CloudSEK TRIAD uncovered a MuddyWater spearphishing campaign that used icon‑spoofed Word documents to deploy a Rust-based implant (referred to as RustyWater) against diplomatic, maritime, financial, and telecom targets in the Middle East. The implant is delivered via VBA macros that drop a hex‑encoded PE (reddit.exe / CertificationKit.ini) and provides asynchronous HTTP C2, registry persistence, anti-analysis, process injection, and modular post-compromise capability. #MuddyWater #RustyWater
Keypoints
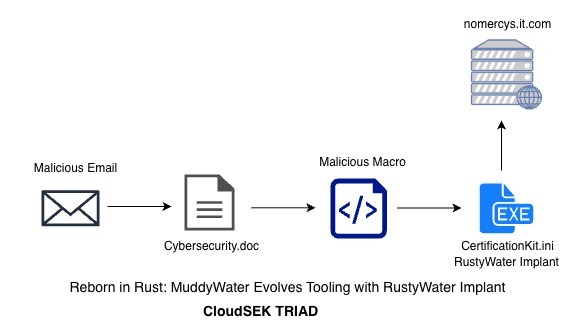
- Initial access via spearphishing email titled “Cybersecurity Guidelines” sent from info@tmcell with an attached Cybersecurity.doc lure targeting Middle East diplomatic, maritime, financial, and telecom organizations.
- VBA macros (WriteHexToFile and love_me_function) extract a hex‑encoded payload from a UserForm control and write it to C:ProgramDataCertificationKit.ini, which is a Rust‑compiled PE masquerading as reddit.exe.
- The Rust implant (RustyWater / Archer RAT / RUSTRIC) implements async C2 using reqwest and tokio, encodes telemetry as JSON→Base64→XOR, and uses randomized sleep/jitter and retry/failover to evade network detection.
- Anti-analysis and persistence mechanisms include Vectored Exception Handler (VEH), position‑independent XOR string encryption, scanning for 25+ AV/EDR artifacts, and registry Run key autostart pointing to CertificationKit.ini.
- Post‑compromise techniques include process injection into explorer.exe via VirtualAllocEx/WriteProcessMemory and runtime modular capability expansion for on‑demand collection and credential theft.
- Attribution to MuddyWater is assessed with high confidence based on VBA code reuse, targeting patterns, tactical overlaps with prior chains, and corroborating technical artifacts; multiple IOCs (10 SHA256s, several IPs) were provided.
MITRE Techniques
- [T1566.001 ] Phishing: Spearphishing Attachment – Used to deliver the malicious Word document attachment that initiated the chain (‘The email titled “Cybersecurity Guidelines” was sent from the email domain “info@tmcell” which looks to be an official contact email for TMCell (Altyn Asyr CJSC).’ )
- [T1204.002 ] User Execution: Malicious File – Victim enables macros/opens the document leading to payload drop and execution (‘User opens Doc leading to payload drop and execution’)
- [T1059.005 ] Command and Scripting Interpreter – VBA macros in the Word document reconstruct and execute commands to write and run the embedded payload (‘WriteHexToFile reads a hex-encoded byte stream embedded in UserForm1.TextBox1.Text… writes the reconstructed payload to disk as CertificationKit.ini’)
- [T1547.001 ] Boot or Logon Autostart Execution: Registry Run Keys/Startup Folder – The malware establishes persistence by writing itself to a Windows startup Run registry key (‘The value points to a file at C:ProgramDataCertificationKit.ini’)
- [T1106 ] Native API – The binary invokes native Windows APIs for system enumeration, registry operations, and timers (e.g., RegOpenKeyExW, GetUserNameW, CreateWaitableTimerExW) (‘Use of RegOpenKeyExW, GetUserNameW, GetComputerNameExW, CreateWaitableTimerExW’)
- [T1047 ] Windows Management Instrumentation – WMI used to execute dropped payload via Win32_Process.Create (‘WMI used to execute CertificationKit.ini via Win32_Process.Create’)
- [T1620 ] Reflective Code Loading – Hex‑encoded PE is decoded and loaded from memory/dropped by the macro prior to execution (‘Hex coded PE payload decode in memory and dropped’)
- [T1055 ] Process Injection – Shellcode/payload is injected into explorer.exe using VirtualAllocEx/WriteProcessMemory and thread context manipulation (‘The binary is launched in suspended state… allocates executable memory inside the remote process via VirtualAllocEx and writes the payload via WriteProcessMemory.’)
Indicators of Compromise
- [SHA256 Hash ] Malware sample hashes observed – 76aad2a7fa265778520398411324522c57bfd7d2ff30a5cfe6460960491bc552, f38a56b8dc0e8a581999621eef65ef497f0ac0d35e953bd94335926f00e9464f, and 8 more hashes
- [IP ] Infrastructure / C2 endpoints – 159.198.68.25, 161.35.228.250, and 1 more IP
- [Email / Domain ] Spearphishing sender – info@tmcell (impersonating TMCell / Altyn Asyr CJSC)
- [File names / Paths ] Lures and dropped artifacts – Cybersecurity.doc, C:ProgramDataCertificationKit.ini, and reddit.exe
Read more: https://www.cloudsek.com/blog/reborn-in-rust-muddywater-evolves-tooling-with-rustywater-implant