MongoBleed (CVE-2025-14847) is a critical, unauthenticated memory-disclosure vulnerability in MongoDB Server that lets remote attackers manipulate the OP_COMPRESSED uncompressedSize field to trigger oversized heap allocations and leak sensitive data such as cleartext credentials and API keys. A public proof-of-concept and confirmed active exploitation were published in late December 2025, and roughly…
Category: Threat Research

Medusa Ransomware is a rapidly expanding RaaS operation (also known as Storm-1175/Spearwing) that has abused unpatched RMM and public-facing application vulnerabilities to gain initial access, perform data exfiltration, and carry out file encryption across diverse sectors. Darktrace and other vendors have observed the group exploiting SimpleHelp and GoAnywhere flaws, abusing legitimate RMM tooling for C2 and persistence, and exfiltrating data to domains such as erp.ranasons[.]com. #Medusa #SimpleHelp
Palo Alto Networks Unit 42 tracked an Ashen Lepus (aka WIRTE) espionage campaign that deployed a new malware suite dubbed “AshTag” against Arabic-speaking government entities, noting improved operational security such as custom payload encryption, infrastructure obfuscation using legitimate subdomains, and in-memory execution to reduce forensic artifacts. The researchers extracted 10 domains and 12 malicious subdomains as IoCs, observed 430 unique client IPs communicating with those domains, and identified historical WHOIS and DNS artifacts that expanded the set of related indicators. #AshTag #AshenLepus

Varonis Threat Labs disclosed “Reprompt,” a one-click attack against Microsoft Copilot Personal that abuses the q URL parameter to inject prompts and then uses server-driven follow-up requests to stealthily exfiltrate user data and conversation memory without further interaction. Microsoft has patched the issue and says enterprise Microsoft 365 Copilot customers are…

Validin’s 2025 recap highlights major research, community growth, product updates, and collaborations that expanded platform capabilities and researcher access. The company’s research exposed campaigns such as the FreeDrain crypto-theft network and phishing infrastructure tied to Scattered Spider. #FreeDrain #ScatteredSpider

The article analyzes how LLM input transformations—tokenization, embeddings, positional encodings, and self-attention—create architectural attack surfaces that enable prompt injection, adversarial suffixes, gradient-based embedding manipulation, and attention hijacking. It reviews attack vectors (filter bypass, GCG-style gradient attacks, chunking/context-window exploits, attention hijacking) and defensive mitigations including randomized smoothing, suffix filtering, adversarial training, and vendor controls like instruction hierarchies. #OpenAI #Anthropic
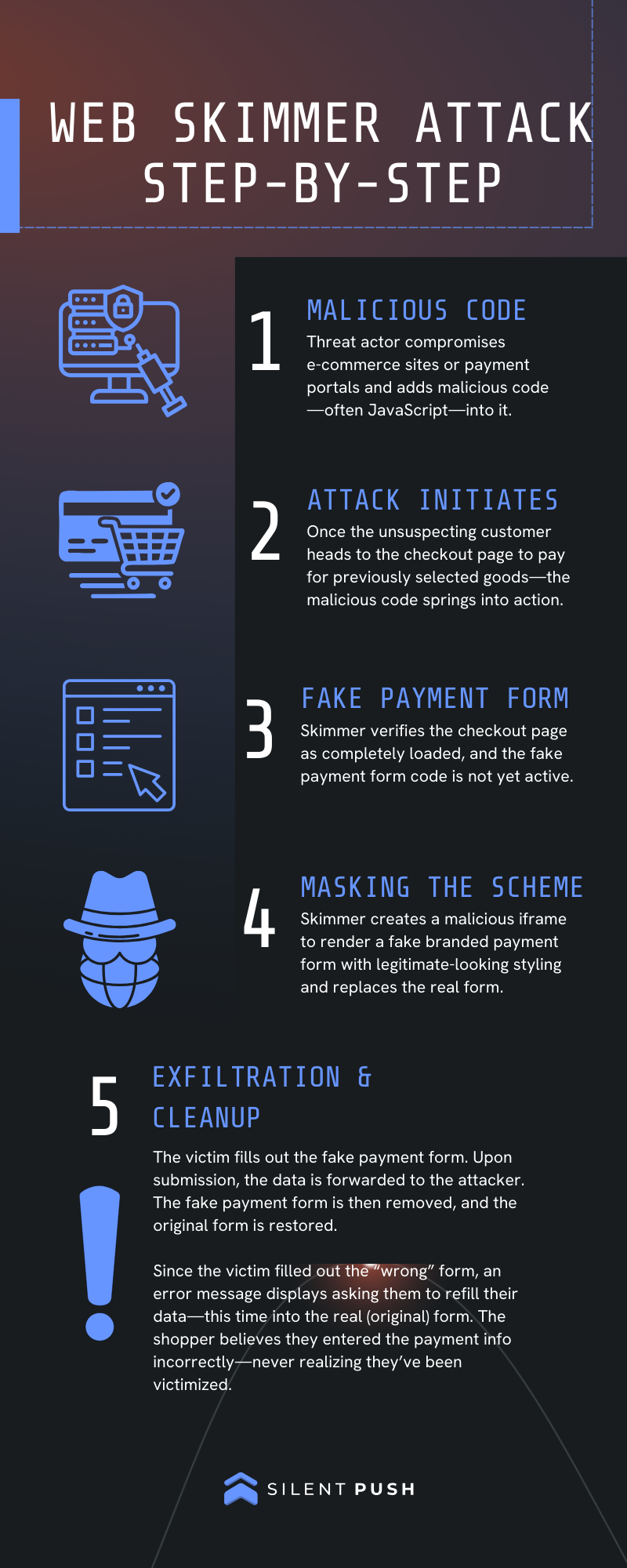
Silent Push analysts uncovered a long-running Magecart web-skimming campaign active since at least January 2022 that uses highly obfuscated JavaScript to inject fake payment forms on compromised e-commerce sites and target major payment networks including American Express, Diners Club, Discover, JCB, Mastercard, and UnionPay. Key indicators include domains such as cdn-cookie[.]com…

ANY.RUN performed a full dynamic and static analysis of CastleLoader, revealing a multi-stage delivery (Inno Setup → AutoIt → process hollowing into jsc.exe) that injects a PE-only-in-memory payload used to deliver information stealers and RATs against government and critical infrastructure targets. The report includes an automated parser to extract configuration strings,…

Mandiant released AuraInspector, an open-source command-line tool to help defenders identify and audit access control misconfigurations in the Salesforce Aura framework and Experience Cloud. The post documents techniques attackers can use—including abusing Aura methods, action-bulking, Record Lists, Home URLs, self-registration discovery, and a GraphQL Aura controller that bypasses the 2,000-record limit—and provides remediation guidance. #AuraInspector #Salesforce
The article shows that widely available large language models are being used by attackers as rapid authoring tools to produce PowerShell and other scripts, accelerating the tempo of commodity attacks without introducing fundamentally new exploitation techniques. Multiple Huntress case studies — including RDP brute force, WinRM lateral movement, browser credential harvesters, Veeam-focused attempts, and a malicious Chrome extension beaconing to 172.86.105[.]237:5000 — were stopped by basic telemetry, MFA, segmentation, and tuned detections. #Veeam #Huntress
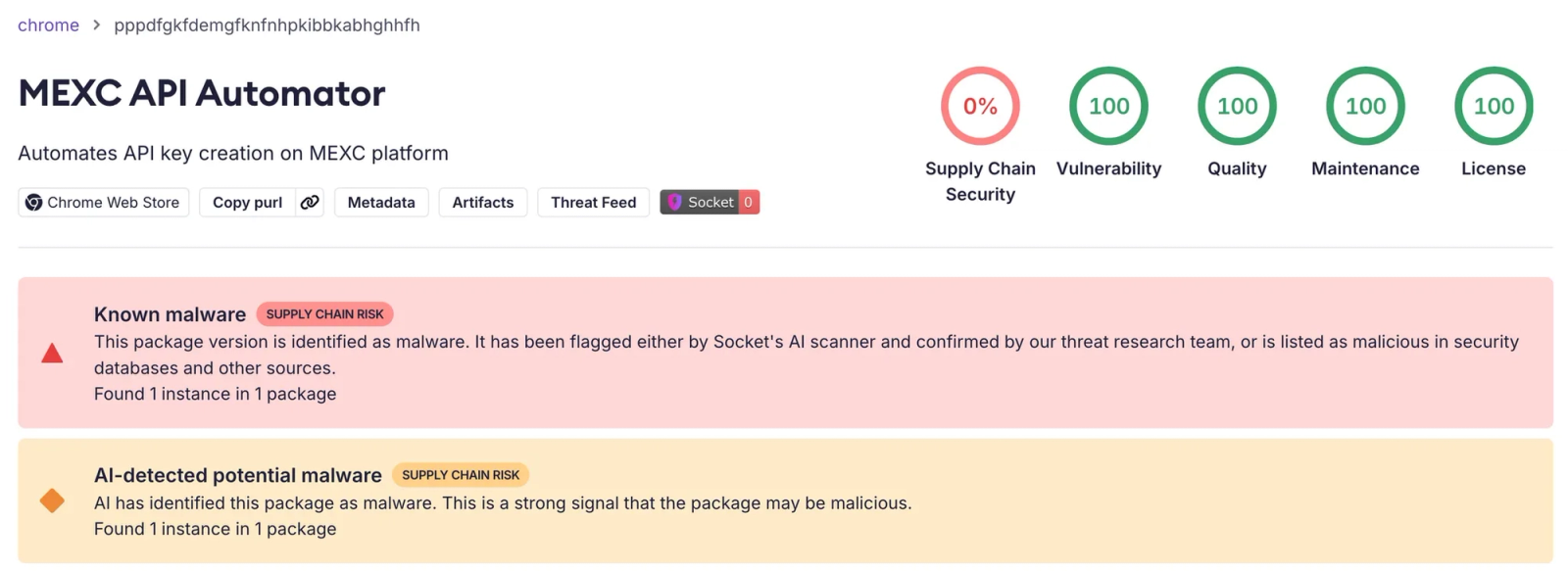
Socket’s Threat Research Team discovered a malicious Chrome extension, MEXC API Automator, that programmatically creates MEXC API keys with withdrawal permissions, hides that permission in the UI, and exfiltrates keys and secrets to a hardcoded Telegram bot, enabling account takeover and fund theft. The extension, published by developer jorjortan142 on the Chrome Web Store, injects script.js into MEXC’s API management page to automate key creation, extract credentials from the success modal, and send them to the actor’s Telegram infrastructure. #MEXC_API_Automator #MEXC

ASEC reported phishing campaigns that distribute malicious PDF files which redirect victims to disguised download pages (e.g., fake Google Drive or adobe-download-pdf[.]com) to install legitimate RMM tools (Syncro, ScreenConnect, NinjaOne, SuperOps) signed with the same certificate. The activity shows repeated use of signed RMM installers and downloaders since at least October…
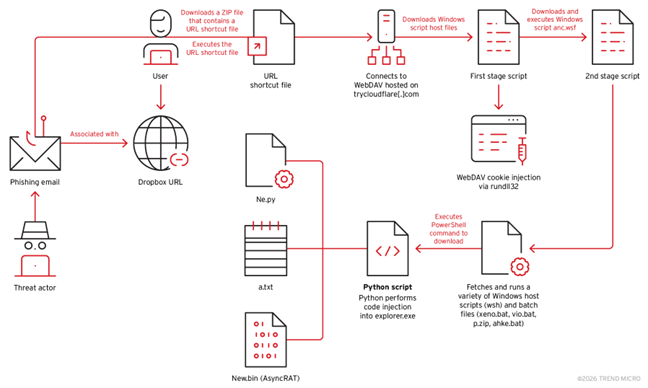
Threat actors abused Cloudflare’s free-tier TryCloudflare tunnels and legitimate Python environments to host WebDAV servers and deliver the AsyncRAT remote access trojan, using double-extension phishing lures and living-off-the-land techniques for persistence. The campaign installs an embedded Python runtime, executes ne.py to APC-inject shellcode from new.bin into explorer.exe, and persists via startup…

In late October 2025, CIS CTI observed increased detections of a fake PDF converter called Crystal PDF on U.S. SLTT endpoints; analysis shows it is a managed .NET (F#) staged loader that performs in-memory execution, process injection, sandbox/VM checks, and contacts likely C2 domains. CIS links its spread to malvertising and…
CrazyHunter is a Go-based ransomware forked from the Prince builder that targets Windows environments—primarily healthcare organizations in Taiwan—using GPO abuse, BYOVD with a vulnerable Zemana driver, memory loaders, and multiple AV-killing components to rapidly propagate and evade defenses. The Trellix analysis details the full attack lifecycle, technical artifacts (including go.exe/go2.exe/go3.exe, bb.exe, crazyhunter.sys), mitigation recommendations, and IOCs for detection and response. #CrazyHunter #SharpGPOAbuse