HoneyMyte (aka Mustang Panda/Bronze President) continues active espionage across Southeast Asia and Europe in 2025, deploying an updated toolset that includes an enhanced CoolClient backdoor, browser credential stealers, USB worms, PlugX, ToneShell, QReverse and multiple data-theft scripts. The report details CoolClient’s DLL sideloading execution flow, new features such as clipboard monitoring and an HTTP proxy credential sniffer, and multiple exfiltration channels including FTP, Pixeldrain and Google Drive. #HoneyMyte #CoolClient
Keypoints
- HoneyMyte updated its toolset in 2025, notably enhancing the CoolClient backdoor and deploying multiple browser login data stealers and data-theft/recon scripts across Myanmar, Mongolia, Malaysia, Thailand and Russia.
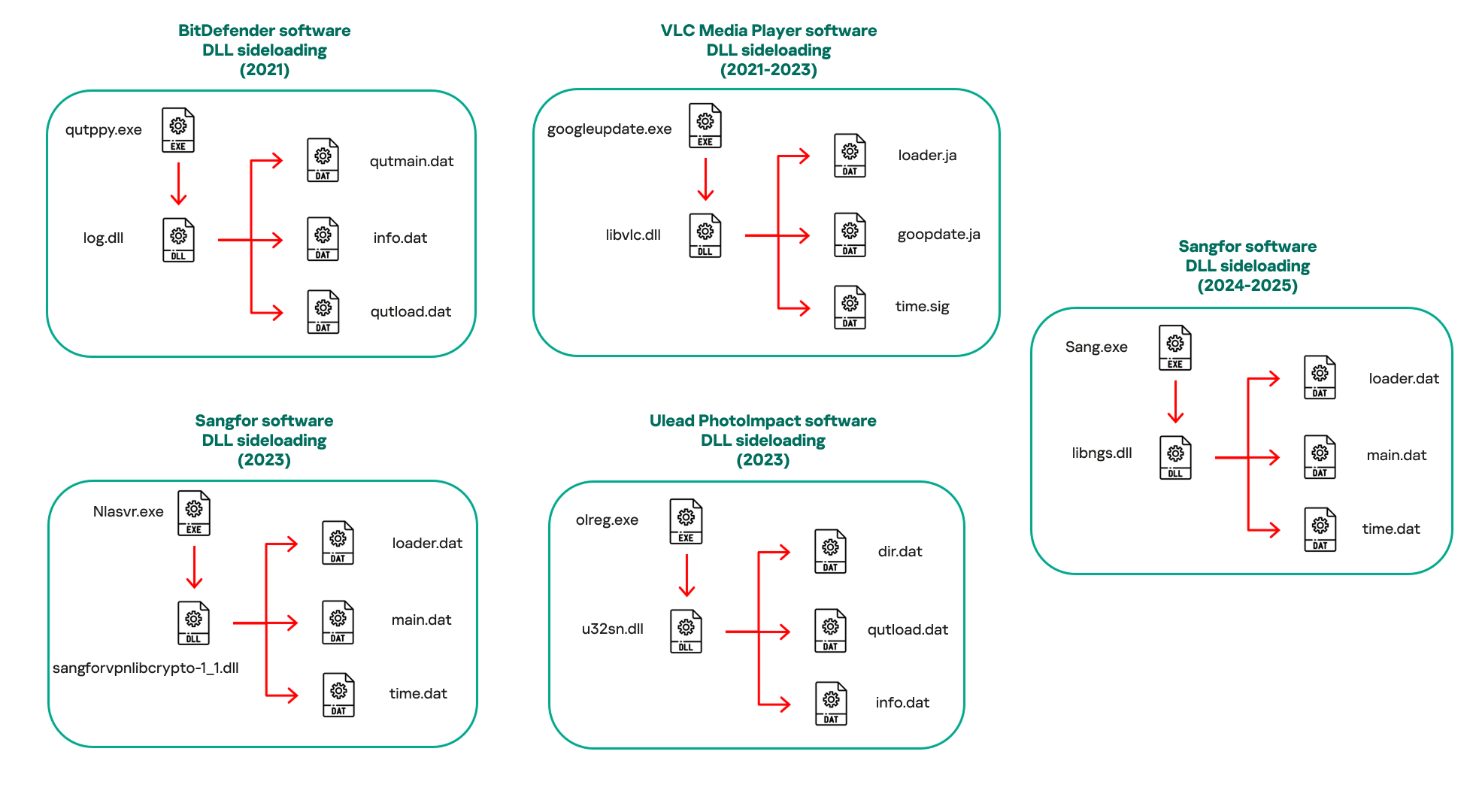
- CoolClient is commonly delivered via encrypted loader files and DLL sideloading using legitimate signed binaries (e.g., Sangfor executables); it supports plugin staging, keylogging, TCP tunneling, reverse proxy and file operations.
- The latest CoolClient adds clipboard monitoring and an HTTP proxy credential sniffer that intercepts raw TCP payloads to extract Proxy-Authorization Basic credentials.
- CoolClient’s execution flow uses staged encrypted files (loader.dat, main.dat, time.dat) and process injection into a launcher process (write.exe) with multiple parameter modes (install, work, passuac) including UAC bypass and scheduled task persistence.
- HoneyMyte deployed dedicated CoolClient plugins observed in telemetry (FileMgrS.dll, RemoteShellS.dll, ServiceMgrS.dll) to extend file management, remote shell and service management capabilities.
- Post-exploitation activity included browser credential stealers targeting Chrome/Edge/Chromium-based browsers, and scripts (1.bat, Ttraazcs32.ps1, t.ps1) that enumerate systems, compress and exfiltrate documents and credentials via FTP, Pixeldrain and Google Drive.
MITRE Techniques
- [T1574.002 ] DLL Side-Loading – CoolClient modules used DLL sideloading to execute malicious DLLs via legitimate signed executables. (‘These modules relied on DLL sideloading as their primary execution method, which required a legitimate signed executable to load a malicious DLL.’)
- [T1055 ] Process Injection – CoolClient decrypts and injects staged payloads into a spawned process (write.exe) to run the final-stage DLL in memory. (‘Decrypts and injects loader.dat into a newly created write.exe process.’)
- [T1218 ] Signed Binary Proxy Execution – The actor abused signed binaries from BitDefender, VLC, Ulead PhotoImpact and Sangfor to load malicious DLLs. (‘the threat actor abused signed binaries from various software products, including BitDefender, VLC Media Player, Ulead PhotoImpact, and several Sangfor solutions.’)
- [T1056.001 ] Input Capture: Keylogging – CoolClient implements a keylogger thread to capture keystrokes for exfiltration. (‘it first checks whether the keylogger…are enabled. If they are, CoolClient creates a new thread for each specific functionality.’)
- [T1115 ] Clipboard Data – New CoolClient functionality captures clipboard contents and active window titles using GetClipboardData and GetWindowTextW. (‘CoolClient creates a new thread…leverages functions…GetClipboardData and GetWindowTextW, to capture clipboard information.’)
- [T1040 ] Network Sniffing – CoolClient intercepts and parses raw network traffic on local IPs to extract HTTP proxy credentials. (‘the malware creates dedicated threads to intercept and parse raw network traffic on each local IP address…extracting proxy authentication credentials from HTTP traffic intercepted by the malware’s packet sniffer.’)
- [T1555.003 ] Credentials from Web Browsers – Browser stealers and scripts extract Login Data and Local State to decrypt and harvest saved browser credentials. (‘extract saved login credentials from the Chrome browser’ and ‘SELECT origin_url, username_value, password_value FROM logins’)
- [T1053.005 ] Scheduled Task/Job – CoolClient creates a scheduled task (ComboxResetTask) to persist and run with elevated parameters. (‘Creates a scheduled task named ComboxResetTask for persistence.’)
- [T1050 ] New Service – CoolClient installs and starts a service (media_updaten) as a persistence mechanism. (‘Installs a service named media_updaten and starts it.’)
- [T1547.001 ] Registry Run Keys / Startup Folder – CoolClient adds a Run key to achieve persistence on host startup. (‘Adds new key to the Run registry for persistence mechanism.’)
- [T1105 ] Ingress Tool Transfer – Scripts and operators download tools such as curl.exe and rar.exe onto victim hosts to support collection and exfiltration. (‘The script starts by downloading curl.exe and rar.exe into the public folder.’)
- [T1567 ] Exfiltration to Cloud Storage and Public Services – HoneyMyte exfiltrated archives and browser data to Pixeldrain, Google Drive and other online services. (‘compresses the collected data into a password-protected RAR archive and uploads it to pixeldrain.com using the service’s API’ and Google Drive upload curl example)
Indicators of Compromise
- [File hashes ] CoolClient, plugins and scripts – examples: 1A5A9C013CE1B65ABC75D809A25D36A7 (browser stealer Variant A), 7AA53BA3E3F8B0453FFCFBA06347AB34 (ServiceMgrS.dll), and 10 more hashes
- [File names ] Drop and payload filenames observed – examples: Sang.exe (legitimate Sangfor binary abused for DLL sideloading), libngs.dll, loader.dat, main.dat, time.dat, write.exe, getloginedge.exe, cookies.sqlite
- [Domains ] CoolClient C2 and infrastructure – examples: account.hamsterxnxx[.]com, popnike-share[.]com, japan.Lenovoappstore[.]com
- [IP addresses ] Exfiltration and download hosts – examples: 113.23.212[.]15 (FTP exfiltration server), 45.144.165[.]65 (file download host used to fetch getloginedge.exe)
Read more: https://securelist.com/honeymyte-updates-coolclient-uses-browser-stealers-and-scripts/118664/