Between June and December 2025, the state-sponsored group Lotus Blossom compromised the shared hosting environment for Notepad++ updates and intercepted update traffic to serve malicious installers that delivered the Chrysalis backdoor and Cobalt Strike beacons. The campaign used DLL side-loading, Lua script injection and an adversary-in-the-middle filtering capability to selectively target…
Category: Threat Research

Datadog observed an active campaign using fake GitHub repositories and ClickFix landing pages to social-engineer victims into pasting commands that install macOS infostealers and (in some builds) Windows components. The actor iterates on MacSync and a persistent SHub Stealer v2.0—adding credential validation, broad file and wallet collection, dynamic anti-analysis, and a LaunchAgent-based beacon for remote command execution. #SHub #MacSync
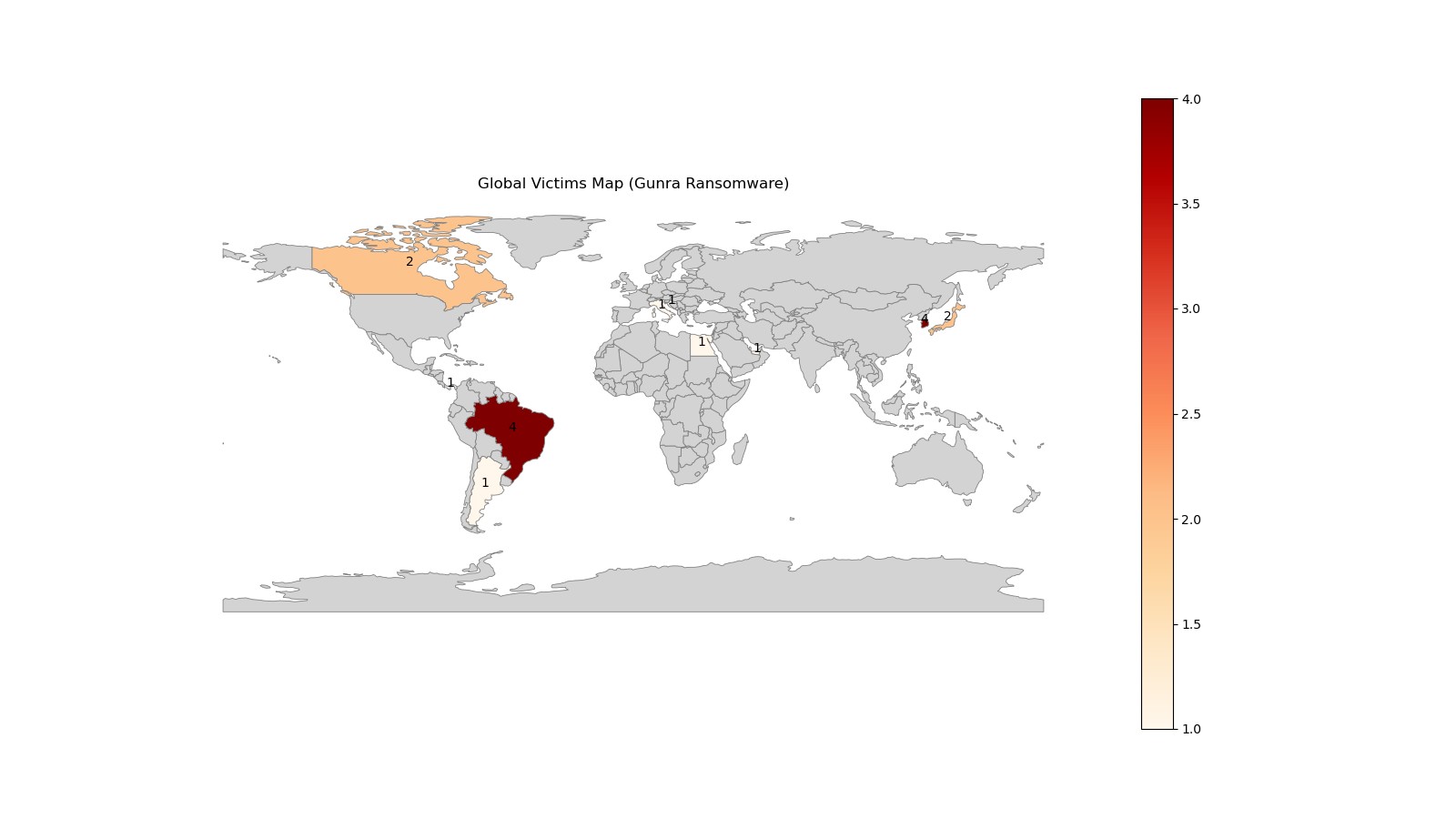
CloudSEK researchers infiltrated a newly launched Gunra affiliate program in January 2026, obtaining RaaS management panel credentials and a live ransomware sample for detailed technical analysis. The Gunra locker is an offline-capable, multi-threaded encryptor that uses per-file ChaCha20 keys protected with RSA-4096, selective system exclusions, .ENCRT renaming, and a Tor-based payment portal. #Gunra #CloudSEK

Fancy Bear (APT28) remains an active Russian state‑aligned espionage actor that quickly adopts newly disclosed vulnerabilities and uses spear‑phishing and credential harvesting to maintain long‑term access to government, defense, energy, and communications targets. The group recently weaponized a Microsoft Office vulnerability to compromise organizations in Eastern Europe and the EU, demonstrating a shift toward lightweight, high‑ROI tradecraft. #FancyBear #CVE-2026-21509

GTIG observed widespread misuse of generative AI in late 2025, including an uptick in model extraction (“distillation”) attempts and AI-augmented operations such as reconnaissance, hyper-personalized phishing, and AI-assisted malware development. Notable examples include the HONESTCUE downloader that called Gemini’s API to generate stage-two code and the COINBAIT phishing kit built with AI-assisted code generation and hosted on legitimate services (#HONESTCUE #COINBAIT)

Socket Threat Research discovered a malicious Chrome extension named CL Suite by @CLMasters that advertises Meta Business Suite scraping and 2FA generation while exfiltrating TOTP seeds, current 2FA codes, Business Manager contact CSVs, and analytics to threat actor infrastructure. The extension reports data to getauth[.]pro (and optionally forwards payloads to a Telegram channel), undermining 2FA and enabling account takeover and long-term business asset hijacking. #CLSuite #MetaBusinessSuite
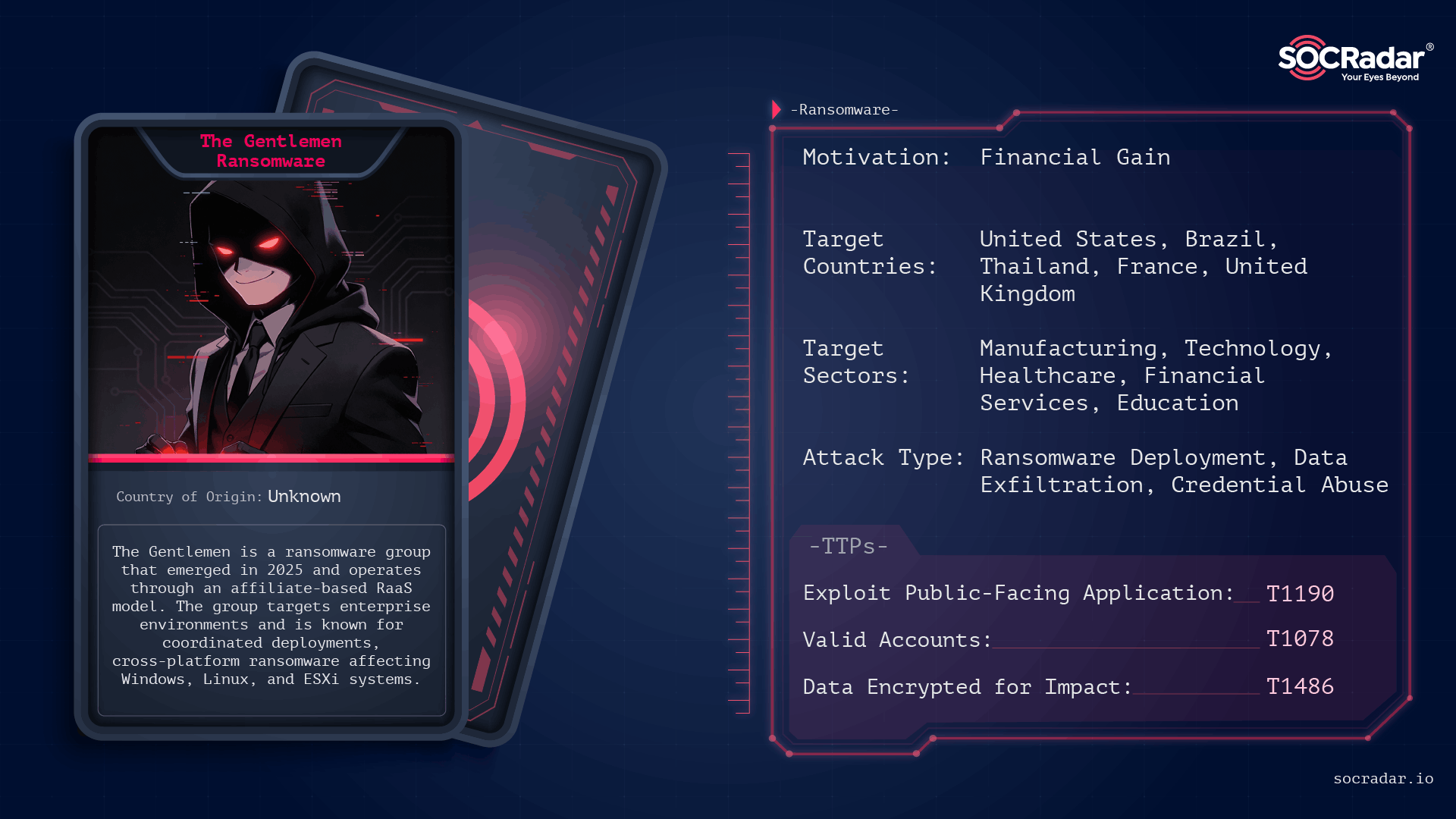
The Gentlemen is an operationally disciplined ransomware group first observed in mid-to-late 2025 that conducts double‑extortion attacks across Windows, Linux, NAS, BSD, and ESXi environments using password‑protected, operator-driven builds. Their campaigns leverage exposed internet-facing services and compromised administrative credentials, and victims have been publicly listed on a Dark Web leak site. #TheGentlemen #ESXi

A multi-stage phishing campaign consistently delivers the Stealerium .NET infostealer by reusing a stable execution core while varying lure themes and front-door delivery methods. #Stealerium #DepartmentOfState
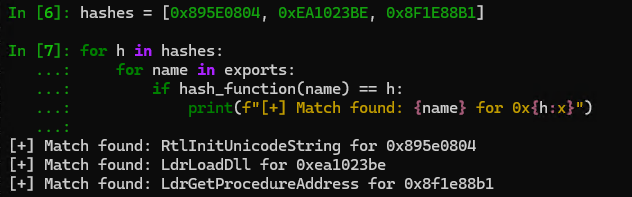
OysterLoader (aka Broomstick / CleanUp) is a multi-stage C++ loader distributed via fake signed MSI installers that delivers payloads (notably Rhysida ransomware and commodity stealer Vidar) using staged shellcode, custom LZMA, and steganographically hidden DLLs. Its operators use extensive obfuscation (API-hammering, dynamic API hashing, custom Base64 alphabets and RC4), robust HTTP-based C2 with fallback servers, scheduled-task persistence, and anti-analysis checks. #OysterLoader #Rhysida

ReversingLabs uncovered a modular software‑supply‑chain campaign called graphalgo, attributed to North Korea’s Lazarus Group, that targets JavaScript and Python developers via fake recruiter job tasks and malicious packages on npm and PyPI. The operation uses fake company personas (e.g., Veltrix Capital), social outreach (LinkedIn, Facebook, Reddit), dependency-based infection (packages such as bigmathutils and graphnetworkx), and multistage downloaders that deploy a token‑protected RAT communicating with codepool[.]cloud. #LazarusGroup #graphalgo
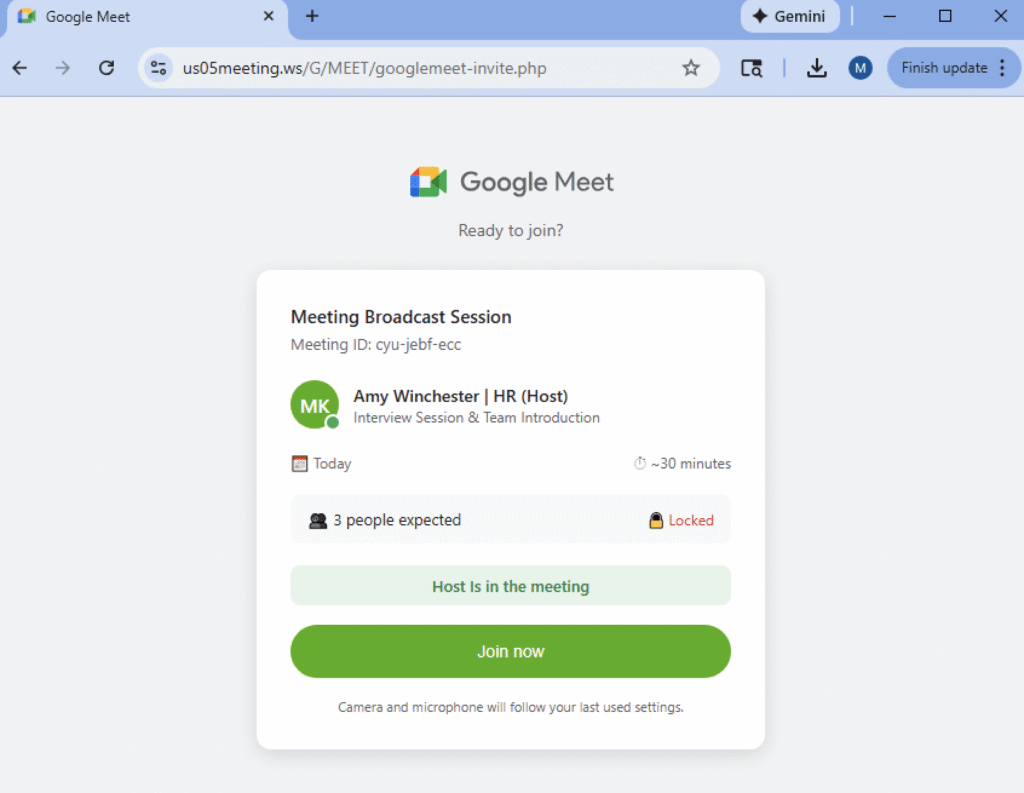
Netskope Threat Labs is tracking phishing campaigns that weaponize fake video conference invites for Zoom, Microsoft Teams, and Google Meet, tricking users into downloading a “mandatory” software update from typo-squatted domains. Those updates are digitally signed remote monitoring and management (RMM) tools — including Datto RMM, LogMeIn, and ScreenConnect — that give attackers administrative access and a platform to exfiltrate data or deploy additional malware. #DattoRMM #ScreenConnect
Researchers observed a mass campaign distributing pirated games that deliver a previously unknown loader, RenEngine, via a modified Ren’Py-based launcher which installs HijackLoader and ultimately deploys stealers such as Lumma and ACR Stealer. Kaspersky detects samples as Trojan.Python.Agent.nb / HEUR:Trojan.Python.Agent.gen and notes extensive use of XOR decryption, DLL overwriting, process injection, and transacted file techniques. #RenEngine #HijackLoader
Bitdefender analysis shows LummaStealer has rapidly rebounded after a 2025 takedown by rebuilding infrastructure, leveraging social-engineering lures and multiple loaders — most prominently CastleLoader — to deliver in-memory payloads and exfiltrate credentials, cookies, documents and crypto data. Detection opportunities include an anomalous DNS lookup pattern from CastleLoader and behavioral indicators around…
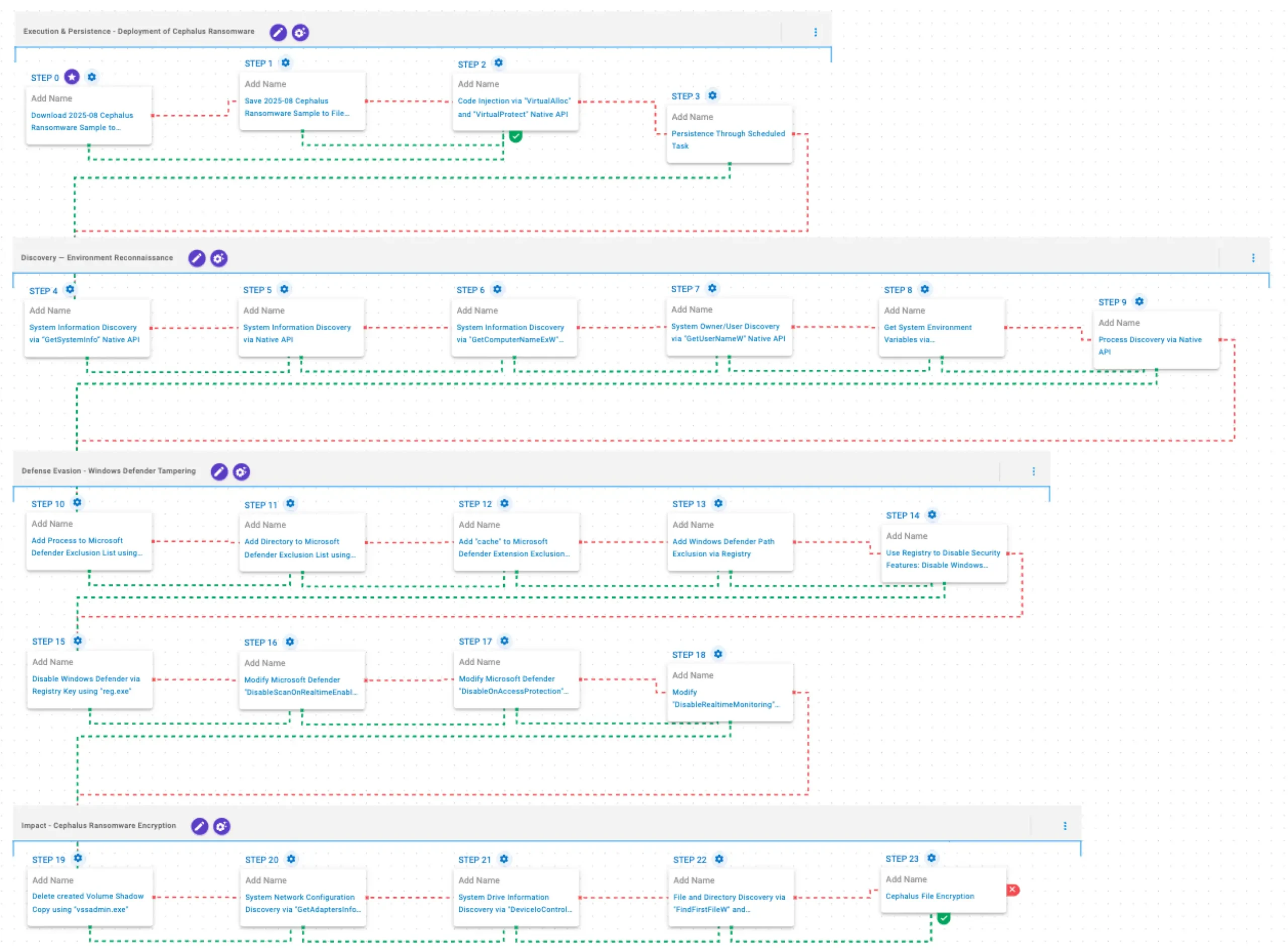
Cephalus is a Go-developed ransomware family observed from June 2025 that gains initial access mainly through exposed RDP without MFA, often using stolen credentials, and follows a double-extortion model by exfiltrating sensitive data prior to encryption. AttackIQ published an emulation of Cephalus TTPs to help organizations validate controls and test detection/prevention…

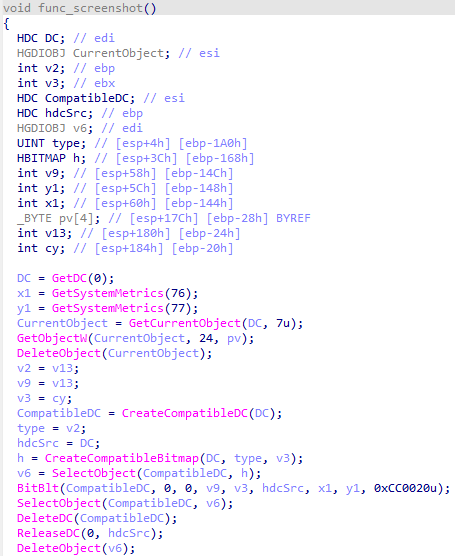
This analysis details a multi-stage Windows attack that begins with a fake Cloudflare CAPTCHA (ClickFix) social-engineering prompt to trick victims into executing malicious PowerShell, which in-memory loads shellcode, a PE downloader, and ultimately the StealC information stealer. The StealC payload harvests browser credentials, crypto wallets, Steam and Outlook data, system fingerprints, and screenshots exfiltrating data to RC4-encrypted HTTP C2 servers. #StealC #ClickFix
