CERT-AGID has identified a phishing campaign that exploits compromised email accounts from Public Administrations to send PDFs and links leading to a malicious Figma-hosted resource which then redirects victims to a fake Microsoft 365 login page to steal credentials. The campaign emphasizes brand spoofing to increase credibility and CERT-AGID has notified affected administrations and distributed indicators of compromise. #CERT-AGID #Microsoft365
Keypoints
- Compromised institutional email accounts belonging to Public Administrations were abused to send phishing messages to other PA recipients, using hidden BCC to conceal real targets.
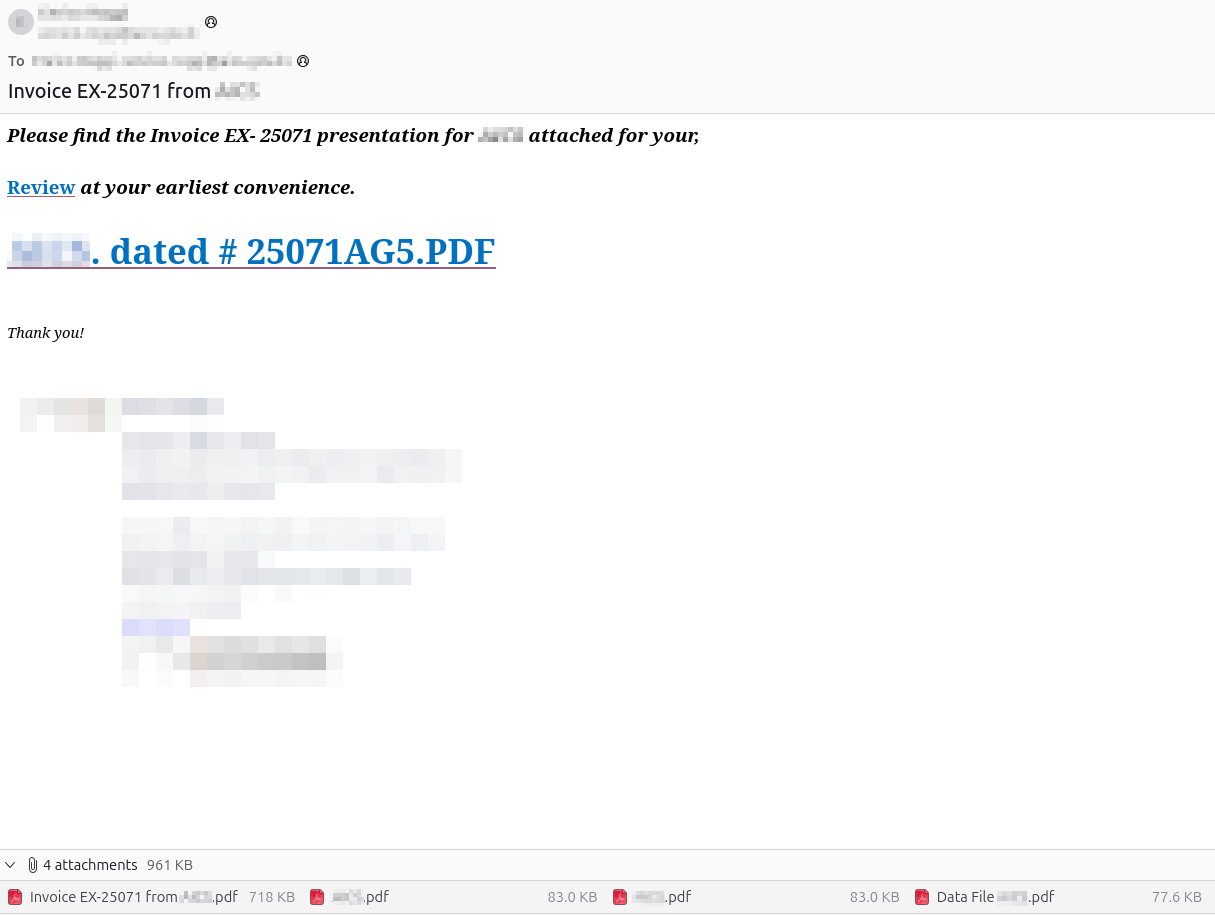
- Phishing emails include multiple PDF attachments that impersonate administrative documents (invoices, presentations) and contain the same malicious link as the email body.
- Links lead to a malicious resource hosted on the legitimate cloud platform Figma, customized with the target administration’s name and logo to increase trust (brand spoofing).
- The Figma resource redirects users to a fake Microsoft 365 login page designed to harvest institutional credentials.
- This variant increases risk by combining legitimate-host platform use and visual spoofing, raising the likelihood of successful credential theft and subsequent account reuse for further fraud or compromise.
- CERT-AGID informed affected administrations and distributed IoCs to accredited Public Administrations; detailed indicators are available via the referenced “Download IoC” link.
MITRE Techniques
- [T1566.002 ] Phishing: Spearphishing Link – Attackers sent emails and embedded links that redirect victims to malicious resources (‘The communication invites the user to click on the link in the body of the email and contains several PDF attachments’).
- [T1566.001 ] Phishing: Spearphishing Attachment – PDF attachments were used to deliver the lure and include the same malicious link (‘several PDF attachments that simulate administrative documents related to invoices or presentations’).
- [T1204.002 ] User Execution: Malicious Link – Users are induced to click links that redirect from the Figma resource to a counterfeit login page (‘From that resource, via a new link, the user is redirected to a forged login page aimed at stealing Microsoft 365 credentials’).
- [T1078 ] Valid Accounts – Attackers abused compromised institutional email accounts to send phishing messages within the Public Administration perimeter (‘compromised email accounts belonging to Public Administrations were used to convey messages to recipients within the PA perimeter’).
- [T1036 ] Masquerading – Brand spoofing was used to build a visual context consistent with the targeted administration’s identity to increase credibility (‘construction of a visual context consistent with the entity’s identity (brand spoofing) increasing the probability that the user completes authentication’).
Indicators of Compromise
- [URLs/Links ] Figma-hosted lure and phishing login pages – example patterns: https://www.figma.com/file/ (malicious resource), https:///microsoft-login (fake Microsoft 365 login).
- [File names ] PDF attachments impersonating administrative documents – examples: Invoice_*.pdf, Presentation_*.pdf (attachments contained the malicious link and mimicked invoices or presentations).
- [Email addresses ] Compromised sender accounts within Public Administrations – examples (generic patterns): [email protected] (abused sender), [email protected] (compromised institutional mailbox).
- [Other ] Full IoC set not listed in article text; CERT-AGID published a “Download IoC” resource with detailed indicators for accredited PA entities.