OX Security discovered two malicious Chrome extensions impersonating the legitimate AITOPIA sidebar that exfiltrate ChatGPT and DeepSeek conversations and full browsing URLs to attacker-controlled servers every 30 minutes. One extension had over 600,000 users and retained a Google “Featured” badge while both sent stolen chat content and browsing data to C2 domains like deepaichats[.]com. #ChatGPT #DeepSeek
Category: Threat Research

A malicious WordPress plugin named Modern Recent Posts was found injecting Base64‑encoded JavaScript into the wp-admin dashboard to display fake browser/Java update pop-ups and force downloads from attacker-controlled domains. The campaign is served from the C2 domain persistancejs[.]store (observed on 28 sites), targets logged-in administrators on Windows, and includes a self-update/self-destruct mechanism to maintain persistence. #ModernRecentPosts #persistancejs.store

AhnLab ASEC discovered Guloader being distributed via phishing emails that impersonate an employee performance report and include a RAR attachment containing an NSIS executable named “staff record pdf.exe” which can be mistaken for a PDF. The executable downloads shellcode from a Google Drive URL and loads Remcos RAT in memory, enabling…

GoBruteforcer is a modular Go-based botnet that brute-forces FTP, MySQL, PostgreSQL and phpMyAdmin credentials to compromise Linux servers and recruit them as scanning and brute-force nodes. The 2025 variant adds an obfuscated Go IRC bot, downloader modules, process-masking and cron persistence, and has been observed targeting crypto project databases and legacy stacks like XAMPP that expose weak defaults #GoBruteforcer #XAMPP

SafePay emerged in late 2024 as a centralized, closed ransomware group that escalated rapidly into a global threat, using double-extortion by stealing financial and intellectual property data and pressuring victims via a Tor data leak site. Its modular Windows PE32 DLL employs compromised credentials, backdoors (e.g., QDoor), PowerShell discovery scripts, LOLBins (PsExec, regsvr32/rundll32), archiving and exfiltration tools (WinRAR, FileZilla, Rclone), defense evasion (killing AV/backup services, deleting Volume Shadow Copies, modifying boot settings), and a Cyrillic-language kill switch. #SafePay #QDoor
The Italian CERT-AGID identified a recently registered malicious domain hosting a fake Ministry of the Interior portal (with references to the Polizia di Stato) that purports to let users check the status of immigration-related applications. The fraudulent site asks visitors to enter personal and document details to harvest identities for subsequent targeted fraud, and CERT-AGID alerted the Ministry, requested domain takedown, and distributed IoCs. #CERT-AGID #MinistryOfInterior #PoliziaDiStato

Recorded Future’s Insikt Group tracked BlueDelta credential-harvesting campaigns from February to September 2025 that impersonated Microsoft OWA, Google, and Sophos VPN portals and abused free hosting and tunneling services to capture and exfiltrate credentials. The campaigns targeted researchers and policy-linked organizations—using legitimate PDF lures, customized JavaScript for input capture and redirection to real sites to reduce detection and suspicion. #BlueDelta #MicrosoftOWA

Zscaler ThreatLabz discovered three malicious npm packages—bitcoin-main-lib, bitcoin-lib-js, and bip40—that deploy a Node.js remote access trojan named NodeCordRAT which uses Discord for command-and-control. The malware exfiltrates Chrome credentials, .env files, and MetaMask data (including LevelDB .ldb files and seed phrases) and was distributed via postinstall scripts and PM2; #NodeCordRAT #bip40
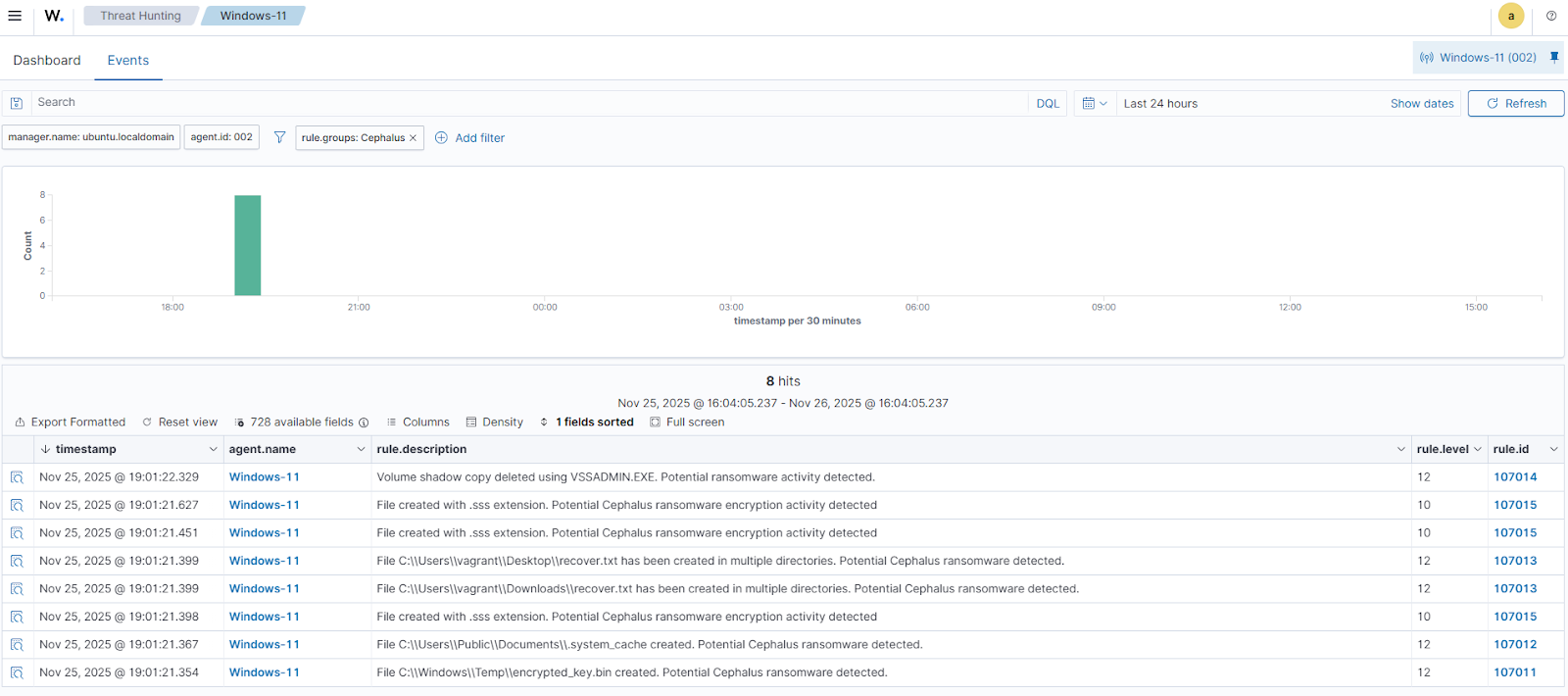
Cephalus ransomware surfaced in mid‑August 2025, targets Windows endpoints via exposed RDP accounts lacking MFA, and performs stealthy local encryption, data exfiltration, and Volume Shadow Copy deletion to hinder recovery. The article demonstrates detection and automated response using Wazuh (Sysmon integration, custom detection rules, File Integrity Monitoring, YARA rules, and Active…

The article explains GitHub’s guidance to harden npm package publishing by adopting Trusted Publishing (OIDC), enforcing stronger 2FA for publishing actions, and preferring WebAuthn/passkeys over TOTP while outlining benefits and trade-offs for CI/CD and account changes. It emphasizes replacing long‑lived tokens with ephemeral OIDC flows or scoped granular access tokens, tightening publishing settings, and adopting WebAuthn to reduce supply‑chain compromise risk. #ShaiHulud #npm

A single, well-resourced Chinese threat actor called DarkSpectre operated at least three large extension-based campaigns—ShadyPanda, GhostPoster, and the newly disclosed Zoom Stealer—infecting over 8.8 million users across Chrome, Edge, Firefox, and Opera using varied techniques including steganography, remote code injection, and real-time WebSocket exfiltration. The Zoom Stealer campaign alone harvested corporate meeting intelligence from 2.2M users by scraping 28+ conferencing platforms and streaming data to attacker-controlled Firebase and cloud function infrastructure. #DarkSpectre #ZoomStealer
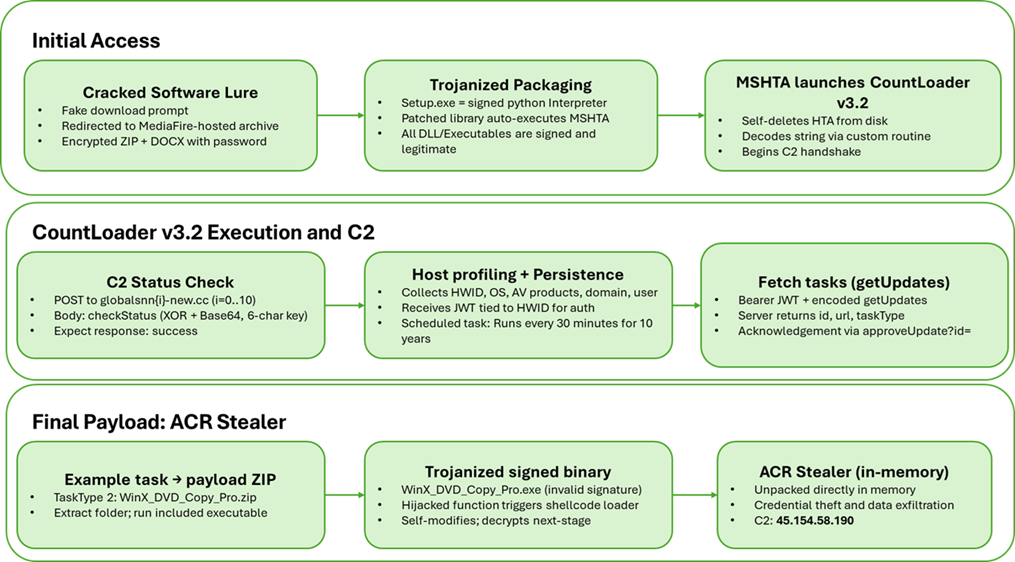
Howler Cell identified a multi-stage campaign distributing a new CountLoader v3.2 variant via cracked software sites that ultimately delivers an in-memory ACR Stealer payload. The loader expands capabilities (nine task types), employs MSHTA/PowerShell fileless execution, removable-media propagation, custom XOR+Base64 C2 encoding, and persistence via scheduled tasks. #CountLoader #ACRStealer
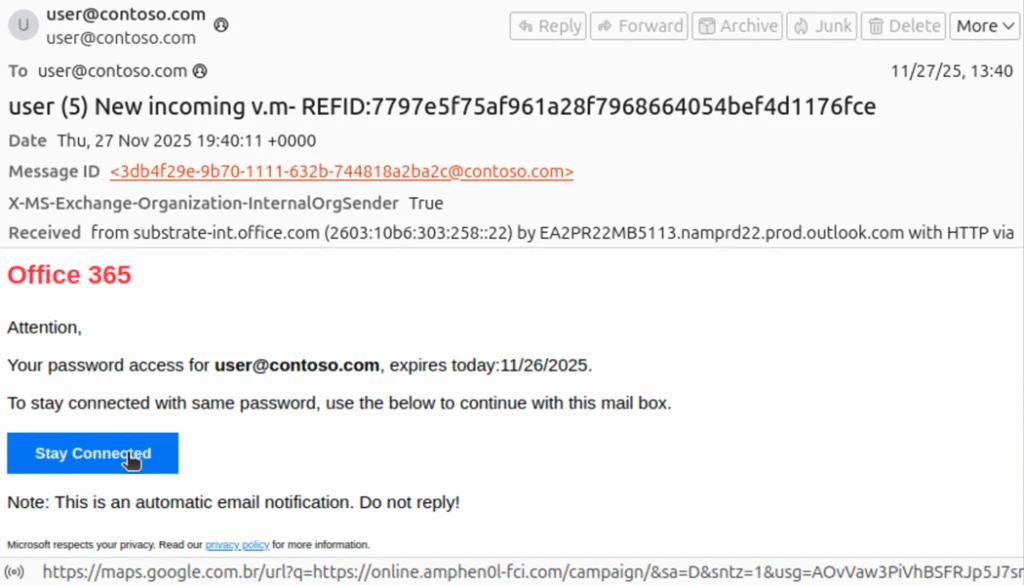
Phishing actors exploit complex mail routing and misconfigured spoof protections to send emails that appear to originate from an organization’s own domain, increasing success of credential phishing and invoice/financial scams. Microsoft observed widespread use of PhaaS platforms like Tycoon2FA in these opportunistic campaigns and recommends enforcing strict SPF/DMARC, properly configuring third-party connectors, and deploying phishing-resistant MFA to mitigate risk. #Tycoon2FA #Office365

Securing AI must be approached as a lifecycle challenge that crosses development, operations, data, supply chain, and user interaction boundaries rather than fitting into any single existing security function. The article outlines five categories of enterprise AI risk and recommends lifecycle-based frameworks, real-time monitoring, supplier validation, and governance to maintain trust, accountability, and resilience. #ISOIEC42001 #NISTAIRMF

A VBScript backdoor named 1.vba (1 MB) uses simple Caesar-shift (-5) string obfuscation and Execute to decode and immediately run malicious VBScript that downloads and runs additional payloads. Observed download hosts include AWS S3 bucket proradead and an IP-based hxxp URL, and Avast flags the sample as VBS:Kimsuky-Y.[Trj] #1.vba #VBS:Kimsuky-Y