In late November 2025 a malicious Visual Studio Code extension named “prettier-vscode-plus” was published to the official Marketplace and used as a supply-chain entry point to deliver a multi-stage attack targeting developers. The chain deployed an Anivia loader (AES-encrypted in-memory decryption and process hollowing into vbc.exe) which dropped the OctoRAT remote access toolkit with extensive data-theft, persistence, privilege‑escalation and C2 capabilities. #Anivia #OctoRAT
Keypoints
- A fake VSCode extension “prettier-vscode-plus” was published to the official Marketplace and removed within four hours after minimal installs.
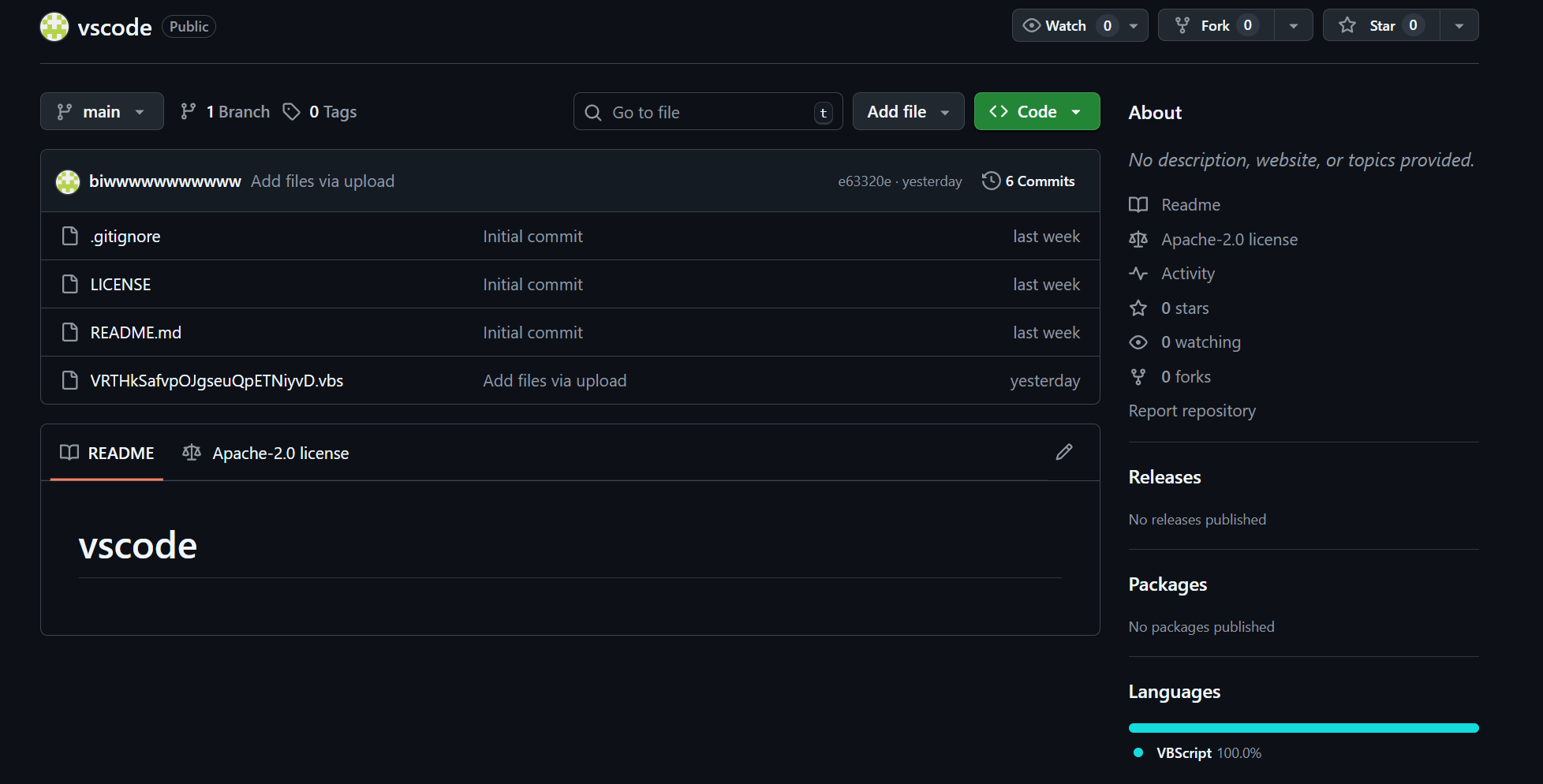
- The extension and a GitHub repository (“vscode” under handle biwwwwwwwwwww) hosted VBScript droppers that unpacked an embedded PowerShell stage and an AES-encrypted C# Anivia loader.
- Anivia decrypts an embedded PE in memory and uses process hollowing into C:WindowsMicrosoft.NETFrameworkv4.0.30319vbc.exe to execute the OctoRAT payload.
- OctoRAT provides over 70 commands including browser credential and wallet theft, keylogging, screen capture/remote desktop, persistence via scheduled task, UAC bypass, and reverse proxy capabilities.
- Threat actor operational security included active payload rotation (frequent GitHub uploads/deletes) and infrastructure reuse such as a distinctive OctoRAT Center web panel and TLS certificate fingerprint across many hosts.
- Defender detection opportunities include monitoring for installs of prettier-vscode-plus, VBS→PowerShell AES chains, vbc.exe process hollowing, and OctoRAT Center HTML title fingerprints.
- Confirmed IOCs include file hashes for the VBS, PowerShell, loader, and RAT stages, plus exposed C2 panels discovered via internet-wide scanning.
MITRE Techniques
- [T1195.002 ] Supply Chain Compromise – Used to publish a malicious VSCode extension that delivered the initial payload ( ‘malicious extension “prettier‑vscode‑plus” appeared on the official Visual Studio Code Marketplace’ )
- [T1059.001 ] PowerShell – Embedded PowerShell performs Base64/AES decryption and executes the decrypted script in memory ( ‘Execute the decrypted script directly in memory using Invoke-Expression’ )
- [T1059.005 ] Visual Basic – Initial dropper is a VBScript that creates COM objects, writes the PowerShell payload to disk, and executes it hidden ( ‘initial infection vector relies on a VBScript dropper that initializes two Windows COM objects’ )
- [T1053.005 ] Scheduled Task – Persistence via Windows Task Scheduler with a task named “WindowsUpdate” scheduled to run every minute ( ‘The scheduled task is named “WindowsUpdate” … execution every single minute’ )
- [T1548.002 ] Bypass UAC – FodHelper UAC bypass implemented by creating ms-settings registry keys to auto-elevate the malware ( ‘creates a registry key at HKCUSoftwareClassesms-settingsShellOpencommand’ )
- [T1055.012 ] Process Hollowing – Loader injects decrypted PE into a legitimate Microsoft-signed binary (vbc.exe) to evade detection ( ‘injects its payload into the legitimate Visual Basic Compiler … vbc.exe’ )
- [T1562.004 ] Disable Windows Firewall – Malware can disable the firewall via netsh to reduce host defenses ( ‘disable_firewall: Uses netsh advfirewall set allprofiles state off’ )
- [T1564.001 ] Hidden Files and Directories – Option to hide malware binary by setting hidden and system attributes ( ‘meltEnabled controls whether the malware hides its executable file by setting hidden and system filesystem attributes’ )
- [T1555.003 ] Credentials from Web Browsers – Targets browser SQLite databases to extract saved passwords, cookies, and autofill data ( ‘targets SQLite databases from all major browsers’ )
- [T1555 ] Credentials from Password Stores – Loads SQLite libraries to access browser-stored credentials and other password stores ( ‘SQLite loading is strategically important: modern web browsers store sensitive user data in SQLite databases’ )
- [T1082 ] System Information Discovery – Collects host reconnaissance data in a JSON packet ( ‘transmits a JSON-formatted reconnaissance packet containing: computer hostname, current username, Windows version’ )
- [T1057 ] Process Discovery – Implements commands to list and manage running processes ( ‘get_processesList all running processes’ )
- [T1083 ] File and Directory Discovery – Enumerates directories and wallet application folders for data theft ( ‘list_dirList directory contents’ )
- [T1056.001 ] Keylogging – Supports keystroke capture via start_keylogger ( ‘start_keyloggerBegin keystroke capture’ )
- [T1115 ] Clipboard Data – Monitors and exfiltrates clipboard contents ( ‘start_clipboard_monitorBegin clipboard monitoring’ )
- [T1113 ] Screen Capture – Remote desktop streaming and screenshot capture ( ‘start_desktopBegin screen capture streaming’ )
- [T1071 ] Application Layer Protocol – JSON over HTTP(s) used for C2 reconnaissance and command exchange ( ‘transmits a JSON-formatted reconnaissance packet’ )
- [T1041 ] Exfiltration Over C2 Channel – Stolen browser/wallet data is uploaded to attacker-controlled servers over the C2 channel ( ‘Immediately after extraction, the malware uploads this data to the attacker’s server’ )
Indicators of Compromise
- [File Hash ] Main stage binaries and scripts – VBS: f4e5b1407f8a66f7563d3fb9cf53bae2dc3b1f1b93058236e68ab2bd8b42be9d, RAT: 360e6f2288b6c8364159e80330b9af83f2d561929d206bc1e1e5f1585432b28f, and 2 more hashes
- [IP Address ] Confirmed C2/control panels – 51.178.245[.]127:8000 (OctoRAT Center web panel), 178.16.55[.]109 (Railnet host observed serving OctoRAT C2)
- [Repository/Extension ] Supply-chain artifacts – GitHub repo ‘biwwwwwwwwwww/vscode’ (malicious VBScript uploads/deletes), VSCode extension ‘prettier-vscode-plus’ (publisher ‘publishingsofficial’)
- [File Name / Path ] Dropper and target executables – example VBScript names RpnBmNFeHtFeIAJpKRKNUBtKS.vbs and mBDDLJmBMDgxPkaTbPhMEPoGE.vbs; injection target C:WindowsMicrosoft.NETFrameworkv4.0.30319vbc.exe
- [TLS Certificate Fingerprint ] Certificate reuse across infrastructure – SHA-256: 279F7AB5979E82CAA75AC4D7923EE1F3D76FE8C3EDC6CC124D619A8F7441EB5E (seen across ~93 servers)
- [Mutex ] Process mutex identifying OctoRAT – OctoRAT_Client_Mutex_{B4E5F6A7-8C9D-0E1F-2A3B-4C5D6E7F8A9B}
- [Registry Key ] UAC bypass artifact – HKCUSoftwareClassesms-settingsShellOpencommand (used by FodHelper bypass)
Read more: https://hunt.io/blog/malicious-vscode-extension-anivia-octorat-attack-chain