The article examines the growing use of modern compiled languages—particularly Rust—by malware authors, explains how Rust’s compilation and runtime behaviors complicate static analysis, and contrasts Rust’s adoption with Golang and Nim. It demonstrates practical reverse-engineering techniques (using cargo/rustc, Ghidra, and custom scripts) on a Hello World binary and an unknown Rust malware sample (SHA256: 8f47d1e39242ee4b528fcb6eb1a89983c27854bac57bc4a15597b37b7edf34a6), and recommends dynamic analysis and community tooling to improve detection. #LucaStealer #BlackCat
Keypoints
- Modern compiled languages like Rust, Golang, and Nim are increasingly used to build cross-platform malware, complicating defender efforts.
- Rust adoption in malware is rising (examples include BlackCat ransomware and the open-source Luca Stealer), enabling researchers to study Rust-based threats.
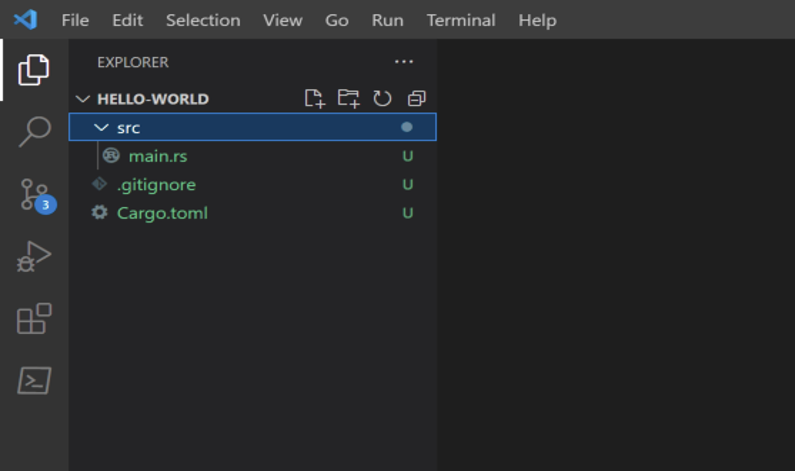
- Rust projects build with cargo/rustc produce embedded strings, dependency paths (cargo registry), and PDB paths that can leak build-time information useful for analysis.
- Reverse engineering Rust binaries requires different techniques: locating the user main via std::rt::lang_start_internal, fixing overlapping/non-null-terminated strings, and clearing data structures in Ghidra.
- Rust’s lack of a stable ABI, frequent compiler changes, built-in runtime checks, and low-level features (no-std, inline assembly, pointer use) increase binary variability and evasion options.
- Static analysis has limitations for Rust malware; the author recommends dynamic analysis (debugging, emulation, sandboxes) and sharing open-source tooling to accelerate detection and reverse engineering.
MITRE Techniques
- [None ] No MITRE ATT&CK techniques are explicitly mentioned in the article.
Indicators of Compromise
- [SHA256 ] Unknown Rust malware sample – 8f47d1e39242ee4b528fcb6eb1a89983c27854bac57bc4a15597b37b7edf34a6
- [URL/Domain ] Sample and tooling references – https://malshare.com/sample.php?action=detail&hash=8f47d1e39242ee4b528fcb6eb1a89983c27854bac57bc4a15597b37b7edf34a6, https://github.com/BinaryDefense/GhidraRustDependenciesExtractor
- [File names/paths ] Build and project artifacts that can leak information – Cargo.toml, src/main.rs, target/release/.exe, and PDB path embedded in Debug Data (can include builder username)