Socket’s Threat Research Team discovered a malicious Chrome extension, MEXC API Automator, that programmatically creates MEXC API keys with withdrawal permissions, hides that permission in the UI, and exfiltrates keys and secrets to a hardcoded Telegram bot, enabling account takeover and fund theft. The extension, published by developer jorjortan142 on the Chrome Web Store, injects script.js into MEXC’s API management page to automate key creation, extract credentials from the success modal, and send them to the actor’s Telegram infrastructure. #MEXC_API_Automator #MEXC
Keypoints
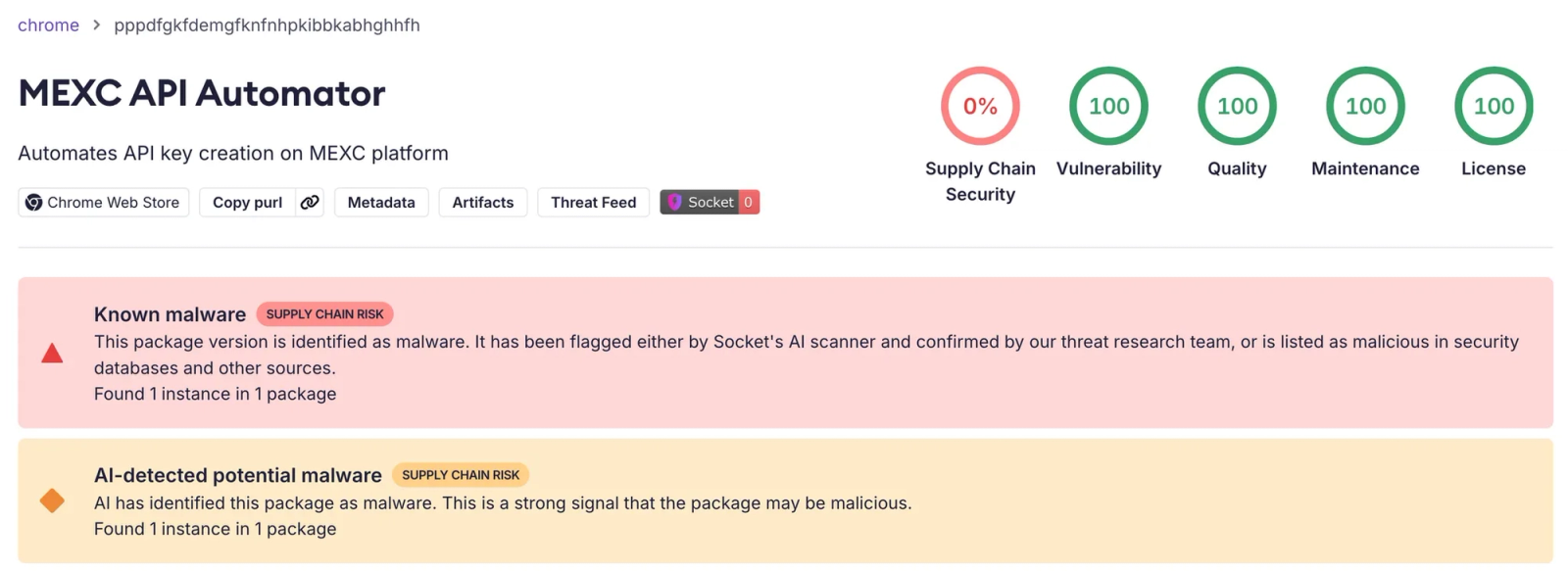
- MEXC API Automator was published to the Chrome Web Store on September 1, 2025 by the alias jorjortan142 and is flagged as malicious by Socket AI Scanner.
- The extension injects a content script (script.js) into MEXC’s /user/openapi page, programmatically selects all permissions, ensures withdrawals are enabled server-side, and hides the withdrawal checkbox visually.
- When a new API key is created, the extension extracts the Access Key and Secret Key from MEXC’s success modal and exfiltrates them via HTTPS POST requests to a hardcoded Telegram bot and chat controlled by the actor.
- Any MEXC account accessed in an infected browser can be fully controlled programmatically—threat actor can execute trades and initiate withdrawals without needing the user’s password or 2FA.
- Indicators link the extension to the SwapSushi-branded infrastructure (X/@jorjortan142, t[.]me/swapsushibot, YouTube channel, swapsushi[.]net) and Russian-language comments in the code suggest a Russian-speaking developer.
- Recommendations include removing the extension, auditing and centrally managing browser extensions, treating API keys as secrets and rotating them, and monitoring exchange logs for anomalous API activity.
MITRE Techniques
- [T1195.002 ] Supply Chain Compromise – The Chrome Web Store was used as the delivery mechanism for the malicious extension (‘the threat actor uses the Chrome Web Store as the delivery mechanism’).
- [T1176.001 ] Software Extensions: Browser Extensions – A malicious Chrome extension injects a content script into MEXC to perform unauthorized actions (‘injects script.js into *://*.mexc.com/user/openapi*’).
- [T1204 ] User Execution – The attack is triggered by normal user behavior: opening the API key management page automatically starts the malicious automation (‘simply opening MEXC’s API key management page is enough to trigger the attack.’).
- [T1059.007 ] Command and Scripting Interpreter: JavaScript – The extension executes JavaScript in the page context to manipulate the form, monitor UI changes, and extract keys (‘the script locates the API key form, programmatically selects every available permission checkbox’).
- [T1552.004 ] Unsecured Credentials: Private Keys – The extension harvests API keys and secrets from the success modal and transmits them in plaintext to the actor (‘extracts both values from the modal, and sends them in a background HTTPS request to a hardcoded Telegram bot’).
- [T1071.001 ] Application Layer Protocol: Web Protocols – Exfiltration occurs over HTTPS to the Telegram Bot API (‘Exfiltrate credentials to Telegram over HTTPS’).
- [T1657 ] Financial Theft – The stolen API keys with withdrawal permissions enable direct theft and draining of wallets reachable via the exchange (‘Drain wallets and balances reachable via MEXC.’).
Indicators of Compromise
- [Chrome Extension ] Malicious extension details and store listing – MEXC API Automator (Extension ID: pppdfgkfdemgfknfnhpkibbkabhghhfh), https://chromewebstore.google.com/detail/mexc-api-automator/pppdfgkfdemgfknfnhpkibbkabhghhfh
- [Telegram Identifiers ] Exfiltration endpoints used by the actor – botToken: 7534112291:AAF46jJWWo95XsRWkzcPevHW7XNo6cqKG9I, chatId: 6526634583
- [Script/File Name ] Injected script operating in-page – script.js (content script injected into /user/openapi to automate key creation and extraction)
- [Email ] Developer registration/contact – jorjortan142@gmail[.]com (listed on the Chrome Web Store developer account)
- [Accounts & Channels ] Associated social infrastructure and profiles – x[.]com/jorjortan142 (SwapSushi), YouTube channel @SwapSushiBot (channel ID UC22QT_xOrH9PWhORCkjGI_As)
- [Domains ] Associated or promoted domains and bot links – t[.]me/swapsushibot, swapsushi[.]net
Read more: https://socket.dev/blog/malicious-chrome-extension-steals-mexc-api-keys