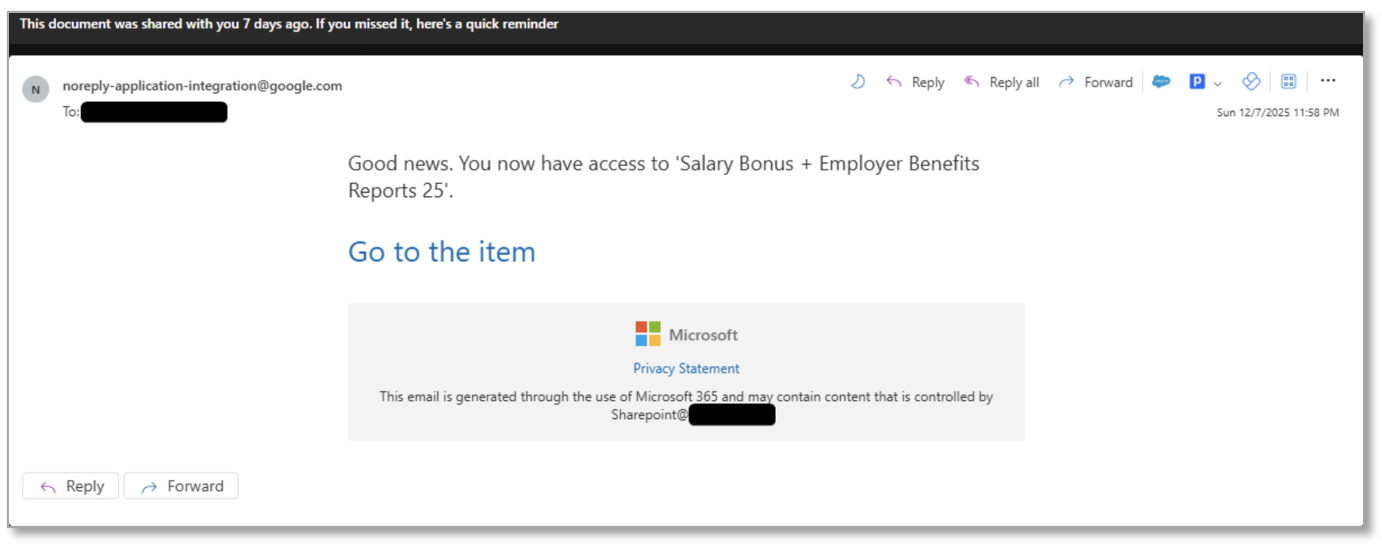
Proofpoint observed multiple state-aligned and financially motivated threat clusters abusing the OAuth 2.0 device authorization grant flow and social-engineering lures (embedded URLs and QR codes) to trick users into approving malicious applications and grant attackers access to Microsoft 365 accounts. These campaigns leveraged tools and kits such as SquarePhish2 and Graphish…
Category: Threat Research
CYFIRMA analyzed a targeted “quishing” campaign that uses payroll-themed emails with embedded QR codes to redirect victims to obfuscated, per-target phishing pages that auto-fill email addresses and harvest passwords. The campaign relied on randomized domains, encrypted JavaScript, fake CAPTCHA interactions, and rotating collection endpoints to evade detection and complicate forensics. #quishing #CYFIRMA

ClickFix social-engineering pages on compromised websites led victims to download and run a batch that installed NetSupport Manager (NetSupport RAT), which connected to a C2 and delivered a sideloaded StealC V2 infostealer. Stolen credentials harvested by StealC appear to have been used to access a Fortinet VPN and enable a subsequent Qilin ransomware deployment. #StealC_V2 #Qilin

In November 2025, AhnLab’s report summarizes confirmed counts of affected systems, DLS-based ransomware statistics, and notable incidents in Korea and abroad, with data collected via AhnLab TIP and ATIP. The report highlights active campaigns from established and emerging ransomware groups and provides trends by country, industry, and DLS/detection statistics. #Clop #Akira…

pathfinding.cloud is an open-source knowledge base that documents over 60 AWS IAM privilege escalation paths with prerequisites, exploitation steps, remediation, and tooling coverage. It standardizes each path with unique IDs and machine-readable YAML so security teams and tool authors can identify detection gaps and contribute fixes. #pathfinding.cloud #AWS

A coordinated YouTube Ghost Network campaign used compromised accounts to distribute obfuscated Node.js malware (GachiLoader) that retrieves or drops a second-stage loader (Kidkadi) which employs a novel PE injection method abusing Vectored Exception Handling to load malicious payloads such as the Rhadamanthys infostealer. Check Point Research released a Node.js Tracer to defeat anti-analysis checks and reproduced the injection technique (Vectored Overloading) as a PoC for researchers. #GachiLoader #Rhadamanthys
ReversingLabs uncovered a NuGet supply-chain campaign (July–October 2025) involving 14 malicious packages that impersonated legitimate crypto libraries to steal wallet secrets, OAuth credentials, or redirect funds. The packages used homoglyphs, version bumping, inflated download counts and hidden functions (e.g., Shuffle, MapAddress) to exfiltrate data to hxxps://solananetworkinstance[.]info/api/gads or overwrite transaction destinations. #Netherеum.All #NuGet

Operation ForumTroll conducted targeted phishing against Russian academics in October 2025 using a spoofed e-library domain to deliver a PowerShell-based downloader and an OLLVM-obfuscated DLL loader. The final payload deployed the commercial Tuoni framework and used COM Hijacking for persistence, with C2 infrastructure on fastly.net. #ForumTroll #Tuoni

Zscaler ThreatLabz attributes a spear-phishing campaign targeting a Colombian government agency to the BlindEagle actor, which used a compromised internal email account, an SVG-smuggled fake judicial portal, nested JavaScript and PowerShell, steganography, the Caminho downloader, and DCRAT as the final RAT. The attack chain involved in-memory execution, Discord-hosted artifacts, process hollowing, and an AES-encrypted DCRAT configuration tied to a certificate-based C2 authentication. #BlindEagle #DCRAT
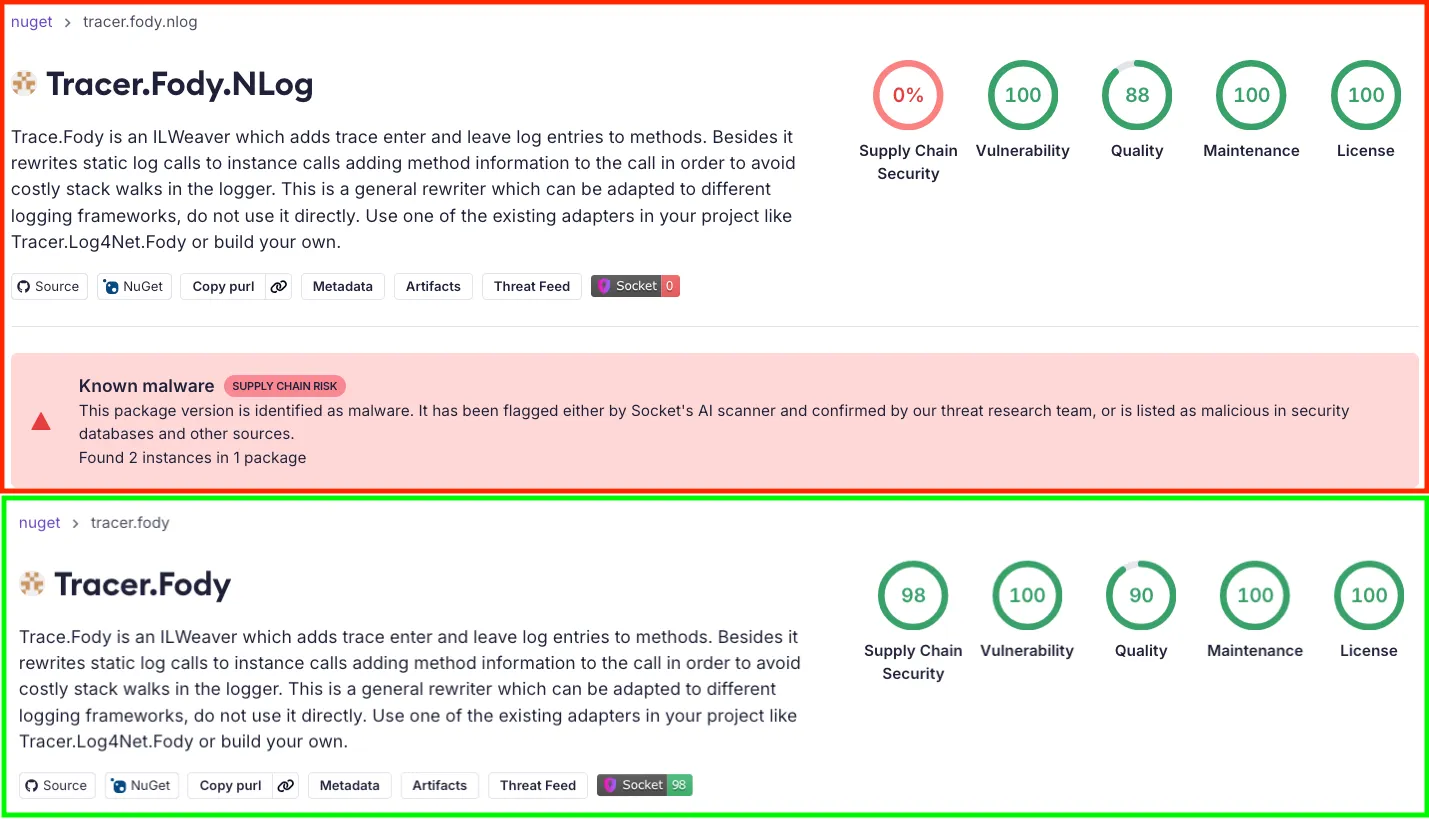
Socket Threat Research Team discovered a malicious NuGet package, Tracer.Fody.NLog, that typosquats the legitimate Tracer.Fody library and contains an embedded Tracer.Fody.dll which scans %APPDATA% for Stratis *.wallet.json files and exfiltrates wallet data and passwords. The package has been live on NuGet since 2020 with roughly 2,000 downloads, employs homoglyphs and an impersonating publisher alias (csnemess), and sends stolen data to 176[.]113[.]82[.]163:4444. #Tracer.Fody.NLog #Stratis

Check Point Research attributes a sustained espionage campaign to the Chinese-aligned cluster Ink Dragon that exploits ASP.NET ViewState deserialization and ToolShell SharePoint vulnerabilities to gain initial access and then deploys ShadowPad IIS listener modules and FinalDraft implants to build a distributed relay and cloud-backed C2 fabric. The operator harvests credentials (LSASS dumps, IIS worker accounts), uses RDP/SMB lateral movement, DLL sideloading, debugger-based loaders, scheduled tasks/services for persistence, and turns victims into active C2 relay nodes. #InkDragon #ShadowPad
This article analyzes RansomHouse, a RaaS operation run by the group tracked as Jolly Scorpius, detailing its attack chain, tooling (MrAgent and Mario), and the scope of its operations. It highlights an upgrade in Mario’s encryption from a single-pass linear method to a two-stage, chunked process using primary and secondary keys…
Parked and lookalike domains are increasingly weaponized via “direct search” parking and complex traffic distribution systems (TDS) to funnel real users to scams, scareware, spyware, and malware while presenting benign pages to scanners. The report details three distinct domain portfolio actors and examples of delivered threats, including infections by Tedy and typosquats targeting Scotiabank users. #Tedy #Scotiabank
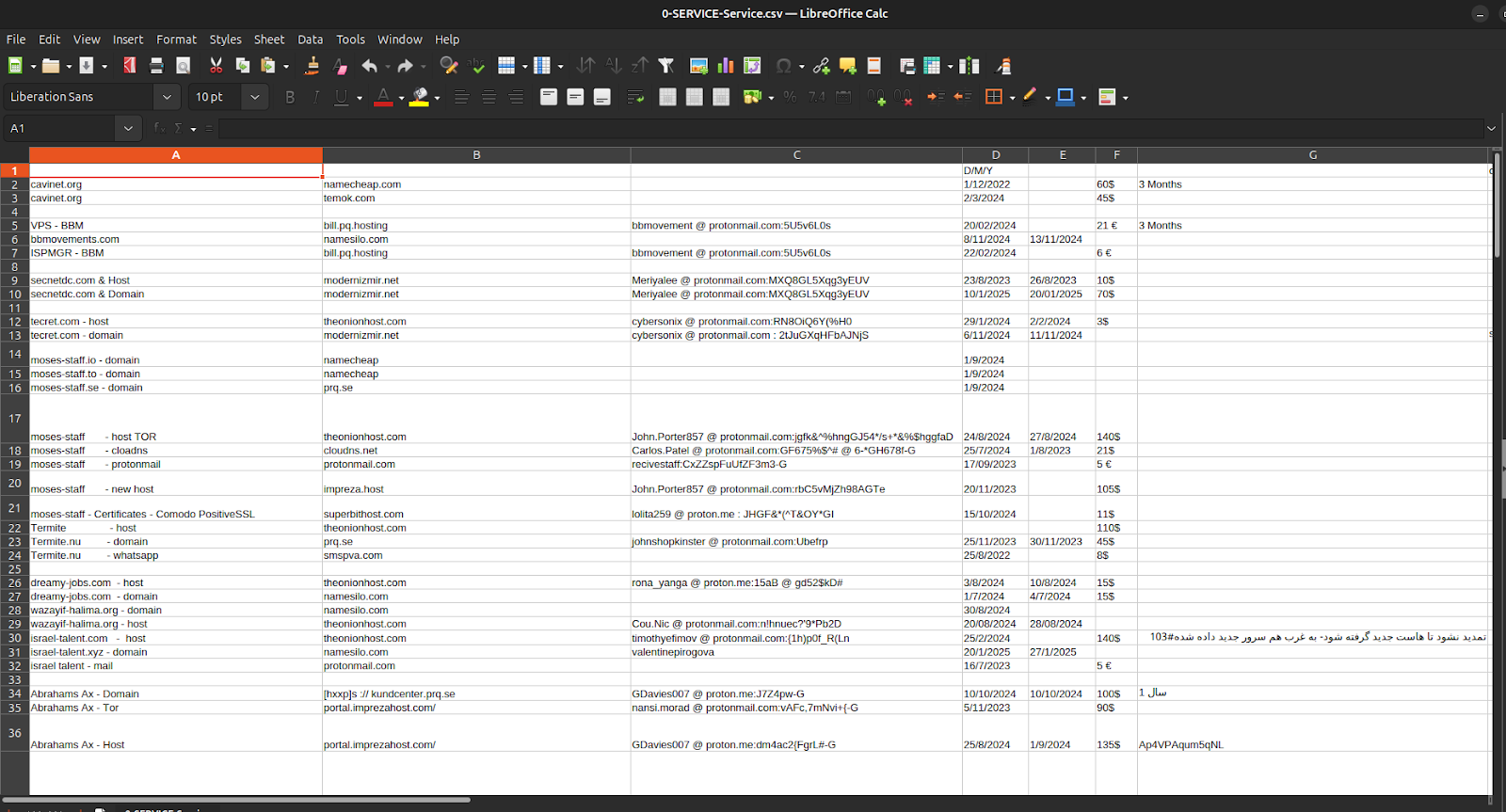
Episode 4 of the Charming Kitten / APT35 leak shows Iranian cyber operations run like a bureaucratic procurement system, with spreadsheets linking domain registrations, VPS rentals, ProtonMail identities, and Cryptomus payments that tie requests, invoices, and live infrastructure together. The same administrative apparatus mapped in the ledgers also supported Moses Staff’s leak-and-defacement campaigns—domains such as moses-staff.io, linked ProtonMail addresses, IP allocations, and bitcoin wallets were documented—exposing operational hygiene failures and reusable supply-chain patterns. #APT35 #MosesStaff

SNOWLIGHT is a lightweight ELF downloader that retrieves an XOR-encoded payload (hardcoded key 0x99) from a remote C2 over a raw TCP socket and executes it in memory using memfd_create and fexecve to avoid disk artifacts. The article describes an automated extractor built with LIEF and Capstone that parses .rodata to find the C2 (always following the “[kworker/0:2]” marker), reconstructs GOT/PLT mappings to locate the gethostbyname call, and recovers the hardcoded port (e.g. 8065). #SNOWLIGHT #UNC5174