Researchers found a selective content injection in a WordPress index.php that serves malicious remote content to search engine crawlers while showing the normal site to human visitors. The script uses a hardcoded library of Google ASN CIDR ranges and bitwise IP verification, fetching payloads via hxxps://amp-samaresmanor[.]pages[.]dev and risking SEO blacklisting and deindexing. #WordPress #amp-samaresmanor_pages_dev
Keypoints
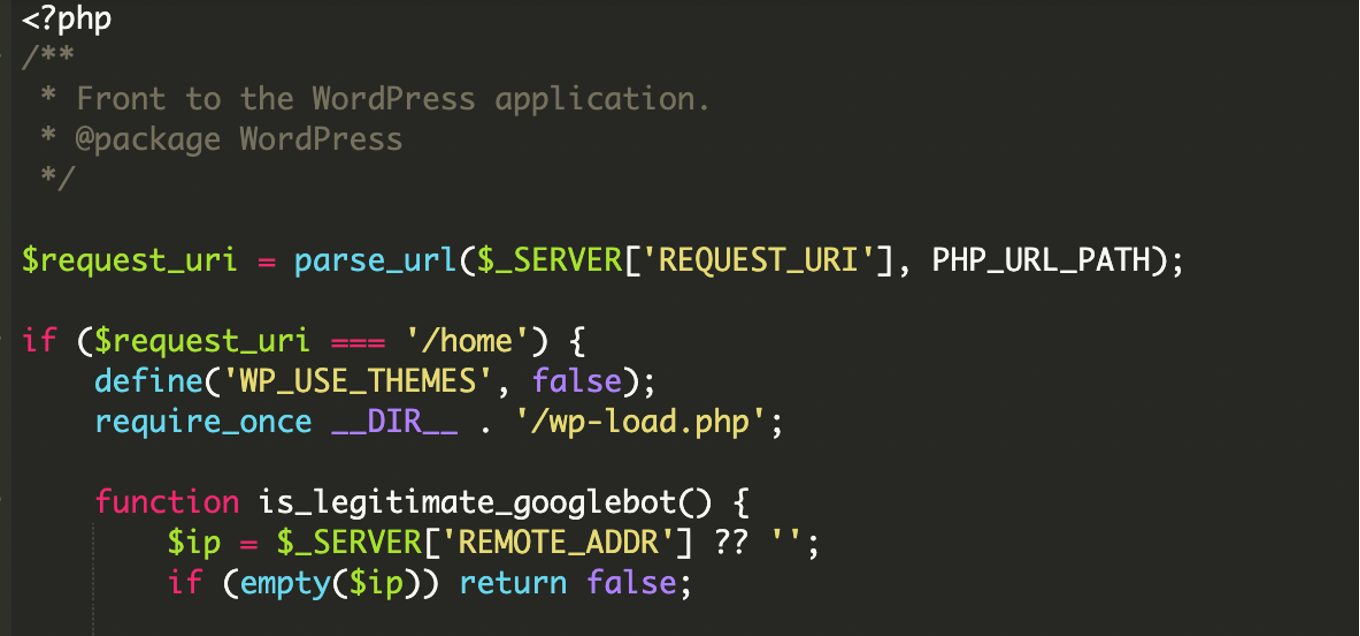
- Attackers modified the main index.php of a WordPress site to selectively serve external content only to search engine infrastructure.
- The malware performs multi-layer verification: User-Agent filtering plus bitwise IP/CIDR validation against a hardcoded list of Google ASN ranges (including IPv6 support).
- Verified bots receive remote content pulled via cURL from hxxps://amp-samaresmanor[.]pages[.]dev, which is printed directly to the page to appear native to search engines.
- The infection focuses on SEO manipulation and can cause search engine blacklisting, deindexing, resource hijacking, and delayed detection.
- Indicators include recently modified core files (index.php), suspicious remote URLs, unusual log entries, and unexpected Google Search results for the site.
- Recommended mitigations: remove malicious files, audit and remove suspicious admin users, reset credentials, scan endpoints, update components, use a WAF, and implement File Integrity Monitoring and Search Console audits.
MITRE Techniques
- [T1036 ] Masquerading – Cloaking to present different content to search engine crawlers while hiding malicious behavior from normal visitors (‘This approach filters out regular human visitors, allowing attackers to serve malicious content to search engine crawlers while remaining invisible to the website owner.’)
- [T1105 ] Ingress Tool Transfer – Remote payload retrieval and injection using cURL to fetch external content that is served to verified crawlers (‘the script uses cURL to fetch content from an external pages URL:hxxps://amp-samaresmanor[.]pages[.]dev.’)
- [T1071.001 ] Web Protocols – Use of HTTP(S) application-layer protocols to deliver fetched content and make it appear native to search engines (‘This content is printed directly to the page, making the search engine believe the site is hosting this content natively.’)
Indicators of Compromise
- [Domain ] Malicious remote content host – amp-samaresmanor[.]pages[.]dev
- [File name ] Modified WordPress core file used as gatekeeper – index.php
- [File path ] WordPress bootstrap and header files referenced by the malware – wp-load.php, wp-blog-header.php
- [User-Agent strings ] Crawler verification and filtering targets – examples include ‘Googlebot’ and other Google verification/inspection/API crawler strings
- [IP ranges/CIDR ] Hardcoded Google ASN CIDR blocks used for IP verification – Google ASN CIDR ranges (no specific public ranges listed in the article); example CIDR format shown: 192.168.1.0/24
Read more: https://blog.sucuri.net/2026/01/malware-intercepts-googlebot-via-ip-verified-conditional-logic.html