Researchers at Koi Security discovered two malicious Visual Studio Code extensions (Bitcoin Black and Codo AI) that deliver a DLL-hijacking infostealer via the legitimate Lightshot binary to capture screenshots, clipboard data, WiFi credentials, installed programs, and browser sessions. The attacker iterated delivery methods across versions (PowerShell with multiple extraction fallbacks to a streamlined curl-based batch downloader), used a memorable mutex (COOL_SCREENSHOT_MUTEX_YARRR), and phoned home to domains such as syn1112223334445556667778889990.org #BitcoinBlack #CodoAI
Keypoints
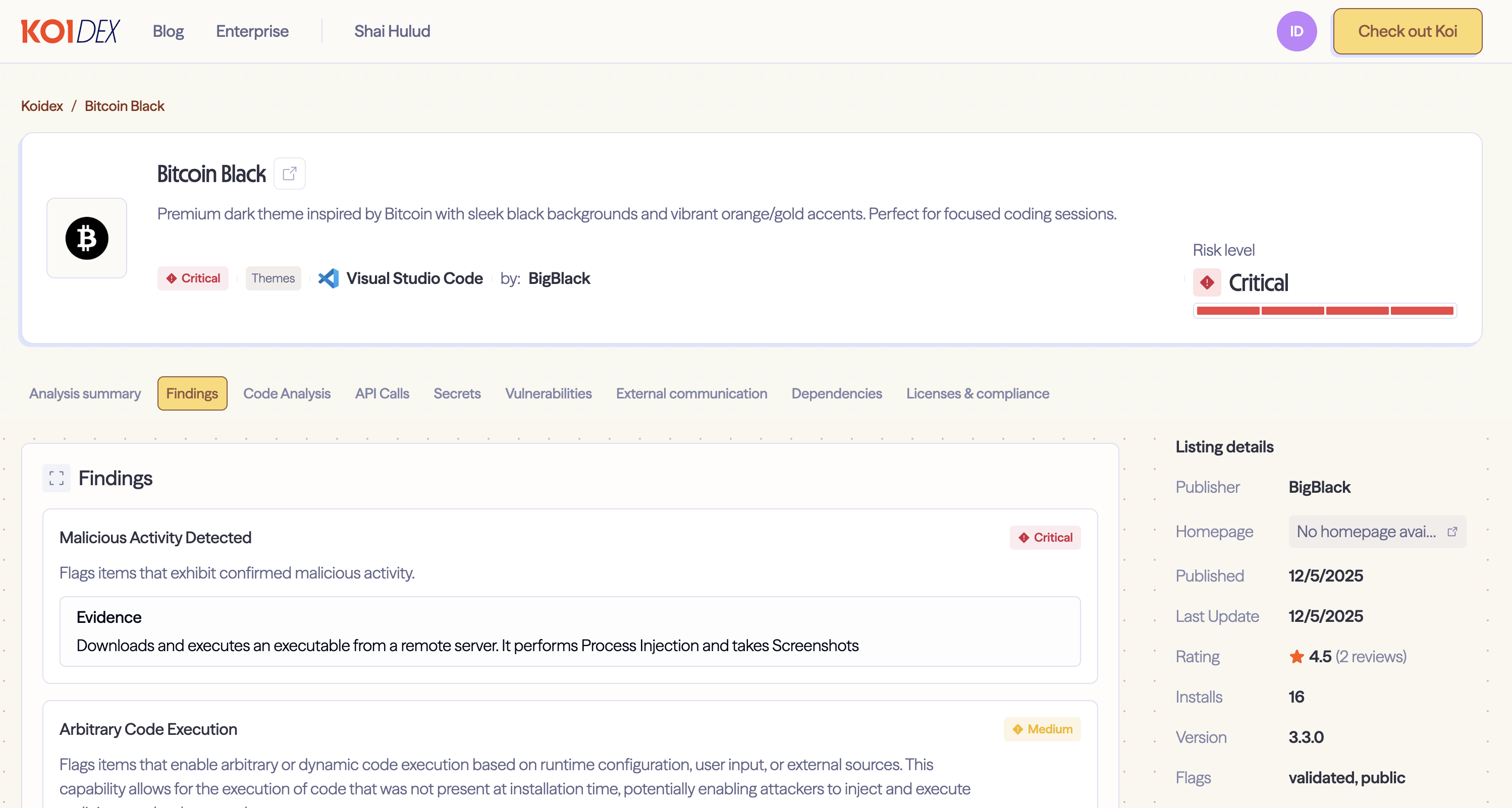
- Two malicious VS Code extensions—Bitcoin Black (a fake theme) and Codo AI (a functional AI assistant)—were used as lures to distribute an infostealer.
- Both extensions deliver a legitimate Lightshot.exe paired with a malicious Lightshot.dll using DLL hijacking so the signed binary loads the attacker’s payload.
- The infostealer harvests screenshots, clipboard contents, stored WiFi credentials, installed programs, running processes, and detailed system information, and it hijacks browser sessions.
- The campaign evolved from a complex PowerShell-based downloader with multiple extraction fallbacks (version 2.5.0) to a streamlined curl-based batch downloader with hidden execution and marker-file persistence (version 3.3.0).
- Command-and-control infrastructure includes syn1112223334445556667778889990.org and server09.mentality.cloud:40207, with payload URLs hosting Lightshot.exe/Lightshot.dll/Lightshot.zip.
- Reliable detection artifacts include the mutex COOL_SCREENSHOT_MUTEX_YARRR, extension identifiers (bigblack.bitcoin-black, bigblack.codo-ai), and file-system staging locations under %TEMP% and %APPDATA%.
MITRE Techniques
- [T1539 ] Steal Web Session Cookie – Used to exfiltrate browser cookies/session data via headless browser execution flags and remote access (‘T1539 (Steal Web Session Cookie)’)
- [T1185 ] Browser Session Hijacking – Achieved by launching Chrome/Edge with hidden position/size and incognito to harvest sessions (‘T1185 (Browser Session Hijacking)’)
- [T1574.001 ] DLL Search Order Hijacking – The attacker places a malicious DLL alongside the real Lightshot.exe so the legitimate binary loads the malicious library (‘This is DLL hijacking (MITRE T1574.001).’)
Indicators of Compromise
- [Extension ] Malicious VS Code extensions – bigblack.bitcoin-black, bigblack.codo-ai
- [Domain ] Primary C2 and control domains – syn1112223334445556667778889990.org, server09.mentality.cloud:40207
- [Payload URLs ] Hosted payloads on C2 – http://syn1112223334445556667778889990.org/Lightshot.exe, http://syn1112223334445556667778889990.org/Lightshot.dll, and other 1 items
- [File paths ] Malware installation and staging directories – %TEMP%Lightshot, %APPDATA%LocalEvelyn, and other 5 items
- [File names ] Deployed binaries and markers – Lightshot.exe, Lightshot.dll, .done marker
- [File hashes ] Known sample hashes – Lightshot.dll: 369479bd9a248c9448705c222d81ff1a0143343a138fc38fc0ea00f54fcc1598, Lightshot.exe: 0b899508777d7ed5159e2a99a5eff60c54d0724493df3d630525b837fa43aa51
- [Mutex ] Execution mutex used by the malware – COOL_SCREENSHOT_MUTEX_YARRR
- [Publisher ] Marketplace publisher identifier – BigBlack
Read more: https://www.koi.ai/blog/the-vs-code-malware-that-captures-your-screen