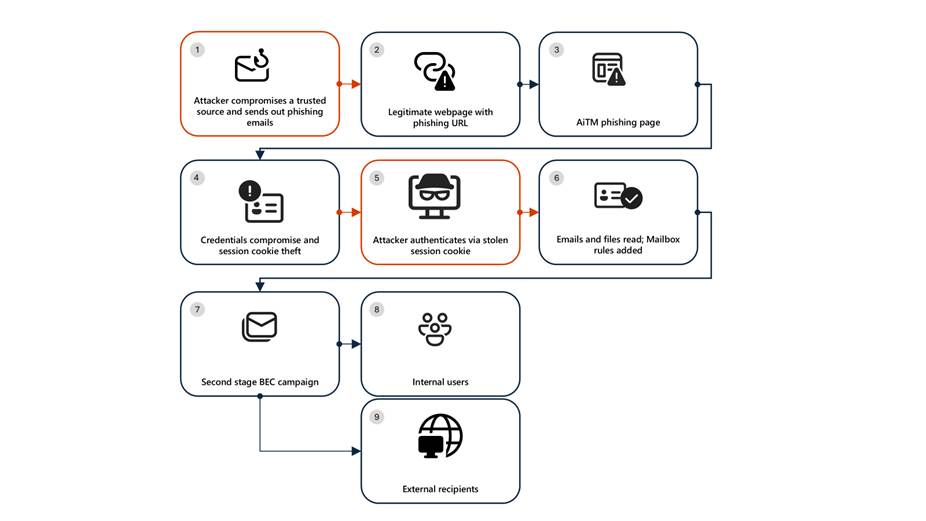
Microsoft Defender researchers uncovered a multi-stage adversary‑in‑the‑middle (AiTM) phishing and BEC campaign that used compromised trusted vendor SharePoint links to harvest credentials, steal session cookies, create malicious inbox rules, and send large‑scale phishing to internal and external contacts, compromising multiple accounts in the energy sector. Remediation requires more than password resets—organizations must revoke active session cookies, remove attacker‑created inbox rules, enforce MFA/conditional access, and use Defender XDR detection and ZAP to contain and remediate the campaign. #AiTM #SharePoint
Keypoints
- The campaign began with a phishing email appearing to come from a trusted vendor and leveraged a SharePoint URL requiring user authentication to deliver the phishing payload.
- Users who clicked the malicious SharePoint link were redirected to a credential prompt, enabling credential/session cookie capture and limited visibility beyond the landing page.
- Attackers created mailbox inbox rules that deleted incoming mail and marked messages as read to maintain persistence and evade detection.
- The compromised accounts were used to send a large‑scale phishing campaign (600+ emails) to internal contacts, external recipients, and distribution lists based on recent email threads.
- Follow‑on BEC tactics included monitoring and deleting undelivered or out‑of‑office emails, reading and responding to inquiries to maintain credibility, and removing traces from mailboxes.
- Microsoft Defender XDR detected activity (e.g., stolen session cookie usage, suspicious sign‑ins, malicious inbox rules) and responded with automated disruption and zero‑hour auto purge (ZAP); recommended remediation includes revoking session cookies, resetting passwords, removing malicious rules, and enforcing MFA/conditional access.
MITRE Techniques
- [T1566.003 ] Spearphishing via Service – Attackers used SharePoint links requiring authentication to deliver phishing payloads and lure users (‘The lure employed a SharePoint URL requiring user authentication and used subject‑line mimicry consistent with legitimate SharePoint document‑sharing workflows to increase credibility.’)
- [T1539 ] Steal Web Session Cookie – The campaign involved theft and replay of web session cookies to maintain access beyond credential capture and to bypass password resets (‘This attack demonstrates the operational complexity of AiTM campaigns … Password resets alone are insufficient. Impacted organizations … must additionally revoke active session cookies.’)
- [T1078 ] Valid Accounts – Adversaries signed in with compromised internal accounts and used trusted identities to send phishing at scale and expand the campaign (‘the attackers leveraged trusted internal identities from the target to conduct large‑scale intra‑organizational and external phishing’)
- [T1114 ] Email Collection – The attacker monitored the victim mailbox for undelivered and out‑of‑office emails, read them, and deleted archive items to facilitate BEC and remain covert (‘The attacker then monitored the victim user’s mailbox for undelivered and out of office emails and deleted them from the Archive folder.’)
- [T1556 ] Modify Authentication Process – Attackers tampered with MFA or added authentication persistence mechanisms (for example, OTP to an attacker‑controlled number) to retain access despite standard remediation (‘the attacker can add a new MFA policy to sign in with a one‑time password (OTP) sent to attacker’s registered mobile number.’)
Indicators of Compromise
- [IP Address ] Attacker infrastructure – 178.130.46.8, 193.36.221.10
- [Email subject ] Hunting/detection indicator used in queries – “NEW PROPOSAL – NDA”
- [Service/URL ] Phishing hosting vector – SharePoint URL requiring user authentication (used as the malicious landing and lure)