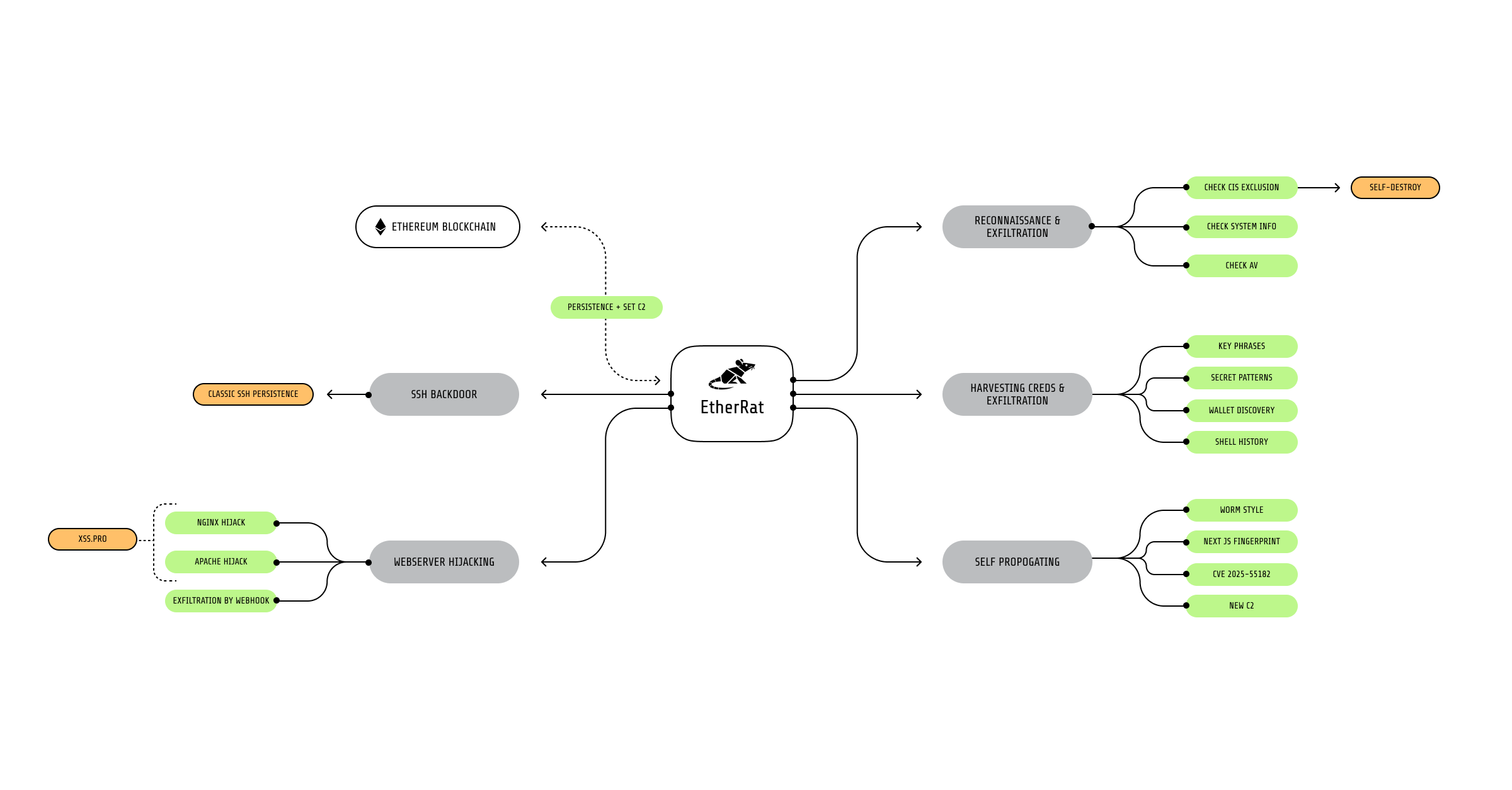
Sysdig TRT documented EtherRAT, a fileless, Ethereum smart-contract–backed implant delivered via React2Shell (CVE-2025-55182) that provides persistent access, comprehensive credential and crypto-wallet theft, worm-like propagation, web server hijacking, and SSH backdoor installation. The blockchain-based C2 grants attackers resilient command-and-control while creating an immutable forensic trail that exposed C2 URLs, wallet addresses, and a brief Grabify-based victim enumeration step. #EtherRAT #React2Shell
Category: Threat Research

GTIG observed widespread exploitation of CVE-2025-55182 (React2Shell) leading to deployment of MINOCAT, SNOWLIGHT, HISONIC, COMPOOD, ANGRYREBEL.LINUX, and XMRIG across multiple threat clusters including China-nexus espionage and financially motivated actors. Defenders are advised to patch affected React Server Components, deploy WAF rules, audit dependencies, monitor for specific IOCs and hunt for persistence artifacts like hidden directories, cron jobs, systemd services, and modified shell configs. #CVE-2025-55182 #MINOCAT #SNOWLIGHT #HISONIC #COMPOOD #XMRIG #UNC6600
The article examines the growing use of modern compiled languages—particularly Rust—by malware authors, explains how Rust’s compilation and runtime behaviors complicate static analysis, and contrasts Rust’s adoption with Golang and Nim. It demonstrates practical reverse-engineering techniques (using cargo/rustc, Ghidra, and custom scripts) on a Hello World binary and an unknown Rust malware sample (SHA256: 8f47d1e39242ee4b528fcb6eb1a89983c27854bac57bc4a15597b37b7edf34a6), and recommends dynamic analysis and community tooling to improve detection. #LucaStealer #BlackCat

FortiGuard Labs and PolySwarm analyzed UDPGangster, a UDP-based backdoor tied to the MuddyWater threat actor that targets users in Turkey, Israel, and Azerbaijan via phishing emails containing macro-enabled Word documents. The malware uses UDP C2 on port 1269, extensive anti-analysis checks, persistence via AppData and registry run keys, and supports commands for remote execution, file exfiltration, payload deployment, and C2 updates. #UDPGangster #MuddyWater

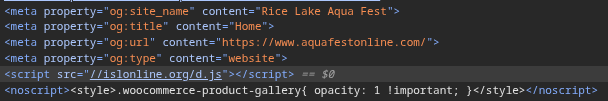
GhostPoster is a multi-extension campaign that hides a JavaScript loader inside extension logo PNGs using steganography, which extracts, decodes, and XOR-encrypts staged payloads fetched from C2 domains to fully compromise browsers. The malware performs affiliate link hijacking, tracking injection (UA-60144933-8), security-header stripping, CAPTCHA bypasses, and hidden iframe injections across 17 Firefox extensions with over 50,000 installs. #GhostPoster #FreeVPNForever

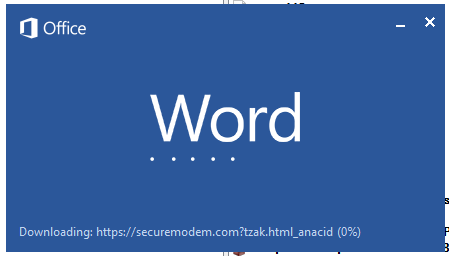
ClickFix is a social-engineering delivery method that tricks users into copying and executing obfuscated PowerShell commands, which download an HTA (dark.hta) from a malicious domain and save it as c:userspublicnC.hta. The multi-stage attack decodes nested base64 payloads, injects a PowerShell command into the clipboard to prompt user execution, and ultimately deploys DarkGate via AutoIt components. #ClickFix #DarkGate
ClickFix pages hosted via compromised legitimate websites were used to trick victims into downloading and executing a batch file that installed NetSupport Manager (NetSupport RAT), which contacted a C2 server and delivered a sideloaded malicious DLL that executed StealC V2. Stolen credentials harvested by StealC were then leveraged to access a Fortinet VPN and ultimately enable Qilin ransomware deployment. #StealC #Qilin

CYFIRMA analyzed a targeted APT-36 campaign that used a malicious Windows shortcut masquerading as a government advisory PDF to retrieve an MSI installer which deployed a .NET loader, malicious DLLs (including wininet.dll), dropped a decoy PDF, and established registry-run persistence via an HTA. Although the C2 domain wmiprovider[.]com was inactive during analysis, the loader contains obfuscated HTTP endpoints that enable remote command execution and long-term access. #APT36 #NCERT_Whatsapp_Advisory

Zscaler Threat Hunting uncovered a targeted espionage campaign impersonating the Income Tax Department of India that uses URL shorteners and public file hosting to deliver a DLL side-loading implant linked to SideWinder activity. The campaign leverages signed Microsoft binaries (SenseCE.exe) to load a malicious MpGear.dll, performs timezone-based geofencing for India (UTC+5:30), and communicates with C2 servers to deploy a resident agent. #SideWinder #SenseCE
CRIL identified a commodity loader used by multiple threat actors in targeted email campaigns that primarily impacted Manufacturing and Government organizations in Italy, Finland, and Saudi Arabia. The multi-stage, fileless infection chain uses weaponized Office documents (CVE-2017-11882), steganographic PNGs hosted on Archive.org, trojanized TaskScheduler assemblies, reflective loading and process hollowing to deliver payloads such as PureLog Stealer to a C2 at 38.49.210[.]241. #PureLogStealer #TaskScheduler
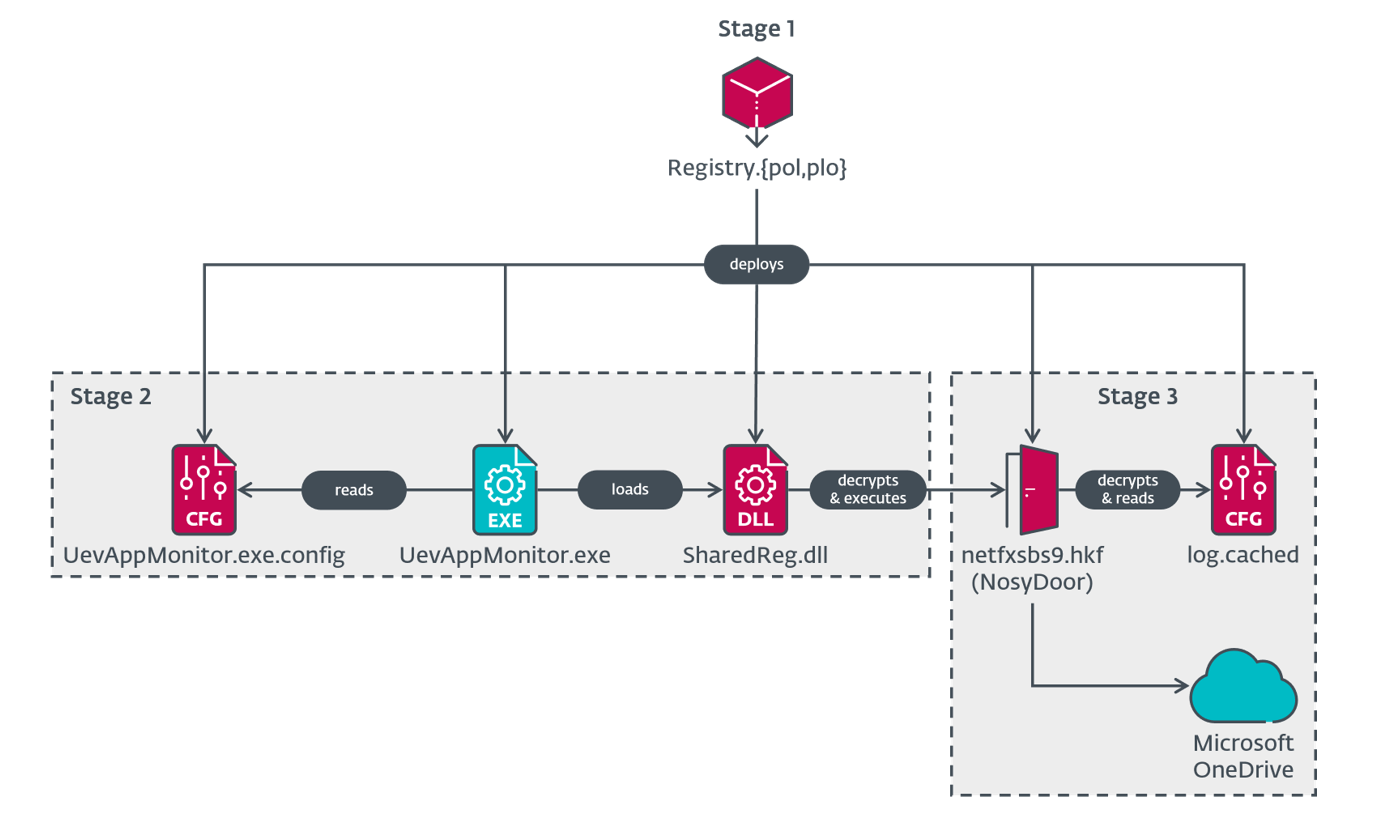
ESET discovered a previously undocumented China-aligned APT group, LongNosedGoblin, using Group Policy and cloud services to deploy a diverse C#/.NET toolset for cyberespionage against governmental entities in Southeast Asia and Japan. The toolset includes NosyHistorian (browser-history collection), NosyDoor (OneDrive-based backdoor with AppDomainManager injection), NosyStealer, NosyDownloader, NosyLogger, and supporting utilities. #LongNosedGoblin #NosyDoor
Cloud Atlas continues to target organizations in Russia and Belarus using phishing emails that exploit CVE-2018-0802 in Microsoft Office to deliver an HTA which installs a chain of VBScript- and PowerShell-based backdoors (VBShower, VBCloud, PowerShower) and the CloudAtlas implant. The group uses DLL hijacking with legitimate VLC as a loader, cloud services (WebDAV) for C2 and payload distribution, and plugins for file theft and credential/cookie extraction. #CloudAtlas #VBShower

Acronis TRU and Hunt.io collaborated to map DPRK-linked infrastructure, uncovering reused certificates, open directories staging credential-theft toolkits, FRP tunneling nodes, and a new Linux variant of the Badcall backdoor tied to Lazarus and Kimsuky activity. The report shows repeatable operational patterns—identical FRP deployments on port 9999, exposed HTTP staging directories, and certificate reuse across RDP/TLS hosts—that enable defenders to pivot on infrastructure indicators to reveal related DPRK campaigns. #Lazarus #Badcall

During analysis researchers identified multiple domains serving different roles, including an Opendir server, C2 domains for malicious browser extensions, and a C2 for EnigmaUiLauncher, with many domains masquerading as banking or invoice-related resources. Investigators traced additional malicious domains via the login panel HTML (for example systemcloud26[.]com) and verified results using paths like /enjoy.php. #EnigmaUiLauncher #Cloudflare

AhnLab ASEC’s November 2025 report details widespread distribution of Infostealer families (notably ACRStealer, LummaC2, Rhadamanthys, and AURA Stealer) using SEO-poisoned posts and cracks/keygens, with a marked shift toward DLL sideloading and new loader variants that fetch payloads from multiple fake C2s. The report includes behavioral details (HTTP(s) C2 traffic, XOR/Base64 obfuscation,…