Acronis TRU identified a targeted campaign delivering a DLL-sideloaded backdoor, tracked as LOTUSLITE, via a politically themed ZIP archive aimed at U.S. government and policy-related entities. The implant uses a simple loader/DLL execution chain, hard-coded IP-based C2, basic persistence via a Run key and ProgramData directory, and shows behavioral overlaps with Mustang Panda. #LOTUSLITE #MustangPanda
Category: Threat Research
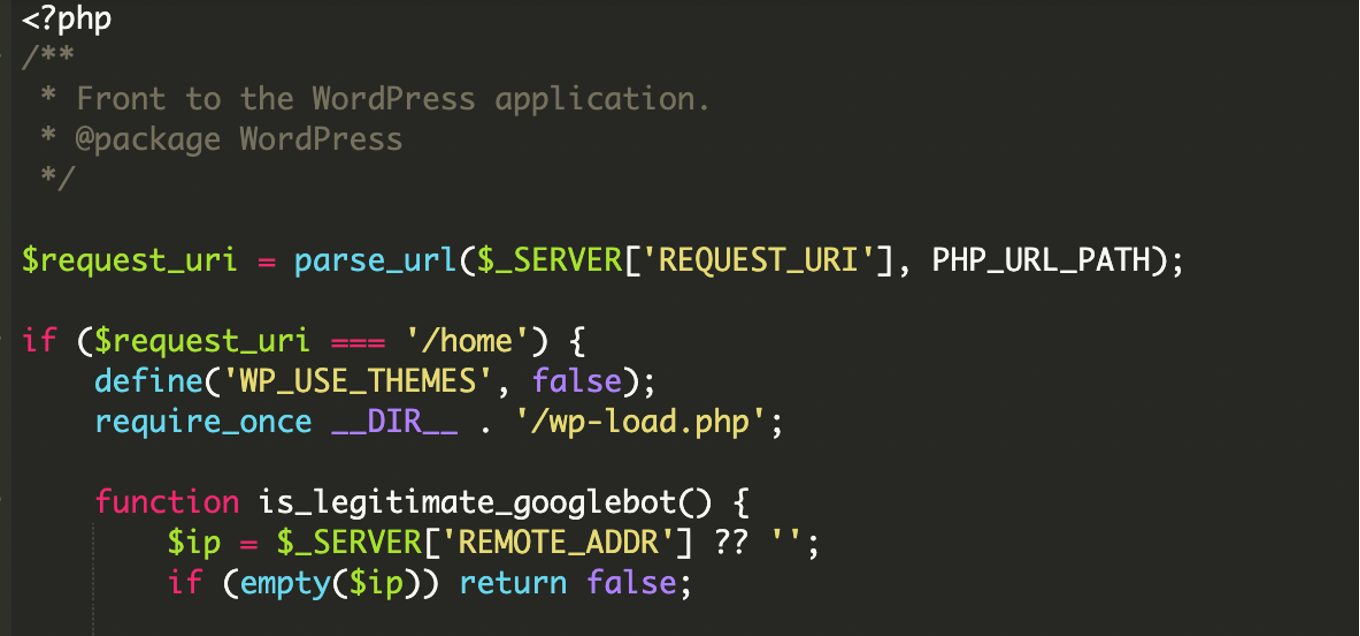
Researchers found a selective content injection in a WordPress index.php that serves malicious remote content to search engine crawlers while showing the normal site to human visitors. The script uses a hardcoded library of Google ASN CIDR ranges and bitwise IP verification, fetching payloads via hxxps://amp-samaresmanor[.]pages[.]dev and risking SEO blacklisting and deindexing. #WordPress #amp-samaresmanor_pages_dev
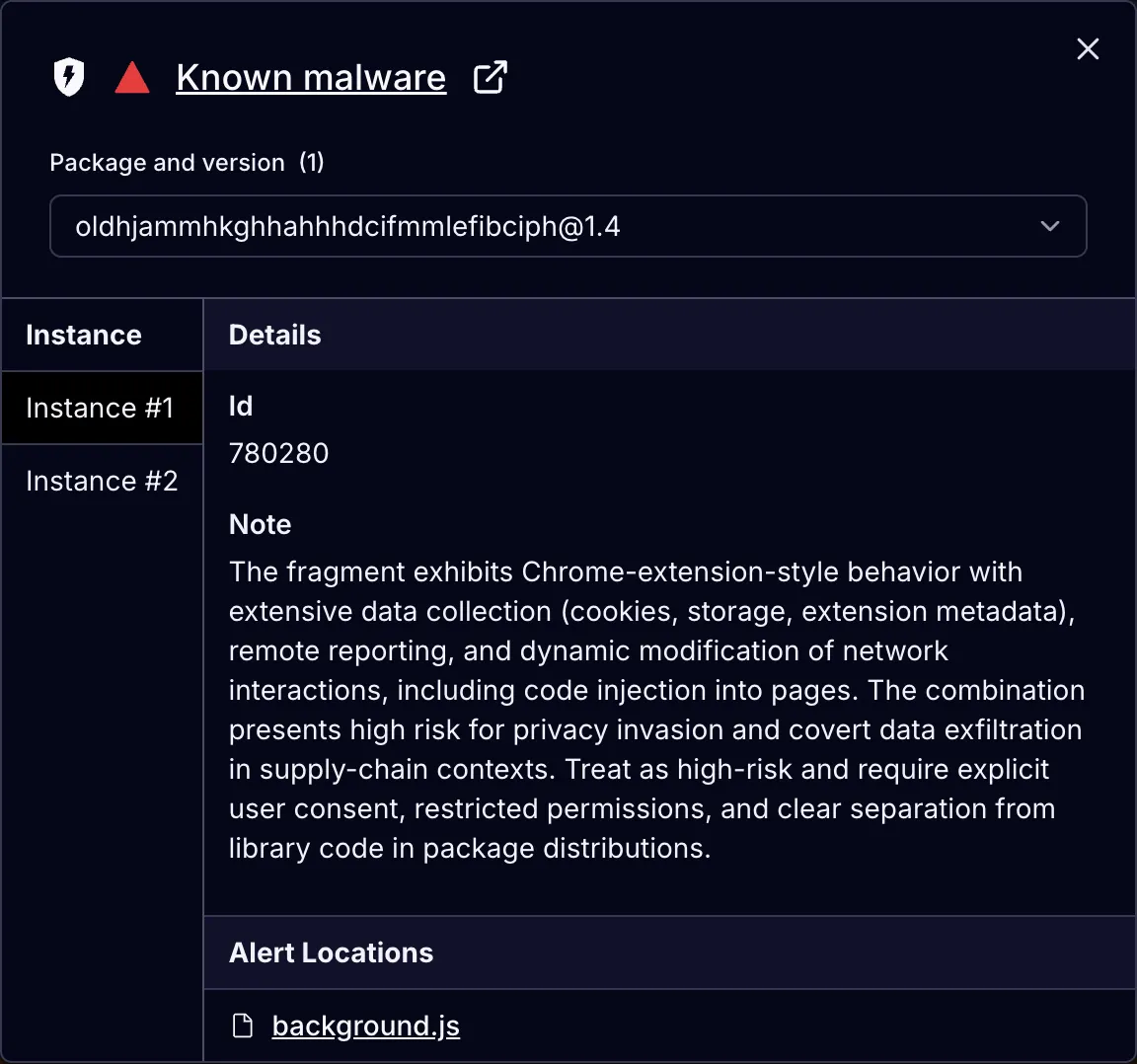
Five malicious Chrome extensions impersonating productivity tools targeted enterprise HR and ERP platforms (Workday, NetSuite, SuccessFactors) to continuously exfiltrate __session authentication tokens, block administrative incident-response pages, and enable full account takeover via session hijacking. The extensions (four under databycloud1104 and one under softwareaccess) share identical code structures, detection lists, and API patterns, communicating with api.databycloud[.]com and api.software-access[.]com and reaching over 2,300 users. #DataByCloud #SoftwareAccess

Intelligence-driven detection that combines endpoint/XDR, network detection, and threat intelligence enables earlier identification of ransomware precursor behaviors like reconnaissance, credential theft, and data staging before encryption occurs. Recorded Future and similar platforms strengthen detection by providing organization-specific, real-time context on active campaigns, attacker infrastructure, and vulnerabilities prioritized by what ransomware operators are actually exploiting. #LockBit #RecordedFuture

Sicarii is a newly observed RaaS operation that combines functional ransomware capabilities (data exfiltration, credential harvesting, LSASS dumping, network reconnaissance, Fortinet exploitation, and AES-GCM encryption adding a .sicarii extension) with unusually explicit Israeli/Jewish branding and geo-fencing that prevents execution on Israeli systems. The group’s public behavior, linguistic inconsistencies, performative identity signaling, and early-stage testing artifacts (VirusTotal uploads, Project3.exe, ransomawre.cs) suggest an immature or possibly false-flag operation rather than a mature ideologically driven actor. #Sicarii #CVE-2025-64446
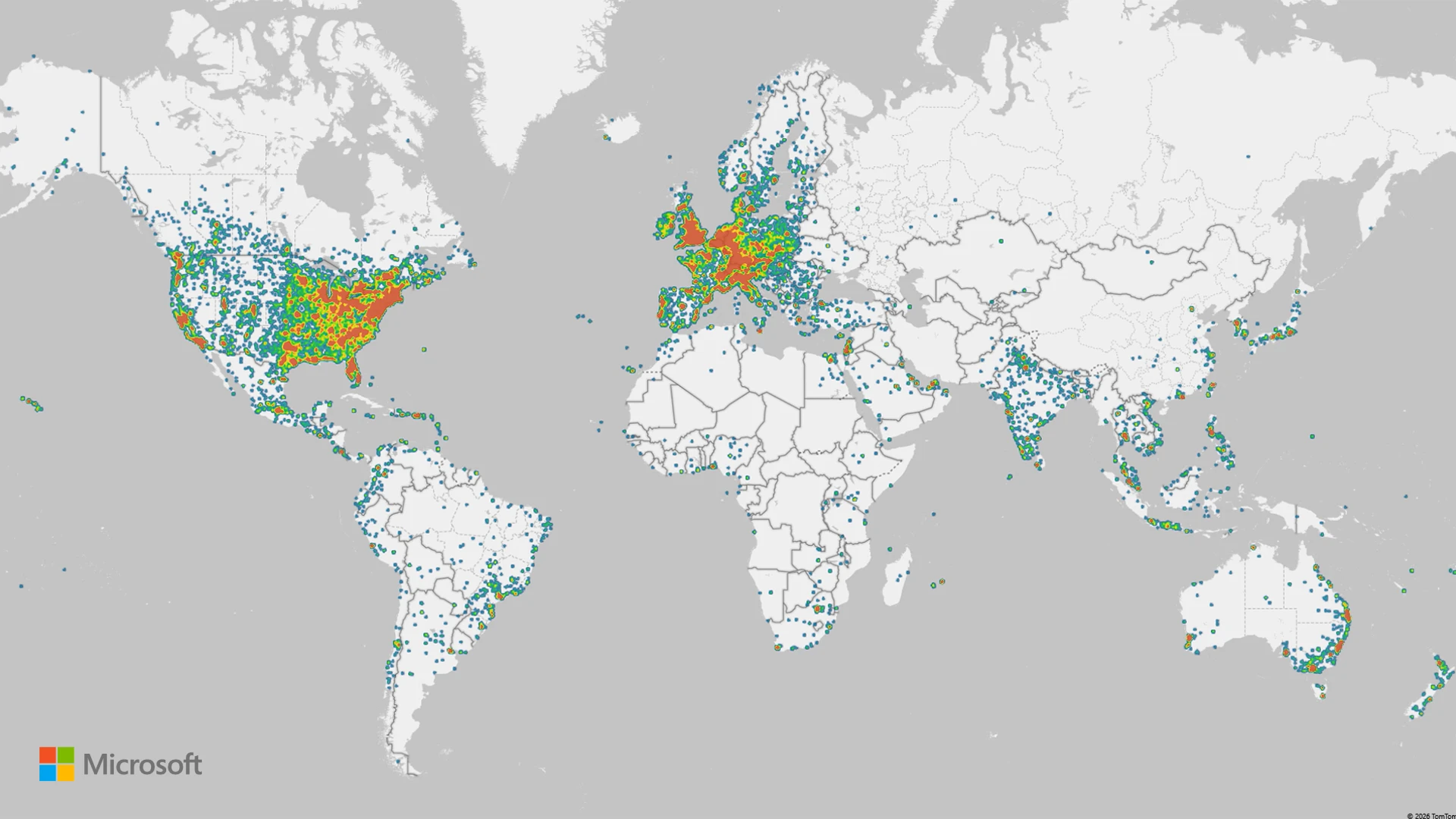
Microsoft Threat Intelligence exposed RedVDS, a criminal VDS marketplace operated by the actor tracked as Storm-2470 that sold cloned Windows Server 2022 RDP hosts and enabled mass phishing, BEC, account takeover, and large-scale financial fraud across multiple countries and sectors. Microsoft, in coordination with law enforcement, disrupted RedVDS infrastructure and published detections, IOCs, and mitigation guidance to reduce impact and harden defenses. #RedVDS #Storm-2470
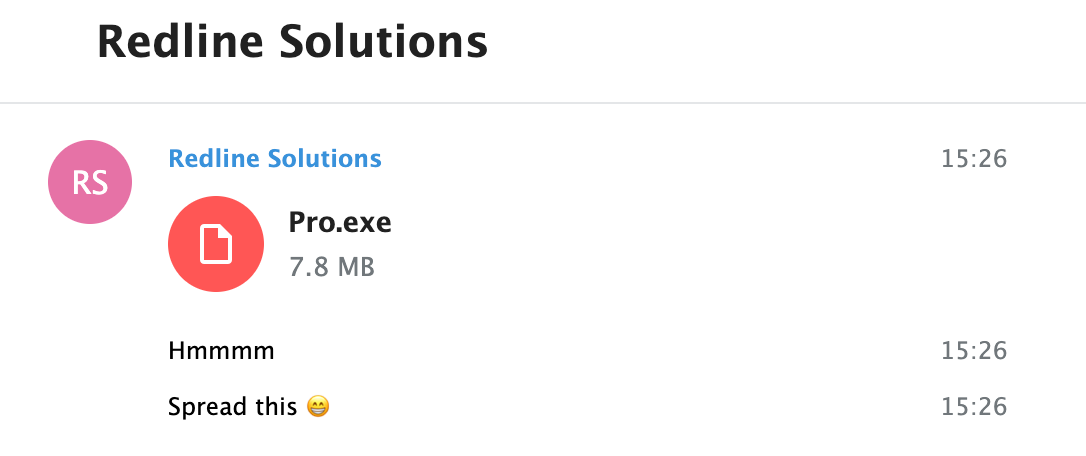
CloudSEK STRIKE’s HUMINT uncovered a false-flag campaign by an actor using the alias “RedLineCyber” who distributes a PyInstaller-packed clipboard hijacker via Discord and Telegram, targeting cryptocurrency streamers and gambling communities. The malware, distributed as Pro.exe (also peeek.exe), monitors the Windows clipboard and silently replaces copied crypto addresses with attacker-controlled wallets for six cryptocurrencies while persisting via an HKCU Run key. #RedLineCyber #Pro.exe

The article analyzes a Konni-attributed malicious shortcut named “국가안보연보고서2.hwp.lnk” that uses a hidden PowerShell command to locate a 2,116,116-byte container file, extract three hex-encoded payload segments, recreate three files (attach.hwp, heidi.db, heidisqls.exe), open the decoy HWP and execute the dropped EXE with the DB file as an argument. It documents the sample’s file hashes and disk IOCs and notes execution techniques (hidden window, ExecutionPolicy bypass) and a behavioral similarity to RoKRAT. #Konni #국가안보연보고서2

Iru researchers uncovered a Mach-O binary named Portfolio_Review.exe that masquerades as a Windows .exe and contains a PyInstaller CArchive bundling a portfolio_app.pyc payload researchers named MonetaStealer. MonetaStealer—still in early development and relying heavily on AI code—targets Chrome credentials/cookies/history, crypto wallets, macOS Keychain and Wi‑Fi credentials, stages data to STOLEN{sessionID}.zip and uses api.telegram.org for reporting while remaining undetected on VirusTotal. #MonetaStealer #Iru

This article explains CVE-2020-8554, an unpatchable Kubernetes vulnerability that allows a user who can create Service objects to hijack traffic intended for external IP addresses by leveraging ExternalIP services and kube-proxy’s iptables rules. It shows a proof-of-concept redirecting traffic for icanhazip.com to an in-cluster echoserver, describes how kube-proxy generates NAT rules for services, and outlines mitigations such as blocking ExternalIP services with DenyServiceExternalIPs or Kyverno and using Cilium’s kube-proxy replacement. #CVE-2020-8554 #kube-proxy

On January 13, 2026, Node.js released a security update that fixes a bug where async context tracking caused stack overflows to terminate processes immediately instead of throwing catchable RangeError exceptions. The flaw impacted many production applications and observability tools (including React Server Components, Next.js, Datadog, New Relic, Elastic APM, Dynatrace, and OpenTelemetry) and was patched in Node.js 20.20.0, 22.22.0, 24.13.0, and 25.3.0, though maintainers warned the fix is a mitigation and stack exhaustion remains inherently unreliable to recover from. #Node.js #AsyncLocalStorage

SentinelLABS researcher Jim Walter explains how nation-states and mercenary groups increasingly exploit hacktivist personas to obscure intent, destabilize targets, and weaponize public narratives. Using a four-tier pyramid framework and examples such as Anon Sudan and MeteorExpress, he concludes that much high-impact “hacktivism” is actually state-sponsored “fictivism” employed for plausible deniability and strategic influence. #AnonSudan #MeteorExpress

The 2025 cyber-extortion epidemic reached record levels driven by a rise in encryptionless extortion—attackers increasingly steal data (often via zero-days or supply-chain weaknesses) and threaten leaks instead of using encryption. This trend coexists with persistent ransomware activity and the rapid expansion of actors such as Akira and Qilin following the disruption of LockBit and RansomHub. #Snakefly #OracleEBS
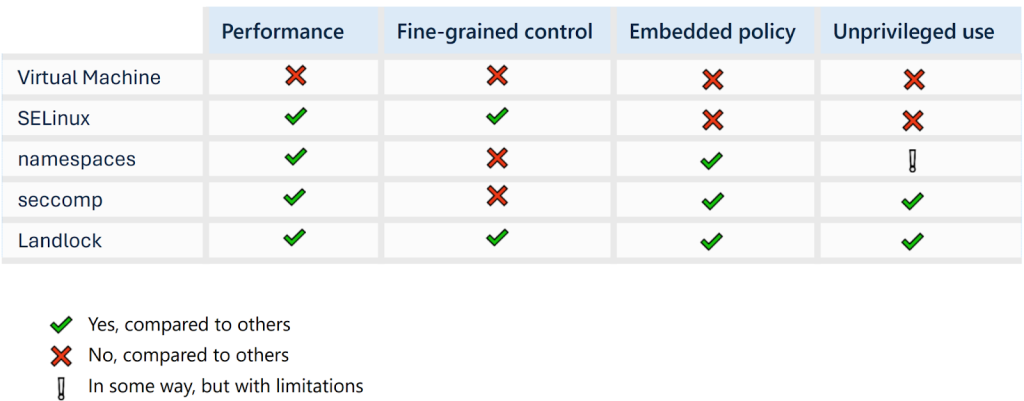
Landlock, a Linux Security Module integrated since kernel 5.13 with logging in 6.15, can both harden applications and provide precise, low-false-positive telemetry for detection engineering. The article demonstrates Landlock’s logging for filesystem and network denials, use in tools like XZ Utils, and how Sekoia leverages go-libaudit logs to create Sigma detections. #Landlock #XZUtils
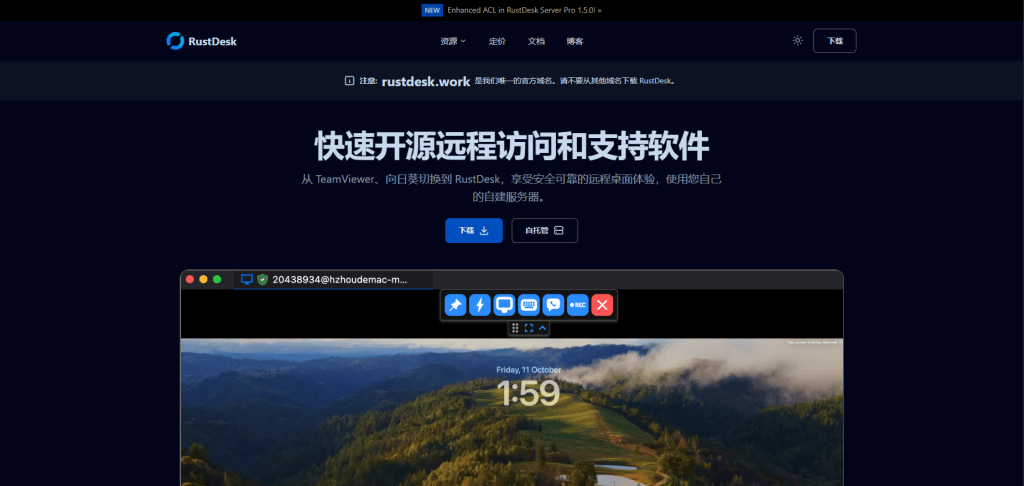
Attackers registered a convincing fake RustDesk site (rustdesk[.]work) that distributed a trojanized installer which installed both the real RustDesk client and a hidden backdoor, Winos4.0. The backdoor runs largely in memory, captures screenshots and keystrokes, and establishes C2 communications to 207.56.13[.]76:5666 to exfiltrate data and receive commands. #RustDesk #Winos4.0…
