Silent Push analysts uncovered a long-running Magecart web-skimming campaign active since at least January 2022 that uses highly obfuscated JavaScript to inject fake payment forms on compromised e-commerce sites and target major payment networks including American Express, Diners Club, Discover, JCB, Mastercard, and UnionPay. Key indicators include domains such as cdn-cookie[.]com and lasorie[.]com, injected files like 1-197056a9.js, and exfiltration to hxxps[:]//lasorie[.]com/api/add; the report recommends CSP, PCI DSS compliance, timely patching, strong access controls, and user vigilance to mitigate risk. #Magecart #cdn-cookie.com
Keypoints
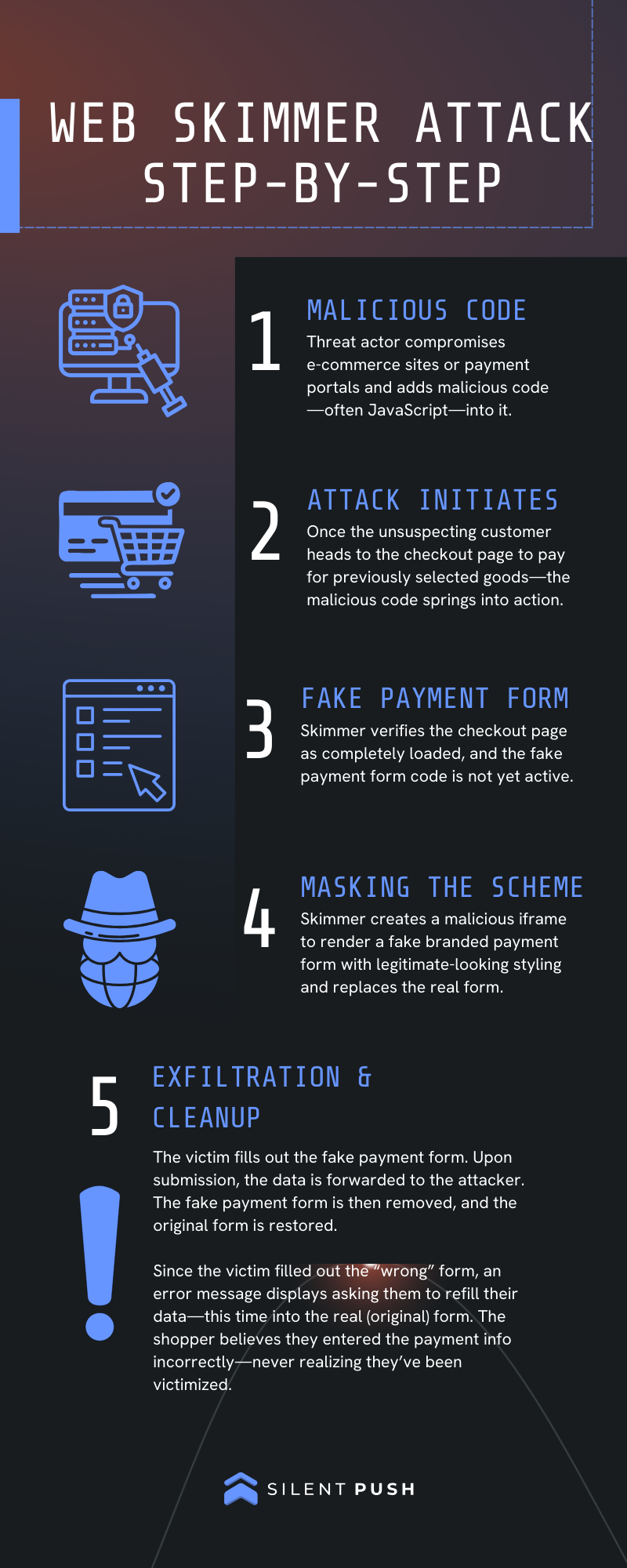
- Silent Push discovered a multi-year web-skimming (Magecart) campaign active since at least January 2022 that targets online checkout processes on compromised e-commerce sites.
- The skimmer uses highly obfuscated JavaScript loaded from attacker-controlled domains (seed domain cdn-cookie[.]com) and additional related infrastructure (e.g., lasorie[.]com).
- Attack logic detects admin users (wpadminbar) and WooCommerce/Stripe checkout elements, hides the legitimate Stripe form, injects a fake payment iframe, and harvests full checkout data (card + personal details).
- Collected data is XOR-encrypted with key “777”, Base64-encoded, and exfiltrated via HTTP POST to an API endpoint (hxxps[:]//lasorie[.]com/api/add), after which the skimmer cleans up and sets wc_cart_hash to prevent re-execution.
- The campaign explicitly recognizes and adapts to multiple card brands (Mastercard, American Express, JCB, Diners Club, Discover, UnionPay) to improve form legitimacy and success rates.
- Indicators observed include obfuscated files (e.g., 1-197056a9.js, recorder.js), attacker-controlled domains, and hosting on an ASN (209847) linked to a bulletproof hosting provider; mitigations recommended include CSP, PCI DSS adherence, patching, MFA for admin accounts, and user/merchant vigilance.
MITRE Techniques
Indicators of Compromise
- [Domain ] attacker infrastructure and injector hosts – cdn-cookie[.]com, lasorie[.]com
- [Compromised Website ] observed active infections and resource loading – colunexshop[.]com and several other webshops (multiple vendor sites loading cdn-cookie[.]com resources)
- [File Name / Resource ] injected and loaded JavaScript files used by the skimmer – 1-197056a9.js, recorder.js (also observed: cplnfwtlrkb.js, tab-gtm.js)
- [URL / API Endpoint ] exfiltration endpoint and injected resource URLs – hxxps[:]//cdn-cookie[.]com/1-197056a9.js, hxxps[:]//lasorie[.]com/api/add
- [Hosting / ASN ] infrastructure attribution and bulletproof hosting – ASN 209847 (recently associated with PQ.Hosting / Stark Industries / THE.Hosting / WorkTitans B.V.)
- [Local Storage Key ] persistence / re-execution prevention indicator used by the skimmer on victim browsers – wc_cart_hash (set to “true” after successful exfiltration)
Read more: https://www.silentpush.com/blog/magecart/?utm_source=rss&utm_medium=rss&utm_campaign=magecart