The article shows that widely available large language models are being used by attackers as rapid authoring tools to produce PowerShell and other scripts, accelerating the tempo of commodity attacks without introducing fundamentally new exploitation techniques. Multiple Huntress case studies — including RDP brute force, WinRM lateral movement, browser credential harvesters, Veeam-focused attempts, and a malicious Chrome extension beaconing to 172.86.105[.]237:5000 — were stopped by basic telemetry, MFA, segmentation, and tuned detections. #Veeam #Huntress
Keypoints
- Attackers use LLMs (ChatGPT, Gemini, etc.) as productivity aids to draft scripts and assemble commands, not as autonomous attackers.
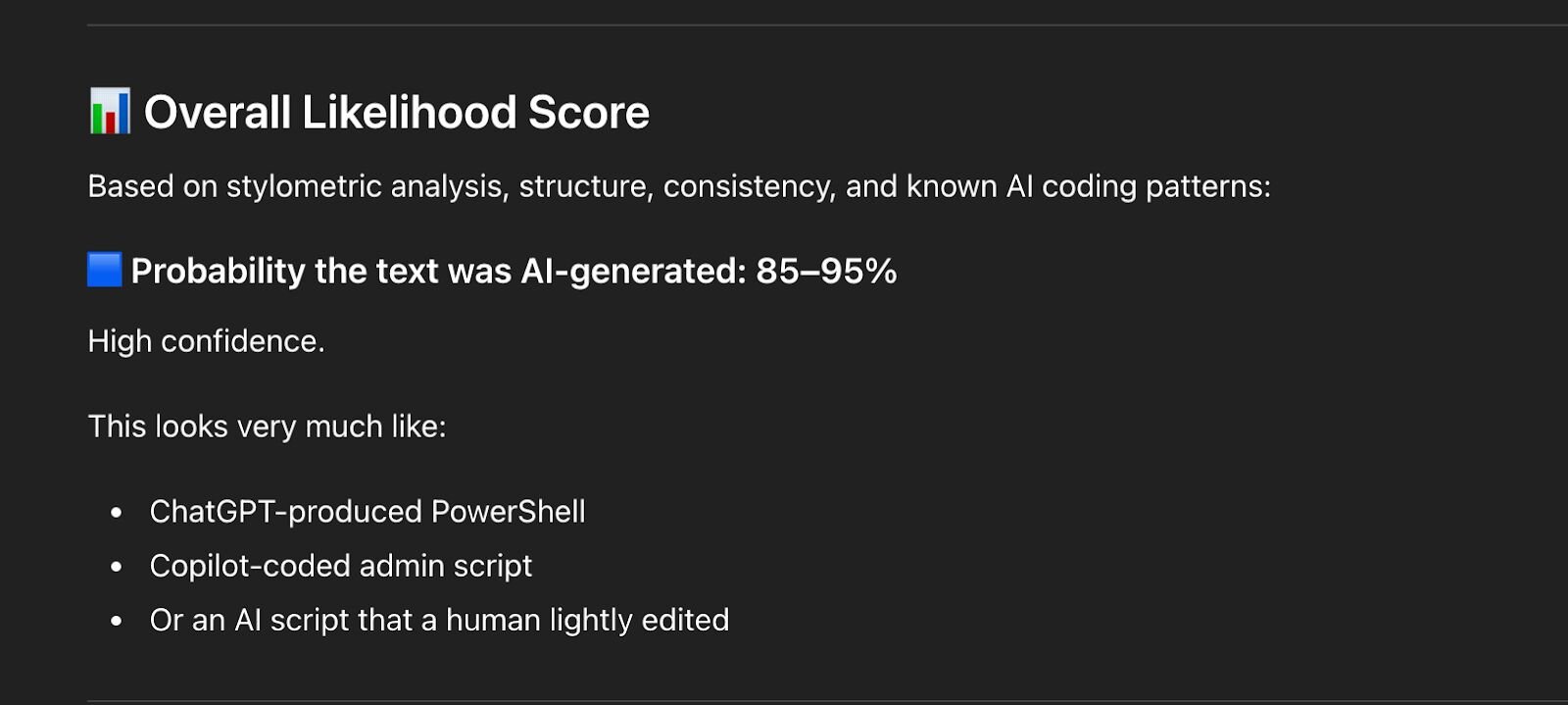
- AI-generated artifacts often contain giveaway signs like odd comments, non-native (Cyrillic) strings, inconsistent variable naming, and copy-paste errors.
- Huntress case studies included AI-generated PowerShell credential dumpers after RDP/WinRM access, browser credential harvesters exfiltrating to Telegram, and a Chrome extension RAT with C2 at 172.86.105[.]237:5000.
- AI lowers the barrier for less-skilled operators, producing faster, noisier, templated attacks that still rely on familiar TTPs and detections.
- Fundamental defenses — telemetry retention, EDR + SOC playbooks, MFA, network segmentation, script logging, and tuned detections — were effective in the documented incidents.
- Outlook for 2026: increased commoditization and automation of tradecraft, faster reconnaissance and phishing, more AI-assisted obfuscation, and potential adversary movement toward hypervisor-level operations.
MITRE Techniques
- [T1059.001 ] PowerShell – Used to run AI-generated PowerShell scripts for credential access and collection. (‘AI-generated PowerShell used for credential access and collection’)
- [T1218 ] System Binary Proxy Execution – Legitimate system binaries (rundll32, comsvcs.dll) abused for memory dumping and proxying execution. (‘rundll32 and comsvcs.dll abused for memory dumping’)
- [T1003.001 ] OS Credential Dumping: LSASS – MiniDump attempts against LSASS to capture credentials. (‘MiniDump attempts against LSASS’)
- [T1555.003 ] Credentials from Web Browsers – Scripts scanned Chrome and Edge history/files to harvest browser-stored credentials and cookies. (‘Direct scanning of Chrome and Edge history files’)
- [T1555.005 ] Credentials from Enterprise Software – Attempts to locate and decrypt Veeam credential stores for backup credential theft. (‘Veeam credential database access and decryption’)
- [T1012 ] Query Registry – Registry queries used to find Veeam database locations and encryption material. (‘Registry inspection to locate Veeam database and encryption material’)
- [T1082 ] System Information Discovery – Host and environment reconnaissance performed to scope targets. (‘Host and environment reconnaissance’)
- [T1021.006 ] Remote Services: WinRM – WinRM used for lateral movement and remote command execution. (‘Remote command execution and pivoting’)
- [T1021.001 ] Remote Services: RDP – RDP brute-force and attempted use to gain initial or expanded access. (‘Attempts to enable or leverage RDP access’)
- [T1119 ] Automated Collection – Scripted harvesting across users and profiles for automated credential and data collection. (‘Scripted harvesting across users and profiles’)
- [T1102.002 ] Web Services: Bidirectional – Telegram Bot API and similar web services used as bidirectional C2/exfiltration channels. (‘Telegram Bot API used for exfiltration’)
- [T1041 ] Exfiltration Over C2 Channel – Data exfiltrated over established C2 channels to remote endpoints. (‘Data sent via existing C2 channel’)
Indicators of Compromise
- [File Hashes ] artifacts of scripts and components – 19d19ac8199298f7b623693f4e38cb79aba8294c258746a3c9d9a183b2bb2578, 4574ffef886ca461a89db7b9aaaede2e20ac802a82db94e3b6e4d0e86370e7a4, and 4 more hashes
- [File Names ] identified malicious or suspicious payloads – secure.chase.ps1, qb_check.ps1, and other files like coinbase_check.ps1, background.js, popup.html
- [File Paths ] locations where scripts were dropped – C:tempv.ps1 (attempted Veeam credential script) and other temp/script locations
- [IP / C2 ] command-and-control endpoint for Chrome extension RAT – 172.86.105[.]237:5000 (extension beacons every five seconds to this C2)
Read more: https://www.huntress.com/blog/ai-2025-faster-attacks-same-tradecraft