Check Point Research identified a KONNI-linked phishing campaign targeting blockchain developers across the APAC region that uses Discord-hosted lures and weaponized LNK shortcuts to deploy a multi-stage infection chain. The operation deploys an AI-generated, obfuscated PowerShell backdoor, leverages UAC bypass and scheduled-task persistence, and communicates with a PHP-based C2 protected by a JavaScript/AES challenge. #KONNI #SimpleHelp
Category: Threat Research

CISOs are shifting 2026 cybersecurity budgets from reactive, optimization-driven strategies toward growth-focused, precision investments that prioritize measurable risk reduction and operational efficiency. Adversarial Exposure Validation (AEV) and continuous testing (via platforms like Picus) are emphasized as essential to proving ROI, optimizing tool sprawl, and prioritizing exploitable vulnerabilities. #Picus #Kerberoasting
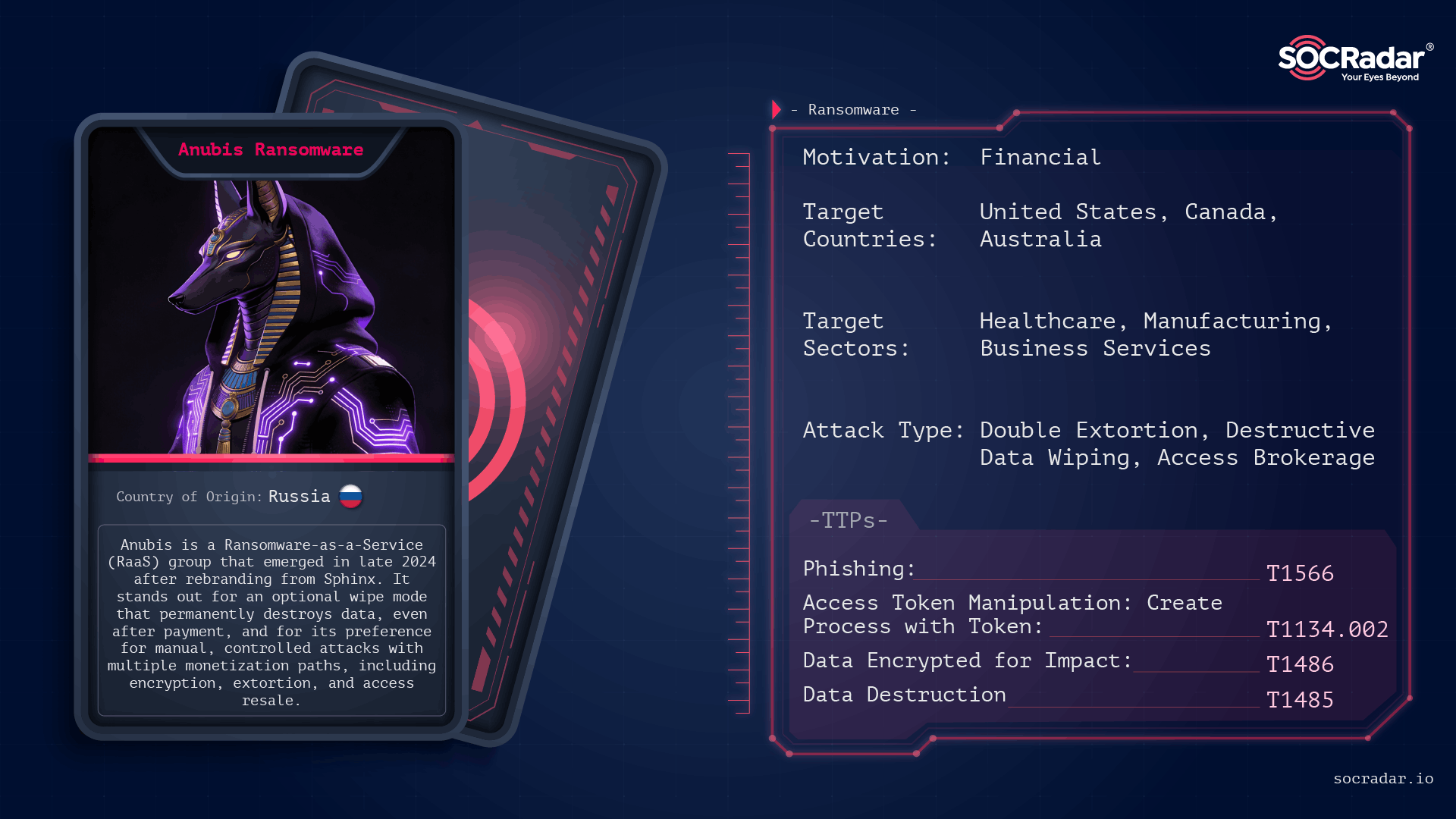
Anubis (formerly Sphinx) is a Ransomware-as-a-Service operation first observed in late 2024 that combines standard file encryption with an optional destructive wipe mode, permanently destroying data and removing decryption as a guaranteed outcome. Its affiliate-driven model and parallel monetization channels (data extortion and access resale) let operators choose between encryption, data-only extortion, or selling access, concentrating on high-value targets and controlled, high-impact intrusions. #Anubis #Sphinx
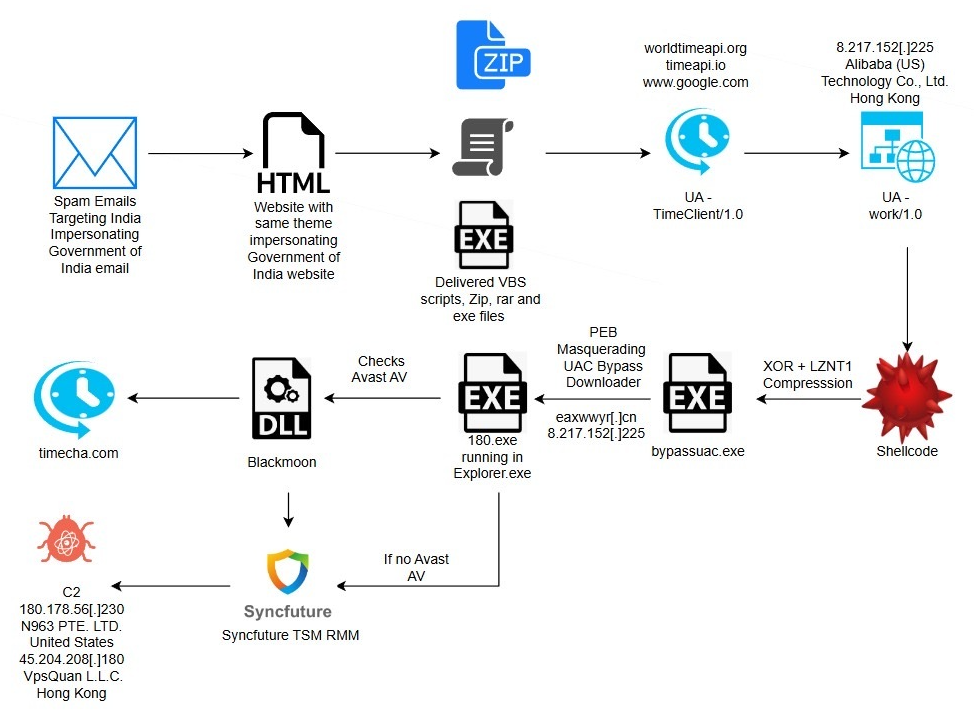
eSentire TRU uncovered a multi-stage espionage campaign targeting residents of India that uses phishing lures impersonating the Income Tax Department to deliver a DLL side-loading loader which fetches shellcode, bypasses UAC via a COM elevation moniker, and ultimately deploys a repurposed SyncFuture TSM platform for persistent remote surveillance. The intrusion chain includes anti-analysis, PEB process masquerading, Avast-specific GUI automation to create antivirus exclusions, service-based Safe Mode persistence, and multiple signed binaries and certificates abused to appear legitimate. #Blackmoon #SyncFuture
Rust significantly reduces memory-safety vulnerabilities in embedded and firmware development but does not eliminate logic, hardware, or protocol design flaws that create security risk. Academic research and professional reviews show embedded Rust commonly uses unsafe blocks for hardware interaction, suffers from tooling and static-analysis gaps, and remains vulnerable to logic-based issues such as authentication bypass, race conditions, nonce reuse, and incorrect hardware assumptions #Rust #PurdueUniversity

A new malware-as-a-service toolkit called Stanley is being sold on a Russian-language cybercrime forum to deploy Chrome-extension-based website-spoofing attacks that overlay attacker-controlled phishing pages while the browser URL bar still shows the legitimate site. The toolkit includes a C2 management panel, guaranteed Chrome Web Store publication at higher price tiers, IP-based…
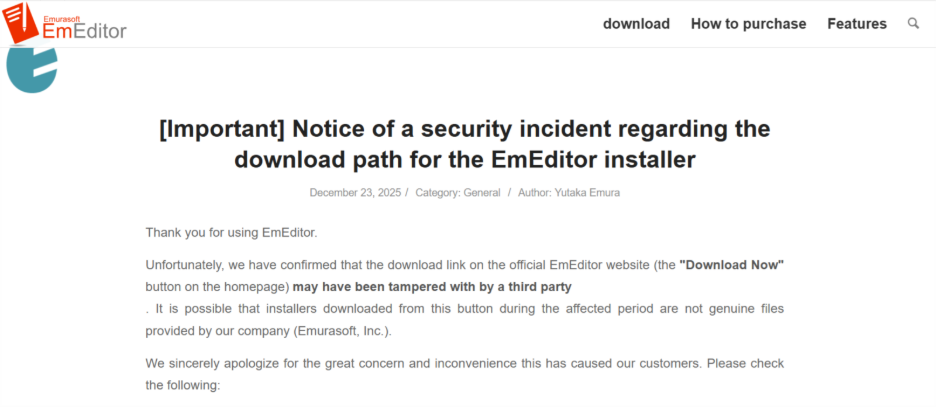
TrendAI Research analyzed a supply-chain compromise of EmEditor’s official download page in which a modified EmEditor .MSI installer executed PowerShell to retrieve multistage malware. The malware disables PowerShell ETW, harvests credentials from Windows Credential Manager, fingerprints and geofences hosts, and exfiltrates data to a C2 at cachingdrive[.]com #EmEditor #cachingdrive…

The report documents major financial-sector incidents including a 3-million-record database leak from Indonesia’s largest bank sold on DarkForums by the actor BreachLaboratory and a ransomware breach by INC Ransom that published roughly 100GB of stolen data. It additionally analyzes a phishing email campaign targeting financial institutions, lists top malware strains affecting…
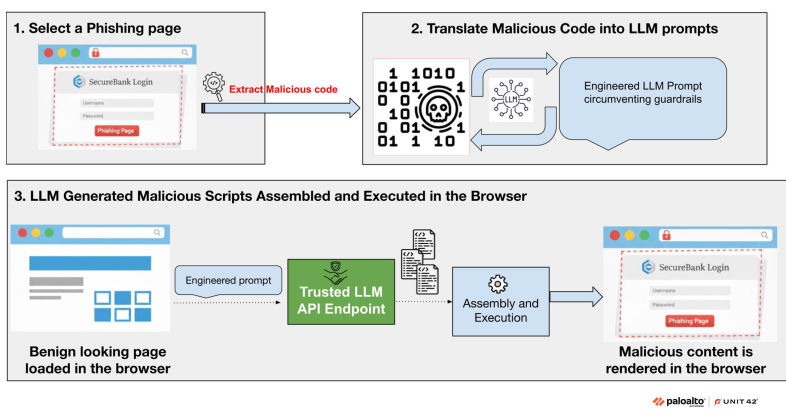
This article describes a novel AI-augmented attack where a benign webpage requests code from trusted LLM APIs, assembles malicious JavaScript in-browser at runtime, and renders personalized phishing pages that evade network-based detection. The report demonstrates a proof-of-concept that leverages prompt engineering and polymorphic LLM-generated code to bypass guardrails and recommends runtime…

A new, distinct ransomware family called Osiris was used in a November 2025 attack against a major food service franchisee in Southeast Asia, employing hybrid ECC+AES-128-CTR encryption, VSS deletion, and a variety of living-off-the-land and dual-use tools. The intrusion included data exfiltration to Wasabi buckets, use of a Mimikatz build named kaz.exe, and deployment of a malicious signed driver (Poortry/Abyssworker) consistent with a BYOVD defense‑impairment tactic. #Osiris #Poortry
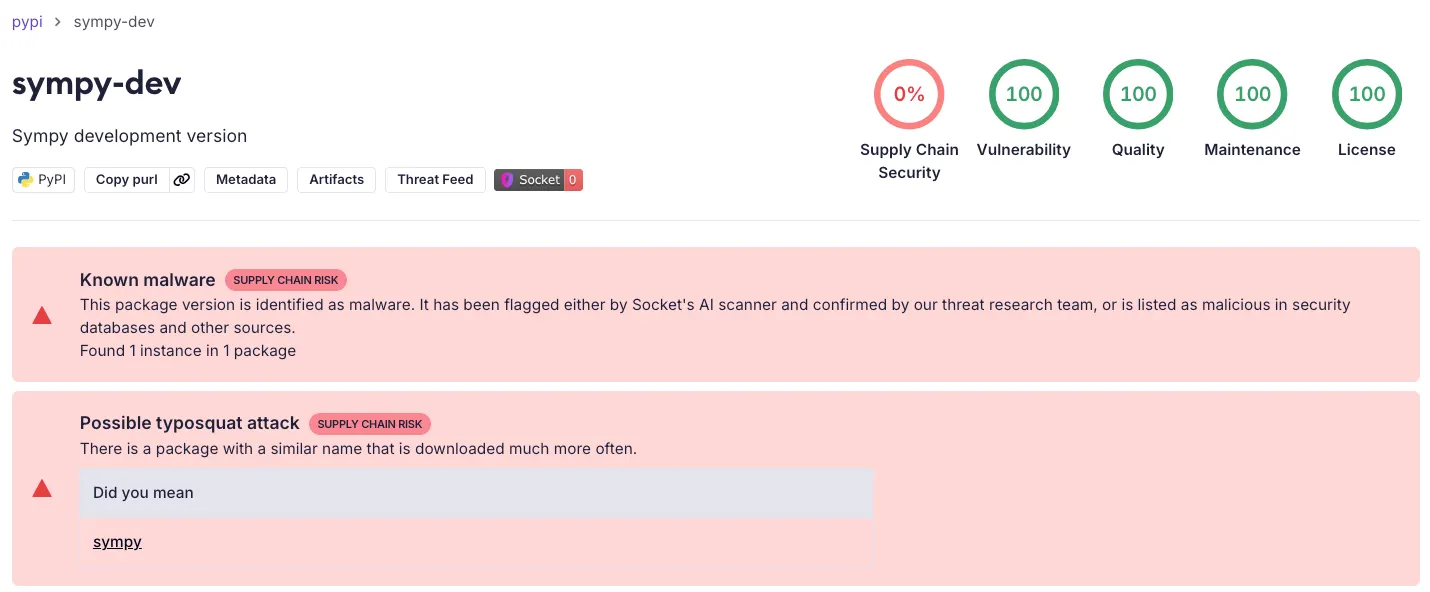
Socket’s Threat Research Team discovered a malicious PyPI package named sympy-dev that impersonates the legitimate SymPy library and embeds a downloader and in-memory loader to fetch and execute ELF payloads. The loader retrieved XMRig cryptominer binaries from threat actor-controlled hosts, the package surpassed 1,000 downloads on day one, and the malicious releases remain live on PyPI pending removal. #sympy-dev #XMRig
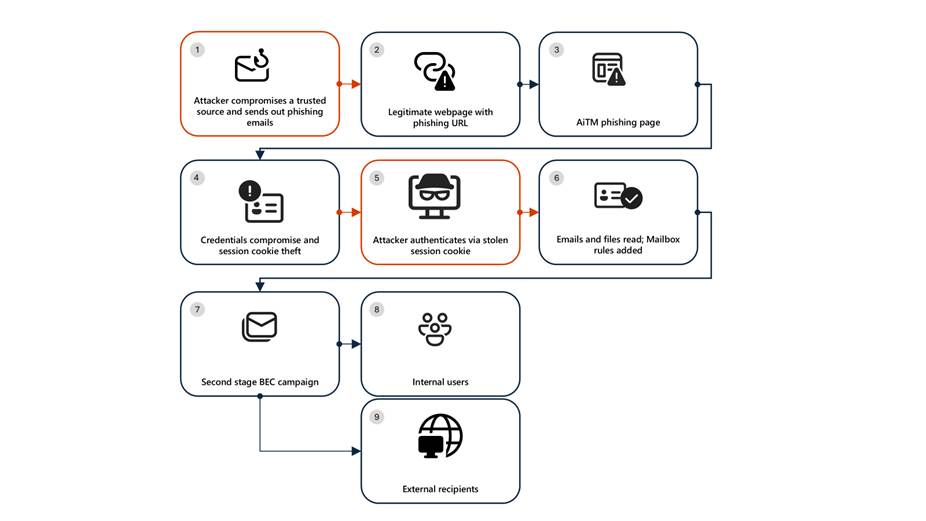
Microsoft Defender researchers uncovered a multi-stage adversary‑in‑the‑middle (AiTM) phishing and BEC campaign that used compromised trusted vendor SharePoint links to harvest credentials, steal session cookies, create malicious inbox rules, and send large‑scale phishing to internal and external contacts, compromising multiple accounts in the energy sector. Remediation requires more than password resets—organizations must revoke active session cookies, remove attacker‑created inbox rules, enforce MFA/conditional access, and use Defender XDR detection and ZAP to contain and remediate the campaign. #AiTM #SharePoint

BlackSuit is an evolution of the Royal ransomware family active since at least May 2023, using phishing for initial access, extensive data exfiltration, a double-extortion model, and a configurable partial-encryption approach to speed encryption and reduce detection. AttackIQ released an emulation based on CISA and DFIR reporting to help organizations validate…
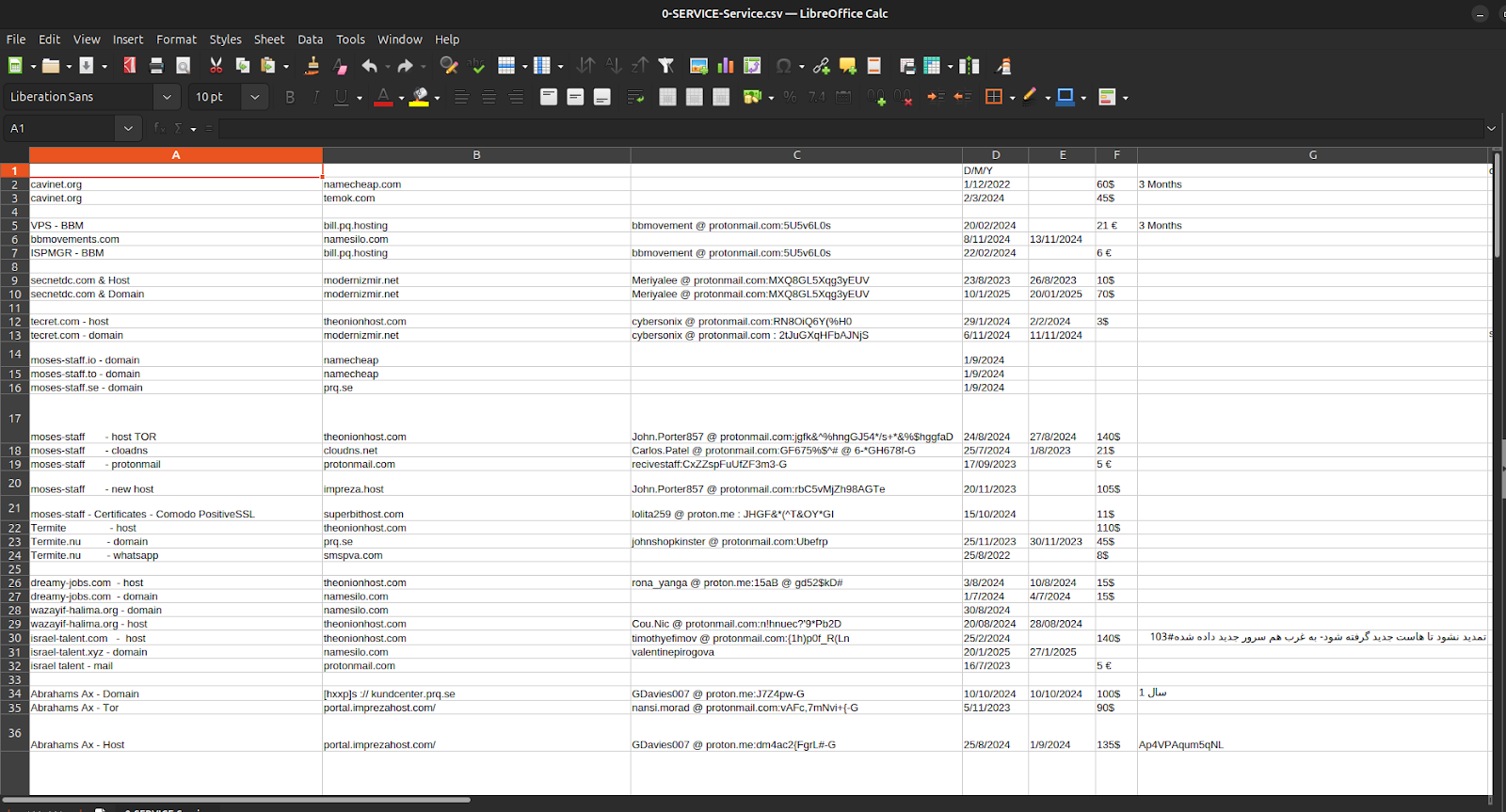
Episode 4 of the Charming Kitten / APT35 leaks exposes not sophisticated zero-day exploits but the bureaucratic infrastructure—spreadsheets, invoices, crypto receipts, hosting accounts, and one-time ProtonMail identities—that fund, procure, and maintain Iranian cyber operations. The documents tie APT35’s procurement and payment chains to Moses Staff’s leak domains and operational tooling, showing micro-crypto payments via Cryptomus, recurring European VPS providers (EDIS, Impreza), and repeatable, auditable workflows that convert state intent into persistent infrastructure. #APT35 #MosesStaff
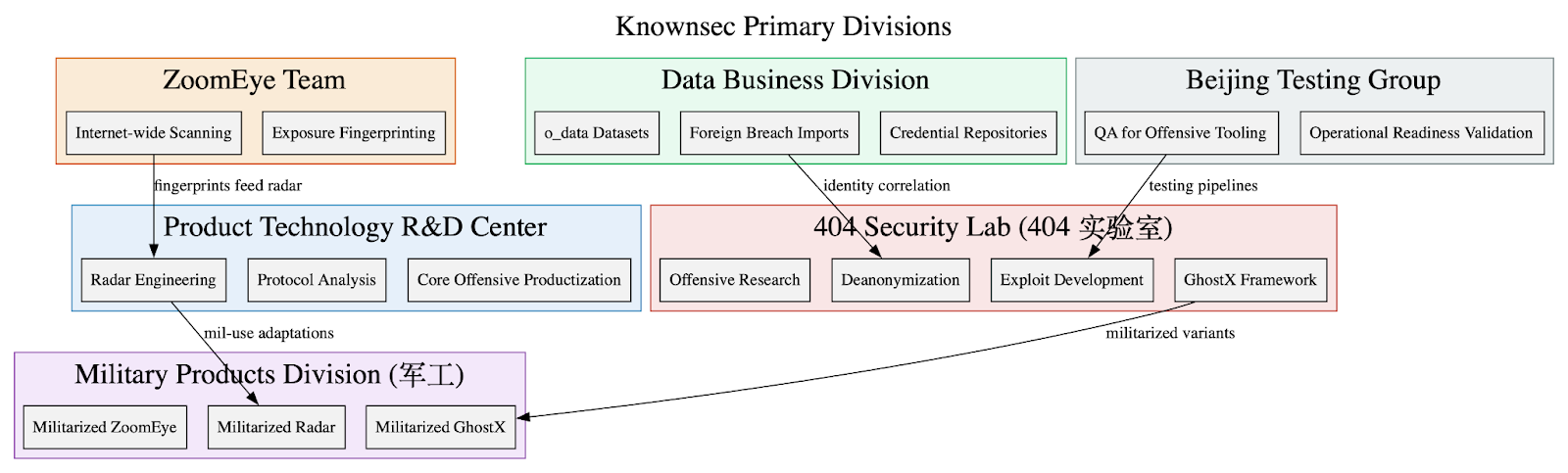
Leaked internal documents show Knownsec operates as a state-aligned cyber contractor supplying a vertically integrated espionage stack—ZoomEye/TargetDB reconnaissance, o_data_* identity correlation, GhostX/Un‑Mail exploitation and mailbox takeover, and Passive Radar PCAP-based internal mapping—to Chinese public‑security, military, and regulator customers. The corpus includes organizational charts, employee emails, high‑confidence IOCs targeting Taiwanese critical infrastructure, and detailed tradecraft emphasizing persistence, anti‑forensics, and APT‑style operational workflows. #Knownsec #GhostX
