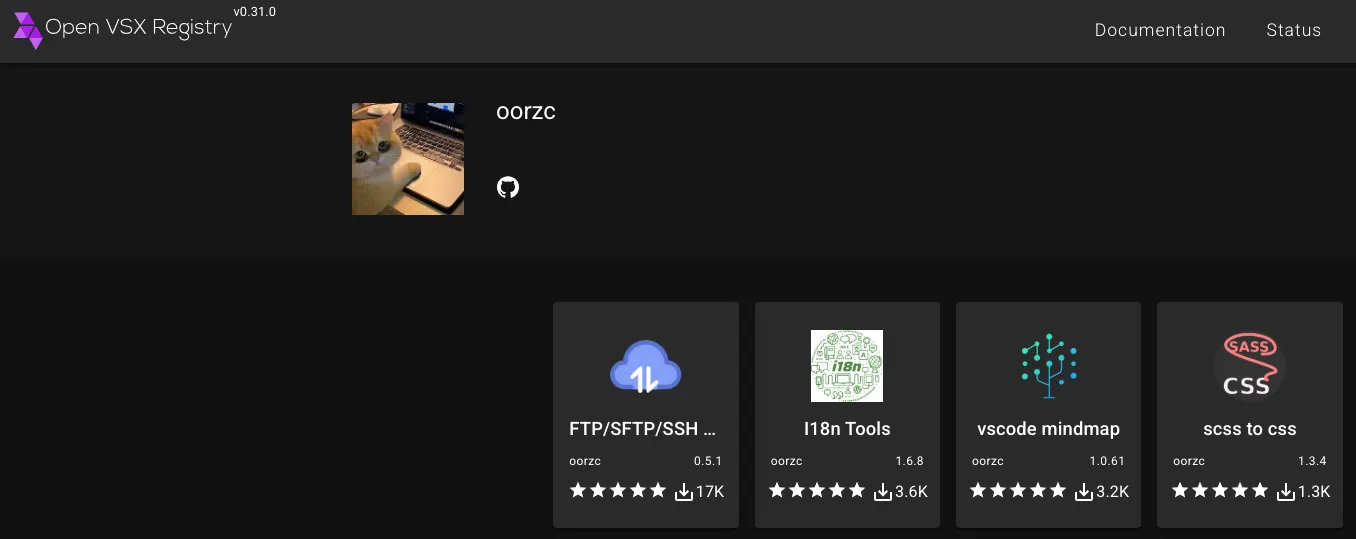
Socket researchers identified a developer-account compromise in the Open VSX Registry that published malicious updates to four oorzc extensions embedding the GlassWorm loader, using staged AES-encrypted loaders and Solana transaction memos as a dynamic dead drop. The macOS-focused follow-on payload steals browser cookies, wallet files, keychain, AWS and SSH credentials and establishes persistence via a LaunchAgent; remove affected extensions, check for persistence, and rotate exposed tokens and keys. #GlassWorm #OpenVSX
Category: Threat Research

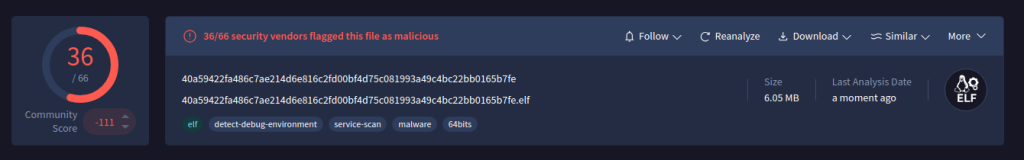
LockBit 5.0 is an evolved, cross-platform ransomware variant that uses the ChaCha20 256-bit stream cipher across Windows, Linux, and ESXi environments while adopting modular, stealthy behaviors to evade detection. The sample analyzed scored 1/65 on VirusTotal and the variant includes features such as in-memory execution, ETW patching, VSS Coordinator usage for shadow copy removal, and an irreversible hashing method for API/process resolution. #LockBit5.0 #ChaCha20
Arsink is a cloud-native Android RAT that exfiltrates extensive personal data and grants remote operators intrusive control over infected devices while abusing legitimate cloud services for C2 and media/file exfiltration. The campaign deployed 1,216 distinct APKs across global social-engineered distribution channels and used 317 Firebase Realtime Database endpoints, Google Apps Script/Drive, and Telegram for C2 and exfiltration. #Arsink #Firebase
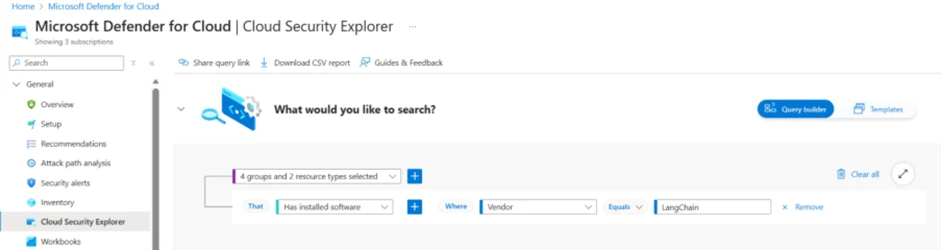
The article analyzes CVE-2025-68664 (LangGrinch), a high-severity serialization injection vulnerability in the langchain-core Python package that can enable secret extraction, unintended class instantiation, and malicious side effects via an unescaped reserved lc marker. It outlines mitigation steps—upgrade to patched versions, use Microsoft Defender for Cloud and Defender XDR for discovery and hunting, and integrate Defender workflows with GitHub for faster remediation. #LangGrinch #LangChain

The Android app Hicas (package com.apptool.hicash.newhicash) is distributed as a travel utility but dynamically switches on Indian devices to a fully web-based, coercive loan platform delivered via remote WebView and aggressive UI pressure. Static and dynamic analysis revealed heavy obfuscation, runtime XOR string decryption, contact harvesting, excessive permissions, and remote configuration hosted at in-h5.oss-ap-southeast-1.aliyuncs.com and bksn515.vercel.app, indicating a Chinese-operated loan ecosystem with coercive repayment tactics. #Hicas #hicas.tech
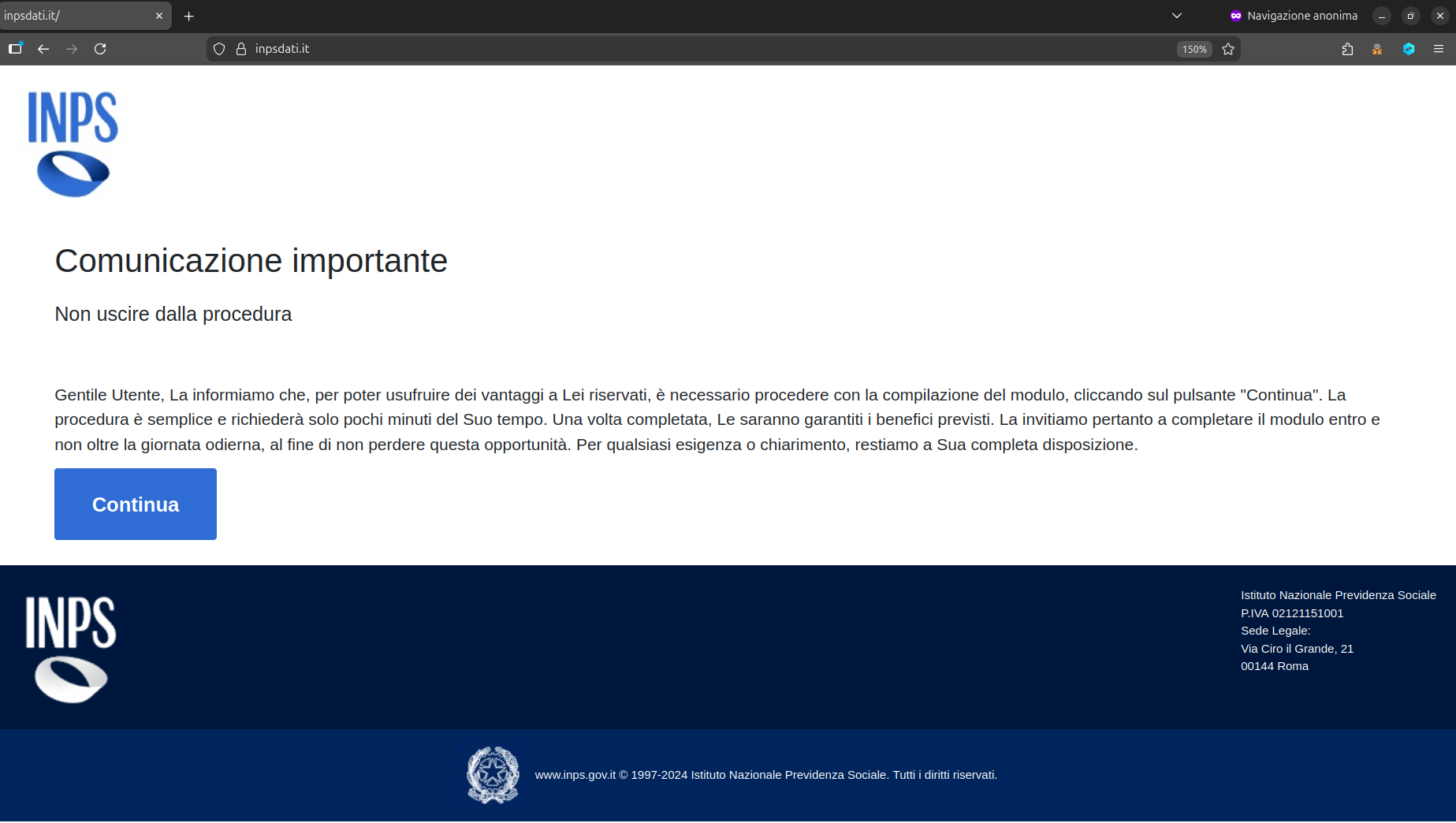
CERT-AGID received notification from INPS about an active phishing campaign that uses the INPS name and logo to trick victims into uploading identity documents and personal data. The fraudulent site has added new pages requesting CUD and detailed employment/income information to build more complete victim profiles potentially usable for higher-value financial fraud. #INPS #CERT-AGID

Cyble uncovered ShadowHS, a fileless Linux post‑exploitation framework that uses an encrypted, obfuscated POSIX shell loader to reconstruct and execute a weaponized variant of hackshell entirely in memory. The framework emphasizes stealth and operator-driven control—fingerprinting EDR/AV, enabling covert GSocket-backed rsync exfiltration, credential theft, lateral movement, and on‑demand cryptomining—while leaving no persistent disk artifacts. #ShadowHS #hackshell

AI agents that select and execute capabilities based on language and metadata introduce a new attack surface called agentic tool chain attacks, which manipulate tool descriptions, schemas, and context to cause data leaks or unauthorized actions without changing code. Effective defenses require reasoning-layer controls such as signed manifests, version pinning, strict…
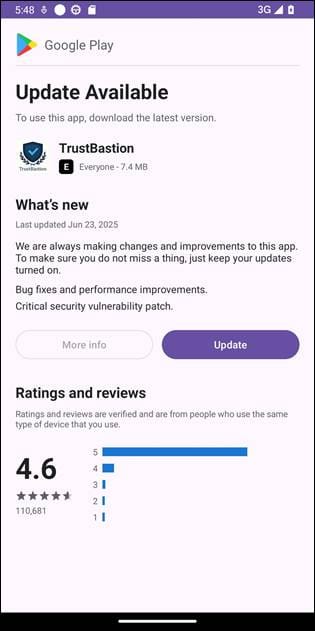
Bitdefender researchers uncovered an Android RAT campaign that uses a malicious dropper (TrustBastion) and Hugging Face as a hosting/staging platform to deliver polymorphic APK payloads. The malware abuses Accessibility Services, screen-capture/overlay permissions and fake financial interfaces to steal credentials and exfiltrate data via a C2 at 154.198.48.57. #TrustBastion #HuggingFace…
Attackers compromised a contractor’s mailbox and hijacked an active executive approval thread to deliver a phishing link that led through multi-step redirects and Cloudflare Turnstile gates to an EvilProxy AiTM Microsoft credential‑theft page. ANY.RUN researchers detonated the message in a sandbox, revealed the full execution chain, and linked the incident to…
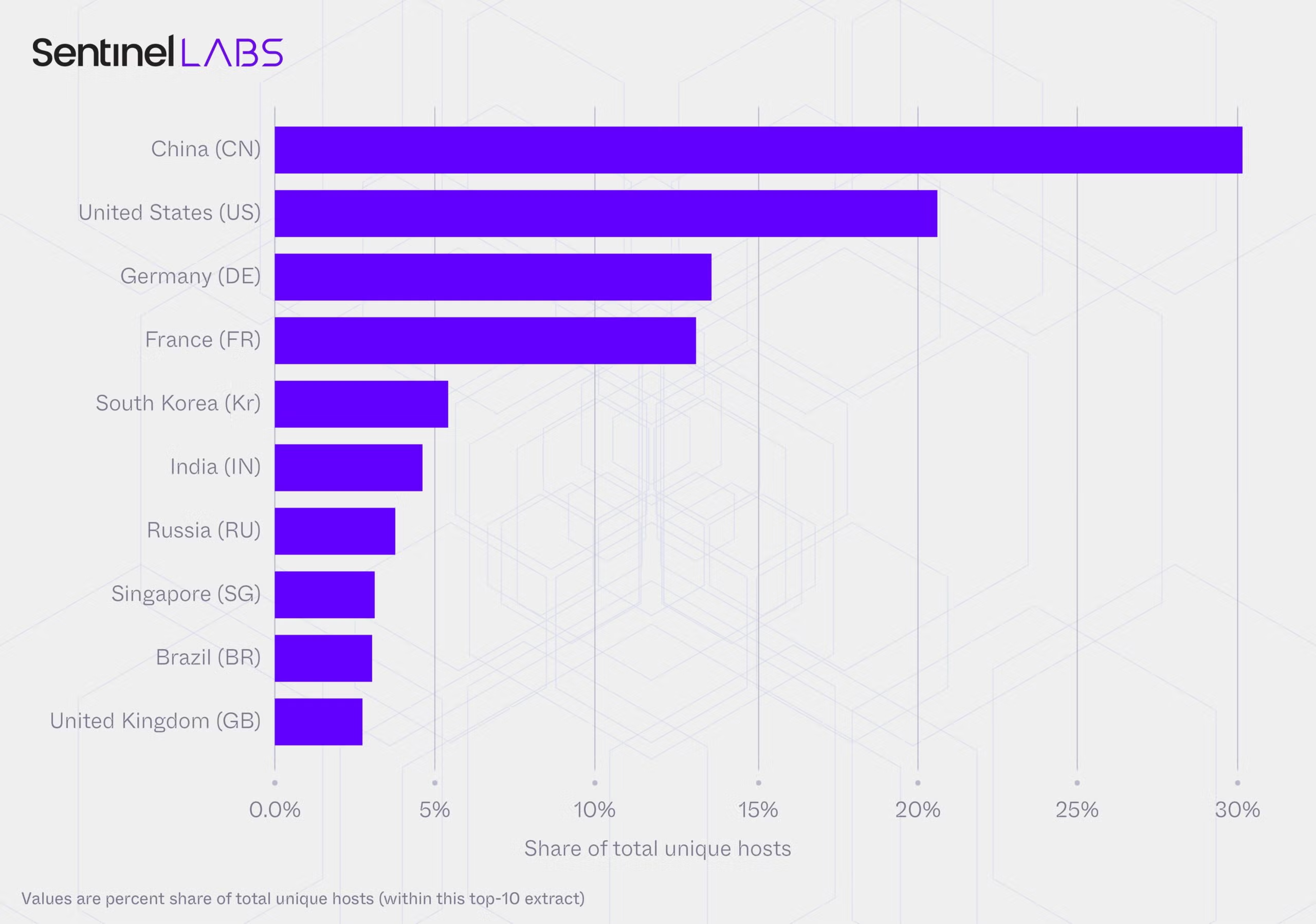
A joint SentinelLABS and Censys study found an unmanaged, publicly accessible layer of Ollama deployments spanning 175,108 hosts across 130 countries, with a persistent core of roughly 23,000 hosts generating the majority of observed activity. Nearly half of hosts expose tool-calling and multimodal capabilities while the ecosystem converges on a small set of model families and the Q4_K_M 4-bit quantization format, creating a brittle monoculture and governance gaps that complicate attribution and defense. #Ollama #Q4_K_M
On January 20 a supply-chain compromise of MicroWorld’s eScan update server distributed a malicious Reload.exe to customers, prompting Kaspersky to detect and block related attacks while eScan contained the incident after Morphisec notified them the next day. Reload.exe modified the HOSTS file to block antivirus updates, established persistence via scheduled tasks (example: CorelDefrag), wrote consctlx.exe to disk, and communicated with attacker control servers to download additional payloads. #eScan #Reload.exe
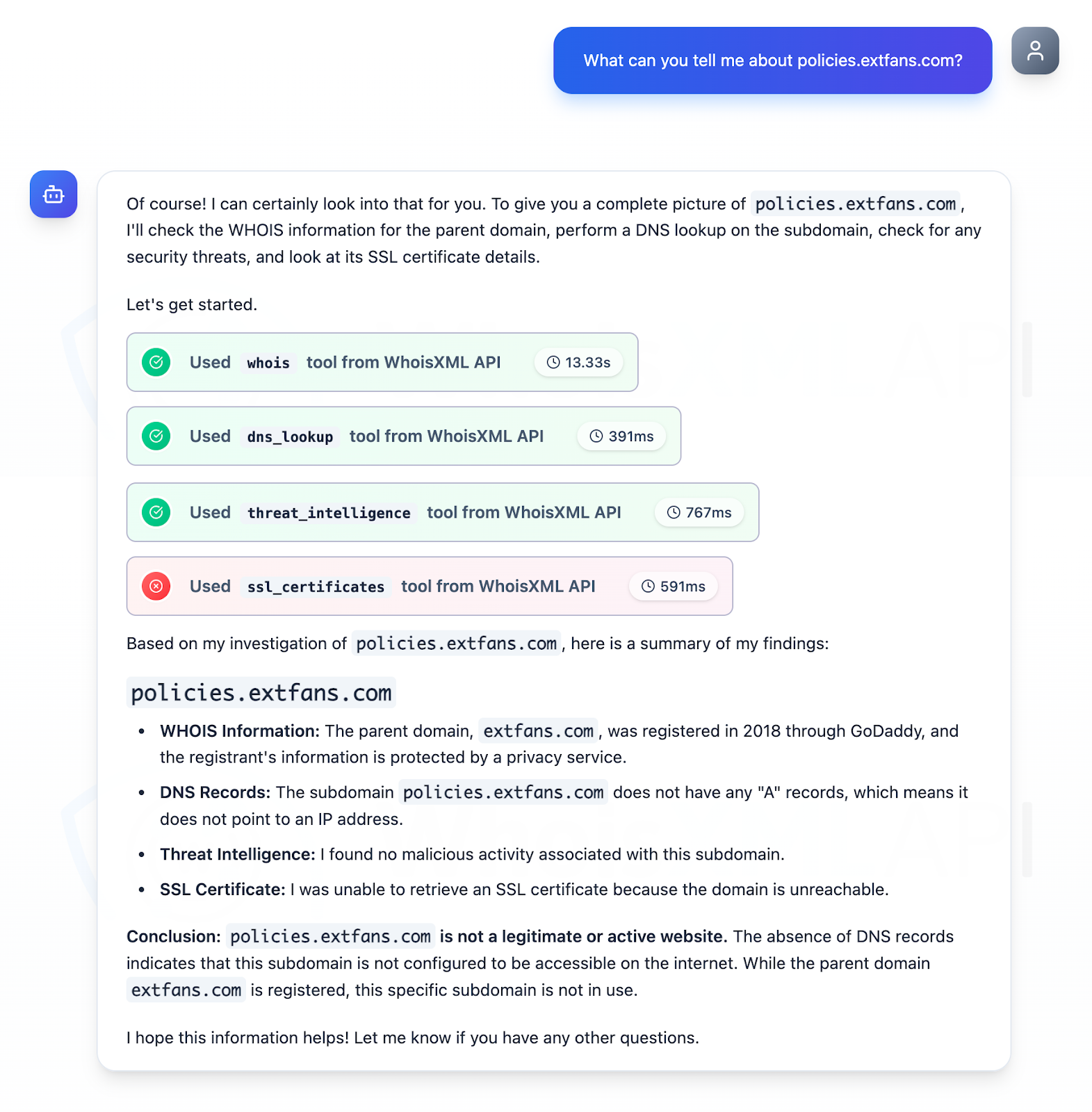
Koi Security tracked the threat group “DarkSpectre” across multiple campaigns (Zoom Stealer, ShadyPanda, GhostPoster) that collectively affected over 8.8 million users and uncovered a new GhostPoster-linked Opera extension installed nearly 1 million times by December 2025. Their analysis produced 15 prioritized IoCs (three subdomains, seven domains, one IP, four emails), revealed aged-domain reuse and China-hosted infrastructure, and discovered 8,579 email-connected domains for further investigation. #DarkSpectre #GhostPoster
IClickFix is a widespread malicious JavaScript framework that has been injected into over 3,800 compromised WordPress sites since at least December 2024 to display a fake Cloudflare Turnstile (ClickFix) lure and deliver downstream payloads. The framework uses a YOURLS-based Traffic Distribution System, multi-stage obfuscated JavaScript, and clipboard-based social engineering to install NetSupport RAT via a PowerShell dropper. #IClickFix #NetSupportRAT
This report analyzes a cross‑platform Python‑based Remote Access Trojan (RAT) packaged as an ELF that performs system fingerprinting, generates a semi‑persistent UID, communicates with an unencrypted HTTP C2 (/api/{uid}/hello), supports threaded remote command execution, unrestricted file transfer, screenshot capture, ZIP bundling, and persistence via XDG autostart and the Windows Run key. K7 Labs observed high detection rates for the sample (MD5: 0fed60850aa38127095f21182cc2c85d) and recommends keeping protections like K7 Total Security up to date. #PythonRAT #K7Labs