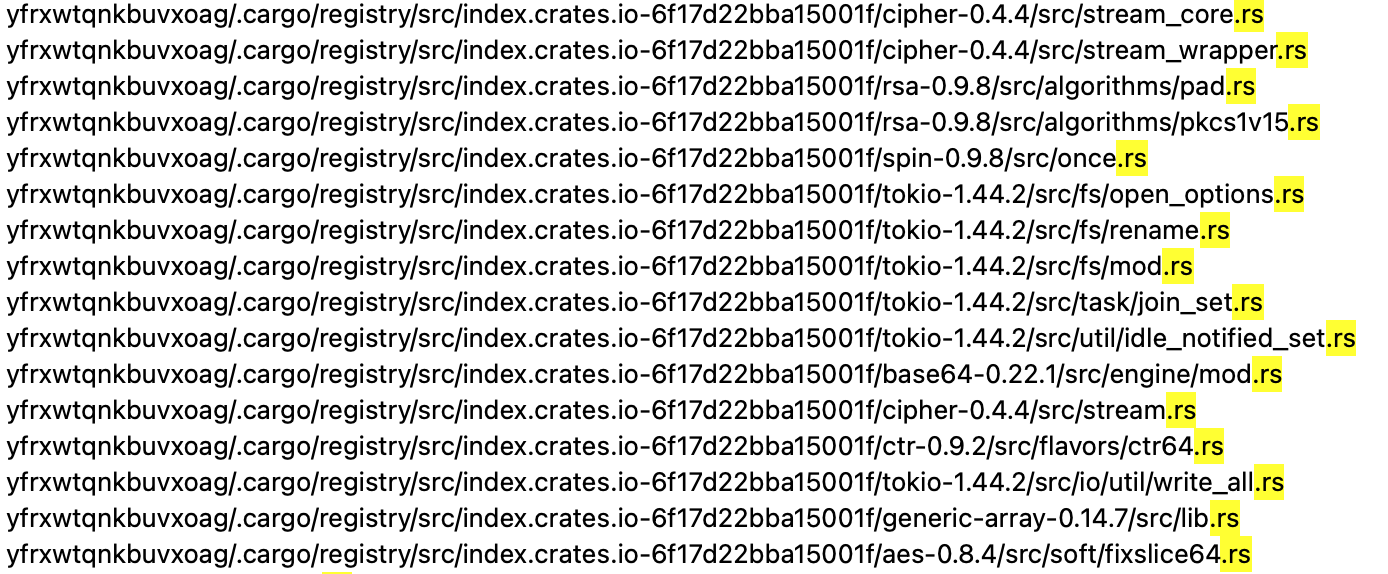
- 01flip encrypts files using AES-128-CBC with a session key protected by an embedded RSA-2048 public key and renames files with a .01flip extension.
- Ransomware implements defense-evasion measures such as low-level system calls, encoded strings decoded at runtime, and a simple anti-sandbox filename check.
- After encryption the malware attempts indicator removal by zeroing/overwriting and deleting its binary on both Windows and Linux.
- An alleged data leak linked to the activity was posted to a dark web forum shortly after the ransomware deployment; victims may include organizations in the Philippines, Taiwan, and other Southeast Asia critical infrastructure.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – Attackers attempted exploits against an internet-facing application (CVE-2019-11580) to gain initial access. Quote: ‘attackers had been attempting exploits targeting older vulnerabilities such as CVE-2019-11580 against a victim’s internet-facing applications since early April 2025.’
- [T1105 ] Ingress Tool Transfer – Adversary downloaded and installed Sliver implants onto compromised hosts to deliver tooling. Quote: ‘they successfully deployed a Linux version of Sliver, a publicly available cross-platform adversary emulation framework written in Go.’
- [T1021 ] Remote Services (Lateral Movement) – Used Sliver implants (TCP Pivot) to move laterally between Linux machines and spread the ransomware. Quote: ‘successfully performed lateral movement to another Linux machine by downloading another Sliver implant, which was a TCP Pivot profiled implant.’
- [T1003 ] Credential Dumping – Threat actors likely performed credential dumping to support rapid distribution and lateral movement across the network. Quote: ‘it is highly likely that the attackers conducted the following activities, possibly through Sliver and its modules: Credential dumping.’
- [T1071 ] Application Layer Protocol (Command and Control) – Sliver beacon and TCP pivot implants provided C2 communications for the campaign. Quote: ‘Linux Sliver Beacon, TCP Pivot as C2.’
- [T1486 ] Data Encrypted for Impact – 01flip encrypts files using AES-128-CBC and protects the session key with an embedded RSA-2048 public key, appending a .01flip extension to files. Quote: ‘Encrypting files using AES-128-CBC and RSA-2048’ and ‘renaming files… .01flip.’
- [T1070 ] Indicator Removal on Host – After encryption the ransomware attempts to overwrite and delete its binary to remove traces. Quote: ‘fsutil file setZeroData offset=0 length=4194303 ${self_name} … Del /f /q ${self_name}’ and ‘dd if=/dev/urandom of=${self_name} bs=1M count=4 … rm ${self_name}.’
- [T1497 ] Virtualization/Sandbox Evasion – The sample implements a filename-based guardrail that alters behavior in sandboxed environments (checks for ’01flip’). Quote: ‘if the sample’s filename contains the string 01flip, the ransomware proceeds to indicator removal without performing file encryption.’
- [T1027 ] Obfuscated Files or Information – User-defined strings (ransom note, filenames, extension list, RSA key) are encoded in the binary and decoded at runtime. Quote: ‘Most of the user-defined strings in the ransomware code are encoded. These strings are decoded at runtime.’
Indicators of Compromise
- [File Hash – SHA-256] Malicious binaries associated with the campaign – 6aad1c36ab9c7c44350ebe3a17178b4fd93c2aa296e2af212ab28d711c0889a3 (Windows 01flip), e5834b7bdd70ec904470d541713e38fe933e96a4e49f80dbfb25148d9674f957 (Linux 01flip), and ba41f0c7ea36cefe7bc9827b3cf27308362a4d07a8c97109704df5d209bce191 (Linux Sliver beacon).
- [Email Address] Ransom contact found in ransom note – 01Flip@proton[.]me.
- [File Names / Extensions] Ransom note and encrypted file extension – RECOVER-YOUR-FILE.TXT (ransom note), .01flip (appended encrypted-file extension).
- [Vulnerability / CVE] Exploited public-facing vulnerability used for initial access – CVE-2019-11580 (Atlassian Crowd Server RCE) referenced as an attempted exploitation vector.
- [Software / Service] Compromised or targeted services – Zimbra Server (alleged compromise reported by a victim) and Sliver (adversary C2/implant software observed).
Read more: https://unit42.paloaltonetworks.com/new-ransomware-01flip-written-in-rust/