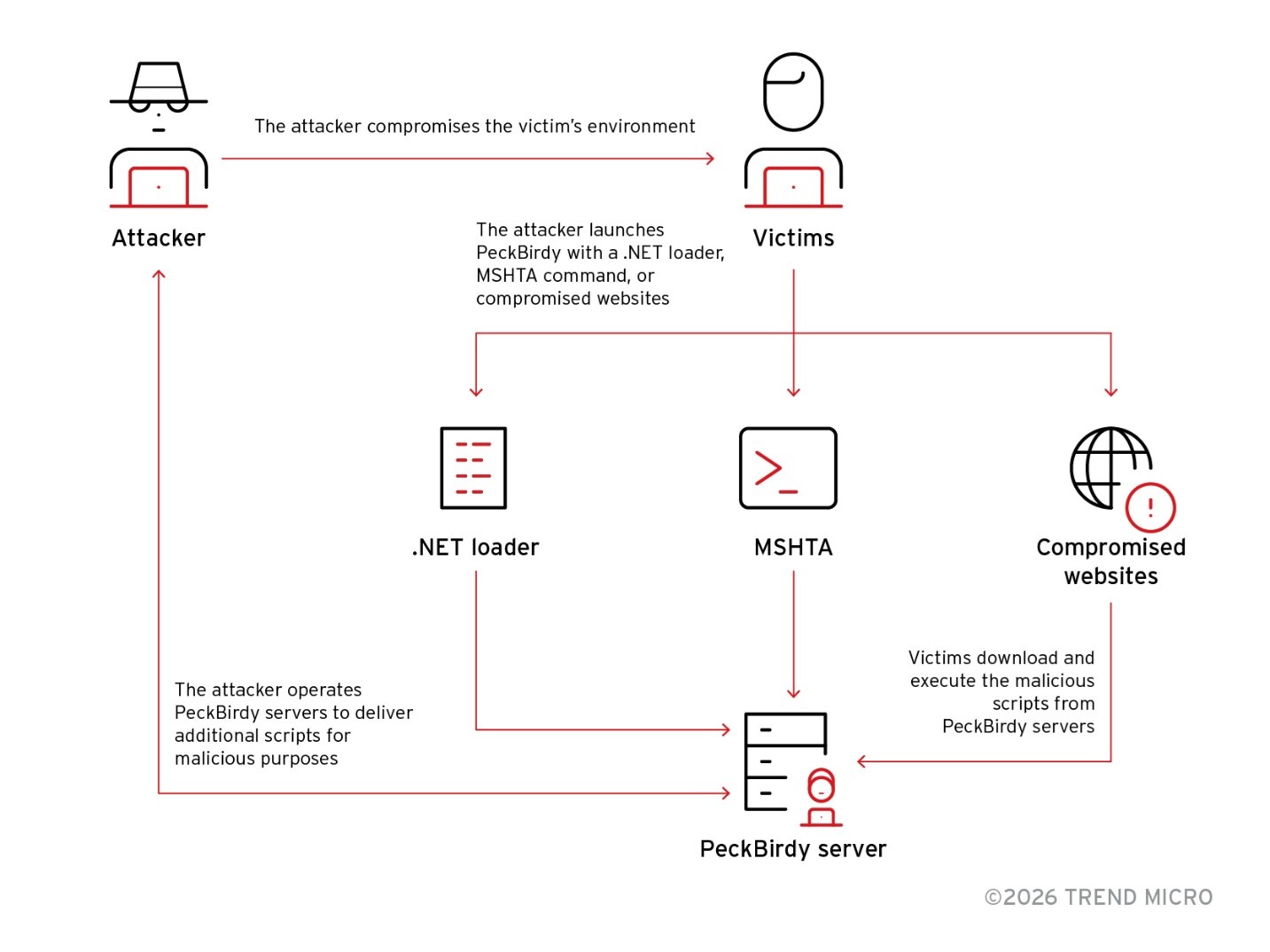
PeckBirdy is a versatile JScript-based command-and-control framework used by China-aligned APT groups since 2023 to abuse LOLBins and deliver modular backdoors across browsers, MSHTA, WScript, Classic ASP, NodeJS and .NET environments. Related campaigns SHADOW-VOID-044 and SHADOW-EARTH-045 deployed backdoors such as HOLODONUT and MKDOOR, used watering‑hole and phishing lures, exploited CVE-2020-16040, and…
Category: Threat Research

Elastic’s Infosec team reduced endpoint event volume and costs by using Event Filtering and Advanced Policy Settings in Elastic Defend across their worldwide distributed workforce. By identifying noisy processes and hosts with ES|QL queries, applying event filters, disabling unnecessary hash calculations, and enabling event aggregation they cut event volume per host by ~75% and saved terabytes of storage per month. #ElasticDefend #Elastic
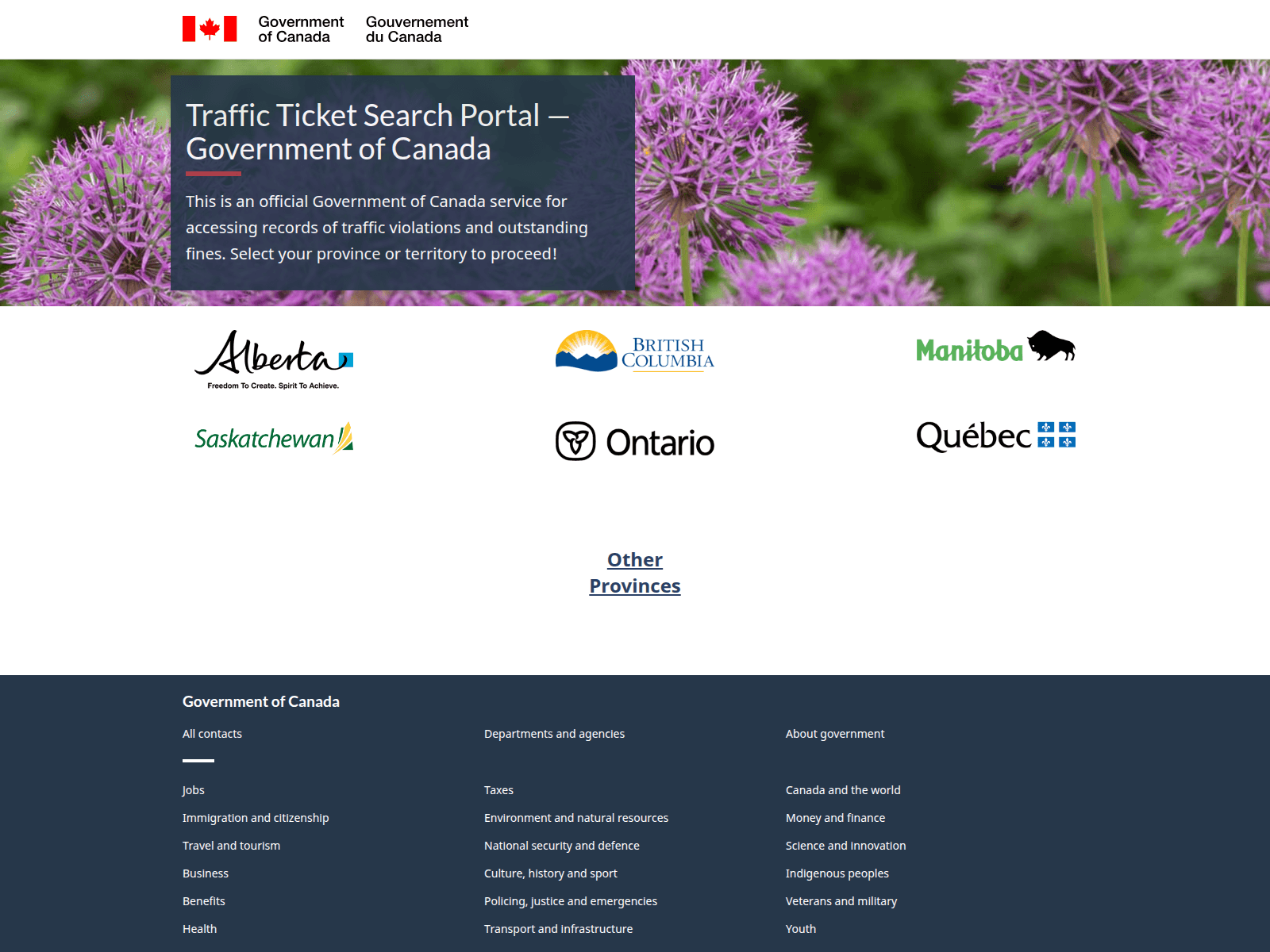
CloudSEK identified interconnected phishing campaigns impersonating Canadian government bodies and national brands (traffic-ticket portals, CRA, Canada Post, Air Canada) to harvest PII and financial data using SMS lures, typosquatted domains, and fake payment gateways. The activity aligns with the PayTool ecosystem and is being commoditized on underground forums by a seller advertising specialized phishing kits. #PayTool #theghostorder01

Socket’s Threat Research Team found that the Chrome extension “Amazon Ads Blocker” hides sponsored listings as advertised but secretly injects and replaces affiliate tags with the developer’s tag (10xprofit-20) on every Amazon product link. The extension’s Chrome Web Store disclosure is misleading and violates Google’s June 2025 affiliate policy by performing automatic, non-consensual tag replacement without providing direct user benefit or required user action. #AmazonAdsBlocker #10xprofit-20

Security research found multiple malicious or deceptive Chrome extensions that collectively reach over 100,000 users and perform undisclosed actions such as clipboard access, cookie exfiltration, command-and-control communication with a DGA fallback, search hijacking, ad injection, and an exploitable XSS vulnerability. Users are advised to uninstall affected extensions and the report highlights specific offenders like Good Tab and Children Protection for immediate action. #GoodTab #ChildrenProtection
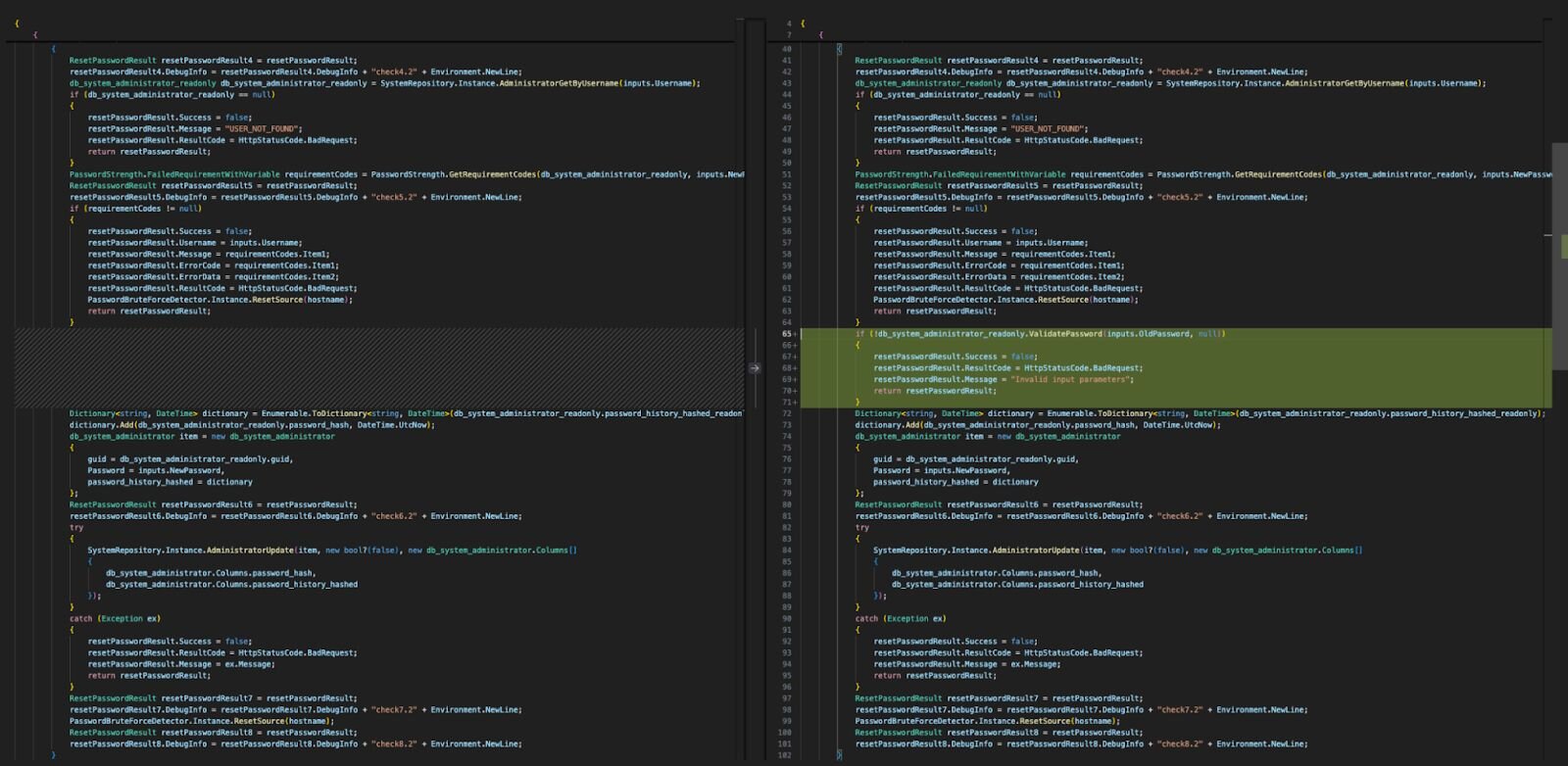
A privilege escalation vulnerability (CVE-2026-23760) in SmarterTool’s SmarterMail allowed attackers to take over privileged accounts and achieve remote code execution; users should upgrade to Build 9511 released January 15, 2026. Huntress observed mass automated exploitation using HTTP POST requests to SmarterMail API endpoints and malicious System Events configured to run reconnaissance commands. #SmarterMail #CVE-2026-23760
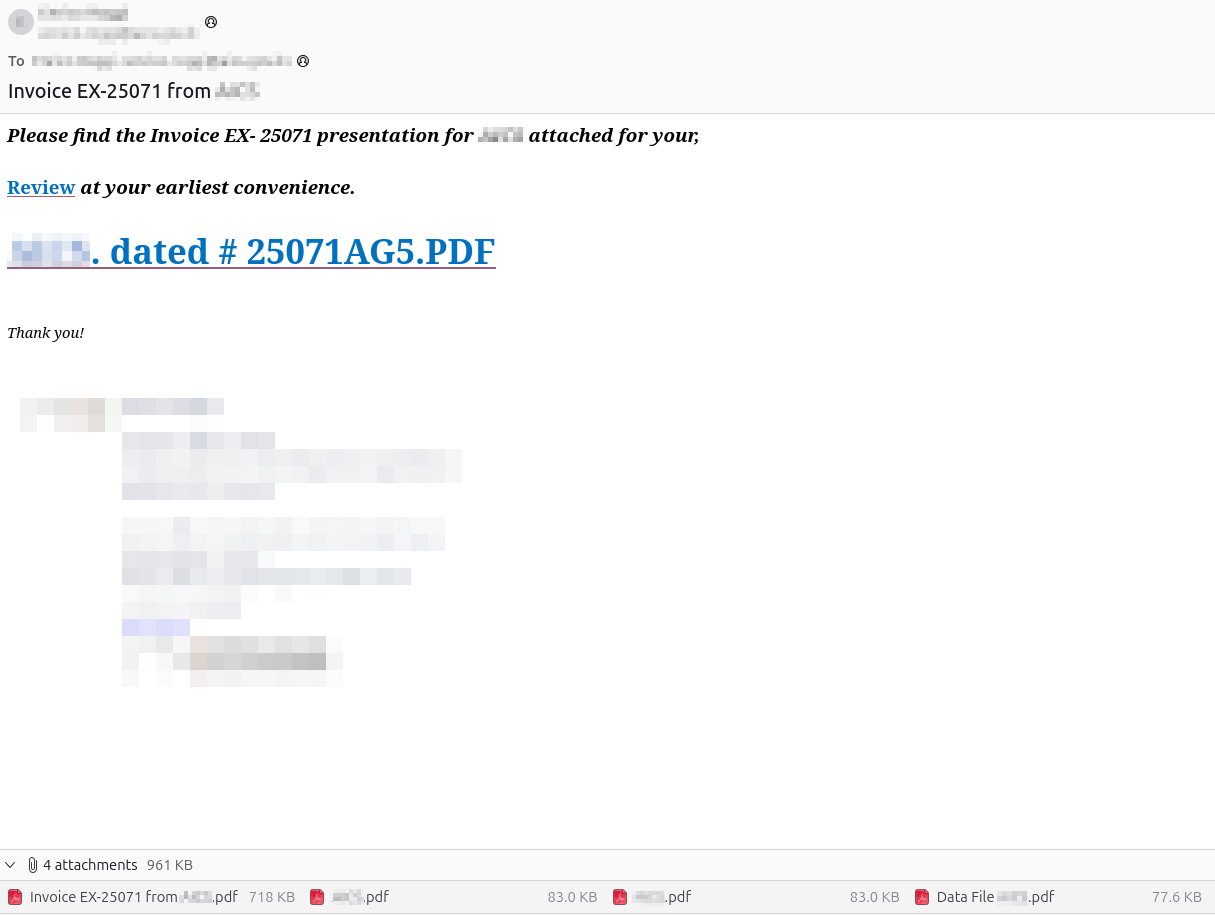
CERT-AGID has identified a phishing campaign that leverages compromised email accounts from Public Administrations to send PDFs and links leading to a malicious Figma-hosted resource which then redirects victims to a counterfeit Microsoft 365 login page to steal credentials. The campaign emphasizes brand spoofing to increase credibility, and CERT-AGID has notified affected administrations and distributed indicators of compromise. #CERT-AGID #Microsoft365
Darktrace analysts identified a DPRK-aligned campaign targeting users in South Korea that delivered a JSE script disguised as a Hangul (HWPX) document to deploy a Visual Studio Code tunnel for prolonged remote access. The attacker downloaded legitimate VS Code binaries, launched a tunnel named “bizeugene”, authorized it via a GitHub device code, and exfiltrated the tunnel token to a compromised South Korean site. #VSCodeTunnel #DPRK

Zscaler ThreatLabz identified two Pakistan-linked campaigns in September 2025—Gopher Strike and Sheet Attack—targeting Indian government entities and using novel Golang tools and private GitHub repositories for C2 and payload staging. The Gopher Strike chain uses spearphishing PDFs leading to an ISO that delivers a Golang downloader (GOGITTER), a GitHub-based backdoor (GITSHELLPAD), and a Golang shellcode loader (GOSHELL) that ultimately deploys a Cobalt Strike Beacon. #GOGITTER #GITSHELLPAD #GOSHELL #CobaltStrike #APT36 #IndianGovernment
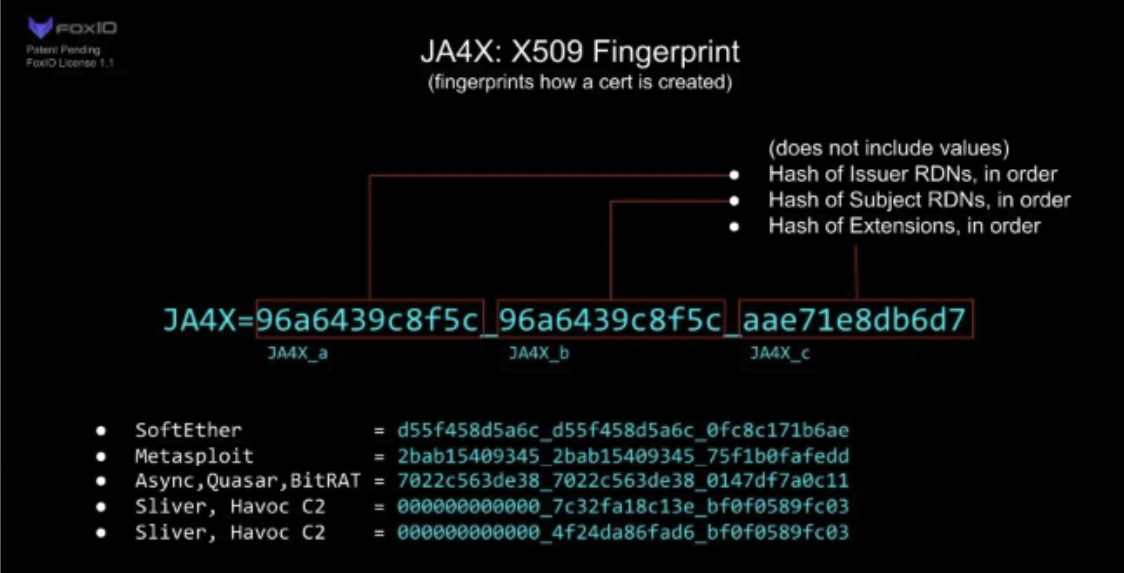
Validin has added support for JA4X fingerprints from the JA4+ suite to its platform to detect structural anomalies in X.509 certificates and improve hunting for malicious infrastructure. The post demonstrates using JA4X to uncover and narrow C2 infrastructure associated with BianLian and QuasarRAT, including example fingerprints and an advanced search combining a JA4X value with cert.not_after=”9999-12-31T23:59:59Z”. #BianLian #QuasarRAT

Modern IDEs like VS Code and Cursor rely on a trust-based model that grants extensions and trusted workspaces full user-level privileges, enabling malicious extensions or workspace files to execute arbitrary code and spawn hidden network connections. IDE-SHEPHERD is an open-source extension that injects into the extension-host Node.js runtime to intercept dangerous APIs (child_process, http, https), block malicious operations (PowerShell execution, remote downloads, auto-run tasks), and provide runtime and heuristic defenses to mitigate attacks such as the “Contagious Interview” campaign and marketplace-based compromises. #IDE-SHEPHERD #ContagiousInterview
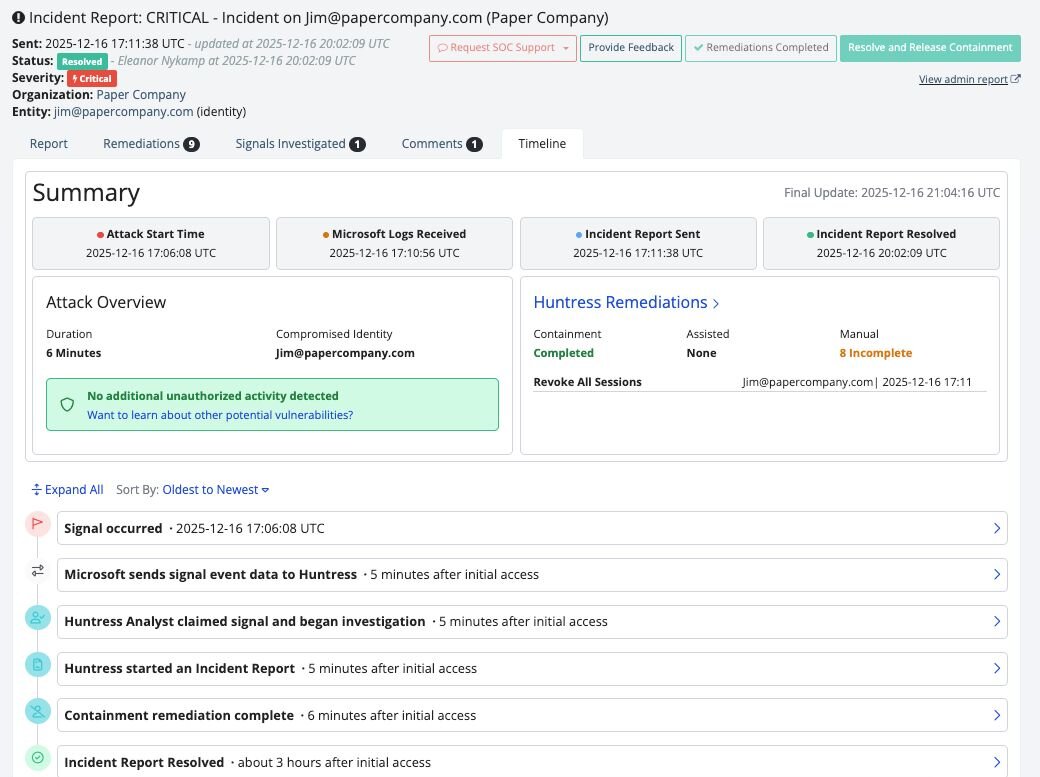
Huntress has added an Incident Report Timeline to Managed ITDR to provide a detailed, chronological view of identity-driven incidents, showing both attacker actions and Huntress remediation steps. The timeline improves visibility into potential data exfiltration, speeds impact assessment, and helps MSPs clearly communicate incident impact and response. #Huntress #ManagedITDR

Varonis Threat Labs discovered a stealthy data-exfiltration technique called Exfil Out&Look that abuses Outlook add-ins—especially those installed via Outlook Web Access (OWA)—to silently capture and transmit outgoing email content without generating Microsoft 365 audit logs. The PoC shows minimally-permissioned add-ins can hook the OnMessageSend/ItemSend event to send email contents to external…
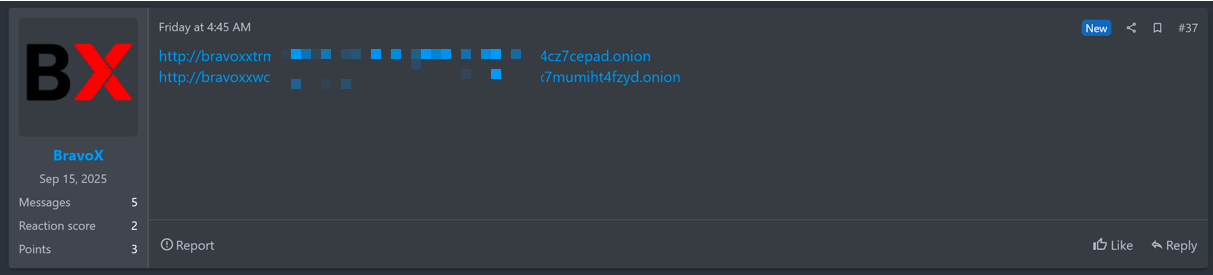
BravoX is a newly observed Ransomware-as-a-Service operation that publicly surfaced on January 23, 2026 after posting a Tor address on the RAMP forum and launching a TOR-based data leak site. The operation currently lists three alleged U.S. victims (two healthcare, one retail) and is advertising a selective affiliate model to scale its activities. #BravoX #RAMP

FortiGuard Labs describes a multi-stage Windows-focused campaign that uses social-engineered archives and LNK-triggered PowerShell to deploy staged loaders, abuse Defendnot to disable Microsoft Defender, install Amnesia RAT for extensive data theft and surveillance, and finally deliver Hakuna Matata–derived ransomware and a WinLocker to encrypt and lock victims’ systems. The operation leverages GitHub and Dropbox for modular hosting and the Telegram Bot API for C2 and exfiltration, while using registry and policy manipulation to suppress defenses and destroy recovery options. #Defendnot #AmnesiaRAT