A VBScript backdoor named 1.vba (1 MB) uses simple Caesar-shift (-5) string obfuscation and Execute to decode and immediately run malicious VBScript that downloads and runs additional payloads. Observed download hosts include AWS S3 bucket proradead and an IP-based hxxp URL, and Avast flags the sample as VBS:Kimsuky-Y.[Trj] #1.vba #VBS:Kimsuky-Y
Category: Threat Research

Researchers discovered exposed Sliver C2 databases and logs in open directories, linking a threat actor that exploited multiple FortiWeb appliances and used React2Shell (CVE-2025-55182) to deploy Sliver and FRP to expose local services. Analysis shows Sliver implants, C2 domains, FRP and a renamed microsocks proxy (cups-lpd) persisted via systemd/supervisord on outdated FortiWeb devices, highlighting a major visibility blindspot. #Sliver #FortiWeb

LevelBlue SpiderLabs warns of active exploitation of critical flaws in widely used software—MongoBleed (CVE-2025-14847) in MongoDB and React2Shell (CVE-2025-55182) in React Server Components—urging immediate patching, network segmentation, and forensic monitoring. The update also details active malware campaigns (MINOCAT, SNOWLIGHT, HISONIC, COMPOOD, XMRIG), new IOCs and trackers, USM Anywhere detection improvements, and numerous OTX pulses shared with the community. #MongoBleed #React2Shell

The ransomware ecosystem in 2025 fragmented rather than collapsed: affiliates became more independent, groups blurred their boundaries, and operators shifted toward identity abuse, supply-chain compromise, and data-first extortion. Long dwell times, widespread exploitation of enterprise software, and high victim impact (with Fortinet reporting 73% of organizations hit and low full-recovery rates) show the threat evolved into quieter, more targeted campaigns. #ScatteredLapsusHunters #OracleEBS
Open WebUI v0.6.34 and older contain a high-severity vulnerability (CVE-2025-64496, CVSS 7.3) in the Direct Connections feature that lets a malicious model server stream SSE “execute” events which run JavaScript in the user’s browser, enabling JWT theft and account takeover. If a compromised user has workspace.tools permission, the attacker can create malicious Tools that run unsandboxed Python via exec() on the backend, leading to full server compromise; update to v0.6.35 or newer. #OpenWebUI #CVE-2025-64496
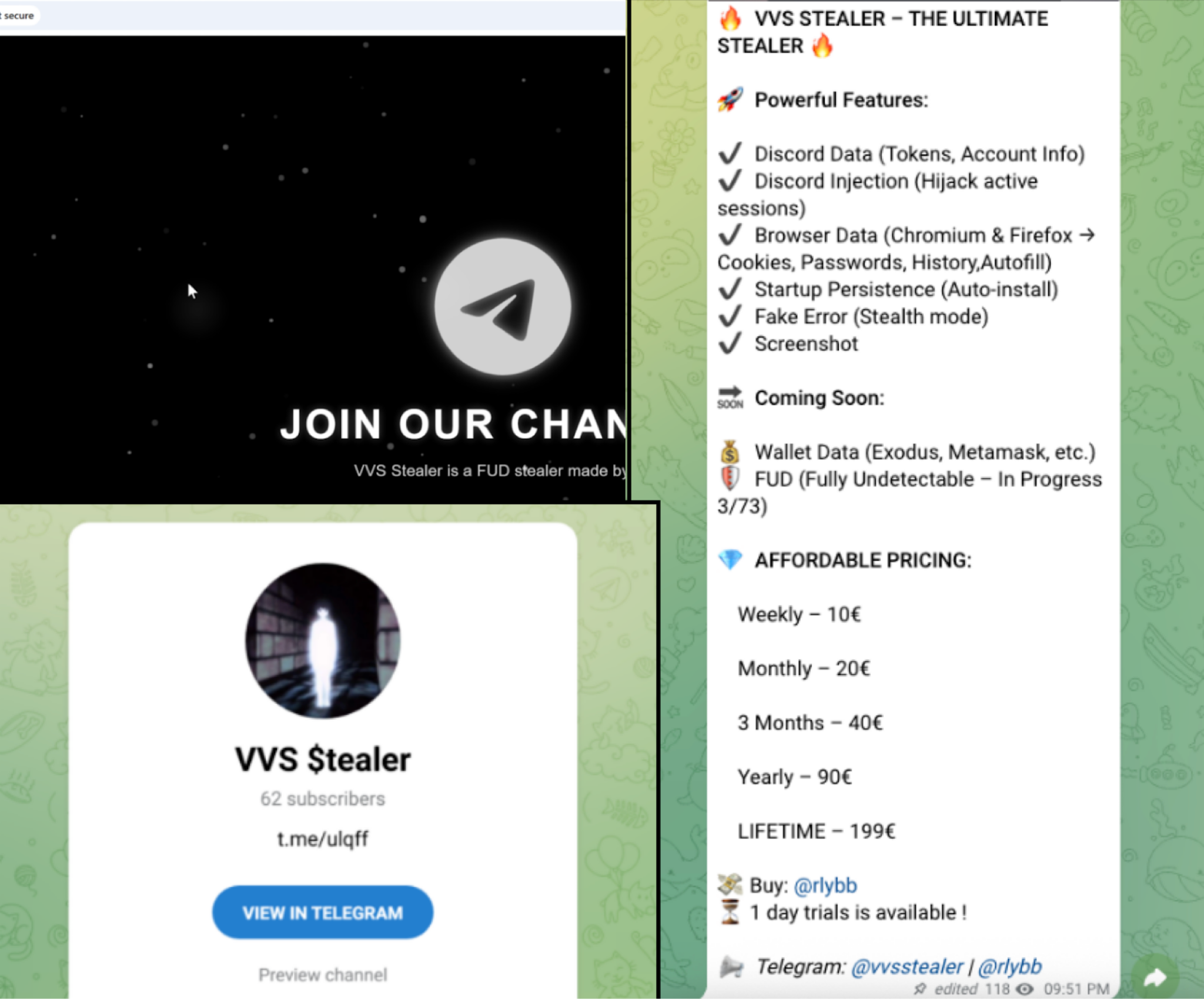
VVS stealer is a Python-based information stealer that targets Discord users and web browsers, using Pyarmor obfuscation, PyInstaller packaging, AES encryption, and injected JavaScript to exfiltrate credentials, tokens, and browser data. The malware achieves persistence via the Windows Startup folder, captures screenshots, and sends stolen data via HTTP POST to predefined…
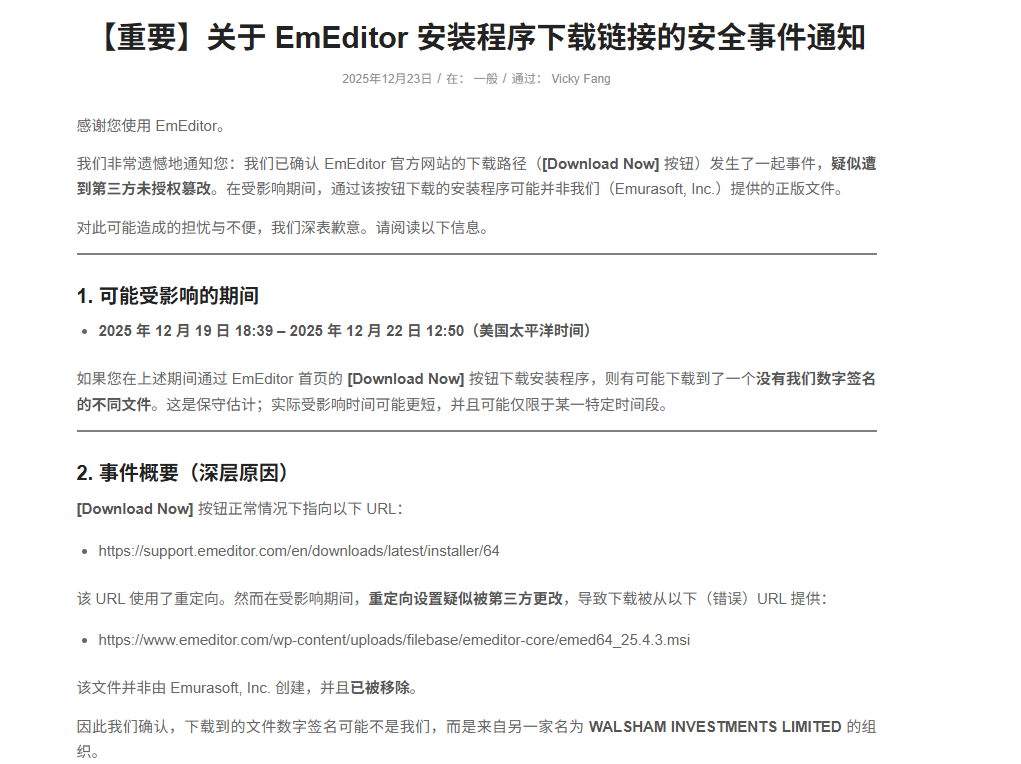
EmEditor’s official MSI installers were replaced with maliciously-signed packages between December 19–22, 2025, delivering an information‑stealing payload that collects system data, credentials, and files before exfiltrating them to attacker-controlled C2 infrastructure. The campaign also installs a persistent browser extension named “Google Drive Caching” with extensive data‑stealing, clipboard‑hijacking, and remote‑control capabilities. #EmEditor #GoogleDriveCaching
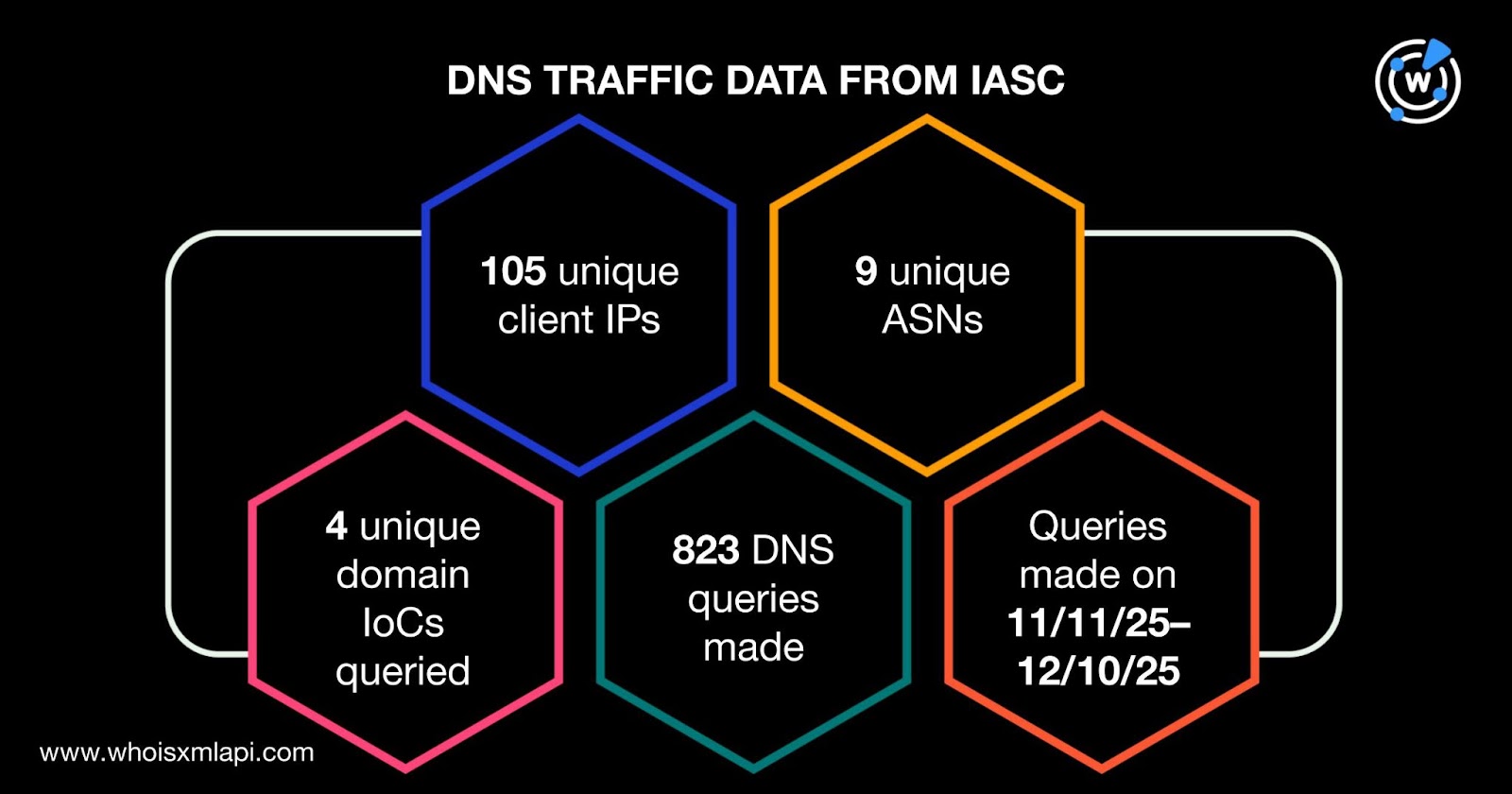
Koi Security documented a seven-year ShadyPanda campaign that leveraged verified Google Chrome and Edge extensions to build trust, accumulate users, and push silent malicious updates, ultimately impacting an estimated 4.3 million browser users. Their investigation produced six domains and three subdomains as IoCs, identified 105 unique client IPs communicating with IoC domains, 735 email-connected domains (one used for phishing), and multiple malicious IPs such as 104.21.45.44 and 104.21.49.170. #ShadyPanda #gotocdn
A kernel-mode malicious driver (ProjectConfiguration.sys) signed with a leaked certificate was used to inject a new ToneShell backdoor into system processes and to protect malicious files, registry keys, and user-mode processes. This activity is attributed to the HoneyMyte APT and uses ToneShell connecting to avocadomechanism[.]com and potherbreference[.]com for C2 communication. #ToneShell #HoneyMyte

CYFIRMA attributes a targeted multi-stage, fileless espionage campaign to APT36 (Transparent Tribe) that uses weaponized LNK files masquerading as PDFs to deliver HTA loaders and in-memory .NET deserialization payloads. The operation deploys configuration and RAT payloads (ReadOnly/WriteOnly -> ki2mtmkl.dll, iinneldc.dll), adapts persistence based on detected AV products, and maintains encrypted C2 communications to 2.56.10.86 for surveillance and data exfiltration. #APT36 #ReadOnly

Validin has launched a completely rewritten documentation hub that provides comprehensive coverage of integrations, data sources, platform features, API usage, and account management with unified global search. The new docs, which include advanced features such as YARA-based workflows, are live at docs.validin.com and aim to be more thorough, precise, and easier to navigate for analysts and engineers. #Validin #YARA
CloudSEK recovered nine months of exposed RondoDoX/Rondo botnet C2 logs that document a three‑phase campaign evolving from reconnaissance and web‑app exploitation to large‑scale IoT botnet deployment and a December 2025 Next.js Server Actions RCE wave. The activity included automated command-injection and deserialization attacks, mass binary downloads (e.g., /nuts/poop) from C2s such as 51.81.104.115 and 5.255.121.141, and repeated exploitation of internet‑facing routers and Next.js servers #Rondo #NextJS
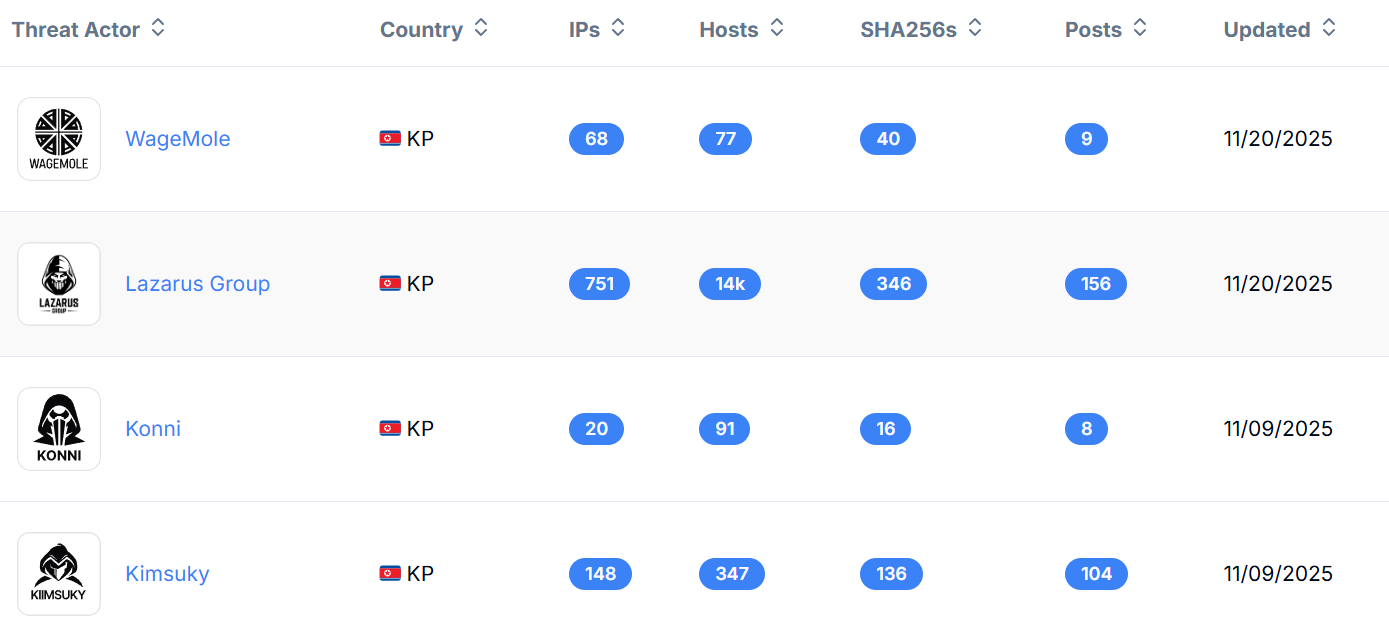
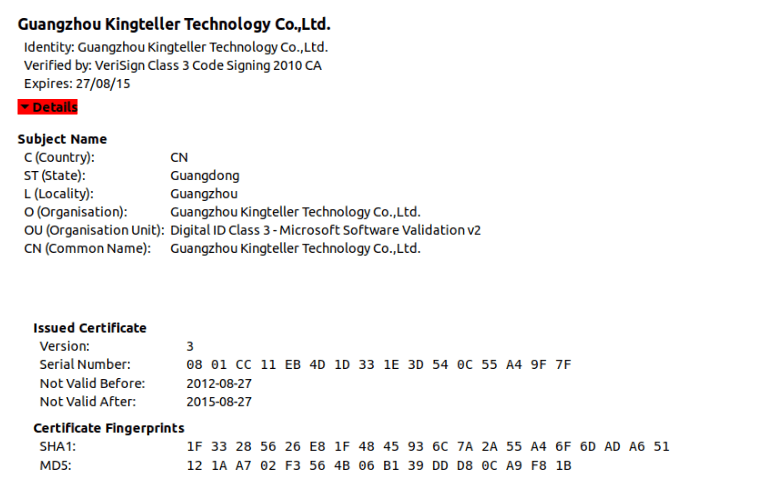
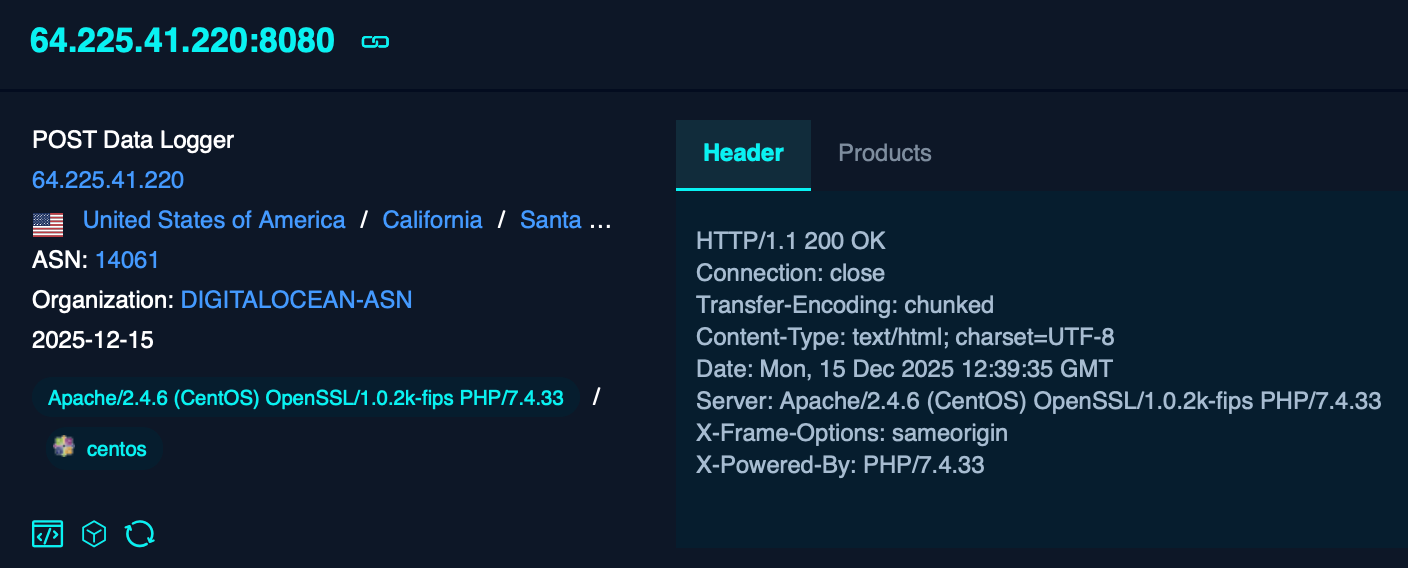
Hunt.io and Acronis mapped a broad DPRK operational infrastructure linking Lazarus, Kimsuky, and related subgroups through reused open directories, credential-harvest toolkits, FRP tunneling nodes, and certificate-linked clusters. The investigation exposed a new Linux Badcall variant, widespread MailPassView/WebBrowserPassView staging, identical FRP deployments on port 9999, and certificate pivots that reveal larger Lazarus ecosystems. #Lazarus #Badcall

Arkanix Stealer is an actively developed credential‑theft malware family distributed via Discord and forums that exists in both Python and a paid C++ “Premium” edition and uses VMProtect obfuscation, AMSI/ETW bypasses, anti‑VM/debugging checks, ChromElevator process hollowing to defeat App‑Bound Encryption, and HTTP POST exfiltration to arkanix[.]pw. The operators host a gated control panel and expose infrastructure mistakes that reveal origin IPs used for C2 and hosting. #ArkanixStealer #ChromElevator

Jamf Threat Labs analyzed a newly observed MacSync Stealer dropper delivered as a code-signed, notarized Swift application distributed via a DMG (zk-call-messenger-installer-3.9.2-lts.dmg) that silently downloads and executes a base64-encoded second-stage payload using a Swift helper and shelling out to /bin/zsh. The campaign abuses notarization and signing to evade early detection, removes com.apple.quarantine, thwarts sandbox/offline analysis with internet checks and rate-limiting, and uses domains such as gatemaden.space and focusgroovy[.]com for payload delivery. #MacSyncStealer #JamfThreatLabs
