Recorded Future / Insikt Group documents PurpleBravo, a North Korean-linked campaign that uses fraudulent developer/recruiter personas and malicious GitHub repositories to deliver infostealers and multi-platform RATs (BeaverTail, GolangGhost/PylangGhost, InvisibleFerret) targeting software developers—especially in the cryptocurrency sector and South Asia. The report details obfuscated JavaScript (Base64 + XOR), RC4/MD5 C2 protocols, registry Run-key persistence, Chrome credential-theft techniques (including DPAPI and app-bound bypasses), extensive C2 infrastructure (dozens of IPs and Astrill VPN nodes), and overlap with PurpleDelta activity. #PurpleBravo #BeaverTail
Category: Threat Research

Dan Tentler of Phobos Group demonstrates a fully portable security system using Home Assistant, Z-Wave devices, CO2 sensors, and millimeter-wave radar to detect human presence through walls and automate alerts. The LABScon 2025 presentation by SentinelLabs shows how this rapidly deployable platform can capture images, trigger actions, and provide situational awareness in hotel rooms and other temporary accommodations #HomeAssistant #PhobosGroup
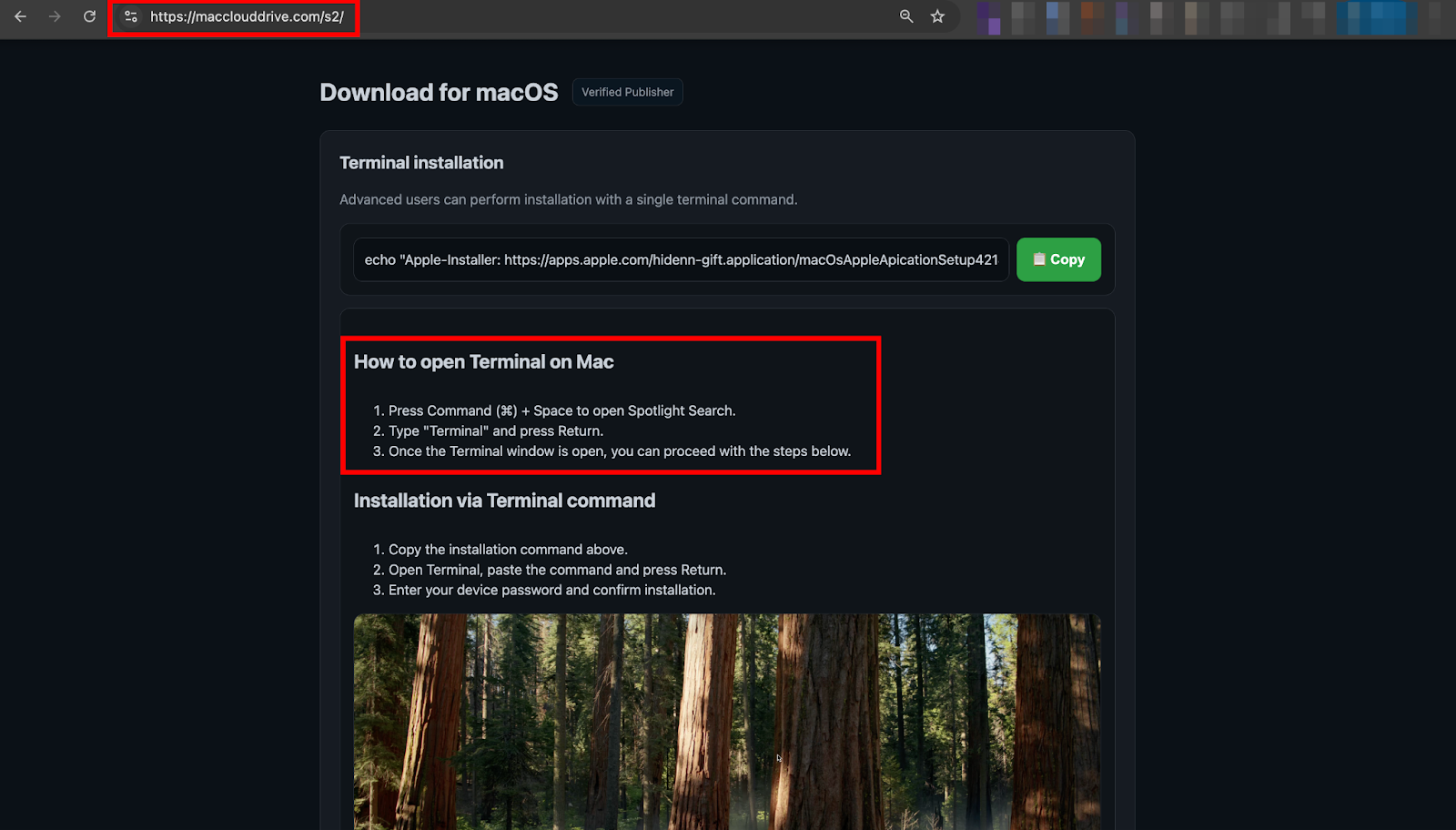
Researchers discovered a ClickFix-style macOS lure (macclouddrive.com/s2) that tricks users into pasting a Terminal one-liner which downloads a daemonized Zsh stager that executes a remote AppleScript to harvest browser credentials, Keychain data, crypto wallets, and other sensitive files. The campaign uses the MacSync infostealer with rotating jmpbowl.* C2 domains and conditionally trojanizes Electron wallet apps (Ledger Wallet.app, Trezor Suite.app) to capture PINs and recovery phrases for long-term phishing. #MacSync #jmpbowl

AhnLab ASEC reports that the Larva-25012 threat actor is distributing Proxyware via malicious installers masquerading as Notepad++ and cracked-software download pages, using both MSI and ZIP vectors that deploy DPLoader and multiple Proxyware families such as Infatica and DigitalPulse. The attacker persists via scheduled tasks, DLL side‑loading and process injection, and…
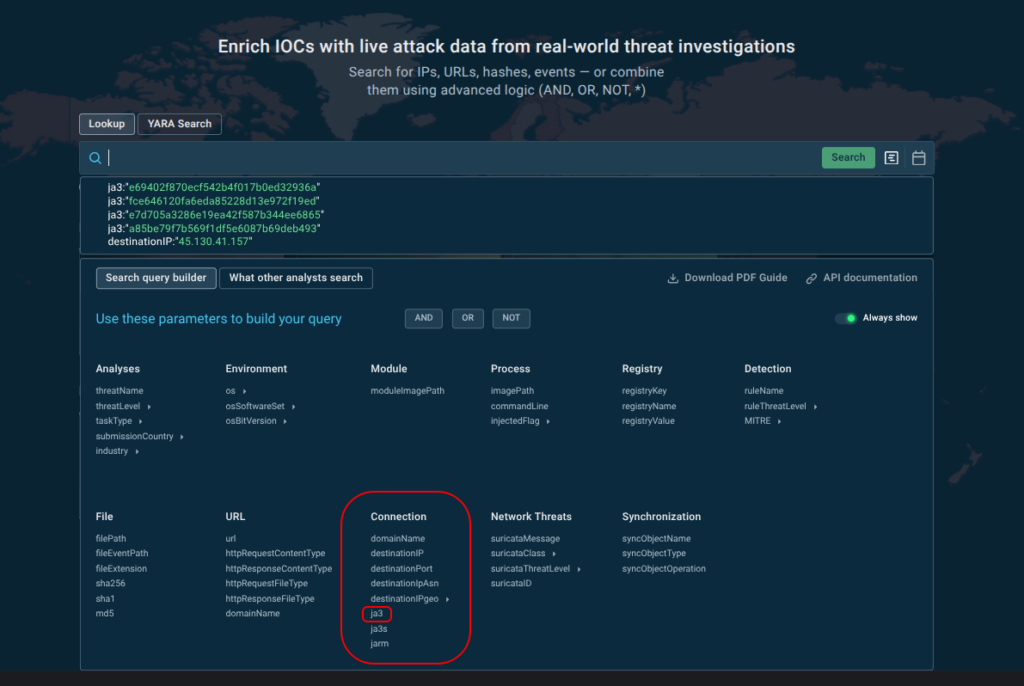
JA3 TLS fingerprints are still useful as durable, tool-level behavioral indicators that can reveal new malicious tooling and enable clustering of related activity when enriched with context. ANY.RUN shows how JA3 frequency analysis and TI Lookup link specific JA3 hashes to malware and exfiltration channels, e.g., Remcos and Skuld. #Remcos #Skuld…
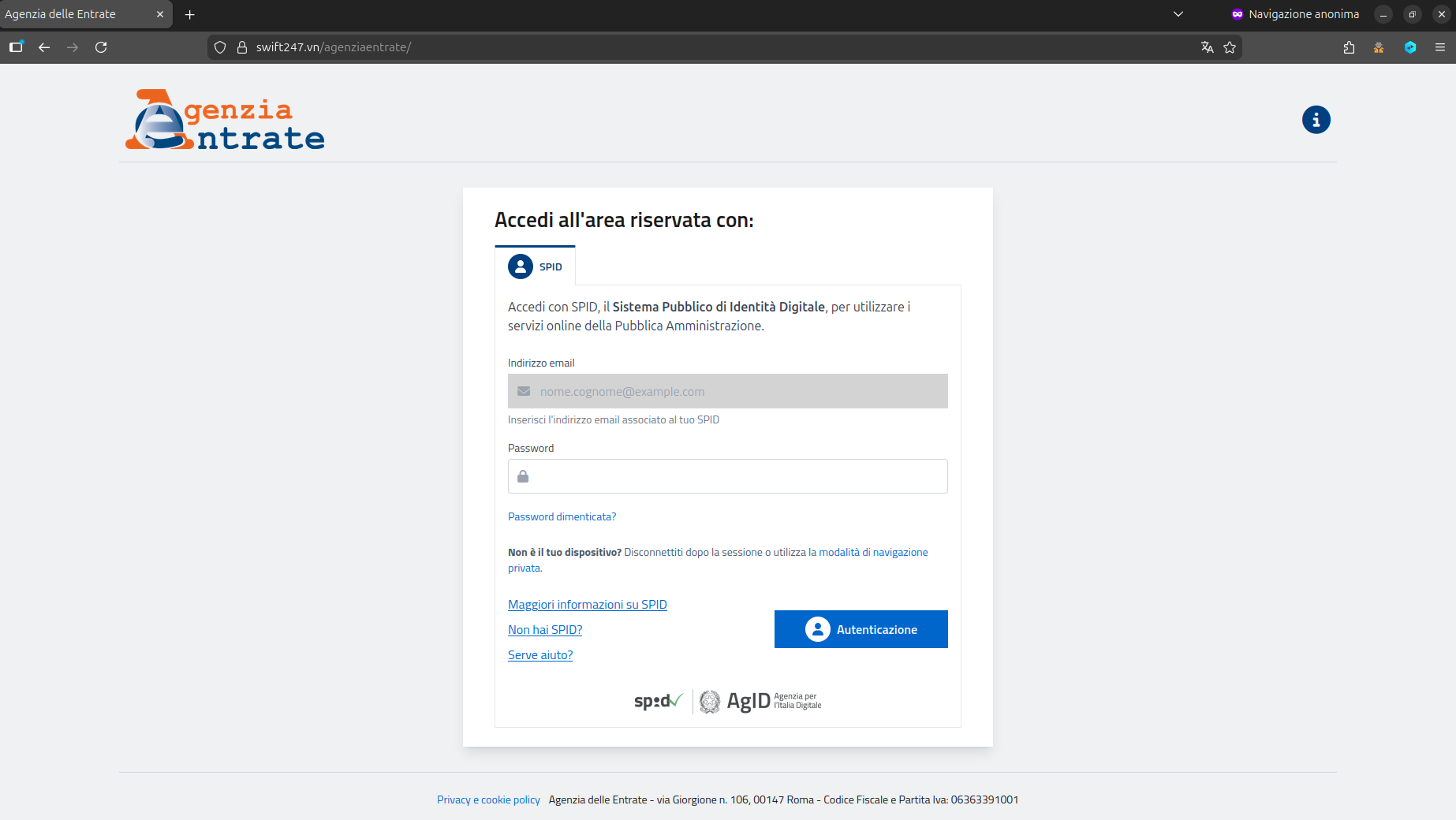
CERT-AGID detected a phishing campaign impersonating the Agenzia delle Entrate that aims to steal users’ SPID credentials via a fake SPID login page. The campaign uses deceptive messages with personalized links to a fraudulent site that pre-fills the victim’s email and asks only for the SPID password; CERT-AGID notified the agency, requested takedown of the hosting site, and distributed IoCs to accredited structures. #AgenziadelleEntrate #SPID
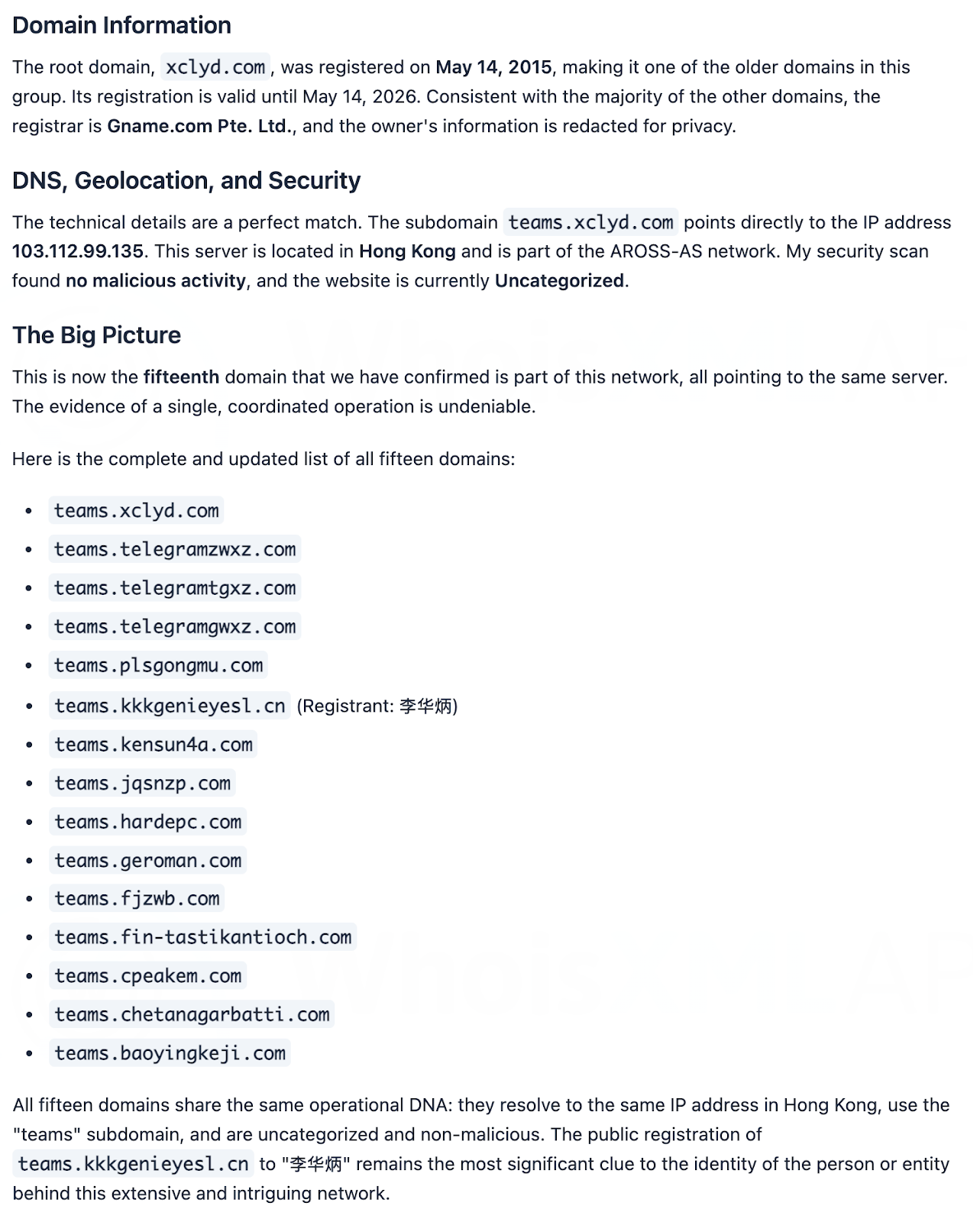
Chinese APT group SilverFox used Cyrillic characters in SEO-poisoning lures and abused Microsoft Teams to deliver ValleyRAT for espionage and financial theft. ReliaQuest and subsequent analysis identified dozens of IoCs and large-scale infrastructure links — including 20 domains, 18 IPs, 2,357 client IPs contacting one IoC domain, and 45,949 email-connected domains (51 weaponized). #SilverFox #ValleyRAT
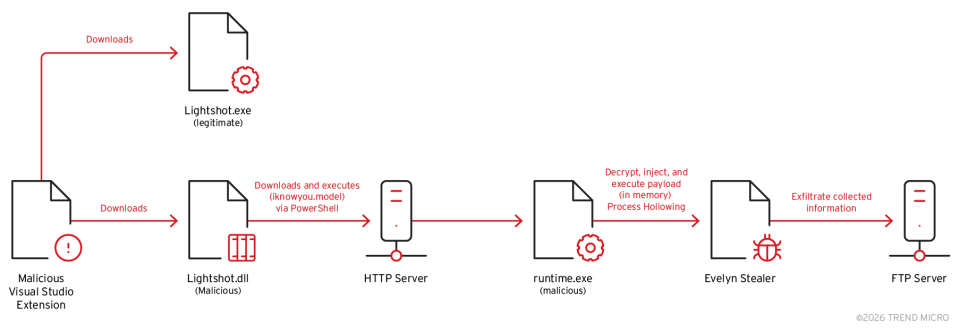
The blog analyzes a multistage campaign that weaponized Visual Studio Code extensions to deliver the Evelyn information stealer, using a DLL downloader, a process-hollowing injector, and a final payload that harvests developer credentials and cryptocurrency data. The malware uses AES-256-CBC encryption, multiple anti-analysis checks, and FTP-based C2/exfiltration to evade detection and…
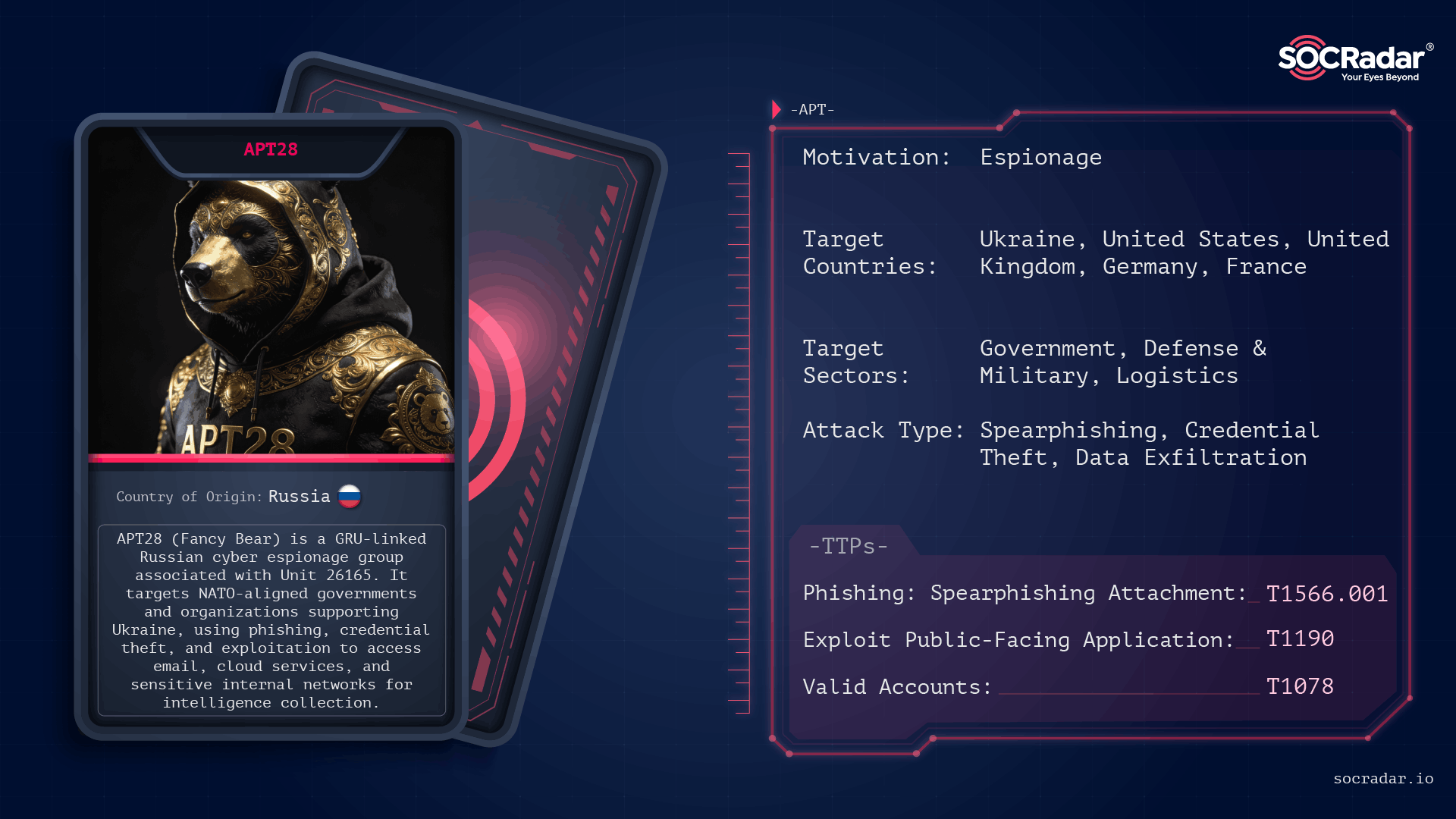
APT28 is a long-running, GRU-linked espionage group that prioritizes stealthy credential access, targeted phishing, and long-term intelligence collection across Europe, North America, and Ukraine. Recent reporting through 2025 highlights new tooling like the LAMEHUG AI-assisted malware and sustained credential/token harvesting campaigns against services such as UKR[.]net. #APT28 #LAMEHUG
Check Point Research documents VoidLink as a sophisticated malware framework largely authored with AI, showing that a single developer leveraged an AI-centric IDE (TRAE/TRAE SOLO) and Spec Driven Development to build a functional implant in under a week. Leaked artifacts—including TRAE-generated instructions, a c2架构.txt seed file, extensive Markdown sprint plans, and source code—reveal use of eBPF and LKM rootkits and a rapid, modular C2/design lifecycle. #VoidLink #TRAESOLO

SentinelLABS’ analysis finds that current LLM benchmarks from major players reduce continuous, collaborative security work to isolated, static tasks and therefore do not measure the operational outcomes defenders need. Benchmarks such as Microsoft’s ExCyTIn-Bench, Meta’s CyberSOCEval/CyberSecEval 3, and CTIBench show LLMs struggle with multi-hop investigations, poor calibration on severity, and evaluation loops that rely on vendor models to judge vendor models. #ExCyTIn-Bench #CyberSOCEval

Operation Poseidon is a spear-phishing campaign attributed to the Konni APT that abused legitimate advertising redirection (ad.doubleclick[.]net, mkt.naver[.]com) and compromised WordPress sites to distribute EndRAT via LNK files and AutoIt scripts disguised as PDFs. The campaign reused C2 infrastructure (e.g., jlrandsons.co[.]uk), multiple IPs and file hashes, and underscores the need for behavior-based EDR detection and multi-stage redirection analysis. #EndRAT #Konni
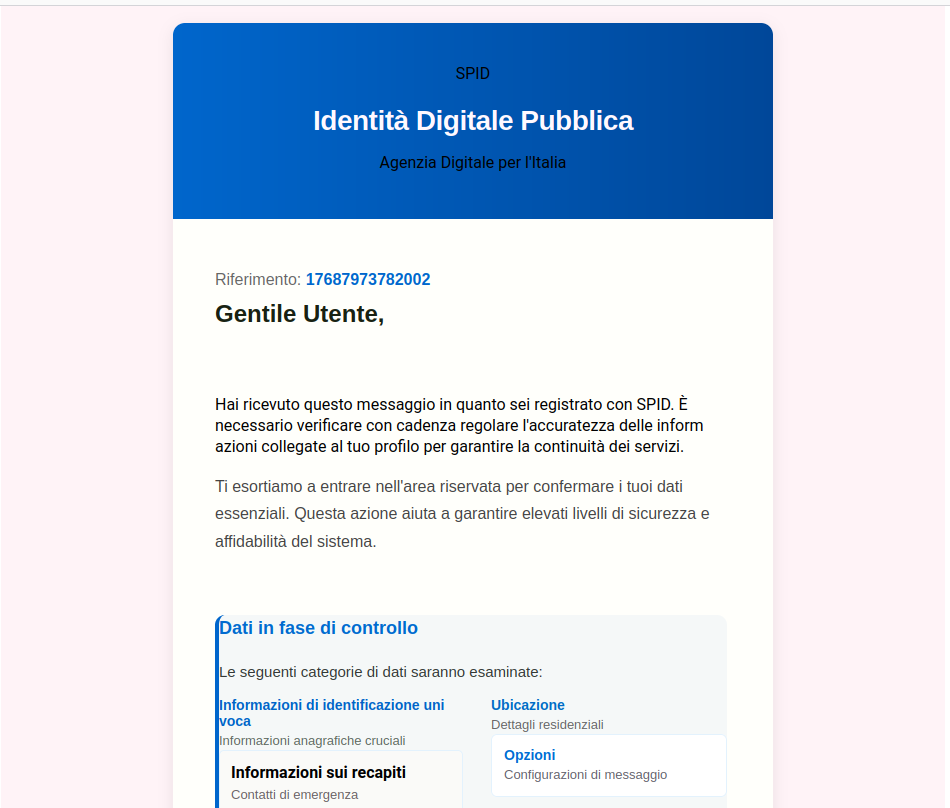
CERT-AGID has identified a SPID-themed phishing campaign that uses deceptive emails linking to a fake SPID portal hosted on Google Sites to collect personal and banking data. The fraudulent pages request names, addresses, contact details and IBANs; CERT-AGID requested takedown of the hosting site and distributed IoCs via its feed to accredited structures. #SPID #CERT-AGID #GoogleSites #AgID #DipartimentoPerLaTrasformazioneDigitale
KongTuke distributed a malicious Chrome extension (NexShield, typosquatting uBlock Origin Lite) that tracks installs via UUID beacons, delays execution, and triggers a browser denial-of-service while displaying a fake “CrashFix” popup to socially engineer victims. The campaign delivers a multi-stage infection chain—using finger.exe as a LOLBin, multi-layer PowerShell obfuscation and DGA domains, and culminating in ModeloRAT and a GateKeeper .NET payload with AES+XOR string encryption. #KongTuke #ModeloRAT
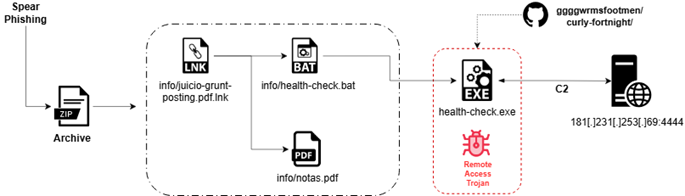
Seqrite Labs uncovered “Operation Covert Access,” a targeted spear-phishing campaign that abuses authentic Argentine federal court documents to deliver a multi-stage Rust-based Remote Access Trojan (CovertRAT) via a weaponized LNK, BAT loader, and a GitHub-hosted second-stage binary. The implant demonstrates extensive anti-VM/anti-debug checks, IPv4/IPv6 C2 fallback (default 181.231.253.69:4444), and a modular command set for persistence, data theft, file transfer, encryption, and privilege escalation. #CovertRATCiR #ArgentinaJudicialSector
