Over the past year Socket observed a rise in destructive open-source packages that directly sabotage developer environments by deleting source code, breaking builds, and wiping repositories or CI artifacts. These packages—published to npm, PyPI, NuGet, and Go module indexes—used remote kill switches, time-delays, typosquatting/dependency confusion, and remote payload loaders to trigger targeted codebase destruction. #Socket #npm
Category: Threat Research
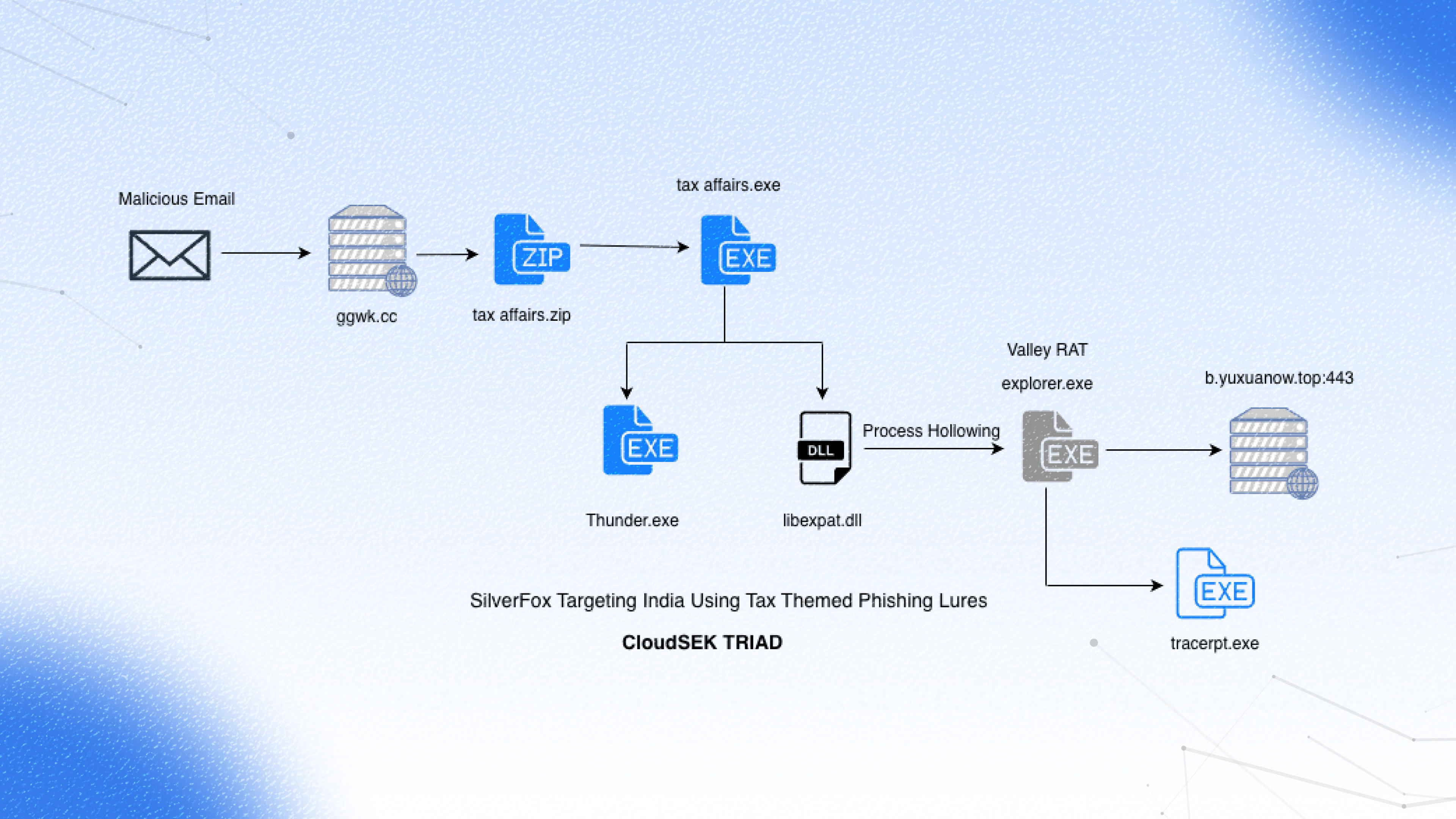
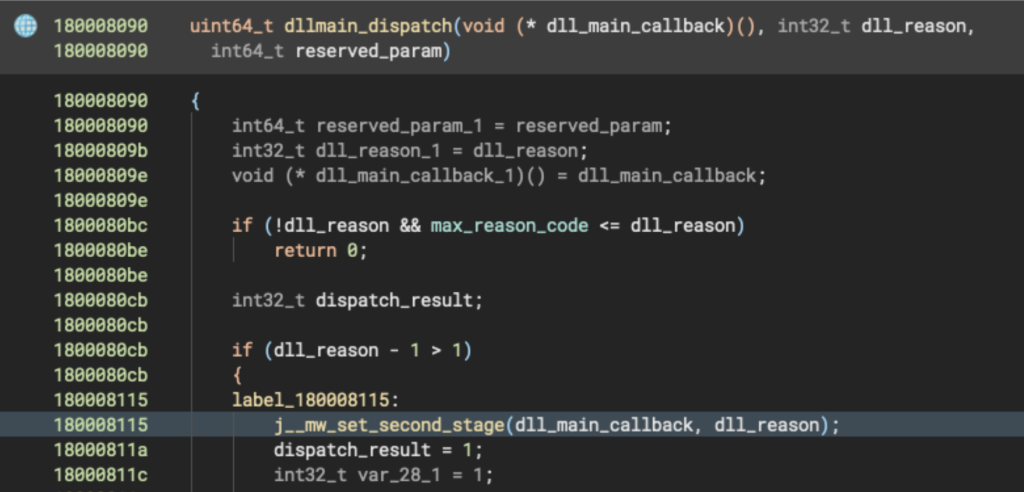
CloudSEK’s TRIAD uncovered an Income-tax-themed phishing campaign targeting India that uses an NSIS installer to drop a signed Thunder.exe and a malicious libexpat.dll, leading to in-memory Donut shellcode execution and deployment of Valley RAT. The report attributes the campaign to Silver Fox APT and details a multi-stage kill chain with DLL hijacking, process hollowing, registry-resident plugins for persistence, and a three-tier C2 infrastructure. #SilverFox #ValleyRAT

A critical remote code execution vulnerability (CVE-2025-68613, CVSS 9.9) was disclosed in n8n on December 19, 2025, affecting versions prior to the December 2025 patches. Public proof-of-concept exploits exist, many instances are internet-exposed (477 in Italy per Censys), and immediate upgrades to 1.120.4, 1.121.1, or 1.122.0 are strongly recommended. #n8n #CVE-2025-68613

Evasive Panda ran targeted adversary-in-the-middle campaigns from November 2022 to November 2024, using poisoned DNS responses and fake updaters to deliver a new loader that ultimately deployed the MgBot implant. The operation used DLL sideloading, in-memory process injection, and a DPAPI+RC5 hybrid encryption scheme to create victim-unique encrypted payloads and long-lived C2 infrastructure. #EvasivePanda #MgBot
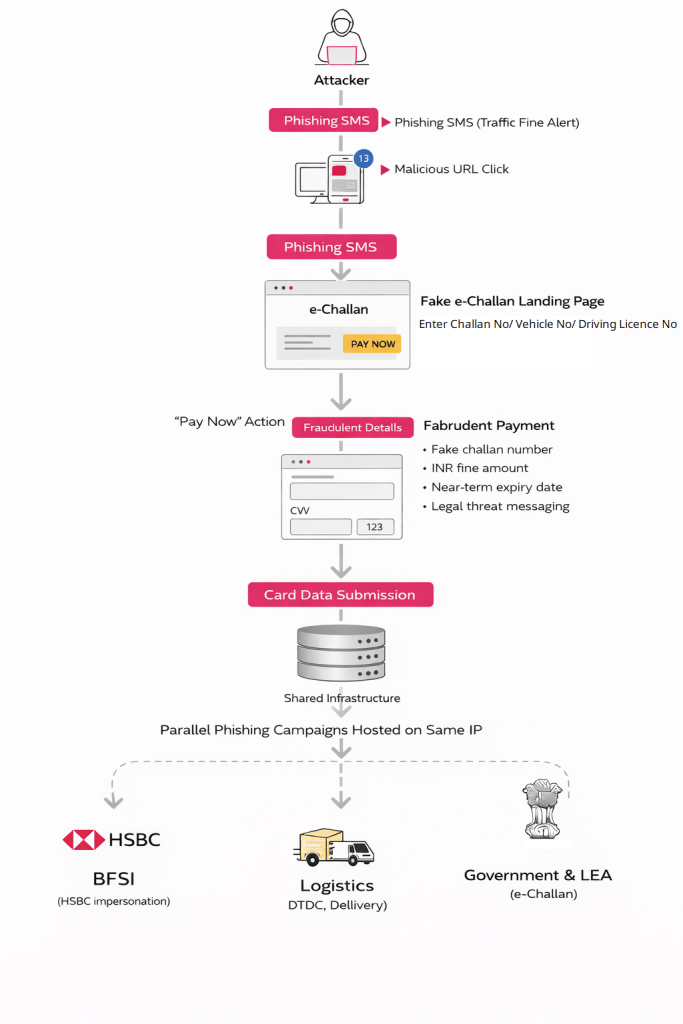
RTO Scam Wave Continues: A Surge in Browser-Based e-Challan Phishing and Shared Fraud Infrastructure
CRIL uncovered a large-scale, browser-based phishing campaign impersonating India’s e-Challan/Parivahan services that delivers malicious links via SMS and harvests card data through fake payment pages. The same shared infrastructure also hosts BFSI and logistics-themed lures, with key artifacts including domains like echala[.]vip and hosting IPs 101[.]33[.]78[.]145 and 43[.]130[.]12[.]41. #eChallan #StateBankOfIndia

Threat actors are actively exploiting CVE-2024-36401 in GeoServer to deploy XMRig-based coin miners and auxiliary tools like NetCat, using PowerShell, bash, certutil, and custom downloaders across multiple campaigns (Type A, B, C). These campaigns reuse mining pool credentials, multiple hosting domains/IPs and employ persistence via NSSM and attempts to disable Windows…
CIS published the top 10 malware of Q3 2025 and identified 31 domain IoCs for five malware; after filtering with WhoisXML MCP Server, 26 domains were analyzed in depth, revealing historical resolutions, registration patterns, and associated artifacts. The investigation found early warnings for some domains, a likely typosquatter, thousands of email-connected domains (56 weaponized), and multiple IP- and string-linked artifacts. #SocGholish #Gh0stRAT
.png)
Cofense Phishing Defense Center observed a phishing campaign impersonating ADP that used convincing display names and urgent messages to trick employees into visiting a counterfeit login site. The forged URL (hxxps://myadpaccess[.]web[.]app/signin/v1/pin4nas) and successive pages phished credentials, 2FA codes, and personal data which were exfiltrated to attacker-controlled web servers. #ADP #CofensePDC
Two novel XLL-based campaigns delivered a 64-bit backdoor named EchoGather via malicious Excel add-ins and weaponized archives exploiting a WinRAR ADS path-traversal vulnerability to target Russian organizations. Analysis links the infrastructure and decoy documents to the Paper Werewolf (GOFFEE) group and highlights techniques including delayed execution via DLL_THREAD_DETACH, hidden process creation, HTTP(S) C2 over WinHTTP, Base64-encoded communications, and exploitation of CVE-2025-8088. #EchoGather #PaperWerewolf #XLL #CVE-2025-8088
Phantom 3.5 is distributed via a fake “Adobe 11.7.7 installer” that downloads an obfuscated PowerShell payload (floor.ps1) from hxxp[:]//positivepay-messages.com/file/floor[.]ps1, decrypts an RC4/base64 payload and injects a reconstructed .NET stealer into Aspnet_compiler.exe using a BLACKHAWK.dll injector. The stealer harvests browser master keys, cookies, wallets, credentials, screenshots, keylogs and other PII, uses anti-analysis and Heaven’s Gate techniques to evade detection, persists via Run registry entries, and exfiltrates data over SMTP/FTP/Telegram. #Phantom #BLACKHAWK
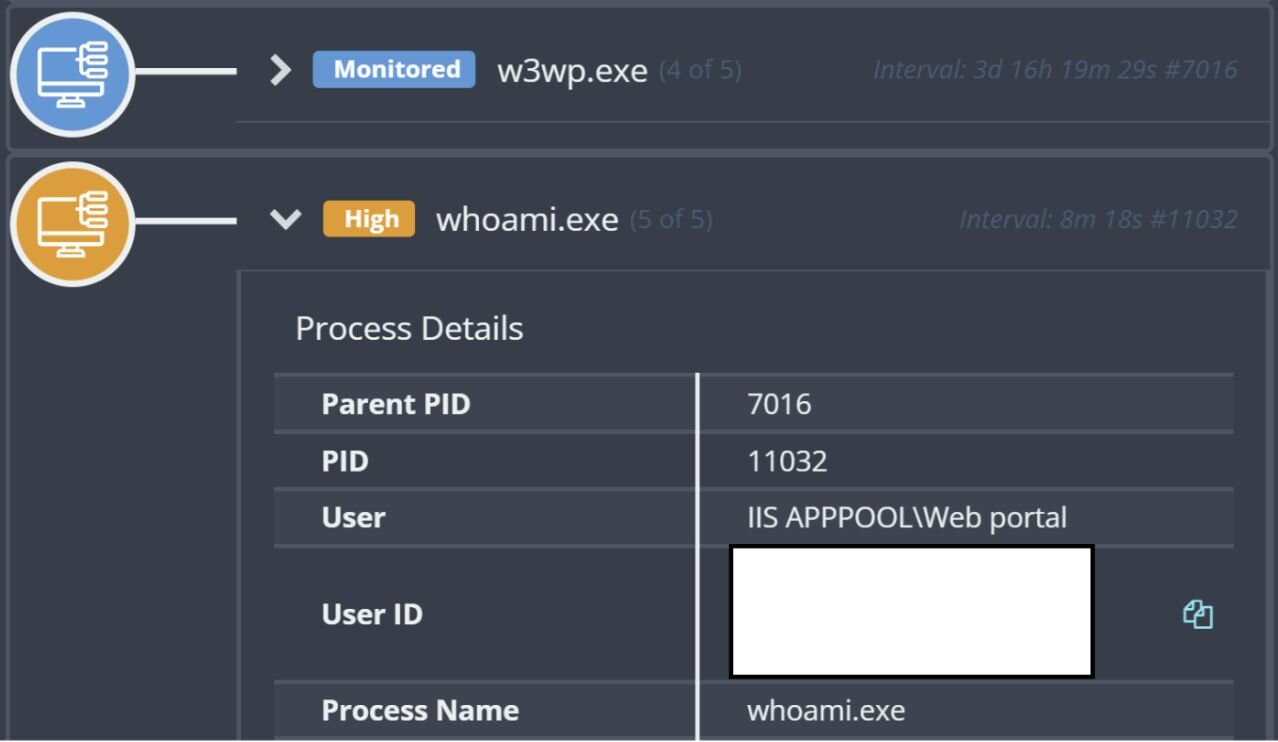
Three related IIS-originated intrusions demonstrated a consistent attacker workflow: exploitation of web application flaws to run commands via w3wp.exe, attempts to deploy a Go-based agent (agent.exe/815.exe/test.exe), use of LOLBins (certutil) to fetch payloads, and attempts to establish persistence via a Windows service (dllhost.exe/WindowsUpdate) and RMM tooling (GotoHTTP). Huntress telemetry and Windows Event Logs reveal multiple failed attempts, Defender detections/quarantines, and the actor changing tactics across incidents—initially retrying tooling, then applying Defender exclusions—while reusing infrastructure such as 110.172.104.95 and several client IPs. #Warlock #GotoHTTP #SparkRAT #ShellcodeRunner #Velociraptor #Huntress

Socket’s Threat Research Team discovered two malicious Chrome extensions named Phantom Shuttle (幻影穿梭) that pose as paid multi-location network speed test/VPN tools while injecting hardcoded proxy credentials and routing targeted traffic through attacker-controlled proxies. The extensions perform continuous credential exfiltration and man-in-the-middle data capture via a 60-second heartbeat and proxy infrastructure at phantomshuttle.space using the credentials topfany/963852wei. #PhantomShuttle #phantomshuttle.space
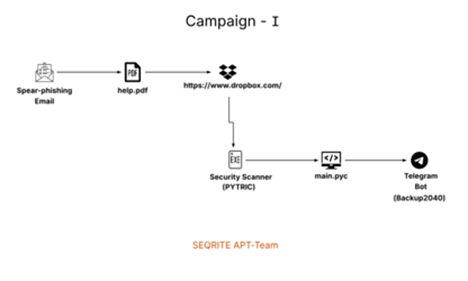
SEQRITE Labs tracked Operation IconCat (UNG0801), a Western Asia–linked activity cluster that targeted Israeli organizations using Hebrew-themed phishing lures and consistent antivirus‑icon spoofing to increase trust. Two campaigns delivered distinct implants — a PyInstaller Python wiper (PYTRIC) via a Check Point‑themed PDF and a Rust espionage implant (RUSTRIC) via a SentinelOne‑themed spear‑phishing Word document — while relying on Dropbox/HTTP C2 infrastructure and AV enumeration. #PYTRIC #RUSTRIC
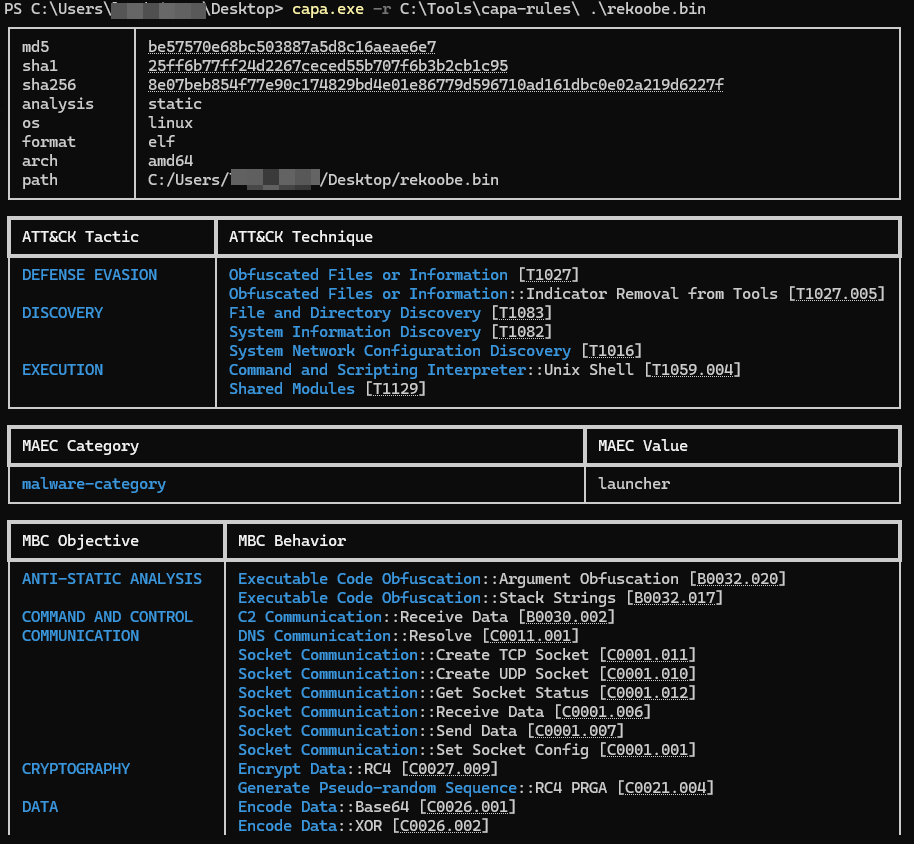
This report describes a configuration extraction pipeline for a lightweight Linux backdoor derived from TinySHell that provides silent, persistent remote access while hiding identifiable metadata. The extractor embeds FLARE capa rules to locate an RC4 decryption routine and combines Capstone and LIEF to reconstruct stack-based RC4 keys and decrypt configuration blobs (including the C2 address) stored in the .rdata section. #TinySHell #FLAREcapa
APT37’s “Artemis” campaign uses social engineering to deliver malicious HWP documents that embed OLE objects and abuse Sysinternals utilities to perform DLL side-loading and deploy RoKRAT. The multi-stage attack leverages steganography, multi-layer XOR decryption, and cloud-based C2 (Yandex/pCloud) to evade signature-based detection and highlights the need for EDR-driven behavior monitoring. #APT37 #RoKRAT
