CERT-AGID detected a phishing campaign impersonating the Agenzia delle Entrate that aims to steal users’ SPID credentials via a fake SPID login page. The campaign uses deceptive messages with personalized links to a fraudulent site that pre-fills the victim’s email and asks only for the SPID password; CERT-AGID notified the agency, requested takedown of the hosting site, and distributed IoCs to accredited structures. #AgenziadelleEntrate #SPID
Keypoints
- CERT-AGID identified a phishing campaign targeting the Agenzia delle Entrate to harvest SPID credentials.
- The attack is delivered via deceptive communications containing a link that redirects to a purpose-built fraudulent website.
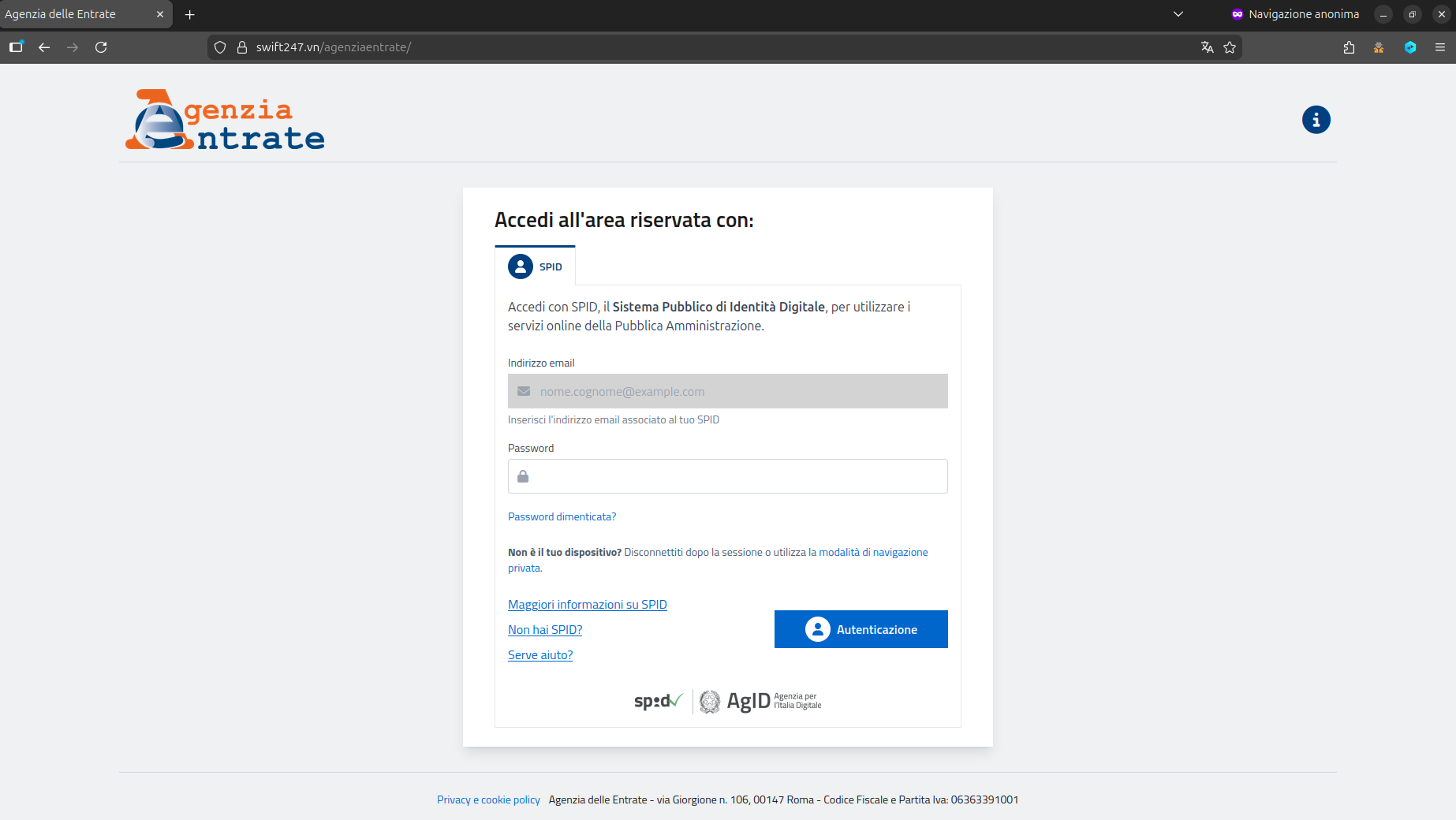
- The phishing page mimics the Agenzia delle Entrate’s reserved-area SPID login and requests only the SPID password while the victim’s email is prefilled.
- A screenshot of the fraudulent login page was observed and referenced by CERT-AGID.
- CERT-AGID alerted the affected agency and requested deactivation of the hosting site to prevent further credential theft.
- Indicators of Compromise related to the campaign were distributed through the CERT-AGID feed to accredited structures.
MITRE Techniques
- [T1566.002 ] Spearphishing Link – The campaign uses deceptive messages with links that redirect victims to credential-harvesting sites (‘The campaign is distributed through deceptive communications that invite the user to access their reserved area of the Agenzia delle Entrate and contain a link that redirects to a site created ad hoc to collect credentials.’).
- [T1566 ] Phishing – The adversary presented a fraudulent SPID login page to trick users into submitting authentication information (‘The fraudulent web page presents a fake SPID login screen that requests only the SPID password while the victim’s email address is already prefilled via link personalization.’).
Indicators of Compromise
- [URL ] phishing site/link – “Download IoC” link referenced in the article (IoC download link provided in source), fraudulent SPID login page referenced by screenshot.