Seqrite Labs uncovered “Operation Covert Access,” a targeted spear-phishing campaign that abuses authentic Argentine federal court documents to deliver a multi-stage Rust-based Remote Access Trojan (CovertRAT) via a weaponized LNK, BAT loader, and a GitHub-hosted second-stage binary. The implant demonstrates extensive anti-VM/anti-debug checks, IPv4/IPv6 C2 fallback (default 181.231.253.69:4444), and a modular command set for persistence, data theft, file transfer, encryption, and privilege escalation. #CovertRATCiR #ArgentinaJudicialSector
Keypoints
- Attackers targeted Argentina’s judicial sector with highly authentic decoy PDFs purporting to be federal court resolutions to increase user trust and likelihood of interaction.
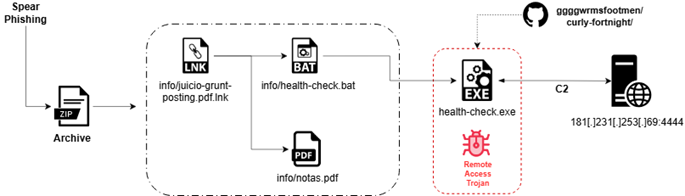
- Initial delivery used a ZIP archive containing a malicious LNK (info/juicio-grunt-posting.pdf.lnk), a BAT loader (info/health-check.bat), and a decoy PDF (info/notas.pdf) to hide the execution chain.
- The LNK stealthily launches PowerShell with execution policy bypass and hidden window to run the BAT loader, which downloads a second-stage binary from a GitHub URL and saves it as msedge_proxy.exe in an Edge user-data directory.
- The msedge_proxy.exe implant is Rust-based and implements extensive anti-VM, sandbox, and anti-debug checks (WMIC checks, registry and file-path checks, tasklist scans, PEB/timing checks) to evade analysis and terminate on detection.
- The RAT establishes resilient C2 connectivity with IPv4/IPv6 parsing and a hardcoded fallback (181.231.253.69:4444), advertises Base64-encoded commands, and supports persistence, file upload/download, harvesting, encryption/decryption, and privilege escalation modules.
- Seqrite detections (Trojan.50322.SL, Trojan.50321.SL, CovertRATCiR) and published IOCs (file hashes, filenames, and C2 IP) accompany the disclosure to aid detection and response.
MITRE Techniques
- [T1566.001 ] Spearphishing Attachment – Used as the initial vector delivering a ZIP with malicious LNK/BAT and decoy PDF (‘spear-phishing emails containing a ZIP archive’).
- [T1204.002 ] User Execution: Malicious File – Reliance on user opening the LNK/pdf decoy to execute the loader (‘weaponized LNK file … upon user interaction with the LNK file, the execution chain is initiated’).
- [T1059.003 ] Windows Command Shell – Batch loader and spawned cmd processes were used to perform registry and environment checks (‘EXE file exhibits environment and virtualization detection behaviour by spawning multiple command-line processes’).
- [T1059.001 ] PowerShell – LNK launches PowerShell with execution policy bypass and hidden window to download and execute the second-stage payload (‘-ep bypass -w hidden -f health-check.bat’ and PowerShell downloading from GitHub).
- [T1059 ] Command-Line Interface – Command-line utilities and arguments (schtasks, reg add, Start-Process) are used across stages for execution and persistence (‘Creates tasks via schtasks … adds values under HKCU … using reg add’).
- [T1106 ] Native API – Native Windows APIs and system calls are used for low-level checks and operations (anti-debug/PEB checks and system information collection) (‘IsDebuggerPresent and the PEB’s BeingDebugged flag’).
- [T1053.005 ] Scheduled Task Execution – Persistence implemented via scheduled tasks created with schtasks including /RL HIGHEST and cleanup routines (‘Creates tasks via schtasks with /TN, /TR, /DELAY0001:00’).
- [T1036.004 ] Masquerading (LNK as PDF) – Shortcut file disguised with a PDF icon and name to masquerade as a legitimate document (‘Masquerading (LNK as PDF)’ and LNK uses a PDF icon to deceive users).
- [T1036.005 ] Masquerading (Legitimate Name or Location) – The downloaded binary is named and placed to resemble legitimate Edge components (‘saves it as msedge_proxy.exe within the Microsoft Edge user data directory, using a trusted filename and location’).
- [T1564.003 ] Hidden Window – PowerShell and other processes are launched with hidden windows to avoid user detection (‘-w hidden’ and runs in hidden mode to avoid user visibility).
- [T1027 ] Obfuscated / Encoded Commands (Base64) – C2 commands are Base64-encoded and decoded by the agent before execution (‘Commands arrive encoded in BASE64 … The decoding procedure decodes 4-byte sequences at a time’).
- [T1140 ] Deobfuscate / Decode Files or Information – The implant includes decoding routines to reconstruct commands and payloads from encoded streams (‘agent::base64_decode … This proves C2 commands are always base64-encoded’).
- [T1562.001 ] Execution Policy Bypass – PowerShell invocation uses execution policy bypass to run unsigned scripts (‘-ep bypass’ used in PowerShell command line).
- [T1112 ] Modify Registry – The implant adds and removes Run key entries for persistence under HKCU (‘Adds values under HKCUSoftwareMicrosoftWindowsCurrentVersionRun using reg add’).
- [T1497 ] Virtualization / Sandbox Evasion – The RAT performs broad VM/sandbox detection and exits if indicators are present (‘It checks for artifacts related to popular virtualization and sandbox platforms’).
- [T1497.001 ] Virtualization / Sandbox Evasion: System Checks – WMIC manufacturer checks and MAC-prefix/driver/path checks detect virtualized environments (‘wmic computer system get manufacturer’ and matching vendor strings).
- [T1497.002 ] Virtualization / Sandbox Evasion: User Activity Checks – Tasklist and file-path presence checks detect analysis environments and sandbox artifacts (‘task list … looks for suspicious processes’ and path existence checks for sample folders).
- [T1622 ] Debugger Evasion – Uses IsDebuggerPresent, PEB BeingDebugged flag, timing checks, and QueryPerformanceFrequency to detect debuggers and instrumentation (‘detects debuggers using IsDebuggerPresent and the PEB’s BeingDebugged flag’).
- [T1070 ] Indicator Removal on Host – The malware includes cleanup routines to remove persistence artifacts when instructed (‘Registry cleanup: Deletes all Run key entries it previously created. Scheduled Task removal …’).
- [T1082 ] System Information Discovery – The implant collects hostname, username, OS name, and privilege level to fingerprint hosts (‘This function is the malware’s system information collector … hostname, username, OS name, privilege level’).
- [T1087 ] Account Discovery – The implant queries account/privilege information (net session technique to infer admin rights) (‘privileges → net session technique (net session >nul 2>&1 && echo Admin || echo User)’).
- [T1057 ] Process Discovery – Uses tasklist scans and enumerations to detect processes and analysis tools (‘task list then looks for suspicious processes: procmon.exe, procexp.exe, wireshark.exe …’).
- [T1012 ] Registry Discovery – Checks multiple registry keys associated with virtualization and installed software (‘loads a very large, concatenated string containing: Registry Keys: HKLMSOFTWAREVMware, Inc.VMware Tools …’).
- [T1083 ] File and Directory Discovery – Scans and checks numerous file paths and directories to identify analysis or sandbox artifacts (‘checks around 128 file paths … If any of those paths exist … the malware immediately terminates’).
- [T1518 ] Software Discovery – Detects installed software and drivers (VM guest additions, drivers and analysis tools) to identify virtualization/analysis environments (‘VM/Analysis Files: C:windowsSystem32DriversVmmouse.sys … vboxdisp.dll …’).
- [T1069 ] Permission Groups Discovery – The agent reports privilege level and uses it for operational decisions (‘Privilege Level SYSTEM / Administrator / User in beacon fields’).
- [T1555 ] Credentials from Password Stores – The HARVEST module expects and uses encrypted DLLs for credential harvesting (‘This command activates a dormant credential-harvesting module stored on disk as encrypted files … stealer.enc’).
- [T1003 ] OS Credential Dumping – The presence of stealer modules and credential-harvesting DLLs indicates capability to extract stored credentials (‘stealer.enc → encrypted DLL … triggers credential-harvesting module’).
- [T1547.001 ] Registry Run Keys / Startup Folder – Persistence via Run key entries under HKCU with randomized legit-looking names (‘Adds values under HKCUSoftwareMicrosoftWindowsCurrentVersionRun using reg add … randomised value names’).
- [T1547 ] Boot or Logon Autostart Execution – Implements multiple autostart mechanisms to run on boot/logon (Run keys, scheduled tasks) (‘After implementing multiple persistence mechanisms (Registry Run, Scheduled Tasks …)’).
- [T1546.003 ] WMI Event Subscription – Persistence may include WMI subscription mechanisms as part of its persistence toolkit (‘After implementing multiple persistence mechanisms (Registry Run, Scheduled Tasks, and WMI Subscriptions)’).
- [T1071 ] Application Layer Protocol – C2 uses application-layer network protocols for command/control and exfiltration (‘C2 Connection … attempts to parse the C2 address as a standard IPv4 endpoint …’).
- [T1071.001 ] Application Layer Protocol: Web Protocols – The BAT/PowerShell downloader uses web protocols to retrieve payloads from GitHub (‘establishes a connection to a GitHub-hosted URL and retrieves a second-stage payload’).
- [T1573 ] Encrypted Channel – The C2 supports encrypted communication channels for confidentiality (‘Encrypted Channel’ listed and the implant supports encrypted channels for C2 interactions).
- [T1573.001 ] Encrypted Channel: Symmetric Cryptography – Uses symmetric cryptography for secure C2/exfiltration modules (ransomware/stealer DLLs encrypted on disk and decrypted with provided keys) (‘The malware checks for ransomware.enc … then decrypts the DLL using the provided key’).
- [T1132 ] Obfuscated / Encoded Channel – Commands and channels are obfuscated/encoded (Base64-encoded commands and encoded channel traffic) (‘Commands arrive encoded in BASE64 … C2 commands are always base64-encoded’).
- [T1008 ] Fallback Channels – Implements fallback C2 strings and IPv6/IPv4 parsing with an embedded fallback server if parsing fails (‘When both IPv4 and IPv6 parsing fail, the malware finally defaults to a hardcoded, embedded command-and-control (C2) string’).
- [T1571 ] Non-Standard Port – Uses a non-standard port for C2 communications (181.231.253.69:4444) rather than common ports to avoid detection heuristics (‘181.231.253.69:4444__PERSIST__:PERSIST_REMOVE…’).
- [T1568 ] Dynamic Resolution (IPv4/IPv6 Parsing) – The implant parses both IPv4 and IPv6 C2 formats and falls back to embedded strings if needed (‘first attempts to parse the C2 address as a standard IPv4 endpoint … then falls back to an IPv6 parsing routine’).
- [T1105 ] Ingress Tool Transfer – The BAT/PowerShell stage downloads executable payloads from GitHub to the victim host (‘The command retrieves a file named health-check.exe from GitHub and saves it as msedge_proxy.exe’).
- [T1005 ] Data from Local System – Collection capabilities include reading local files for exfiltration and for harvesting modules (‘This command activates a dormant credential-harvesting module … and file exfiltration formatting’).
- [T1560 ] Archive Collected Data – The malware formats and archives collected files for exfiltration (builds [filename | size | base64-data] messages for transfer) (‘The malware builds a formatted message containing: File name | File size | Base64 data’).
- [T1056 ] Input Capture – The malware includes modules for input capture as part of its collection capabilities (Input Capture listed and general stealer functionality present).
- [T1113 ] Screen Capture – Capabilities include screen capture as part of data collection (Screen Capture included in the capability list for collection).
- [T1041 ] Exfiltration Over C2 Channel – Stolen files and data are exfiltrated to the C2 using the implant’s application-layer channel (‘_DOWNLOAD_ is a file exfiltration mechanism … sends base64-data to the attacker’).
- [T1486 ] Data Encryption for Impact – Ransomware modules (ransomware.enc and key) are supported and can encrypt directories on command (‘ENCRYPT command … loads the DLL dynamically and calls encrypt_directory’).
- [T1490 ] Inhibit System Recovery – Ransomware capabilities imply actions that inhibit recovery (ransomware module processing and potential deletion of recovery artifacts listed in impact capabilities).
- [T1021 ] Remote Services – Lateral movement via remote services is listed as a potential capability for post-compromise actions (‘Remote Services’ included under Lateral Movement in the technique table).
Indicators of Compromise
- [File Hashes ] Archive and payload identification – dc802b8c117a48520a01c98c6c9587b5 (info/juicio-grunt-posting.pdf.lnk), 45f2a677b3bf994a8f771e611bb29f4f (ZIP archive) and 3 more hashes.
- [File Names ] Malicious files and decoys observed in the delivery package – info/juicio-grunt-posting.pdf.lnk, info/health-check.bat, info/notas.pdf, msedge_proxy.exe (downloaded second-stage RAT).
- [C2 IP:Port ] Command-and-control endpoint used by the RAT – 181.231.253.69:4444 (default/fallback C2 for beaconing and command exchange).
- [Archive Path ] Delivery archive location (artifact referenced in analysis) – D:auto_black_abuseresourcesunzipped…13adde53bd767d17108786bcc1bc0707c2411a40f11d67dfa9ba1a2c62cc5cf3.zip (ZIP used for initial delivery).