Episode 4 of the Charming Kitten / APT35 leaks exposes not sophisticated zero-day exploits but the bureaucratic infrastructure—spreadsheets, invoices, crypto receipts, hosting accounts, and one-time ProtonMail identities—that fund, procure, and maintain Iranian cyber operations. The documents tie APT35’s procurement and payment chains to Moses Staff’s leak domains and operational tooling, showing micro-crypto payments via Cryptomus, recurring European VPS providers (EDIS, Impreza), and repeatable, auditable workflows that convert state intent into persistent infrastructure. #APT35 #MosesStaff
Keypoints
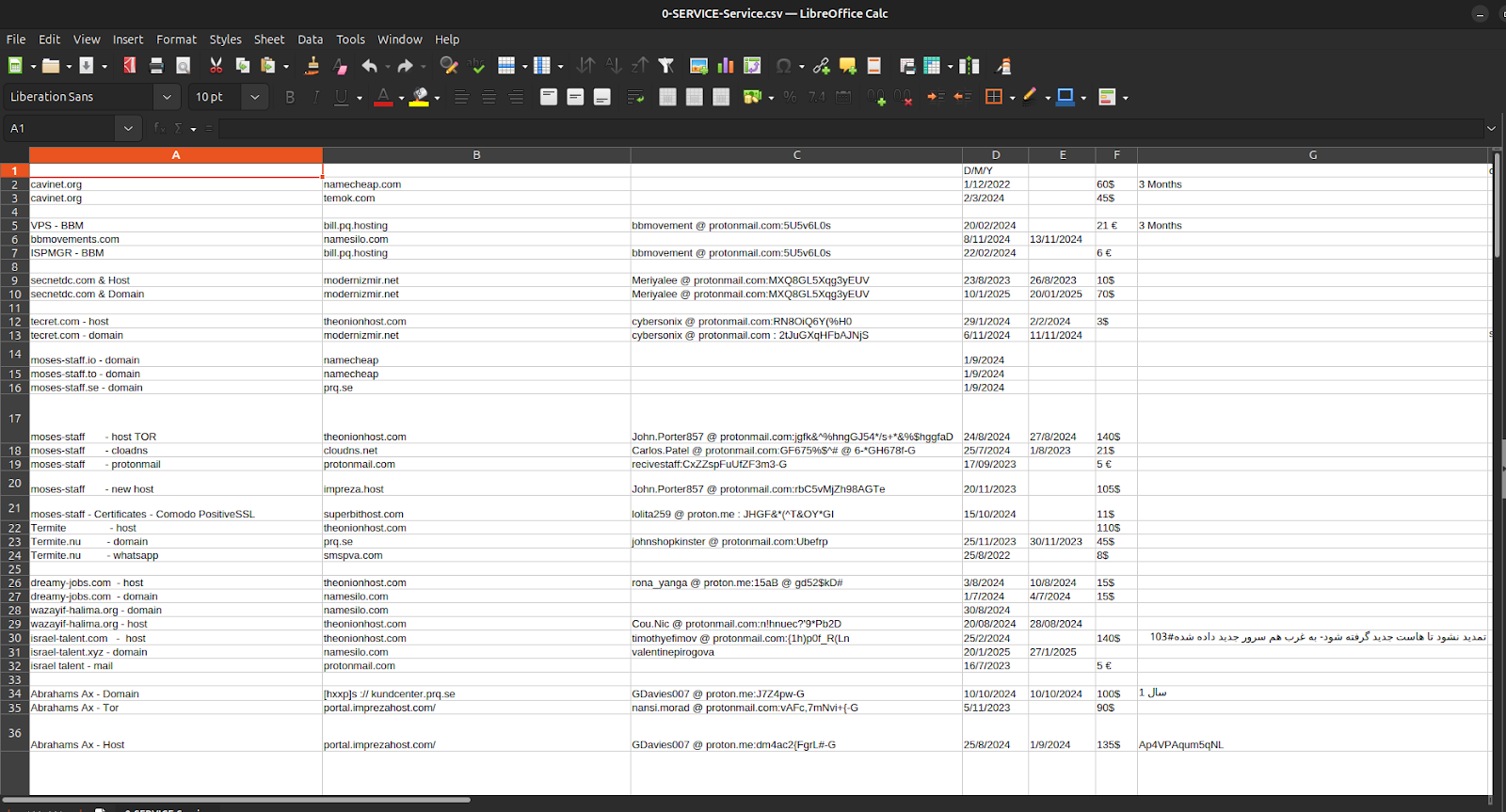
- Episode 4 leaks reveal operational ledgers (service, payment, network CSVs) that document domain registrations, VPS rentals, ProtonMail identities, and cleartext credentials used by APT35.
- Financial records show dozens of micro-crypto payments (≈€12–€18 each) routed through Cryptomus and tied to ticket numbers, forming a closed procurement-payment-activation loop.
- The same administrative system links Charming Kitten (APT35) infrastructure to Moses Staff domains (e.g., moses-staff.io), collapsing the distinction between espionage and hacktivist theatre.
- Operators use disposable aliases and one-time ProtonMail inboxes to acquire domains and VPS instances from repeat providers (EDIS, Impreza), then log credentials and renewals in shared spreadsheets.
- Network sheet entries list routable IP allocations and /29–/30 blocks that correspond to live servers and provider dashboards, exposing operational infrastructure and OPSEC lapses.
- The leak reframes Iranian cyber capability as institutional and bureaucratic—sustained by procurement, accounting, and micro-payments—rather than purely technical innovation.
MITRE Techniques
- [T1595 ] Active Scanning – Operators stage VPS nodes to probe target systems and deliver phishing infrastructure. [‘Operators stage VPS nodes to probe target systems and deliver phishing infrastructure.’]
- [T1598 ] Phishing for Information – Domains such as dreamy-jobs.com, israel-talent.com, and wazayif-halima.org are designed to lure specific industries for credential harvesting. [‘Domains such as dreamy-jobs.com, israel-talent.com, and wazayif-halima.org are designed to lure specific industries for credential harvesting.’]
- [T1566 ] Phishing – Job-themed, credential-harvest pages deployed on low-cost VPS nodes purchased through EDIS and Impreza Host. [‘Job-themed, credential-harvest pages deployed on low-cost VPS nodes purchased through EDIS and Impreza Host.’]
- [T1078 ] Valid Accounts – Harvested credentials fed into further access attempts, often timed shortly after domain activation. [‘Harvested credentials fed into further access attempts, often timed shortly after domain activation.’]
- [T1204 ] User Execution – Operators deploy phishing pages requiring victim interaction (login forms, document lures). [‘Operators deploy phishing pages requiring victim interaction (login forms, document lures).’]
- [T1098 ] Account Manipulation – Use of harvested credentials to maintain foothold where applicable. [‘Use of harvested credentials to maintain foothold where applicable.’]
- [T1136 ] Create Account – Single-purpose ProtonMail inboxes created for procurement (operational persistence at the infrastructure layer). [‘Single-purpose ProtonMail inboxes created for procurement (operational persistence at the infrastructure layer).’]
- [T1068 ] Exploitation for Privilege Escalation – Referenced as implied in broader Charming Kitten history against Exchange and Ivanti appliances. [‘(Not a focus of the dump, but implied in reference to Charming Kitten’s broader history of targeting Microsoft Exchange and Ivanti appliances.)’]
- [T1036 ] Masquerading – Use of aliases that imitate Israeli, Russian, European, and American names; job-themed domains; fake recruitment brands. [‘Use of aliases that imitate Israeli, Russian, European, and American names; job-themed domains; fake recruitment brands.’]
- [T1070.004 ] File Deletion – Use of single-use ProtonMail identities deleted or abandoned immediately after procurement. [‘Use of single-use ProtonMail identities deleted or abandoned immediately after procurement.’]
- [T1112 ] Modify Registry – Cited as historically used in Moses Staff post-exploitation phases (not directly in dump). [‘(Not directly in the dump, but historically used in Moses Staff post-exploitation phases.)’]
- [T1027 ] Obfuscated/Encrypted Files – TOR mirrors, private WHOIS, and encrypted communication channels used to reduce visibility. [‘TOR mirrors, private WHOIS, and encrypted communication channels.’]
- [T1564.003 ] Hidden Artifacts: Disposable Email Identities – Strict one-time usage of procurement emails to prevent cross-cluster linkage. [‘Strict one-time usage of procurement emails to prevent cross-cluster linkage.’]
- [T1056 ] Input Capture – Credential-harvesting login portals deployed on purchased domains. [‘Credential-harvesting login portals deployed on purchased domains.’]
- [T1110 ] Brute Force – Occasional activity against Israeli organizations documented in public reporting of Moses Staff operations. [‘Occasional activity against Israeli organizations (documented in public reporting of Moses Staff operations).’]
- [T1087 ] Account Discovery – Infrastructure scans for valid credentials through job-themed lures. [‘Infrastructure scans for valid credentials through job-themed lures.’]
- [T1046 ] Network Service Scanning – EDIS-hosted servers used to probe Israeli networks prior to planned intrusions. [‘EDIS-hosted servers used to probe Israeli networks prior to planned intrusions.’]
- [T1021 ] Remote Services – Use of harvested valid accounts through VPN portals and cloud dashboards. [‘Use of harvested valid accounts through VPN portals and cloud dashboards.’]
- [T1530 ] Data from Cloud Storage – Compromises of cloud/email providers in the civilian tier. [‘Compromises of cloud/email providers in the civilian tier.’]
- [T1114 ] Email Collection – Phished credentials provide mailbox access enabling data theft. [‘Phished credentials provide mailbox access enabling data theft.’]
- [T1071 ] Application Layer Protocol – C2 nodes hosted on low-tier VPS servers via HTTP(S). [‘C2 nodes hosted on low-tier VPS servers via HTTP(S).’]
- [T1105 ] Ingress Tool Transfer – Payloads staged on purchased domains and KVM BASIC VPS instances. [‘Payloads staged on purchased domains and KVM BASIC VPS instances.’]
- [T1568.002 ] Dynamic DNS – Operators rotate hosts rapidly; CloudDNS references seen around Moses Staff mirrors. [‘Operators rotate hosts rapidly; CloudDNS references seen around Moses Staff mirrors.’]
- [T1048 ] Exfiltration Over Alternative Protocol – TOR mirrors used for anonymity during leaks. [‘TOR mirrors used for anonymity during leaks.’]
- [T1567.002 ] Exfiltration to Web Services – Leak sites operated under moses-staff.io, .se, .to. [‘Leak sites operated under moses-staff.io, .se, .to.’]
- [T1491 ] Defacement / Psychological Operations – Public leak sites intended to intimidate Israeli institutions. [‘Public leak sites intended to intimidate Israeli institutions.’]
- [T1485 ] Data Destruction – Moses Staff’s destructive toolchain and historical destructive intrusions. [‘Moses Staff’s destructive toolchain, already known in historical operations.’]
- [T1585.001 ] Establish Accounts: Email Accounts – Single-use ProtonMail addresses for procurement. [‘Single-use ProtonMail addresses for procurement.’]
- [T1583.003 ] Domain Registration Clusters – Clusters of domains purchased for credential harvesting and campaign staging. [‘Clusters of domains purchased for credential harvesting and campaign staging.’]
- [T1583.001 ] Acquire Infrastructure: Virtual Private Servers – Routine procurement from EDIS, Impreza Host, Bulgarian VPS sellers. [‘Routine procurement from EDIS, Impreza Host, Bulgarian VPS sellers.’]
- [T1586.002 ] Compromise Accounts: Webmail – Credential theft from phishing operations targeting webmail. [‘Credential theft from phishing operations.’]
- [T1586 ] Obfuscation via Payment Providers – Cryptomus used to anonymize infrastructure transactions. [‘Cryptomus used to anonymize infrastructure transactions.’]
- [T1587 ] Develop Capabilities – Infrastructure provisioning using micro-crypto payments in a repeatable pattern. [‘Infrastructure provisioning using micro-crypto payments in a repeatable pattern.’]
- [T1599 ] Network Boundary Bridging – By paying through crypto and using global VPS hosting, operators evade regional filtering. [‘By paying through crypto and using global VPS hosting, operators evade regional filtering.’]
Indicators of Compromise
- [Domains ] leak/phishing and propaganda infrastructure – moses-staff.io, bbmovements.com, and other domains such as israel-talent.com (and several others listed in the dump).
- [Hosting Providers ] recurring infrastructure suppliers used for VPS and domains – EDIS Global (Cyprus), Impreza (and NameSilo/Namecheap referenced for domains).
- [IP Addresses / Networks ] routable hosts and /29–/30 allocations used as VPS/C2 – 185.103.130.16/30, 185.212.193.240/29 (and other allocations like 109.230.93.128/29 referenced in the network sheet).
- [Email Addresses ] ProtonMail procurement and operator personas – [email protected], [email protected] (and dozens of other one-time ProtonMail addresses in the ledger).
- [Aliases / Cover Names ] one-time identities used to purchase services – Maja Bosman, Levis Cross (names used as billing/WHOIS personas in provider records).
- [Bitcoin Wallets ] payment/collection addresses tied to micro-payments and consolidations – 1K93styPFkDGsTYNjgqaDN6xWy5NmUDLhh (collection wallet), other addresses beginning with 3F2K… (and many additional wallet fragments in the ledger).
- [IP Clusters ] infrastructure clusters and hosting footprints – 128.199.237.132 (DigitalOcean), 212.175.168.58 (Türk Telekom) and other provider-associated IPs used in campaigns.