EmEditor’s official MSI installers were replaced with maliciously-signed packages between December 19–22, 2025, delivering an information‑stealing payload that collects system data, credentials, and files before exfiltrating them to attacker-controlled C2 infrastructure. The campaign also installs a persistent browser extension named “Google Drive Caching” with extensive data‑stealing, clipboard‑hijacking, and remote‑control capabilities. #EmEditor #GoogleDriveCaching
Keypoints
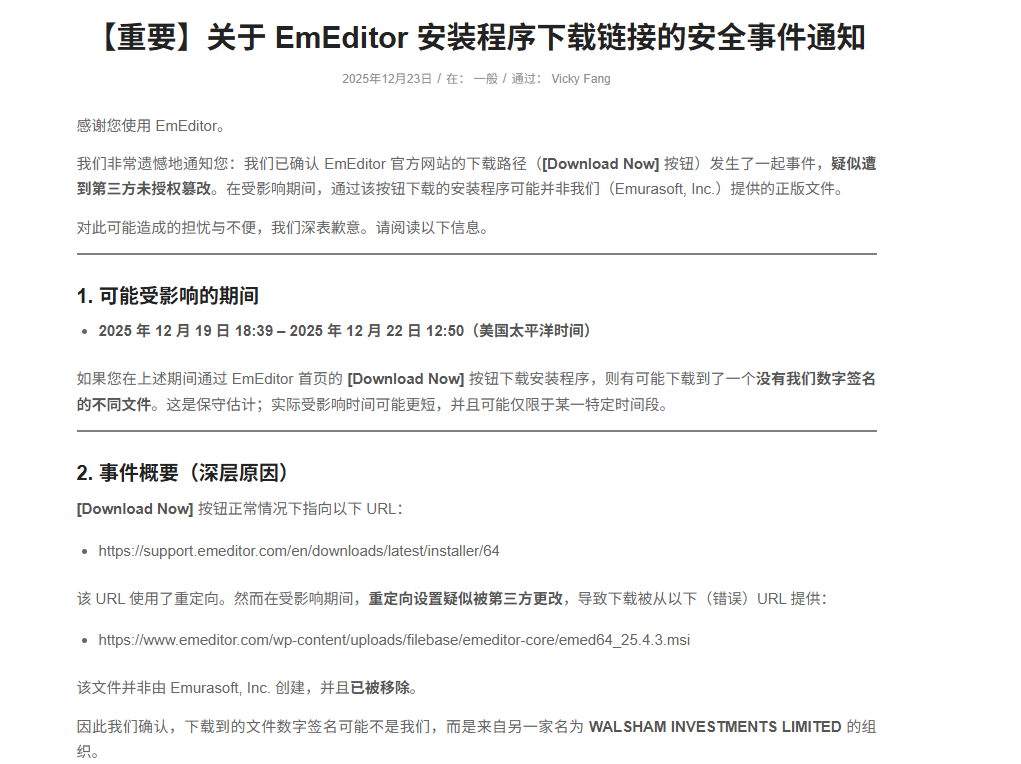
- Between Dec 19–22, 2025 EmEditor’s official MSI installers on the vendor website were replaced by malicious MSI packages signed with a non-official signature “WALSHAM INVESTMENTS LIMITED”.
- The malicious MSI embeds a script that disables logging, defines C# classes, runs PowerShell commands, generates an RSA key, collects system information, and uploads encrypted data to C2 (e.g., https://emeditorgb.com/take/mg8heP0r/ + uuid).
- The payload steals files from Desktop, Documents, and Downloads, harvests VPN and Windows credentials, browser data (cookies, Login Data, history), and credentials from numerous apps (Zoho Mail, Evernote, Notion, Discord, Slack, Skype, MS Teams, Zoom, PuTTY, WinSCP, Steam, Telegram, etc.).
- Stolen data is written to files like sandbox.txt and system.txt, packaged into a compressed archive named array.bin, and exfiltrated to attacker-controlled C2 servers and fallback DGA domains.
- A persistent browser extension called “Google Drive Caching” (core logic in background.js) is installed, with initial C2 cachingdrive.com and a weekly-seeded DGA fallback; the extension supports cookie/history theft, screenshots, keylogging, clipboard hijacking for 30+ cryptocurrencies, and remote commands (get_cookies, start_proxy, execute_js, uninstall, etc.).
- Qianxin observed the incident, captured payloads, and reports that Qianxin products (TIP, Tianqing/Liuhe, Tianyan, NGSOC, Situational Awareness) can detect or block the malicious MSI and subsequent activity; Tianqing “Liuhe” engine can intercept the malicious MSI.
- IOCs include MD5 hashes, multiple C2 domains and IP:port endpoints, and a list of DGA-generated domains for the week of Dec 25, 2025, indicating broad operational infrastructure and fallback mechanisms.
MITRE Techniques
- [T1195 ] Supply Chain Compromise – The attack replaced official MSI installers on the vendor website with malicious packages signed by a non-official certificate (‘the MSI installation packages were replaced with malicious ones signed with a non-official signature “WALSHAM INVESTMENTS LIMITED”‘).
- [T1059.001 ] PowerShell – The embedded malicious script executes subsequent PowerShell commands to run payload logic (’embedded malicious script used to execute subsequent PowerShell commands.’).
- [T1082 ] System Information Discovery – The payload collects system version, username, CPU/GPU/memory, screen resolution, time zone and other system details (‘It then collects system information and generates an RSA public key for encrypting the stolen data.’).
- [T1083 ] File and Directory Discovery – The malware enumerates filenames in Desktop, Documents, and Downloads paths to identify files for exfiltration (‘It steals files from Desktop, Documents, and Downloads paths, first collecting filenames within those paths.’).
- [T1005 ] Data from Local System – Sensitive files and application data (browser cookies, Login Data, VPN configs, app credentials) are collected from the local system (‘It steals VPN configurations, Windows login credentials, browser information including cookies, Login Data, user settings, etc.’).
- [T1113 ] Screen Capture – The malware captures screenshots of the current desktop as part of data collection (‘Captures a screenshot of the current screen:’).
- [T1041 ] Exfiltration Over C2 Channel – Collected and encrypted data are uploaded to attacker-controlled endpoints (e.g., emeditorgb.com/take/…) for exfiltration (‘encrypts it, and uploads it to C2: https://emeditorgb.com/take/mg8heP0r/ + uuid’).
- [T1071.001 ] Application Layer Protocol: Web Protocols – Command-and-control and exfiltration use web/HTTPS endpoints and domains (e.g., cachingdrive.com and listed C2 domains/IPs) for communications (‘cachingdrive.com’ and multiple emeditor-related domains and IP:port endpoints are listed as C2).’
- [T1176 ] Browser Extensions – The attackers install a malicious browser extension “Google Drive Caching” for persistence and data theft, with core logic in background.js (‘Ultimately, it installs a browser extension for persistence, named “Google Drive Caching,” which is a fully-featured information-stealing malware.’).
- [T1056.001 ] Input Capture: Keylogging – The extension includes keylogging functionality categorized by web page to capture user input (‘Keylogging functionality, categorized based on specific web pages:’).
- [T1056.003 ] Input Capture: Clipboard Data – The extension hijacks the clipboard and replaces cryptocurrency addresses for 30+ currencies (‘Clipboard hijacking functionality supports replacing addresses for 30+ types of cryptocurrencies.’).
- [T1568 ] Domain Generation Algorithms – Attackers implemented a DGA fallback with weekly-seeded domain generation to provide resilient C2 (‘the attackers also designed a set of DGA (Domain Generation Algorithm) logic as a fallback list. It changes seeds weekly using the formula [original seed, year, week number, year*100+week number]’).
Indicators of Compromise
- [MD5 ] malicious installer/payload file hashes – a27731876e769ff19e225700085967bf, 6a4554509ce27efe5c6b8e58431f60d8
- [Domains ] C2 and malicious infrastructure – emedjp.com, cachingdrive.com, and 4 more domains (emeditorde.com, emedorg.com, emeditorjapan.com, emeditorjp.com)
- [IP:Port ] network C2 endpoints – 147.45.50.54:443, 5.101.82.118:443, and 46.28.70.245:443
- [DGA Domains ] fallback/generated C2 domains for week of Dec 25, 2025 – brt461jnbjvm52mw.biz, 1a298k7iqspq52l4r9e.space, z2ctmmm61dm0c3wfic.store, and 7 more DGA domains
- [File Names ] artifacts and data files created by the malware – sandbox.txt, system.txt, array.bin (compressed archive), and extension core script background.js
- [Code Signing Certificate ] fraudulent signature used on MSI – ‘WALSHAM INVESTMENTS LIMITED’ (non-official signer for the malicious MSI)
Read more: https://ti.qianxin.com/blog/articles/emeditor-supply-chain-incident-details-disclosed-en/