FortiGuard Labs discovered a Base64-encoded PHP web shell named EncystPHP deployed by exploiting FreePBX Endpoint Manager vulnerability CVE-2025-64328, enabling remote command execution, persistence, and telephony abuse. The campaign, attributed to INJ3CTOR3, delivered droppers from 45[.]234[.]176[.]202 (crm[.]razatelefonia[.]pro), created a root-level user and SSH backdoor, and maintained persistence via cron jobs and widespread web shell copies. #EncystPHP #FreePBX
Category: Threat Research
RedKitten is a January 2026 campaign targeting Iranian interests that uses weaponized XLSM documents to deploy a C# implant (SloppyMIO) which retrieves configuration via steganographic images on GitHub, modules on Google Drive, and communicates with operators via Telegram. The campaign demonstrates AppDomainManager injection for execution, scheduled-task persistence, and likely AI-assisted development;…

Check Point Research’s Cyber Security Report 2026 synthesizes findings from 2025 showing AI is embedded across the attack lifecycle, accelerating reconnaissance, social engineering, and malware development while introducing new governance risks. The report also highlights fragmented, data-only ransomware extortion, exploitation of unmonitored edge and perimeter devices, geopolitically aligned cyber activity, and measurable vulnerabilities in Model Context Protocols and ungoverned AI usage. #ModelContextProtocols #UnmonitoredDevices
Threat actors register accounts on legitimate services and embed phone-scam text in document names, meeting descriptions, or account name fields to have legitimately-sent emails redirected and resent to victims without changing the visible From header. These redirected emails bypass SPF, DKIM, DMARC and many secure email gateways by using legitimate infrastructure like Exchange Online and services such as Zoom. #Zoom #ExchangeOnline
-is-Abused-for-Credential-Theft_Figure1.PNG)
Threat actors are abusing Amazon Web Services—notably Amazon S3, Amazon SES, and AWS Amplify—to host credential-phishing pages and to send obfuscated phishing emails that leverage trusted AWS domains. These capabilities, combined with easy provisioning, free tiers, and weak or misconfigured IAM and logging, enable scalable campaigns that evade some traditional email security controls and complicate takedown and forensics. #AmazonS3 #AmazonSES
TA584 increased its operational tempo in 2025, expanded geographic and language targeting, and changed its attack chains to include ClickFix social engineering, layered redirects, rapid domain rotation, and new payloads such as Tsundere Bot alongside XWorm. These changes produced high campaign churn, frequent use of PowerShell/Node.js-based installers and WebSocket/Ethereum-based C2 retrieval,…
Google Threat Intelligence Group and partners disrupted the IPIDEA residential proxy network by taking down C2 and marketing domains, sharing SDK and infrastructure intelligence, and enforcing Play Protect to remove apps embedding IPIDEA SDKs. The network had enrolled millions of consumer devices via trojanized or monetized SDKs and was abused by numerous threat groups and botnets including BadBox2.0. #IPIDEA #BadBox2.0
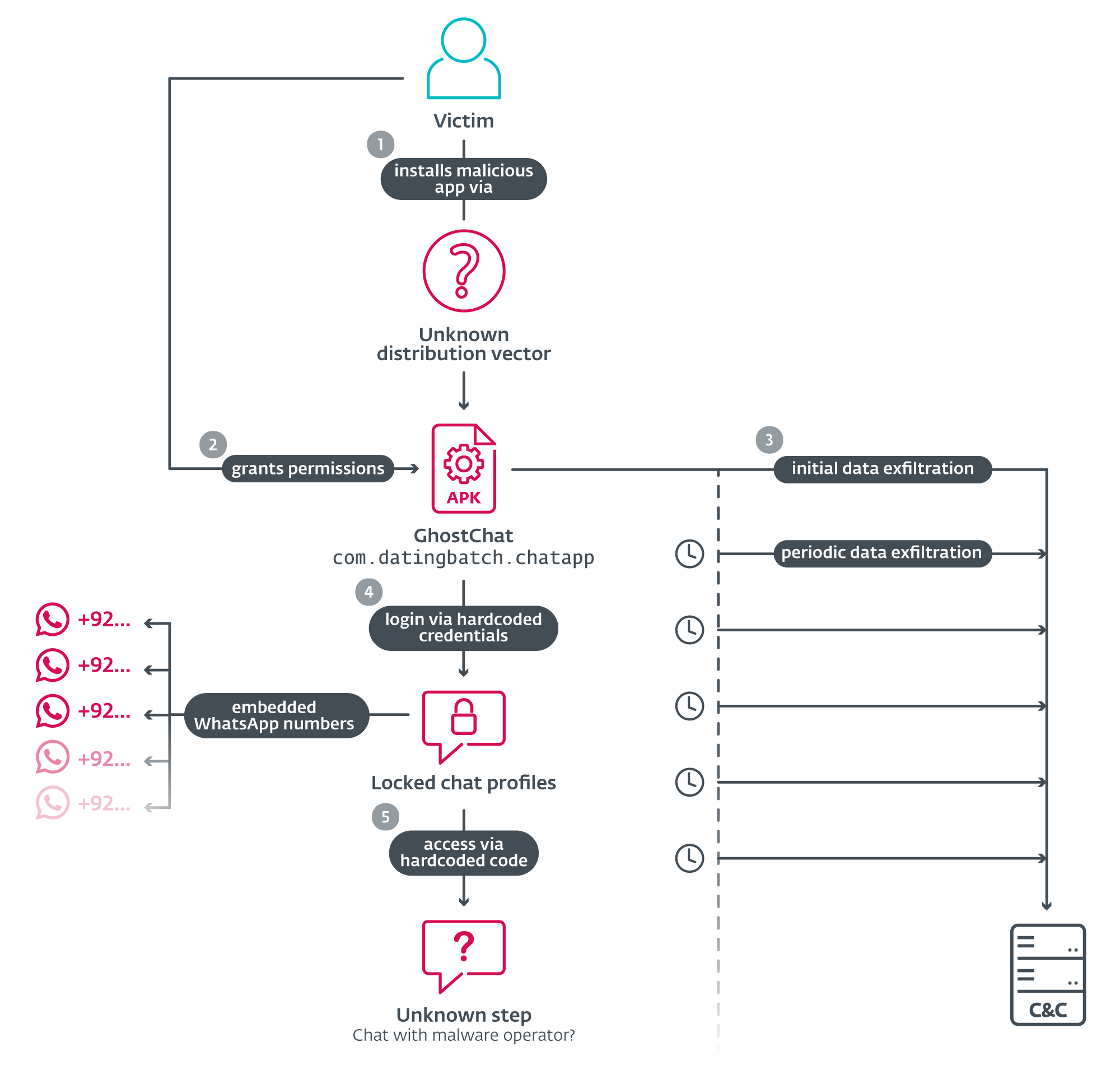
ESET researchers uncovered a targeted Android spyware campaign in Pakistan using a fake dating/chat app called GhostChat that lures victims with “locked” female profiles and hardcoded access codes while silently exfiltrating device data. The investigation links GhostChat to broader activity including ClickFix DLL payloads and a WhatsApp QR-linking scheme (GhostPairing) using fake government websites and the C&C domain hitpak[.]org. #GhostChat #PKCERT

Downloading cracks, keygens, or cheat tools can deliver malware or embed critical vulnerabilities into systems, as shown by examples like iOS jailbreaks, Windows cheat drivers, and the macOS AutoHackGUI helper that runs as root. Researchers reversed AutoHackGUI and demonstrated an XPC-based exploit that connects to the Mach service io.github.marlkiller.AutoHackGUIHelper to execute arbitrary commands as root, illustrating how non-malicious cracking tools can enable local privilege escalation. #AutoHackGUI #IDAPro

A Vietnamese-linked threat actor is using AI-assisted code to run a widespread phishing campaign that lures victims with job-offer themed messages and delivers payloads including PureRAT and HVNC. The attacker uses ZIP/RAR archives or cloud-hosted downloads, DLL sideloading, and persistence mechanisms to maintain access and may be selling compromised access to other actors. #PureRAT #HVNC
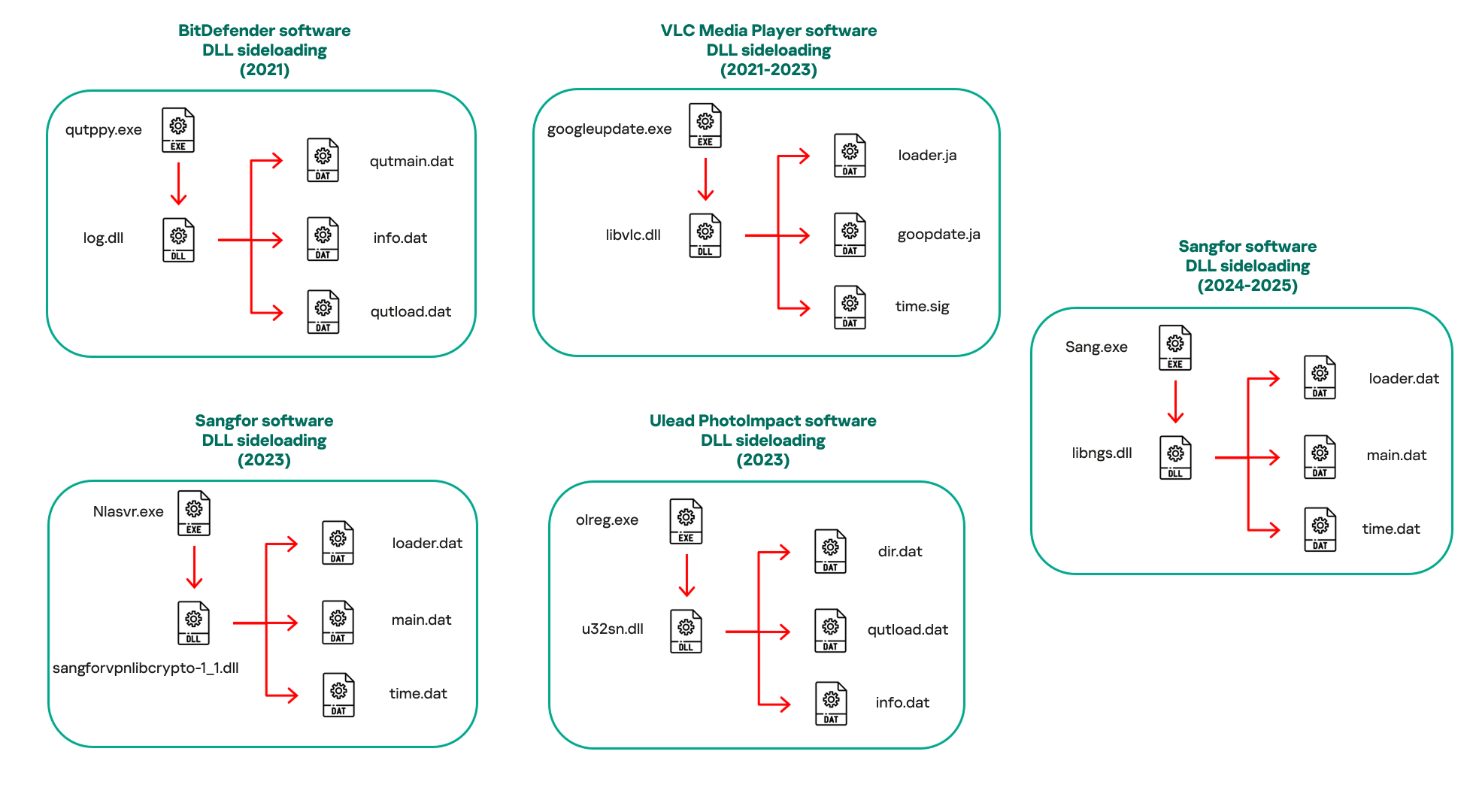
HoneyMyte (aka Mustang Panda/Bronze President) continues active espionage across Southeast Asia and Europe in 2025, deploying an updated toolset that includes an enhanced CoolClient backdoor, browser credential stealers, USB worms, PlugX, ToneShell, QReverse and multiple data-theft scripts. The report details CoolClient’s DLL sideloading execution flow, new features such as clipboard monitoring and an HTTP proxy credential sniffer, and multiple exfiltration channels including FTP, Pixeldrain and Google Drive. #HoneyMyte #CoolClient

The GTIG reported widespread exploitation of CVE-2025-8088 in WinRAR using Alternate Data Streams and path traversal to drop payloads into the Windows Startup folder for persistence across state-sponsored and financially motivated campaigns. Defenders are urged to patch immediately and hunt for indicators such as malicious RAR archives, LNK/HTA/BAT/CMD payloads, and the provided SHA-256 hashes. #CVE-2025-8088 #WinRAR

OpenSSL disclosed a set of vulnerabilities on January 27, 2026, including one high-severity, one moderate-severity, and ten low-severity issues affecting OpenSSL 1.0.2, 1.1.1, and the 3.x series (3.0, 3.3–3.6). The most critical is CVE-2025-15467, a pre-auth stack buffer overflow in CMS AuthEnvelopedData AEAD parsing that can cause crashes and may enable RCE, while CVE-2025-11187 is a PBKDF2-related overflow in PKCS#12 MAC verification that is more likely to cause denial-of-service; mitigations include upgrading affected OpenSSL builds and runtimes and monitoring services that parse untrusted CMS/PKCS#12 inputs. #OpenSSL #CVE-2025-15467
Proofpoint tracked state-sponsored and financially motivated clusters using SquarePhish2 and Graphish to bypass the OAuth device code authorization process and gain access to victims’ Microsoft 365 accounts, leading to account takeover and data exfiltration. Researchers collated and analyzed 46 IoCs (21 subdomains including four variations, 22 domains, one IP, and two email addresses) and uncovered additional connected artifacts such as 91 email-connected domains and 23 more IPs. #SquarePhish2 #Graphish

Zscaler ThreatLabz analyzed the Sheet Attack campaign and identified three new backdoors—SHEETCREEP, FIREPOWER, and MAILCREEP—that abuse Google Sheets, Firebase, and Microsoft Graph API for C2 while using PDF and LNK lures to target Indian government entities. The report also documents signs of generative AI use in malware development and assesses with medium confidence a Pakistan-linked origin or connection to APT36. #SHEETCREEP #APT36
