Five malicious Chrome extensions impersonating productivity tools targeted enterprise HR and ERP platforms (Workday, NetSuite, SuccessFactors) to continuously exfiltrate __session authentication tokens, block administrative incident-response pages, and enable full account takeover via session hijacking. The extensions (four under databycloud1104 and one under softwareaccess) share identical code structures, detection lists, and API patterns, communicating with api.databycloud[.]com and api.software-access[.]com and reaching over 2,300 users. #DataByCloud #SoftwareAccess
Keypoints
- Five Chrome extensions marketed as productivity/security tools target Workday, NetSuite, and SuccessFactors to steal session tokens, block admin/security pages, and perform session hijacking.
- Four extensions are published under databycloud1104 and a fifth under softwareaccess; all share identical API paths (/api/v1/mv3), code patterns, and a 23-extension detection list, indicating a coordinated campaign.
- Three distinct attack types are used: periodic cookie exfiltration to remote C2 servers, DOM manipulation to erase and redirect administrative pages, and bidirectional cookie injection enabling direct account takeover.
- DataByCloud Access and Data By Cloud 1 exfiltrate __session cookies every 60 seconds; Tool Access 11 and Data By Cloud 2 block 44–56 administrative pages including password changes and device management; Software Access both exfiltrates and injects cookies via chrome.cookies.set().
- Anti-analysis techniques include a Vigenère-like C2 encryption variant, extensive variable minification, DisableDevtool anti-debugging, and password field protections that revert DevTools-based inspection attempts.
- Disposable or non-functional frontend infrastructure (404s and Cloudflare 525 errors) and missing legitimate product sites indicate malicious C2-only infrastructure at api.databycloud[.]com and api.software-access[.]com.
- Recommended mitigations include removing the listed extensions, enforcing Chrome Enterprise allowlists, blocking the C2 domains, auditing authentication logs, and forcing password resets from clean systems.
MITRE Techniques
- [T1539 ] Steal Web Session Cookie – Extensions extract and exfiltrate session cookies (targeting __session) to remote APIs for credential theft (‘extracts authentication cookies and exfiltrates them to api[.]databycloud[.]com every 60 seconds’).
- [T1185 ] Browser Session Hijacking – Software Access injects stolen cookies into the browser to gain authenticated access without credentials (‘injects them into the browser using chrome.cookies.set() to enable direct session hijacking’).
- [T1176.001 ] Browser Extensions – Malicious functionality is delivered via Chrome extensions that request cookie and scripting permissions and operate in the browser context (‘Five malicious Chrome extensions targeting enterprise HR and ERP platforms’).
- [T1027 ] Obfuscated Files or Information – Command-and-control traffic and code are obfuscated using a Vigenère-like cipher and variable minification to hinder analysis (‘encrypt their command and control traffic using a Vigenère cipher variant’ and ‘extensive variable name minification’).
- [T1562.001 ] Disable or Modify Tools – Extensions disable inspection and block administrative tools via DOM manipulation and DisableDevtool to prevent remediation and analysis (‘includes the DisableDevtool library to prevent code inspection’ and ‘erases the page and forces navigation’).
Indicators of Compromise
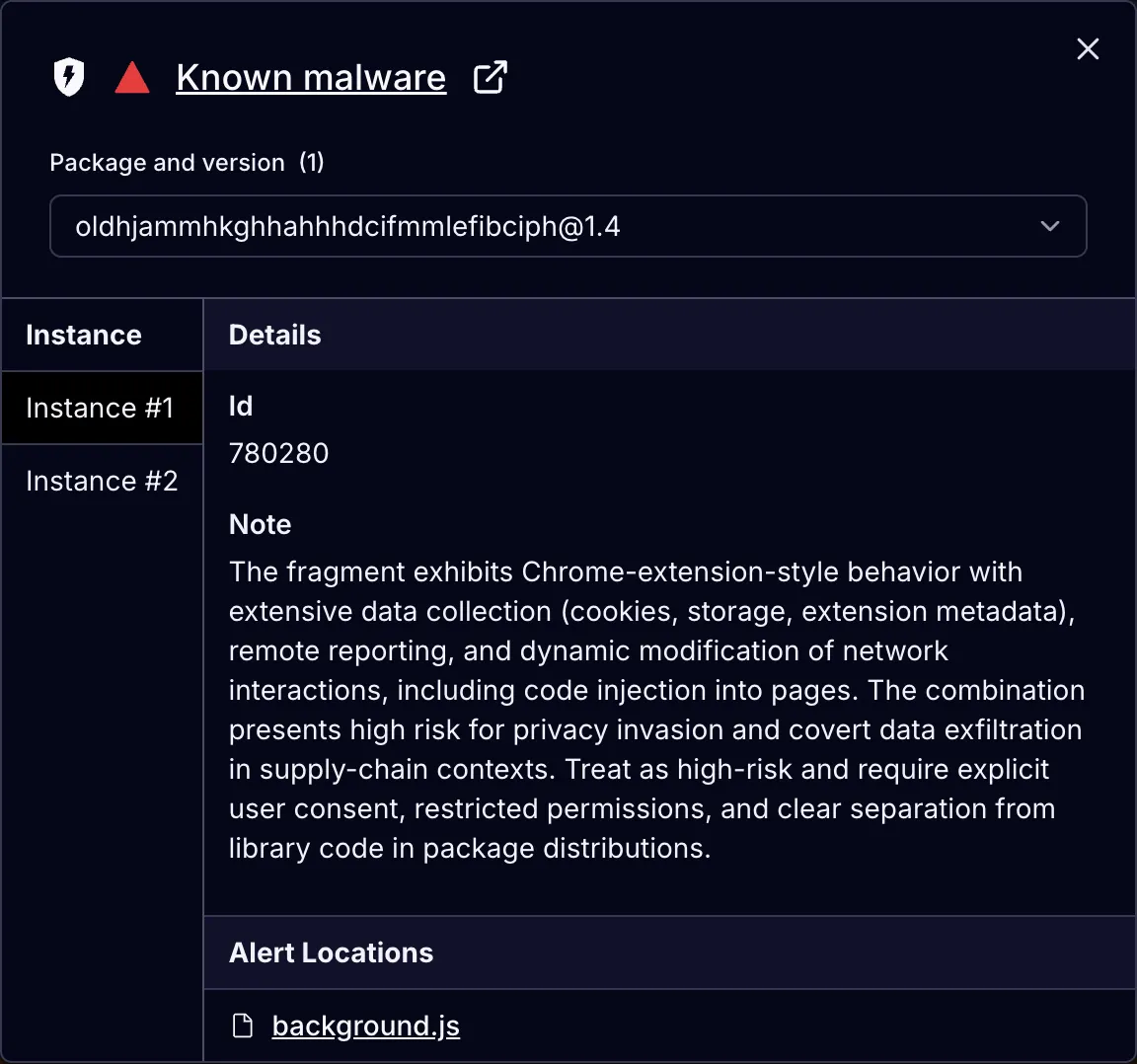
- [Extension Names/IDs ] Malicious Chrome extensions and their IDs – DataByCloud Access (oldhjammhkghhahhhdcifmmlefibciph), Tool Access 11 (ijapakghdgckgblfgjobhcfglebbkebf), and other listed extension IDs.
- [Domains / API Endpoints ] Command-and-control infrastructure – api[.]databycloud[.]com/api/v1/mv3, api[.]software-access[.]com/api/v1/mv3, wss://api[.]software-access[.]com.
- [Registered Names/Emails ] Threat actor registration metadata – databycloud1104 / [email protected], softwareaccess / [email protected].
- [Affected Platforms / Hostnames ] Targeted enterprise services – myworkday.com (and workdaysuv.com sandbox), netsuite.com, successfactors.com (and sapsf.eu variants).
- [Subdomains / Admin Hosts ] Additional infrastructure endpoints – user[.]software-access[.]com, admin[.]software-access[.]com.
Read more: https://socket.dev/blog/5-malicious-chrome-extensions-enable-session-hijacking