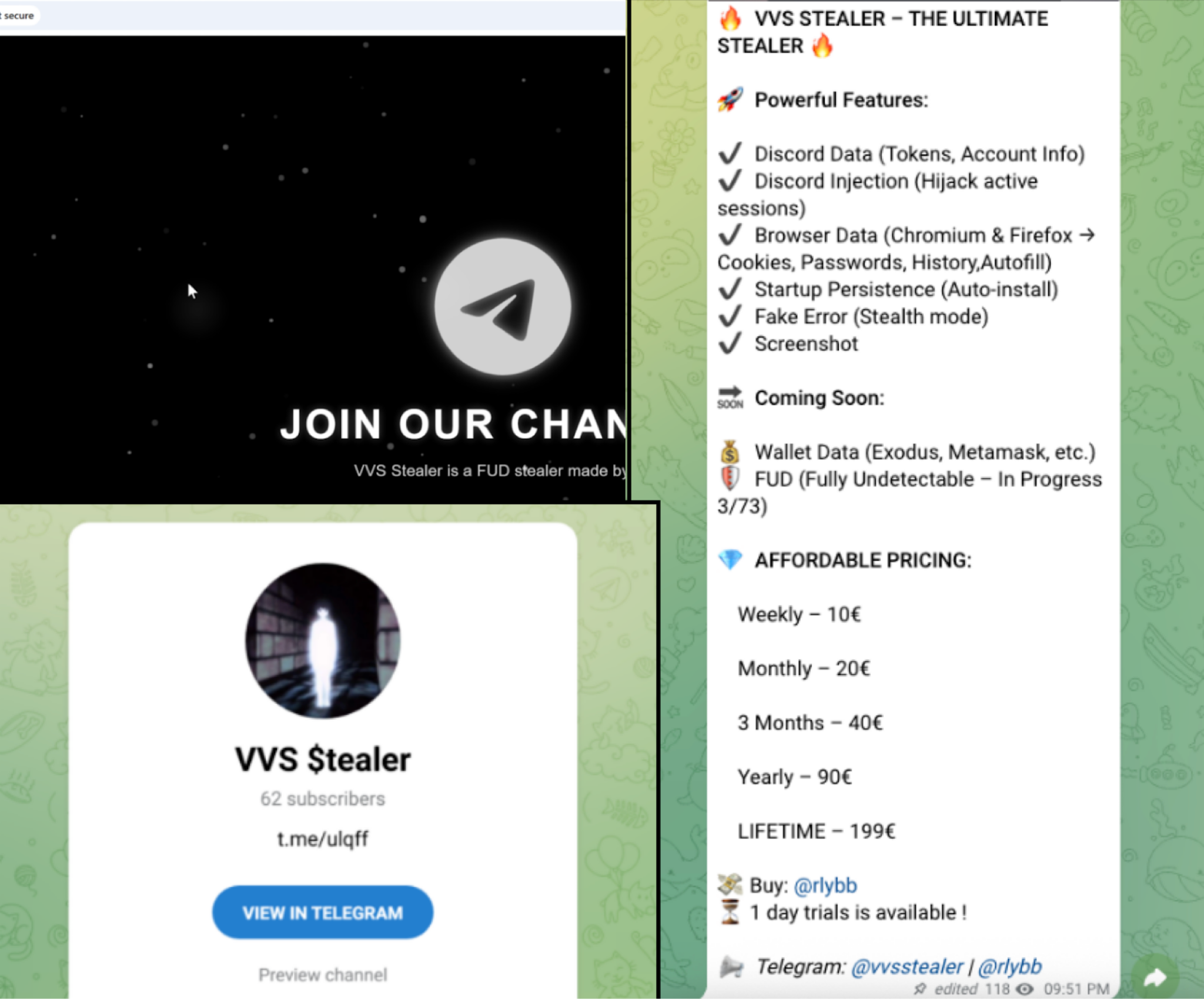
VVS stealer is a Python-based information stealer that targets Discord users and web browsers, using Pyarmor obfuscation, PyInstaller packaging, AES encryption, and injected JavaScript to exfiltrate credentials, tokens, and browser data. The malware achieves persistence via the Windows Startup folder, captures screenshots, and sends stolen data via HTTP POST to predefined Discord webhook endpoints. #VVSstealer #Discord
Keypoints
- VVS stealer is written in Python, distributed as a PyInstaller package, and its code is obfuscated with Pyarmor (including BCC mode and AES-128-CTR encryption) to hinder analysis.
- The malware targets Discord by locating and decrypting encrypted tokens in LevelDB and Local State files, then querying Discord APIs for account and billing data.
- It injects an obfuscated JavaScript payload into the Discord Electron app (modifying ASAR contents) to persist, monitor network traffic, and capture account events for data collection.
- VVS stealer also extracts browser data (cookies, passwords, history, autofill) from many Chromium-based and Firefox browsers and packages results into a ZIP for exfiltration.
- Collected data and archives are exfiltrated via HTTP POST to hard-coded and environment-configured Discord webhook endpoints; the malware uses a fixed User-Agent and expires after 2026-10-31.
- Persistence is achieved by copying the sample to the Windows Startup folder and by restarting the modified Discord process via Update.exe; it displays fake error dialogs to the user for stealth.
- Analysis required restoring .pyc headers, decompiling Python bytecode, and reversing Pyarmor protections to recover strings, BCC-mapped functions, and cryptographic keys.
MITRE Techniques
- [T1027 ] Obfuscated Files or Information – Pyarmor was used to obfuscate bytecode and encrypt strings (AES-128-CTR) to hinder static analysis and signature detection. (‘VVS stealer’s code is obfuscated by Pyarmor.’)
- [T1059 ] Command and Scripting Interpreter – The threat is implemented in Python and packaged with PyInstaller, indicating use of Python scripting for payload logic and automation. (‘The stealer is written in Python and targets Discord users, exfiltrating sensitive information like credentials and tokens stored in Discord accounts.’)
- [T1547 ] Boot or Logon Autostart Execution – Achieves persistence by copying itself to the Windows Startup folder so it runs on user logon. (‘The malware sample copies itself to the %APPDATA%MicrosoftWindowsStart MenuProgramsStartup folder to achieve startup persistence.’)
- [T1539 ] Steal Web Session Cookie or Token – Searches LevelDB/.log/.ldb files for encrypted Discord tokens (prefix dQw4w9WgXcQ:), decrypts them using the Local State DPAPI-derived key, and uses tokens to query Discord APIs. (‘The malware sample first searches for potential encrypted Discord tokens… Encrypted Discord tokens are strings beginning with the prefix dQw4w9WgXcQ:.’)
- [T1113 ] Screen Capture – Captures screenshots of the victim’s desktop as part of its stealthy data collection. (‘…operates stealthily by displaying fake error messages and capturing screenshots.’)
- [T1005 ] Data from Local System – Collects browser artifacts (cookies, passwords, history, autofill) and Discord files from local storage (LevelDB, Local State) for exfiltration. (‘extracting web browser data (cookies, passwords, browsing history and autofill details)’)
- [T1567 ] Exfiltration Over Web Service – Exfiltrates collected data and ZIP archives via HTTP POST to predefined Discord webhook endpoints and fallback URLs. (‘…exfiltrate it in JavaScript Object Notation (JSON) format… via HTTP POST requests to the predefined webhook endpoints…’)
- [T1574 ] Hijack Execution Flow – Modifies the Discord application directory by placing a downloaded obfuscated JavaScript payload (injection-obf.js) into the app code (ASAR) to execute malicious hooks and monitor traffic via CDP. (‘It then downloads the JavaScript (JS) payload… replacing the webhook endpoint URL and discord_desktop_core, into the Discord application directory.’)
Indicators of Compromise
- [SHA-256 ] malware sample hashes – 307d9cefa7a3147eb78c69eded273e47c08df44c2004f839548963268d19dd87, 7a1554383345f31f3482ba3729c1126af7c1d9376abb07ad3ee189660c166a2b, and 1 more hash
- [Discord webhook URL ] exfiltration endpoints observed – hxxps[://]ptb.discord[.]com/api/webhooks/1360401843963826236/TkFvXfHFXrBIKT3EaqekJefvdvt39XTAxeOIWECeSrBbNLKDR5yPcn75uIqKEzdfs9o2, hxxps[://]ptb.discord[.]com/api/webhooks/1360259628440621087/YCo9eVnIBOYSMn8Xr6zX5C7AJF22z26WljaJk4zr6IiThnUrVyfWCZYs6JjSC12IC8c0
- [File name ] artifacts and payload files – vvs (Python bytecode/.pyc), pyarmor_runtime.pyd
- [File path ] persistence and installation path – %APPDATA%MicrosoftWindowsStart MenuProgramsStartup (used to achieve startup persistence)