Socket’s Threat Research Team discovered a malicious PyPI package named sympy-dev that impersonates the legitimate SymPy library and embeds a downloader and in-memory loader to fetch and execute ELF payloads. The loader retrieved XMRig cryptominer binaries from threat actor-controlled hosts, the package surpassed 1,000 downloads on day one, and the malicious releases remain live on PyPI pending removal. #sympy-dev #XMRig
Keypoints
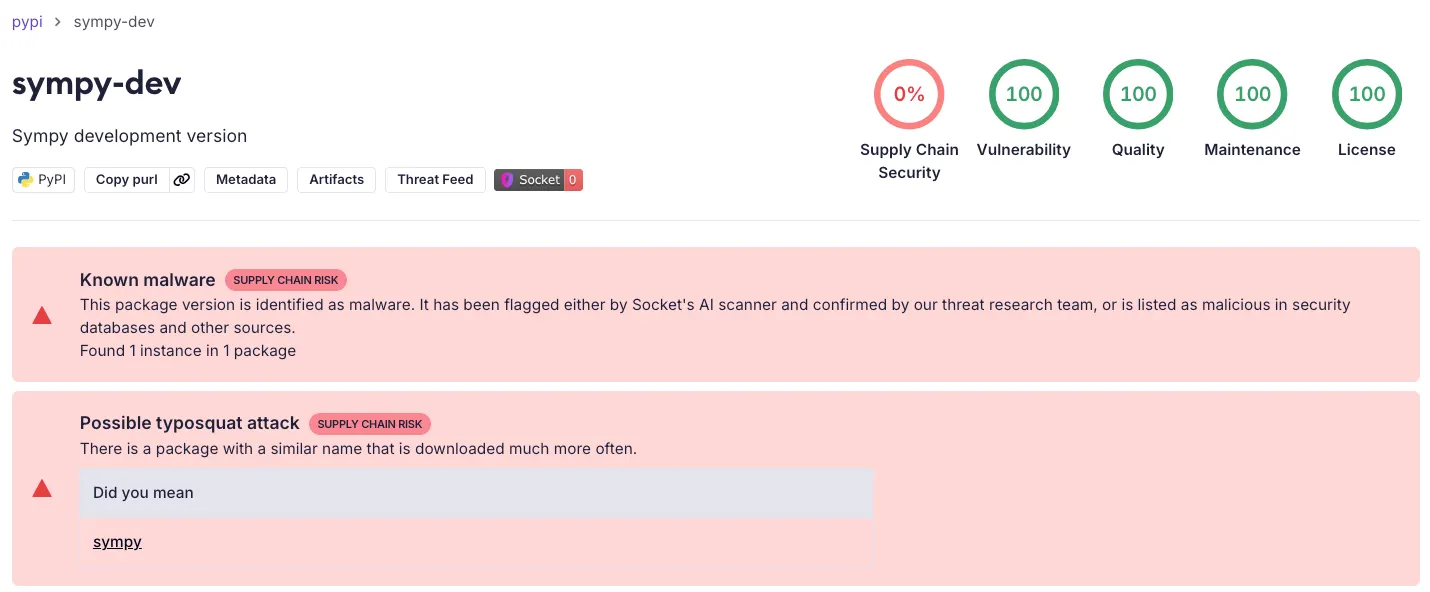
- Socket identified a typosquatted PyPI package, sympy-dev, that copied SymPy’s project description and branding to increase accidental installs.
- Four malicious releases (1.2.3–1.2.6) were published on January 17, 2026, and the package exceeded 1,000 downloads within its first day on PyPI.
- The malicious code injects a downloader and in-memory execution routine into SymPy polynomial code paths (groebner() and roots_cubic()) that trigger during normal SymPy usage.
- The loader fetches a remote JSON config and downloads ELF payloads from attacker-controlled hosts, then executes them from memory using memfd_create and /proc/self/fd to minimize on-disk artifacts.
- Recovered second-stage binaries are UPX-packed XMRig cryptominers that connect to Stratum-over-TLS endpoints on the same C2 IPs; two SHA-256 hashes were observed for these payloads.
- Socket petitioned PyPI to remove the package and suspend the publisher, and recommends dependency pinning, integrity checks, vetted indexes, and monitoring for unexpected outbound requests and in-memory execution.
MITRE Techniques
- [T1195.002 ] Supply Chain Compromise: Compromise Software Supply Chain – A typosquatted package was published on PyPI to deliver malicious code as a dependency (‘malicious PyPI package, sympy-dev, that impersonates SymPy’)
- [T1608.001 ] Stage Capabilities: Upload Malware – The attacker uploaded staged releases to PyPI containing backdoored code that retrieves and executes additional payloads (‘four releases, versions 1.2.3 through 1.2.6, all containing malicious code’)
- [T1204.005 ] User Execution: Malicious Library – The campaign relies on developers installing a malicious library with a trusted name to trigger execution (‘typosquat of the legitimate sympy library’)
- [T1059.006 ] Command and Scripting Interpreter: Python – The malicious logic is implemented in Python and injected into SymPy code paths to perform network retrieval and in-memory execution (‘the threat actor injected a downloader and in-memory execution routine into SymPy polynomial code paths’)
- [T1036 ] Masquerading – The package reuses SymPy’s project description and branding cues to appear legitimate and increase accidental installs (‘copied SymPy’s project description and branding cues into the sympy-dev listing’)
- [T1656 ] Impersonation – The attacker impersonated the SymPy project to exploit users’ trust in the legitimate package name (‘a malicious PyPI package, sympy-dev, that impersonates SymPy’)
- [T1105 ] Ingress Tool Transfer – The loader downloads ELF payloads from remote C2 hosts to the victim environment (‘The loader retrieves its configuration and payload from 63[.]250[.]56[.]54 and 185[.]167[.]99[.]46 command and control (C2) endpoints’)
- [T1071.001 ] Application Layer Protocol: Web Protocols – The loader uses HTTP(S) to fetch configuration and payloads from attacker-controlled endpoints (‘the downloader retrieves a remote JSON configuration, download a threat actor-controlled ELF payload’)
- [T1095 ] Non-Application Layer Protocol – The miner connects to Stratum endpoints over TLS for mining traffic (‘mining to Stratum endpoints over TLS’)
- [T1027.002 ] Obfuscated Files or Information: Software Packing – The recovered second-stage binaries were UPX-packed to hinder analysis (‘both samples are UPX-packed’)
- [T1496.001 ] Resource Hijacking: Compute Hijacking – The payloads are XMRig cryptominers that hijack CPU resources for mining (‘the downloaded payloads are XMRig cryptominers, and the configuration directs mining to Stratum endpoints over TLS’)
Indicators of Compromise
- [Package Name ] Malicious PyPI package – sympy-dev (typosquat of the legitimate sympy package)
- [Publisher Alias ] PyPI maintainer name – Nanit (listed as the package maintainer)
- [IP Addresses ] C2 and Stratum endpoints – 63.250.56.54, 185.167.99.46
- [URLs / Endpoints ] Configuration and payload URLs – http://63.250.56.54/config, http://185.167.99.46/config
- [Ports/Services ] Mining endpoints – 63.250.56.54:3333, 185.167.99.46:3333 (Stratum over TLS)
- [File Names ] Loader-written files and payloads – config.json, payload.bin / payload
- [SHA-256 Hashes ] Observed malicious ELF payloads – 90f9f8842ad1b824384d768a75b548eae57b91b701d830280f6ed3c3ffe3535e, f454a070603cc9822c8c814a8da0f63572b7c9329c2d1339155519fb1885cd59
Read more: https://socket.dev/blog/pypi-package-impersonates-sympy-to-deliver-cryptomining-malware