CERT-AGID has identified a SPID-themed phishing campaign that uses deceptive emails linking to a fake SPID portal hosted on Google Sites to collect personal and banking data. The fraudulent pages request names, addresses, contact details and IBANs; CERT-AGID requested takedown of the hosting site and distributed IoCs via its feed to accredited structures. #SPID #CERT-AGID #GoogleSites #AgID #DipartimentoPerLaTrasformazioneDigitale
Category: Threat Research
KongTuke distributed a malicious Chrome extension (NexShield, typosquatting uBlock Origin Lite) that tracks installs via UUID beacons, delays execution, and triggers a browser denial-of-service while displaying a fake “CrashFix” popup to socially engineer victims. The campaign delivers a multi-stage infection chain—using finger.exe as a LOLBin, multi-layer PowerShell obfuscation and DGA domains, and culminating in ModeloRAT and a GateKeeper .NET payload with AES+XOR string encryption. #KongTuke #ModeloRAT
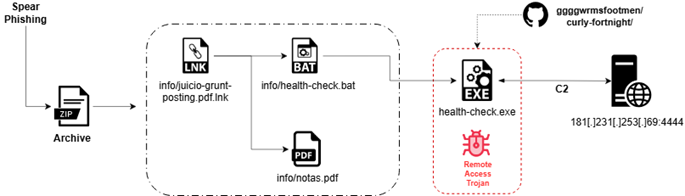
Seqrite Labs uncovered “Operation Covert Access,” a targeted spear-phishing campaign that abuses authentic Argentine federal court documents to deliver a multi-stage Rust-based Remote Access Trojan (CovertRAT) via a weaponized LNK, BAT loader, and a GitHub-hosted second-stage binary. The implant demonstrates extensive anti-VM/anti-debug checks, IPv4/IPv6 C2 fallback (default 181.231.253.69:4444), and a modular command set for persistence, data theft, file transfer, encryption, and privilege escalation. #CovertRATCiR #ArgentinaJudicialSector

AhnLab confirmed a Remcos RAT campaign targeting users in South Korea that uses fake blocklist‑lookup tools for illegal gambling sites and counterfeit VeraCrypt installers to distribute multi‑stage droppers. The attack chain leverages obfuscated VBS/PowerShell scripts, a .NET injector that sends logs via Discord webhooks and injects Remcos into AddInProcess32.exe, with IOCs…
SolyxImmortal is a Python-based Windows information-stealer that persistently collects browser credentials, documents, keystrokes, and screenshots and exfiltrates them via hardcoded Discord webhooks. The sample Lethalcompany.py establishes registry Run-key persistence, stages and compresses artifacts for stealthy long-term surveillance rather than propagation. #SolyxImmortal #Discord
Sysdig TRT’s analysis of VoidLink describes a Chinese-developed, Zig-built Linux malware framework that uses a three-stage fileless loader, serverside rootkit compilation (SRC) to produce kernel modules per-target, and multiple stealth/control channels including prctl, eBPF, and an ICMP covert channel. Despite advanced adaptive evasion, VoidLink’s memfd_create/execveat fileless execution, eBPF and kernel-module activity, and other runtime behaviors are detectable with tools like Falco and Sysdig Secure. #VoidLink #Sysdig

Mamba Phishing-as-a-Service Kit: How Modern adversary-in-the-middle (AiTM) Attacks Operate – CYFIRMA
CYFIRMA assesses Mamba 2FA is a scalable adversary-in-the-middle phishing framework that automates realistic Microsoft authentication flows to capture credentials, bypass MFA, and relay sessions with minimal user interaction. The report highlights encoded URL parameters, Microsoft-style password prompts, client-side password capture, rapid redirection to legitimate sites, and recommends hardened identity controls such as FIDO2/WebAuthn and continuous monitoring to mitigate risk. #Mamba2FA #Microsoft365
Orion Ransomware is a newly observed operation whose public activity is limited to a data leak site listing 13 alleged victims and affiliate recruitment messaging rather than demonstrated ransomware development or independently verified intrusions. Analysis links the operator to prior reputation-driven extortion activity associated with Babuk2, indicating recycled leak material and low confidence in original operational capability. #Orion #Babuk2
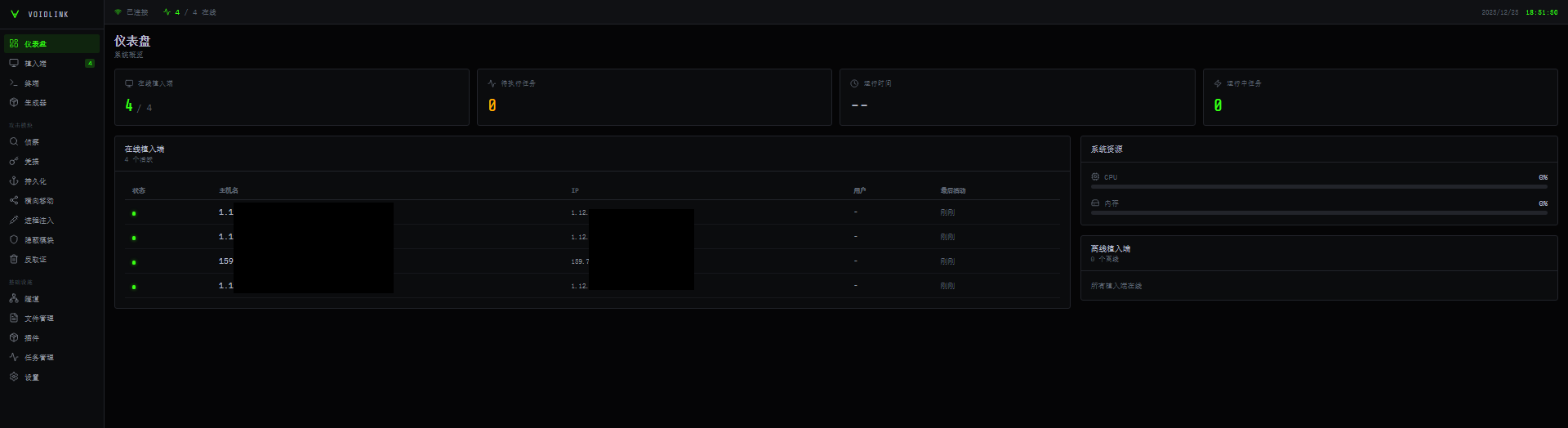
VoidLink is an advanced, modular Linux command-and-control framework designed for long-term stealthy access in cloud and container environments, featuring a Zig-written core, a web-based C2 dashboard, and a BOF-like plugin API. It includes 30+ plugins (credential harvesting, container escape, persistence), multiple rootkit techniques (LD_PRELOAD, LKM, eBPF), adaptive OPSEC, and multi-protocol C2 capabilities. #VoidLink #Kubernetes

Cyble’s analysis describes deVixor, an evolving Android banking RAT distributed via fake automotive websites that deploy malicious APKs to Iranian users to harvest SMS-based financial data, capture credentials, perform keylogging, and surveil devices. The malware now includes WebView-based JavaScript injection, a remotely triggered ransomware module, and uses Telegram and Firebase for command-and-control and large-scale administration. #deVixor #IranianBanks

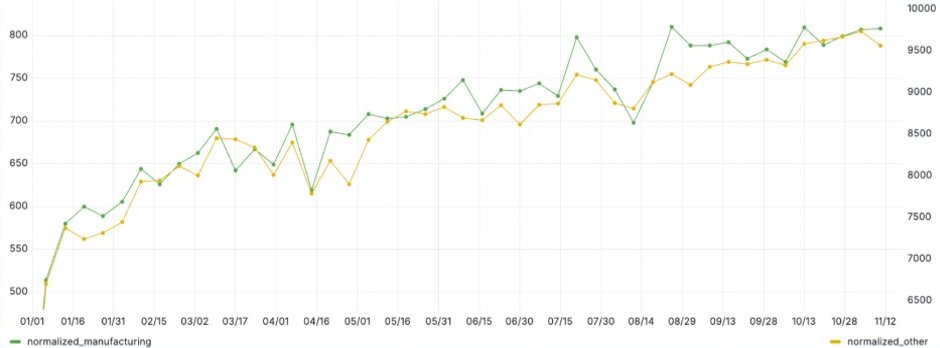
The report summarizes December 2025 ransomware activity, providing DLS-based victim counts, ransomware sample statistics (based on AhnLab diagnostic names), and trend data for top groups and affected industries. It notes a changed aggregation method for victim counts starting December 2025 and highlights active operations by groups such as Qilin and LockBit…

In December 2025 AhnLab ASEC observed heavy distribution of Infostealer families—ACRStealer, LummaC2, and Stealc—primarily disguised as cracks/keygens and spread via SEO-poisoned posts on legitimate websites and compromised WordPress sites. Distribution methods included EXE droppers, DLL sideloading, Python script tampering, and Tor-backed cryptocurrency‑stealing campaigns that monitor clipboards and exfiltrate BIP39 phrases. #ACRStealer…
Manufacturing companies are being actively targeted with localized invoice-themed phishing that leverages CVE-2024-43451 and WebDAV-based shortcuts to deliver AsyncRAT and XWorm. Proactive, industry- and region-specific threat hunting using ANY.RUN’s sandbox and Threat Intelligence Lookup can identify fresh samples, file hashes, malicious filenames, and hosting infrastructure (Dropbox/WebDAV) before widespread detection occurs. #AsyncRAT…

FortiGuard Labs analyzed a phishing campaign that delivers a fileless variant of the Remcos RAT via a malicious Word document that downloads a crafted RTF exploiting CVE-2017-11882 to execute shellcode and launch VBScript and PowerShell loaders. The attack results in in-memory loading of a .NET module and process hollowing to deploy Remcos (version 7.0.4 Pro), with persistence via a scheduled task and C2 communications to 216.9.224.26:51010. #Remcos #CVE_2017_11882

Acronis TRU identified a targeted campaign delivering a DLL-sideloaded backdoor, tracked as LOTUSLITE, via a politically themed ZIP archive aimed at U.S. government and policy-related entities. The implant uses a simple loader/DLL execution chain, hard-coded IP-based C2, basic persistence via a Run key and ProgramData directory, and shows behavioral overlaps with Mustang Panda. #LOTUSLITE #MustangPanda