Attackers poisoned search results to surface malicious ChatGPT and Grok conversations that instruct macOS users to copy-paste a Terminal one-liner which downloads and deploys an AMOS stealer. The campaign abuses platform and format trust to harvest credentials, escalate to root, persist via a LaunchDaemon, and exfiltrate wallet, browser, and keychain data. #AMOS #macOS
Keypoints
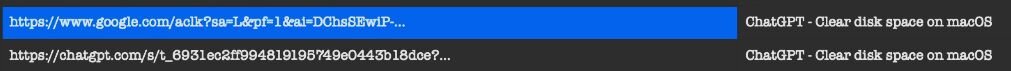
- Attackers used SEO/AI-poisoning to place malicious ChatGPT and Grok conversations at the top of common macOS troubleshooting searches (e.g., “Clear disk space on macOS”).
- Victims copy-pasted a supplied Terminal command which decoded a base64 URL, fetched a loader, and began a multi-stage AMOS stealer deployment without triggering macOS warnings.
- The initial loader prompted for a “System Password,” validated it silently via dscl-authonly, saved the password to /tmp/.pass, and piped it into sudo -S to gain root privileges.
- AMOS deployed a native Mach-O stealer (.helper) in the user’s home directory, trojanized apps (Ledger Wallet, Trezor Suite) to harvest seed phrases, and staged harvested data in /tmp/out.zip for exfiltration.
- Persistence was achieved by installing a LaunchDaemon (/Library/LaunchDaemons/com.finder.helper.plist) that runs an AppleScript watchdog to relaunch the hidden .helper under the GUI user every second.
- Anti-analysis and operational tradecraft included anti-VM checks, ad-hoc signing of payloads, hiding files with dot-prefixed names, and using legitimate platforms (chatgpt.com, grok.com) to build trust.
- Detection challenges: no malicious binary download prompts or Gatekeeper overrides were required—detection should focus on behavioral anomalies like dscl-authonly use, osascript credential prompts, and hidden executables.
MITRE Techniques
- [T1598.004 ] Search Engine Optimization (SEO) – Attackers poisoned search results so malicious AI conversations appeared as top answers (‘Google surfaced two highly ranked results … one directing the end user to a ChatGPT conversation and the other to a Grok conversation’).
- [T1204 ] User Execution – Victims were socially engineered to copy-paste and execute a Terminal command from a trusted AI conversation (‘the victim … executed the provided command’).
- [T1059.004 ] Unix Shell – The initial one-liner used base64 decoding, curl, and bash to fetch and run the first-stage loader (‘the base64-encoded string in the Terminal command decoded to a URL hosting a malicious bash script’).
- [T1059.005 ] AppleScript – An AppleScript-based loader/watchdog (.agent, update) was used to relaunch the payload in the user GUI session and persist execution (‘an AppleScript called ‘update’ … the .agent file … an AppleScript-based watchdog loop’).
- [T1543 ] Create or Modify System Process – The malware installed a LaunchDaemon to achieve persistence across reboots (‘/Library/LaunchDaemons/com.finder.helper.plist’ that runs the .agent script every reboot’).
- [T1497 ] Virtualization/Sandbox Evasion – The loader included anti-VM logic to avoid executing inside virtualized environments (‘it will verify that it is not running in a virtual machine and instead will run anti-VM logic’).
- [T1033 ] System Owner/User Discovery – The watchdog loop queries /dev/console to determine which GUI user is logged in and relaunch the payload under that user (‘Every second, the script checks which user is currently logged into the GUI session by querying /dev/console’).
- [T1056 ] Input Capture – The loader solicited the user’s “System Password” via a fake prompt and captured it to /tmp/.pass for later use (‘the loader … requests the user’s credentials by simply asking for the “System Password” … the script writes it in plaintext to a hidden file in the /tmp directory, called /tmp/.pass’).
- [T1041 ] Exfiltration Over C2 Channel – Harvested data was packaged (e.g., /tmp/out.zip) and transmitted to attacker-controlled servers/C2 (‘After collecting all the data, the attacker will stage the data in /tmp/out.zip before exfiltrating it to their C2 server’).
Indicators of Compromise
- [File name ] Persistent and hidden artifacts – com.finder.helper.plist, .helper, and /tmp/.pass
- [SHA256 hash ] Notable payload hashes – id.helper: ab60bb9c33ccf3f2f9553447babb902cdd9a85abce743c97ad02cbc1506bf9eb, agente: e1ca6181898b497728a14a5271ce0d5d05629ea4e80bb745c91f1ae648eb5e11 (and 3 more hashes listed)
- [Domain/URL ] Delivery and C2 infrastructure – hxxps://putuartana[.]com/cleangpt (base64-decoded loader URL), hxxps://wbehub[.]org, hxxps://sanchang[.]org
- [IP address ] Host-level infrastructure – 45.94.47[.]205 (Gate), 45.94.47[.]186 (C2)
- [Application name ] Trojanzied applications targeted/created – Ledger Wallet.app (trojanised), Trezor Suite (trojanised)
Read more: https://www.huntress.com/blog/amos-stealer-chatgpt-grok-ai-trust